Professional Documents
Culture Documents
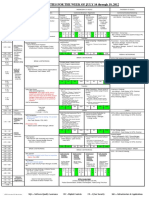
ICIW 2013 Timetable 0306
Uploaded by
sresearcher7Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
ICIW 2013 Timetable 0306
Uploaded by
sresearcher7Copyright:
Available Formats
8th International Conference on Information Warfare and Security Regis University, Denver, USA 25-26 March 2013
Sunday 24 March 2013
18:30 Doubletree Hilton Hotel Pre-conference registration and welcome meeting (Until 1930)
Monday 25 March 2013
09:00 Registration and coffee 09:30 Room: Welcome from the conference chair: Dan Likarish 09:45 Keynote address: David L. Willson, Titan Info Security Group LLC, USA Active Defense: How to Legally Defend Beyond Your Network 10:30 Conference splits into streams Room: Stream A: Chair: Erik Moore 10:45 Improving Public-Private Sector Cooperation on Cyber Event Reporting McNally Julie, Bellevue University, USA Room: Stream B: Chair: Matthew Crosston Strategies for Combating Sophisticated Attacks Arnold Chad, Jonathan Butts and Krishanaprasad Thirunarayan Air Force Institute of Technology, USA Room: Stream C: Mini track on Modelling and Simulation for Cyber Defence Chairs: Joey Jansen van Vururen and Louise Leenen Scada Threats in the Modern Airport McCarthy John, Cranfield University, UK and Bill Mahoney, Nebraska University at Omaha, USA
11:15 Copyright protection based on contextual web watermarking Mir Nighat, Effat University, Saudi Arabia 11:45 The Potential Impact of Cyber-terrorism on National Security of Saudi Arabia Alqahtani Abdulrahman, Hull University, UK, (PhD Research Paper) 12:15 Replication and Diversity for Survivability in Cyberspace: A Game Theoretic Approach Kamhoua Charles, Kevin Kwiat, Partick Hurley, Air Force Research Laboratory, Joon Park, Syracuse University, New York and Mainak Chatterjee, University of Central Florida, Orlando, USA 12:45 07/03/2013 12:46 Lunch
Identifying Tools and Technologies for Professional Offensive Cyber Operations Grant Tim, R-BAR and Ronald Prins, Fox-IT, Delft, Netherlands Situation Management in Aviation Security - A GraphTheoretic Approach Koelle Rainer Eurocontrol Brussels, Belguim and Denis Kolev, Lancaster University, UK The Emergence of Cyber Activity as a Gateway to Human Trafficking Greiman Virginia Boston University and Christina Bain Harvard Kennedy School, Cambridge USA
Deep Routing Simulation Irwin Barry and Alan Herbert, Rhodes University, Grahamstown, South Africa Towards a South African Crowd Control Model Modise Mapule, Zama Dlamini, Sifiso Simelane, Linda Malinga, Thami Mnisi and Sipho Ngobeni, CSIR, Pretoria, South Africa
Lunch This timetable is subject to change
Lunch 1
Room: Stream A: Technical issues Chair: Tim Grant 14:00 Functional Resilience, Functional Resonance, and Threat Anticipation for Rapidly Developed Systems Rohret David, Michael Kraft and Michael Vella, Computer Sciences Corporation Inc., San Antonio USA
Room: Stream B: Hacking Chair: Wilmuth Mller
Room: Stream C: Mini track on Modelling and Simulation for Cyber Defence Chairs: Joey Jansen van Vururen and Louise Leenen
The Adam & Eve Paradox A Vulnerability Modeling in a Bit-Induced Reality Kraft Michael, David Rohret, Michael Vella and Jonathon Moore Erik, Academic Computing Services, Adams 12 Five Holston Computer Sciences Corporation, San Antonio, USA Star School District, Thornton, Colorado, USA (Non-Academic Paper)
14:30 Analysis of Programmable Logic Controller Firmware for Hacking for the Homeland: Patriotic Hackers Versus Threat Assessment and Forensic Investigation Hacktervists: Basnight Zachry, Jonathon Butts, Juan Lopez and Dahan Michael, Sapir College, Israel Thomas Dube Air Force Institute of Technology, USA 15:00 Design of a Hybrid Command and Control Mobile Botnet Pieterse Heloise, CSIR, South Africa and Martin Olivier, University of Pretoria, South Africa 15:30 16:00 Refreshments Refreshments
A Taxonomy of Web Service Attacks Chan Ka Fai Peter and Renier van Heerden, CSIR, Martin Oliver, University of Pretoria, South Africa
Development of a South African Cybersecurity Policy Implementation Framework Jansen van Vuuren Joey, Louise Leenen, Jackie Phahlamohlaka, CSIR, Pretoria and Jannie Zaaiman, University of Venda, Limpopo, South Africa Refreshments
Room: Panel Discussion to be led by Leigh Armistead How to improve metrics and analysis of the testing for cyber security effectiveness Close of conference day Close of conference day Bus leaves to go to The Fort Restaruant for the conference dinner Bus returns to the Doubletree Hotel Close of conference day
17:00 19:00 22:00
07/03/2013 12:46
This timetable is subject to change
Tuesday 26 March 2013
09:30 Room: Keynote address: William Hugh Murray, USA The Drums of War 10:20 Introduction to ICIW 2013 10:30 Refreshments Poster contributors will stand by their posters for participants to discuss their research Room: Stream A: Information and Cyber-War Chair: Michael Dahan Refreshments Poster contributors will stand by their posters for participants to discuss their research Room: Stream B: Chair: Barry Irwin Refreshments Poster contributors will stand by their posters for participants to discuss their research Room: Stream C: Mini Track on The Human Factors of Cyber Operations Chair: Robert Mills Improving Cyber Warfare Decision Making by Incorporating Leadership Styles and Situational Context into Polyhuristics Decision Theory Caudle Daryl, Advanced Education Concepts, Wilmington, DE, USA (PhD Research Paper)
11:00 Consequences of Diminishing Trust in Cyberspace Results From a SCADA-Based Cyber Security Competition Dasgupta Dipankar and Denise Ferebee, The University Novak Heath and Daniel Likarish , Regis University, Dever, of Memphis, USA Colorado, USA
11:30 Offensive Cyber Initiative Framework (OCIF) Raid and Re-spawn Project Rohret David, Micheal Vella and Michael Kraft, Computer Sciences Corporation, USA (Non-Academic Paper) 12:00 Towards a Theory of Just Cyberwar Giesen Klaus-Gerd, Universit d'Auvergne, ClermontFerrand, France
Exercising state sovereignty in cyberspace: An international DUQUS DILEMMA: The Ambiguity Assertion and the cyber-order under construction? Futility of Sanitized Cyber War Liaropoulos Andrew, University of Piraeus, Greece Crosston Matthew, Bellevue University, USA
An Investigation of the Current State of Mobile Strategy Device Management within South Africa Burke Ivan, and F. Mouton CSIR, Pretoria, South Africa
Investigating Hypothesis Generation in Cyber Defense Analysis through an Analogue Task Vickhouse Rachel and Spencer Bryant, Right patterson Air Force Base, Adam Bryant, Riverside Research, Beavercreek, Ohio, USA Lunch
12:30
Lunch
Lunch
07/03/2013 12:46
This timetable is subject to change
Room: Stream A: Information and Cyber-War Chair: Klaus-Gerd Giesen
Room: Stream B: Legal issues Chair: Sam Chung
14:00 Thirst for Information: the Growing Pace of Information What Lawyers Want: Legally Significant Questions That Warfare and Strengthening Positions of Russia, the USA Only IT Specialists Can Answer and China Shiryaev Yaroslav, University of Warwick, Coventry, UK Vasilyeva Inna and Yana Vasilyeva Kuban State University of Technology, Russian Federation 14:30 The Weakest Link The ICT Supply Chain and Information Warfare Shoemaker Daniel and Charles Wilson, University of Detroit Mercy, USA 15:00 Defamation in Cyber Space: Who Do You Sue? Godara Samiksha, Shamsher Bahadur Saxena College Of Law, India
Room: Stream C: Mini Track on The Human Factors of Cyber Operations Chair: Robert Mills Top-Level Goals in Reverse Engineering Executable Software Bryant Adam, Robert Mills, Michael Grimaila and Gilbert Peterson Air Force Institute of Technology, Ohio, USA
Room: A summary of issues raised during the conference Led by Dan Likarish and DougHart Prize for the best poster will be awarded Close of Conference Close of Conference Close of Conference
15:30
Work in Progress and Posters: To be displayed from noon on Thursday until Noon on Friday Poster presenters will stand by their posters to discuss research with others from 1000-1030 on Friday
Evaluation of Cryptographic Security Schemes for Air Traffic Controls Next Generation Upgrade Finke Cindy, Jonathan Butts, Robert Mills and Micheal Grimaila Air Force Institute of Technology, USA Attack-Aware Supervisory Control and Data Acquisition (SCADA) Alexander Otis, Sam Chung and Barbara EndicottPopovsky University of Washington, Seattle, USA Action and reaction: Strategies and tactics of the current political cyberwarfare in Russia Lysenko Volodymyr and Barbara Endicott-Popovsky, University of Washington, Seattle, USA Attack Mitigation Through Memory Encryption of SecurityEnhanced Commodity Processors Henson Michael and Stephen Taylor, Dartmouth College, USA Cyber Disarmament Treaties and the Failure to Consider Adequately Zero-Day Threats Baer Merritt, Harvard Law School, Cabridge, USA
07/03/2013 12:46
This timetable is subject to change
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- Information Security Module OneDocument2 pagesInformation Security Module Onesresearcher750% (2)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Donald BaconDocument5 pagesDonald Baconsresearcher7No ratings yet
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Defense Acquisition Guidebook (DAG), ForewordDocument2 pagesDefense Acquisition Guidebook (DAG), Forewordsresearcher7No ratings yet
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- How To Become A Cyber Warrior - 2012 - 016 - 102 - 67947Document4 pagesHow To Become A Cyber Warrior - 2012 - 016 - 102 - 67947sresearcher7No ratings yet
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (400)
- KYPO Cyber Range Developer: PositionDocument1 pageKYPO Cyber Range Developer: Positionsresearcher7No ratings yet
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- CSD Host Open Soruce Cybersecurity Catalog PDFDocument3 pagesCSD Host Open Soruce Cybersecurity Catalog PDFsresearcher7No ratings yet
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Gradschooltalk PDFDocument22 pagesGradschooltalk PDFsresearcher7No ratings yet
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- CricDocument1 pageCricsresearcher7No ratings yet
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- CricDocument1 pageCricsresearcher7No ratings yet
- Analysis of The Implementation of An Interactive Kinetic Cyber Range ComponentDocument1 pageAnalysis of The Implementation of An Interactive Kinetic Cyber Range Componentsresearcher7No ratings yet
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- Sec Patt IntroDocument19 pagesSec Patt Introkrishnaveni_muruganNo ratings yet
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- NITSL Activities 2012 Rev 09Document1 pageNITSL Activities 2012 Rev 09sresearcher7No ratings yet
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- CFP Cyber v3Document2 pagesCFP Cyber v3sresearcher7No ratings yet
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- CricDocument1 pageCricsresearcher7No ratings yet
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- Ideai2 Att1 Draft SowDocument7 pagesIdeai2 Att1 Draft SowPoer JavaNo ratings yet
- CricDocument1 pageCricsresearcher7No ratings yet
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- 0verview-Crisc Part 1 The Big Picture 2011Document66 pages0verview-Crisc Part 1 The Big Picture 2011saryus2012100% (3)
- CricDocument1 pageCricsresearcher7No ratings yet
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- CricDocument1 pageCricsresearcher7No ratings yet
- CricDocument1 pageCricsresearcher7No ratings yet
- CricDocument1 pageCricsresearcher7No ratings yet
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- CricDocument1 pageCricsresearcher7No ratings yet
- CricDocument1 pageCricsresearcher7No ratings yet
- CricDocument1 pageCricsresearcher7No ratings yet
- CricDocument1 pageCricsresearcher7No ratings yet
- CricDocument1 pageCricsresearcher7No ratings yet
- CricDocument1 pageCricsresearcher7No ratings yet
- CricDocument1 pageCricsresearcher7No ratings yet
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (121)
- CricDocument1 pageCricsresearcher7No ratings yet
- CricDocument1 pageCricsresearcher7No ratings yet
- Fingerprint Reader (Uart) Sn-Fpr-UartDocument35 pagesFingerprint Reader (Uart) Sn-Fpr-Uartejaz2No ratings yet
- TOFU - Toggle Count Analysis Made Simple: Michael Gruber and Georg SiglDocument10 pagesTOFU - Toggle Count Analysis Made Simple: Michael Gruber and Georg Siglrajat835No ratings yet
- Renko Scalper EA Users Manual GuideDocument2 pagesRenko Scalper EA Users Manual GuideRedeemedNo ratings yet
- Release Note E39143Document40 pagesRelease Note E39143Anonymous Ulfg13EGNo ratings yet
- Noveltech Vocal Enhancer Manual enDocument3 pagesNoveltech Vocal Enhancer Manual enpewter6292No ratings yet
- CX ManualDocument9 pagesCX Manualramlijavier75% (4)
- Macherla Pranay KumarDocument2 pagesMacherla Pranay KumarMACHERLA PRANAY KUMARNo ratings yet
- Computer Programming and Applications (ENGG1002C) Assignment 3Document4 pagesComputer Programming and Applications (ENGG1002C) Assignment 3swonder22No ratings yet
- Abdul Majeed ResumeDocument3 pagesAbdul Majeed ResumeM Waqar Ahmad GondalNo ratings yet
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- How To Change Dbname Dbid and Instance NameDocument16 pagesHow To Change Dbname Dbid and Instance NameG.R.THIYAGU ; Oracle DBANo ratings yet
- Exadata Health Resource Usage 2021227Document111 pagesExadata Health Resource Usage 2021227ganurajNo ratings yet
- PMC-53A English Datasheet (20160803)Document4 pagesPMC-53A English Datasheet (20160803)Ronald H SantosNo ratings yet
- Gaussian EleminationDocument7 pagesGaussian EleminationMuhammad RahmandaniNo ratings yet
- Monte Carlo Methods and Bayesian Computation: Importance SamplingDocument5 pagesMonte Carlo Methods and Bayesian Computation: Importance Samplingtadele10No ratings yet
- How To Use AnyConnect VPN - Computing Services - Division of Operations - Carnegie Mellon UniversityDocument4 pagesHow To Use AnyConnect VPN - Computing Services - Division of Operations - Carnegie Mellon UniversityMaheswari JaisankarNo ratings yet
- CryptshyfterDocument6 pagesCryptshyfterapi-357668191No ratings yet
- Kodu Game Lab Privacy StatementDocument3 pagesKodu Game Lab Privacy StatementAli FetohNo ratings yet
- The Story of Gary KildallDocument1 pageThe Story of Gary KildallShubham LashkareNo ratings yet
- Switch On Book 7 - TMDocument65 pagesSwitch On Book 7 - TMThe Promising High SchoolNo ratings yet
- SR No Category Sub Category Course Name Enable / Disable D Hands On? Yes/No Handson DetailDocument3 pagesSR No Category Sub Category Course Name Enable / Disable D Hands On? Yes/No Handson DetailSourav MallickNo ratings yet
- PDFDocument24 pagesPDFSimran KaurNo ratings yet
- SHDB Creare RecordingDocument9 pagesSHDB Creare RecordingElena PuscuNo ratings yet
- Rhino Level 1 Training ManualDocument276 pagesRhino Level 1 Training ManualClaudia TeodoroviciNo ratings yet
- Subject: Theory of Autamata & Formal Languages: Kanpur Institute of Technology Kanpur B.Tech (CS) Smester: Iv SemDocument6 pagesSubject: Theory of Autamata & Formal Languages: Kanpur Institute of Technology Kanpur B.Tech (CS) Smester: Iv Semsantkumar333No ratings yet
- Glomax Discover and Explorer: State-Of-The-Art Multimode Readers For Luminescence, Fluorescence and Absorbance DetectionDocument14 pagesGlomax Discover and Explorer: State-Of-The-Art Multimode Readers For Luminescence, Fluorescence and Absorbance DetectionDanielNo ratings yet
- Mps Series RouterDocument8 pagesMps Series Routers khaNo ratings yet
- Se r18 Lab ManualDocument145 pagesSe r18 Lab Manualpradeeperukulla100% (2)
- SAP End-to-End System Configuration - General LedgerDocument35 pagesSAP End-to-End System Configuration - General LedgerUmaNo ratings yet
- Lecture 02-Modified Galerkin MethodDocument53 pagesLecture 02-Modified Galerkin MethodfefahimNo ratings yet
- Edu 335 Week 5 AssignmentDocument13 pagesEdu 335 Week 5 Assignmentapi-368359457No ratings yet
- The Internet Con: How to Seize the Means of ComputationFrom EverandThe Internet Con: How to Seize the Means of ComputationRating: 5 out of 5 stars5/5 (6)
- Defensive Cyber Mastery: Expert Strategies for Unbeatable Personal and Business SecurityFrom EverandDefensive Cyber Mastery: Expert Strategies for Unbeatable Personal and Business SecurityRating: 5 out of 5 stars5/5 (1)
- Practical Industrial Cybersecurity: ICS, Industry 4.0, and IIoTFrom EverandPractical Industrial Cybersecurity: ICS, Industry 4.0, and IIoTNo ratings yet
- Hacking : The Ultimate Comprehensive Step-By-Step Guide to the Basics of Ethical HackingFrom EverandHacking : The Ultimate Comprehensive Step-By-Step Guide to the Basics of Ethical HackingRating: 5 out of 5 stars5/5 (3)
- Coding Democracy: How a Growing Hacking Movement is Disrupting Concentrations of Power, Mass Surveillance, and Authoritarianism in the Digital AgeFrom EverandCoding Democracy: How a Growing Hacking Movement is Disrupting Concentrations of Power, Mass Surveillance, and Authoritarianism in the Digital AgeRating: 4.5 out of 5 stars4.5/5 (3)