Professional Documents
Culture Documents
Pankaj Content
Uploaded by
Abhay SinghOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Pankaj Content
Uploaded by
Abhay SinghCopyright:
Available Formats
Cisco Certified Network Associate (CCNA)
Training Report On Cisco Certified Network Associate (CCNA) (Network Security, NAT & PAT)
Submitted in the partial fulfillment of the requirement for the award of degree of
Bachelors of Technology In Computer Science Engineering
Submitted by: Name: Pankaj Rai Reg. Number: 10902129 Name and Location of Company: NETMAX Technology Pvt. Ltd. SCO2, Choti Baradari Part-1 Jalandhar, Punjab (144001) Period Training: 01/06/2012- 15/07/2012
Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA)
Department of Computer Science Engineering Lovely Professional University Phagwara144001, Punjab (India)
Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA) Ph. (01824-506960-61) Department of Computer Science Engineering Lovely Professional University Phagwara (Distt. Kapurthala) Punjab India 144001
Ref:__________
Dated: __________
Certificate
Certified that this Training entitled Area of training submitted by Name of the Student (Roll Number), students of Computer Science Engineering Department, Lovely Professional University, Phagwara Punjab in the partial fulfillment of the requirement for the award of Bachelors of Technology (Computer Science Engineering) Degree of LPU, is a record of students own study carried under my supervision & guidance.
Name and Signature of Training Supervisor Designation
Head of the Domain
Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA)
ACKNOWLEDGEMENT
Every piece of creation is originated by the zeal of hard work and determination and to put the effort into action, a lot many factors may influence. Nothing concrete can be achieved without optimum inspiration and perspiration. The phenomenon of creation is very long and involves time consuming process, energy, dedication as well as the skills and Experience of the persons involved in the task. The basic view is to evolve an original and substantial work with many helping hands. Joining NETMAX TECHNOLOGIES as trainees gave me solid platform for nursing my professional career. I t g i v e s m e i m m e n s e p l e a s u r e t o e x p r e s s m y deepest gratitude towards all those persons who have been a vital part of this creation. But thinking them all specifically seems to be impossible, so to fit into the framework of words and acknowledgement. I would like to thank my sir Mr. Jaswinder Singh and Mr. Ajit Pal Brar for providing me the environment which really nursed me to endeavor my professional career. Their backup and motivation always inspired me and acted as a morale booster.
I whole-heartedly thank the whole NETMAX TEAM for giving me the opportunities to bring out the best in me and developing my talents and knowledge, not only in the technical field but also in my overall personality. My sincere thanks goes to all the people who cooperated by providing very cordial environment during the course of work.
All Sincere thanks to Respected HOD sir (CSE) for guiding me not only as a faculty but also for all other problems.
In addition, I would like to thank my colleges T.P. Dept. for the permission to allow me to go on industrial training and have the industry related experience.
Last but not the least, I express my deep felt gratitude to my parents and friends without whose moral support and encouragement, I would have never been able to bring this project to completion in such a presentable form and that too successfully!
INDERPREET SINGH 100610391677
Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA)
TABLE OF CONTENTS S. NO. TITLE 1. ABOUT THE ORGANISATION 2. FLOW CHART OF THE PROCESS AT THE ORGANISATION 3. DETAILS OF WORK/JOB ASSIGNED 4. LEARNING OUTCOMES & ANALYSIS 5. CONCLUSIONS 6. FUTURE SCOPE OF THIS TYPE TRAINING PAGE NO.
The Project Report should be spiral-Binding and the title page should be as per the format (Black on white A4 sheet). Note:
1. One copy is to be submitted to the examiners panel at the time of presentation and evaluation 2. Training report must have minimum 20-30 A4 pages. 3. A power point presentation of 8-10min duration followed by question answer session would be done by each student.
Format must be in New Time Roman (12) for normal and Headlines Size must be
(14+Bold)
Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA)
1. ABOUT THE ORGANISATION
NETMAX TECHNOLOGIES as an organization was established in 2001. It provide training to students and corporate in CISCO, REDHAT, SUN, and MICROSOFT over the past ten years. It is the first Org. to introduce CCNP, CCSP, CCVP and CCIE in north region to meet the current needs of our corporate clients. NETMAX TECHNOLOGIES is active in the following sectors: IT Training IT Support Embedded systems training In Education It has strategic alliance with Pearson VUE. They are authorized certified testing Partner of REDHAT, MICROSOFT & CISCO. We are also NOVELL EDUCATION PARTNER with which we provide NOVELL and SUSE LINUX courses. NETMAX TECHNOLOGIES also conduct courses in CADENCE based design tools. Microcontroller based design Electronics system design
Since Their inception, they have remained true to five unwavering commitments...
Draw on the expertise of experienced trainers. Each of our trainers has an average of four years relevant experience in the industry. Together, they have accumulated thousands of teaching hours. No other training center in Region boasts a team with this level of expertise. Provide an environment that is conducive to learning. Among other things, participants have access to top-of-the-line network and system infrastructure. This is why we adhere to rigorous standards of methodology and ensure that our faculty and technicians provide you with assistance should you encountering any problems. Use comprehensive learning material. We provide each participant with comprehensive material that is recommended and an easy-to-use reference guide in which students can find any of the information covered during the course. Provide concrete and current course content. We constantly update and improve our course content in response to the changes made by vendors like CISCO, Microsoft.
Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA)
OUR TEAM
Presently we have a strong technical team of certified professionals for catering to these solutions and have presence in Chandigarh and Punjab. We have skilled team of engineers who are experienced in design, programming. We are having more than 15 engineers who are having prestigious certifications like CCNA, CCNP, CCSP, CCSA, MCSE, RHCE, C++, C, and JAVA & PHP MySQL Programming.
Support Area (network solutions)
LINUX / UNIX networks SUN networks CISCO devices (Routers, Switches, Firewalls, Cache Engine, RAS etc) Bandwidth Manager software and hardware Radio Links Security Solutions
Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA) NETMAX-TECHNOLOGIES provide the following Courses in IT & Embedded Systems given below:
Network Training
CISCO CCNA, CCNP,CCSP,CCIE
RED HAT LINUX
SUN SOLARIS WINDOWS 2000, 2003 (MCP,MCSA & MCSE) SUSE LINUX
Software Training
VB .Net C# .Net ASP .Net PHP JAVA C/C++
Design Services (Embedded systems)
AVR family MCS 51 ELECTRONIC SYSTEM DESIGN Our core strength is our commitment, technical expertise and cost effective solutions. We ensure high service levels and prompt support availability leading to lower downtime.
Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA)
3. DETAILS OF WORK/JOB ASSIGNED COURSE INTRODUCTION
In this course we are going to study a lot of technologies and our objective will be: Create a large sized LAN network Implement WAN connectivity between multiple locations Routing traffic between different locations Secure networks and Control traffic flow Connect organization to ISP Wi-Fi LAN networks
To achieve all these objectives we must know about following technologies: Switches VLAN, Inter VLAN, Frame Tagging, Spanning Tree, Port Security, Ether Channel Routing Static, Dynamic, RIP, EIGRP, OSPF Security Access-lists, CBAC, VPN, NAT To perform all these tasks on Router and Switches some prerequisites are required: OSI and TCP/IP model IPv4 basics & Sub-netting Router and Switch Administration
Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA)
What is Network?
In one network more than one computer connected with each other through centralized device. They can share files and resources with each other.
LAN
LAN stands for Local Area Network. The scope of the LAN is within one building, one school or within one lab. In LAN (Hub), media access method is used CSMA/CD in which each computer sense the carrier before sending the data over the n/w. if carrier is free then you can transmit otherwise you have to wait or you have to listen. In multiple access each computer have right that they can access each other. If two computers sense the carrier on same time then the collision occur. Each computer, in the network, aware about the collision. Now this stop transmitting and they will use back off algorithm. In which random number is generated. This number or algorithm is used by each computer. Who has short number or small number, he has first priority to transmit the data over the network and other computers will wait for their turn.
WAN
WAN stands for Wide Area Network, in which two local area networks are connected through public n/w. it may be through telecommunication infrastructure or dedicated lines. For e.g: ISDN lines, Leased lines etc. In which we can use WAN devices and WAN technology. You can also connect with your remote area through existing Internetwork called Internet.
Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA)
Network Devices Hub
Hub is centralized device, which is used to connect multiple workstations. There are two types of Hub: (i) Active Hub (ii) Passive Hub It has no special kind of memory. It simply receives the frame (data) and forwards it to all its nodes except the receiving node. It always performs broadcasting. In case of hub, there is one collision domain and one broadcast domain. In case of hub, the media access method is used CSMA/CD (Carrier Sense Multiple Access/Collision Detection). (i) Active Hub In Active hub, it receives the frame regenerate and then forward to all its nodes. (ii) Passive Hub In Passive hub, it simply receives the frame and forward to all its connected nodes. You cannot perform LAN segmentation using hub.
Switch
Switch is also used to connect multiple workstations. Switch is more intelligent than hub. It has special kind of memory called mac address/filter/lookup table. Switch reads mac addresses. Switch stores mac addresses in its filter address table. Switch when receives frame, it reads the destination mac address and consult with its filter table. If he has entry in its filter table then he forwards the frame to that particular mac address, if not found then it performs broadcasting to all its connected nodes. Every port has its own buffer memory. A port has two queues one is input queue and second is output queue. When switch receives the frame, the frame is received in input queue and forward from output queue. So in case of switch there is no chance or place for collisions. In case of switch, the media access method is used CSMA/CA (Carrier Sense Multiple Access/ Collision Avoidance). Switches provide more efficiency, more speed and security. There are two types of switches: Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA) (i) Manageable switches (can be configured with console cable). (ii) Non-manageable switches. We can perform LAN segmentation by using switches.
Bridge
Bridge is a hardware device, which is used to provide LAN segmentation means it is used for break the collision domain. It has same functionality as performed by switch. We can use bridge between two different topologies. It has fewer ports. Each port has a own buffer memory. It works on Data Link Layer of OSI model. It also read mac address and stores it in its filter table. In case of bridge there is one broadcast domain.
Router
Router is hardware device, which is used to communicate two different networks. Router performs routing and path determination. It does not perform broadcast information. There are two types of routers: (i) Hardware Routers are developed by Cisco, HP. (ii) Software Routers is configured with the help of routing and remote access. This feature is offered by Microsoft. This feature is by default installed, but you have to enable or configure it. Hardware routers are dedicated routers. They are more efficient. But in case of software routers, it has less features, slow performance. They are not very much efficient.
LAN Card
LAN card is media access device. LAN card provide us connectivity in the network. There is a RJ45 (Registered Jack) connector space on the LAN card. RJ45 is used in UTP cable. There is another led which is also called heartbeat of LAN card. When any activity occurs it may be receiving or transmitting any kind of data. This led start blinking and also tells us the status of LAN card.
Network Security
Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA)
Access Control List
ACL are the basic security feature that is required in any network to control the flow of traffic. Most of time our network may have servers and clients for which traffic control is required. We can also use ACL to classify the traffic. ACLs are used in features like QOS (Quality of Service), Prioritize traffic and interesting traffic for ISDN.
Classification Access Control List: Types of ACL based on Protocol: (1) IP Access Control List (2) IPX Access Control List (3) AppleTalk Access Control List Types of ACL based on Feature: (1) Standard ACL (2) Extended ACL Types of ACL based on Access mode: (1) Numbered ACL (2) Named ACL Types of ACL based on Order of rules: (1) Deny, permit (2) Permit, deny Types of ACL based on direction of implementation: (1) Inbound ACL (2) Outbound ACL
Flow chart of Inbound ACL
Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA)
A Packet is received
Is there any Accesslist applied on interface in Inbound direction?
No
The packet is passed to Routing Engine
Yes
Is there any matching rule in ACL from topdown order?
No
The packet is dropped.
Yes Yes No
The packet is passed to RE
Is it permit ?
The packet is dropped.
IP Standard ACL (Numbered)
In Standard ACL, we are only able to specify source address for the filtering of packets. The syntax to create IP standard ACL are: Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA)
Router#conf ter Router(config)#access-list <no> <permit|deny> <source> Router(config)#exit <source> Single pc host 192.168.10.5 192.168.10.5 192.168.10.5 0.0.0.0 200.100.100.0 0.0.0.255 200.100.100.32 0.0.0.15 any
N/w Subnet All
Example: - 172.16.0.16 18 should not access Internet; rest of all other pc should access Internet.
Internet
Router
172.16.0.1
172.16.x.x Router#conf ter Router(config)#access-list 30 deny 172.16.0.16 Router(config)#access-list 30 deny 172.16.0.17 Router(config)#access-list 30 deny 172.16.0.18 Router(config)#access-list 30 permit any Router(config)#exit
Applying ACL on interface
Router#conf ter Router(config)#interface <type> <no> Router(config-if)#ip access-group <ACL no.> <in|out>
Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA) Router(config-if)#exit
Rule for applying ACL
Only one ACL can be applied on each interface, in each direction for each protocol. Example: - Suppose we want to allow Internet only for 192.168.10.32 70.
Internet
Router
Router(config)#access-list 25 permit 192.168.10.32 0.0.0.31 Router(config)#access-list 25 permit 192.168.10.64 0.0.0.3 Router(config)#access-list 25 permit 192.168.10.68 Router(config)#access-list 25 permit 192.168.10.69 Router(config)#access-list 25 permit 192.168.10.70 Router(config)#interface serial 0 Router(config-if)#ip access-group 25 out
IP Standard ACL (Named)
In Numbered ACL editing feature is not available that is we are not able to delete single rule from the ACL. In Named ACL editing feature is available. Router#config ter Router(config)#ip access-list standard <name> Router(config-std-nacl)#<deny|permit> <source> Router(config-std-nacl)#exit
Router#conf ter Router(config)#ip access-list standard abc Router(config-std-nacl)#deny 172.16.0.16 Router(config-std-nacl)#deny 172.16.0.17 Router(config-std-nacl)#deny 172.16.0.18
Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA) Router(config-std-nacl)#permit any Router(config-std-nacl)#exit
To modify the ACL
Router#conf ter Router(config)#ip access-list standard abc Router(config-std-nacl)#no deny 172.16.0.17 Router(config-std-nacl)#exit
To control Telnet access using ACL
If we want to control telnet with the help of ACL then we can create a standard ACL and apply this ACL on vty port. The ACL that we will create for vty will be permit deny order. Example: - suppose we want to allow telnet to our router from 192.168.10.5 & 192.168.10.30 pc. Router#conf ter Router(config)#access-list 50 permit 192.168.10.5 Router(config)#access-list 50 permit 192.168.10.30 Router(config)#line vty 0 4 Router(config-line)#access-class 50 in Router(config)#exit
IP Extended ACL (Numbered)
Extended ACL are advanced ACL. ACL, which can control traffic flow on the basis of five different parameters that are: (i) Source address (ii) Destination address (iii) Source port (iv) Destination port (v) Protocol (layer 3/layer 4)
The syntax to create Extended ACL
Router#conf ter Router(config)#access-list <no> <deny|permit> <protocol> <source> [<s.port>] <destination> [<d.port>] router(config)#exit
<no> <protocol>
-> ->
100 to 199 layer IP TCP UDP
Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA) ICMP IGRP no (1 to 65535) or telnet/www/ftp etc. Single pc 192.168.10.4 0.0.0.0 host 192.168.10.4 N/w 200.100.100.0 0.0.0.255 Subnet 172.30.0.32 0.0.0.7 All Any
<Source port> <Destination port> <Source> <Destination>
Example rules of Extended ACL
Router(config)#access-list 140 deny ip 192.168.10.3 0.0.0.0 any (All tcp/ip data is denied from source 192.168.10.3 to any destination) Router(config)#access-list 120 permit ip any any (All tcp/ip data permit from any source to any destination) Router(config)#access-list 145 deny tcp any host 200.100.100.5 (All tcp data is denied from any source to host 200.100.100.5) Router(config)#access-list 130 permit tcp any host 200.100.100.10 eq 80 (All tcp based data from any source is allowed to access destination 200.100.100.10 on port no. 80 that is www(http) ) web access Router(config)#access-list 130 permit udp any host 200.100.100.10 eq 53 (Any pc is able to access our DNS service running on port no. 53) Router(config)#access-list 150 deny tcp any any eq 23 [or telnet] (Telnet traffic is not allowed) Router(config)#access-list 160 deny icmp any any (All icmp data from any source to any destination is denied)
To display ACL
Router#show access-lists or Router#show access-list <no>
Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA)
To display ACL applied on interface
Router#show ip interface Router#show ip interface <type> <no> Router#show ip interface Ethernet 0 Example: - Extended ACL Suppose we want to control inbound traffic for our network. ACL should be designed according the following policy. (1) Access to web server (200.100.100.3) is allowed from any source. (2) FTP server (200.100.100.4) should be accessible only from branch office n/w (200.100.175.0/24). (3) ICMP & Telnet should be allowed only from remote pc 200.100.175.80 (4) Any pc can access DNS (200.100.100.8)
Router
200.100.175.x
Router
200.100.100.x Router(config)#access-list 130 permit tcp any host 200.100.100.3 eq 80 Router(config)#access-list 130 permit tcp 200.100.175.0 0.0.0.255 200.100.100.4 0.0.0.0 Eq 21 Router(config)#access-list 130 permit icmp 200.100.175.80 0.0.0.0 any Router(config)#access-list 130 permit tcp 200.100.175.80 0.0.0.0 any eq 23 Router(config)#access-list 130 permit udp any host 200.100.100.8 eq 53
Switch port ACL
You can only apply port ACLs to layer 2 interfaces on your switches because they are only supported on physical layer 2 interfaces. You can apply them as only inbound lists on your interfaces, and you can use only named lists as well. Extended IP access lists use both source and destination addresses as well as optional
Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA) protocol information and port number. There are also MAC extended access lists that use source and destination MAC addresses and optional protocol type information. Switches scrutinize all inbound ACLs applied to a certain interface and decide to allow traffic through depending on whether the traffic is a good match to the ACL or not. ACLs can also be used to control traffic on VLANs. You just need to apply a port ACL to a trunk port. Switch#conf ter Switch(config)#mac access-list extended abc Switch(config-ext-mac)#deny any host 000d.29bd.4b85 Switch(config-ext-mac)#permit any any Switch(config-ext-mac)#do show access-list Switch(config-ext-mac)#int f0/6 Switch(config-if)#mac access-group abc in
Time-Based ACLs
In this you can specify a certain time of day and week and then identity that particular period by giving it a name referenced by a task. The reference function will fall under whatever time constraints you have dictated. The time period is based upon the routers clock, but it is highly recommended that using it in conjunction with Network Time Protocol (NTP) synchronization. Router#conf ter Router(config)#time-range no-http Router(config-time-range)#periodic <Wednesday|weekdays|weekend> 06:00 to 12:00 Router(config-time-range)#exit
Router(config)#time-range tcp-yes Router(config-time-range)#periodic weekend 06:00 to 12:00 Router(config-time-range)#exit Router(config)ip access-list extended time Router(config-ext-nacl)#deny tcp any any eq www time-range no-http Router(config-ext-nacl)#permit tcp any any time-range tcp-yes Router(config-ext-nacl)#interface f0/0 Router(config-if)#ip access-group time in Router(config-if)#do show time-range
Remarks
Remarks are the comments or remarks regarding the entries you have made in both your IP Standard and Extended ACLs. Router#conf ter Router(config)#access-list 110 remark <remark words> permit rahul from admin only to sale
Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA) Router(config)#access-list 110 permit ip host 172.16.10.1 172.16.20.0 0.0.0.255 Router(config)#access-list 110 deny ip 172.16.10.0 0.0.0.255 172.16.20.0 0.0.0.255 Router(config)#ip access-list extended no_telnet Router(config-ext-nacl)#remark deny all of finance from telnetting to sale Router(config-ext-nacl)#deny tcp 172.16.30.0 0.0.0.255 172.16.20.0 0.0.0.255 eq 23 Router(config-ext-nacl)#permit ip any any Router(config-ext-nacl)#do show run
Network Address Translation (NAT)
NAT is the feature that can be enable in a Router, Firewall or a Pc. With the help of NAT, we are able to translate network layer addresses that are IP addresses of packets. With the help of Port Address Translation, we are also able to translate port no.s present in transport layer header.
Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA)
Advantage of NAT
There are two reasons due to which we use NAT: (1) Conserve Live IP address On Internet, there are limited no of IP addresses. If our Pc wants to communicate on Internet then it should have a Live IP address assigned by our ISP. So that IP address request will depend on no. of PCs that we want to connect on Internet. Due to this, there will be a lot of wastage in IP addresses. To reduce wastage, we can share live IP addresses between multiple PCs with the help of NAT. (2) NAT enhances the network security by hiding PC & devices behind NAT.
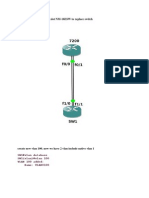
Working of NAT & PAT
10.0.0.5
10.0.0.6
Switch
10.0.0.1
NAT
200.100.100.12
Internet
10.0.0.7
10.0.0.8
10.0.0.5 200.100.100.12 1080 10.0.0.6 200.100.100.12 1085
10.0.0.7 200.100.100.12 1024
1100
Port Translation
10.0.0.8 200.100.100.12 1024
Types of NAT Static NAT
This NAT is used for servers in which one Live IP is directly mapped to one Local IP. This NAT will forward on the traffic for the Live IP to the Local PC in the n/w.
Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA) Static NAT 200.1.1.5 = 192.168.10.6
Internet Router
Live 200.1.1.5
Local 192.168.10.6
Port Base Static NAT
This NAT is also used for servers. It provides port-based access to the servers with the help of NAT. 200.1.1.5:80 -> 192.168.10.6 200.1.1.5:53 -> 192.168.10.7
Router Internet
Web 192.168.10.6
DNS 192.168.10.7
Dynamic NAT using Pool
Dynamic NAT is used for clients, which want to access Internet. The request from multiple clients IPs are translated with the Live IP obtained from the Pool. It is also called Pool Based Dynamic NAT. Pool => 200.1.1.8 200.1.1.12/28
Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA) Local address => 172.16.X.X Except => 172.16.0.5 172.16.0.6 172.16.0.7
Internet
Router
Web Server DNS Full access 172.16.0.5 172.16.0.6 172.16.0.7 Pool allotted => 200.1.1.0 15/28 Server Static => 200.1.1.3 = 172.16.0.7 Port Based Static NAT 200.1.1.4:53 = 172.16.0.6 200.1.1.4:80 = 172.16.0.5 Client Dynamic NAT Pool => 200.1.1.8 200.1.1.12/28 Local address => 172.16.0.X Except 172.16.0.5 172.16.0.6 172.16.0.7
172.16.X.X
Configuring NAT
Router#conf ter Router(config)#int serial 0 Router(config-if)#ip nat outside Router(config-if)#int eth 0 Router(config-if)#ip nat inside Router(config-if)#exit Router(config)#ip nat inside source static 172.16.0.7 200.1.1.3 Router(config)#ip nat inside source static tcp 172.16.0.5 80 200.1.1.4 80
Lovely Professional University Punjab
Cisco Certified Network Associate (CCNA) Router(config)#ip nat inside source static udp 172.16.0.6 53 200.1.1.4 53 Router(config)#access-list 30 deny 172.16.0.5 Router(config)#access-list 30 deny 172.16.0.6 Router(config)#access-list 30 deny 172.16.0.7 Router(config)#access-list 30 permit any Router(config)#ip nat pool abc 200.1.1.8 200.1.1.12 netmask 255.255.255.240 Router(config)#ip nat inside source list 30 pool abc overload NAT + PAT
Command for Basic NAT
Router(config)#ip nat inside source list 30 interface serial 0 <exiting interface name>
To display NAT translation
Router#sh ip nat translations (after ping any address, it shows ping details)
To clear IP NAT Translation
Router#clear ip nat Translation *
4. LEARNING OUTCOMES & ANALYSIS
Lovely Professional University Punjab
You might also like
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (890)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- Data Center Design Case StudiesDocument256 pagesData Center Design Case StudiesGeorgi Dobrev50% (6)
- Manual de Hardware FiberhomeDocument76 pagesManual de Hardware FiberhomeFlavio Rodrigo LeonelNo ratings yet
- Bas Admin Guide 2.0Document354 pagesBas Admin Guide 2.0Greg Williams100% (1)
- 07 Final Exam - B - 1610961584815Document11 pages07 Final Exam - B - 1610961584815Paksi Alam100% (1)
- Article 1Document2 pagesArticle 1Abhay SinghNo ratings yet
- CQDocument5 pagesCQAbhay SinghNo ratings yet
- 1 Time ManagementDocument3 pages1 Time ManagementAbhay SinghNo ratings yet
- 1 Time ManagementDocument3 pages1 Time ManagementAbhay SinghNo ratings yet
- EthicDocument8 pagesEthicAbhay SinghNo ratings yet
- 4294 1 Format of Six Weeks Training Report UpdatedDocument5 pages4294 1 Format of Six Weeks Training Report UpdatedSatnam Singh VirkNo ratings yet
- Slides Prepared by John LoucksDocument30 pagesSlides Prepared by John LoucksAli SyedNo ratings yet
- Chapter 3 - Layered ModelsDocument53 pagesChapter 3 - Layered ModelsDanny KirooNo ratings yet
- Chapter 4 - Firewalls and Intrusion PreventionDocument34 pagesChapter 4 - Firewalls and Intrusion PreventionMohammad Rafsun IslamNo ratings yet
- Lab 9.3.6 Configuring Inter-VLAN Routing: Nombre Del Alumno: GAMBOA CANTO LUIS JORGEDocument7 pagesLab 9.3.6 Configuring Inter-VLAN Routing: Nombre Del Alumno: GAMBOA CANTO LUIS JORGELuis Gamboa CantoNo ratings yet
- corDECT TechnologyDocument29 pagescorDECT TechnologySanketh Somaiah MotteraNo ratings yet
- Sasken IPNetworkingv 3 NewDocument662 pagesSasken IPNetworkingv 3 NewNarasimhan Sree RamNo ratings yet
- Poweredge-1855 User's Guide2 En-UsDocument32 pagesPoweredge-1855 User's Guide2 En-UsShaun PhelpsNo ratings yet
- Industial Phy Layer Dec 2012 CompacDocument120 pagesIndustial Phy Layer Dec 2012 CompacnegrinNo ratings yet
- 8th Computer AssignmentDocument6 pages8th Computer Assignmentpubgkr210407No ratings yet
- Siprotec 5 Communication Protocol Siprotec 5 Communication Protocol Dnp3 v500Document88 pagesSiprotec 5 Communication Protocol Siprotec 5 Communication Protocol Dnp3 v500MherreraNo ratings yet
- As Usual, I'll Use 3660 With Slot NM-16ESW To Replace SwitchDocument9 pagesAs Usual, I'll Use 3660 With Slot NM-16ESW To Replace SwitchLê Chí ThọNo ratings yet
- Tl-sx3008f Jetstream 8-Port 10ge SFP+ l2+ ManagDocument1 pageTl-sx3008f Jetstream 8-Port 10ge SFP+ l2+ ManagVrujesh BhattNo ratings yet
- 715001951ra Breeze 2 Installation Configuration GuideDocument38 pages715001951ra Breeze 2 Installation Configuration GuideAli AnsiNo ratings yet
- NN46205-703 03.02 TroubleshootingDocument466 pagesNN46205-703 03.02 TroubleshootingHarikrishna RamanNo ratings yet
- Valiant Enigmätron-C Data Encryption Router FirewallDocument2 pagesValiant Enigmätron-C Data Encryption Router FirewallJanuardwNo ratings yet
- Building A SupercomputerDocument34 pagesBuilding A SupercomputerTasos KontogiorgisNo ratings yet
- EUCIP - IT Administrator: Module 4 - Expert Network UseDocument8 pagesEUCIP - IT Administrator: Module 4 - Expert Network UseCristian BlanaruNo ratings yet
- 2N Easyroute ManualDocument102 pages2N Easyroute ManualnkoulNo ratings yet
- MCQS On DCNDocument16 pagesMCQS On DCNAvishek ChakrabortyNo ratings yet
- HP Architechtural DiagramDocument71 pagesHP Architechtural Diagrampranav_023No ratings yet
- Catalyst 3750 Series Switches TroubleshootDocument19 pagesCatalyst 3750 Series Switches TroubleshootSugumar DuraisamyNo ratings yet
- Cisco MDS 9000 Family Release Notes For Cisco MDS NX-OS Release 5.2 (8a)Document56 pagesCisco MDS 9000 Family Release Notes For Cisco MDS NX-OS Release 5.2 (8a)David WongNo ratings yet
- 3 CBLSF 50 HDocument6 pages3 CBLSF 50 HNaz LunNo ratings yet
- Dimetra PDFDocument51 pagesDimetra PDFSohaib Omer SalihNo ratings yet
- SAS Sample Specification - IEC 61850 Station Bus PRP Based TopologyDocument1 pageSAS Sample Specification - IEC 61850 Station Bus PRP Based TopologyKASHIFNo ratings yet
- Dell Compellent Sc4020 Owner's Manual en UsDocument59 pagesDell Compellent Sc4020 Owner's Manual en UsAntonio FrancucciNo ratings yet
- What is Multiplexing and its Types (FDM, WDM, TDMDocument26 pagesWhat is Multiplexing and its Types (FDM, WDM, TDMsdfasdfNo ratings yet