Professional Documents
Culture Documents
Extracting Keys From Second Generation Zigbee Chips
Uploaded by
cjwangOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Extracting Keys From Second Generation Zigbee Chips
Uploaded by
cjwangCopyright:
Available Formats
Extracting Keys from Second Generation Zigbee Chips
Travis Goodspeed
1933 Black Oak Street
Jefferson City, TN, USA
travis@radiantmachines.com
ABSTRACT troller cores were added for convenience, not security, as will
First generation Zigbee chips were SPI slaves with no inter- be explained below.
nal processing beyond cryptographic acceleration. Extract-
ing a key was as simple as spying on the SPI transactions. The third generation of chips will include more powerful
The second generation chips, typified by the CC2430 from microprocessors and–hopefully–a lot more security. The of-
Texas Instruments and the EM250 from Ember, contain fering from Texas Instruments is the CC430 family, based
both a microcontroller and a radio, making the SPI sniffing upon the MSP430X2 processor. Ember will be using the
attack all but irrelevant. Nevertheless, both chips are vul- Arm Cortex M3 in its EM300 series. These chips are out
nerable to local key extraction. This paper describes tech- of scope for this paper, as they are not yet commercially
niques for doing so, focusing on the CC2430 as the EM250 available. Also, Freescale’s line of radios have not yet been
has no protection against outside access. Recommendations examined by the author, but they will be in the near future.
are made for defending CC2430 firmware by using compiler
directives to place sensitive information in flash memory, 2. CONCERNING THE EM250
rather than in RAM. All Chipcon radios with 8051 cores The Ember EM250 contains a 16-bit XAP2b microprocessor
released prior to the publication of this paper are expected from Cambridge Consultants Ltd.[3] Debugging support is
to be vulnerable. provided by that firm’s proprietary SIF protocol, with hard-
ware and software available only through Ember. SIF itself
Keywords is a variant of JTAG.
Zigbee, CC2430, EM250, System on a Chip (SoC)
While the datasheet and various piece of marketing liter-
ature claim “The EM250 employs a configurable memory
1. GENERATIONS protection scheme usually found on larger microcontrollers.”,
First generation Zigbee chips, such as the CC2420, were sim- this refers not to a debugging fuse or bootloader password,
ply digital radios with SPI interfaces and a bit of hardware- but rather to protection from accidental self-corruption of
accelerated cryptography. They could not run a Zigbee stack memory. This is in the form of Application/System separa-
themselves, but rather relied upon an external microcon- tion, allowing the EmberZNet stack to defend certain regions
troller to perform even the most basic of functions. It should of RAM and radio registers from accidental corruption by
also be made clear that Zigbee is one specification for the the application software.[3]
use of these radios, which in the first generation never im-
plemented more than the lowest layers of IEEE 802.15.4. [7] The author has not yet evaluated the protection scheme for
pointed out the obvious with regard to the first generation, its use in defending against stack overflow exploits. It is
which is that keys sent as cleartext by SPI can be sniffed to possible, but not likely, that local privilege escalation from
allow an attacker to participate in a network. Application to System mode is difficult.
The second generation of Zigbee chips were the first to hold In any case, the SIF debugging port of the EM250 does not
a complete Zigbee implementation internally, thanks to the contain a security fuse. There is no supported method of
addition of internal, reprogrammable microprocessors. They denying access to an attacker who controls those pins. Em-
also lack the vulnerability to bus probing, as keys need not ber is aware of the oversight, and they expect that the third
travel over an exposed SPI bus. That said, the microcon- generation EM300 series does not share this vulnerability.
There are presently no plans to fix the EM200 series.
3. CONCERNING THE CC2430
The TI/Chipcon 2430 is a the combination of Chipcon’s
radio technology with an 8051 microcontroller. Also in the
same family are the CC1110, CC2431, CC2510, CC2511,
CC2530, and CC2531. These other chips have not been
To appear at Black Hat USA 2009 tested by the author, but are expected by the documentation
July, 2009, Las Vegas, Nevada. to be similarly vulnerable at the time of this writing.
Like many schemes, including the bootloader (BSL) of some 6. CONCLUSION
MSP430 microcontrollers [6][5], the CC2430 protects flash This paper has shown that all Chipcon radios at the time
memory but not RAM. Further, as a Harvard-architecture of publication are vulnerable to key theft because of unpro-
chip, all constants are copied into RAM by default as a per- tected Data memory. Further, as all popular 8051 compilers
formance feature of the compiler. Thus, while the protection place even constants in Data memory for performance rea-
scheme of the chip is sufficient to protect its programming, sons, it can be assumed that all products which were shipped
it does nothing to prevent the extraction of keys! Extrac- prior to the authorship of this paper are vulnerable. Extract-
tion is as simple as erasing the chip by the debugger, then ing a key is as simple as connecting a debugger, erasing the
reconnecting and dumping RAM. chip, then freely reading the contents of RAM.
Further, as the competing radios from Ember offer even less
4. EXPERIMENTAL APPARATUS security, the tamper resistance of wireless sensors should
1
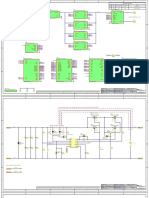
The GoodFET is a USB bus adapter developed by the au-
perhaps be considered forfeit by default.
thor as a means of learning, among other things, the JTAG
protocol. Its firmware includes support for the Chipcon de-
bugging protocol, as documented in [1], allowing the Chip- 7. REFERENCES
con radios to be debugged using a python script, “good- [1] Chipcon. CC1110/CC2430/CC2510 debug and
fet.cc”. programming interface specification.
[2] Chipcon. DN200 using constants in Code with Z-stack.
This vulnerability can be tested for on any 8051-based Chip- [3] Ember. EM250 datasheet.
con device using the script provided in Figure 2. The script [4] J. A. H. et al. Lest we remember: Cold boot attacks on
first places 32 bytes of data into RAM, then dumps those encryption keys.
bytes back out as foo.hex. It then executes CHIP ERASE [5] T. Goodspeed. MSP430 BSL passwords: Brute force
to clear any security fuses and erase flash memory before estimates and defenses, June 2008.
dumping data a second time as bar.hex. If the two dumps [6] T. Goodspeed. A side-channel timing attack of the
are identical, then Data memory (RAM) has not been erased MSP430 BSL. Black Hat USA, August 2008.
along with Code memory (Flash). If the two differ, then the [7] T. Goodspeed, D. Highfill, and B. Singletary. Low-level
chip is not vulnerable to this particular attack. design vulnerabilities in wireless control systems
hardware. In S4 2009.
Figure 1 demonstrates that the CC2430 revision 0x04 is vul-
nerable. Similar results are obtained for all other chips of
this family at the time of this writing. Chipcon has been APPENDIX
made aware of the vulnerability, and they intend to fix fu- A. ACKNOWLEDGMENTS
ture chips. It should be noted that Ember was extremely quick to reply
when contacted about the issue presented within this paper.
While TI was not so quick to respond, thanks are due to
5. PROTECTING 8051 CONSTANTS those employees who ensured that the issue was acknowl-
Key identification within non-key data has been demon- edged.
strated by various authors. The authors of [4] manage to
reliably identify disk encryption keys despite from briefly
unrefreshed DRAM, and they conclude with the statement
that
Ultimately, it might become necessary to treat
DRAM as untrusted, and to avoid storing sensi-
tive information there, but this will not become
feasible until architectures are changed to give
software a safe place to keep its keys.
While personal computers and the EM250 might lack such
a place, it is possible to instruct an 8051 compiler to store
a constant in Code (Flash) memory, rather than in Data
(RAM). This is described in [2], but as a workaround for
RAM limitations rather than as a security measure.
The “ code” keyword must be applied to any const variable
within code memory, as well as any pointer to such a con-
stant. This is because the 8051, as a Harvard machine, does
not have a unified address space. Also note that there is a
slight performance penalty to fetches from code memory, as
they cannot occur at the same time as an instruction fetch.
1
http://goodfet.sf.net/
Chipcon erasure vulnerability test.
by Travis Goodspeed
This script uses the GoodFET to load 32 bytes into data memory
then it sends CHIP_ERASE before requesting those same bytes back.
If the two files are identical, CHIP_ERASE has not cleared data
memory and keys held in data memory are exposed to an attacker.
1) Writing something non-random into data memory.
2) Dumping it back out, so we can compare by MD5 checksum.
3) Erasing the contents of memory, including fuses, by CHIP_ERASE.
4) Dumping a second time, now that the chip has been erased.
5) Comparing:
180e42d3d3850b7a31636385dc2c2eee foo.hex
180e42d3d3850b7a31636385dc2c2eee bar.hex
Images match. RAM is not cleared during a CHIP_ERASE.
Figure 1: Demonstration Log
echo "1) Writing something non-random into data memory."
goodfet.cc writedata app.hex 0xffe0 0xffff >>/dev/null
echo "2) Dumping it back out, so we can compare by MD5 checksum."
goodfet.cc dumpdata foo.hex 0xffe0 0xffff >>/dev/null
echo "3) Erasing the contents of memory, including fuses, by CHIP_ERASE."
goodfet.cc erase >>/dev/null
echo "4) Dumping a second time, now that the chip has been erased."
goodfet.cc dumpdata bar.hex 0xffe0 0xffff >>/dev/null
echo "5) Comparing:"
#Print results.
md5sum foo.hex bar.hex && \
echo "Images match. RAM is not cleared during a CHIP_ERASE." || \
echo "Images differ. Vulnerability not confirmed."
Figure 2: Vulnerability Test Script
You might also like
- Computer Organization and Design: The Hardware / Software InterfaceFrom EverandComputer Organization and Design: The Hardware / Software InterfaceRating: 4 out of 5 stars4/5 (12)
- SOP No. 6Document22 pagesSOP No. 6Eli CohenNo ratings yet
- PlayStation Architecture: Architecture of Consoles: A Practical Analysis, #6From EverandPlayStation Architecture: Architecture of Consoles: A Practical Analysis, #6No ratings yet
- Two 2 Page Quality ManualDocument2 pagesTwo 2 Page Quality Manualtony sNo ratings yet
- Faq MC7455Document20 pagesFaq MC7455jacobbowserNo ratings yet
- Smart Card TopologyDocument163 pagesSmart Card TopologysapnarajeshNo ratings yet
- Smart CardDocument56 pagesSmart CardPrudhvi RajNo ratings yet
- Generic BH2017 Hacking Hardware With A 10 Reader WPDocument17 pagesGeneric BH2017 Hacking Hardware With A 10 Reader WPMichael HarrisNo ratings yet
- MicrophobingDocument8 pagesMicrophobinganushka chaubeyNo ratings yet
- A Microcontroller Is A Programmable Digital Processor With Necessary PeripheralsDocument77 pagesA Microcontroller Is A Programmable Digital Processor With Necessary PeripheralsPrem KumarNo ratings yet
- h2hc2014 Reversing Firmware Radare SlidesDocument46 pagesh2hc2014 Reversing Firmware Radare SlidesntcaseNo ratings yet
- AN201 - Writing To Flash From FirmwareDocument11 pagesAN201 - Writing To Flash From FirmwareMot. Schutzen '90No ratings yet
- Answer Lad d4 3 3 2Document6 pagesAnswer Lad d4 3 3 2Sang NiyomkhamNo ratings yet
- IBM FlashSystem V9000 Quick Start GuideDocument32 pagesIBM FlashSystem V9000 Quick Start GuideSiape GueNo ratings yet
- AN3885Document36 pagesAN3885Dragan ZubacNo ratings yet
- User's Guide: 100/10M PCI Adapter & 100/10M Wake On LAN PCI AdapterDocument7 pagesUser's Guide: 100/10M PCI Adapter & 100/10M Wake On LAN PCI AdapterIrina IovanelNo ratings yet
- Attacking Intel TXT Via SINIT Hijacking PDFDocument9 pagesAttacking Intel TXT Via SINIT Hijacking PDFJuliamNo ratings yet
- A Case Study in Hardware Trojan Design and Implementation: Michael Steffen Joseph ZambrenoDocument14 pagesA Case Study in Hardware Trojan Design and Implementation: Michael Steffen Joseph ZambrenosaraaNo ratings yet
- Network Drives Security WhitepaperDocument40 pagesNetwork Drives Security WhitepaperSaba WasimNo ratings yet
- B450M Ds3H Wifi: User's ManualDocument46 pagesB450M Ds3H Wifi: User's ManualNosue AccountNo ratings yet
- VBMB - 007Document42 pagesVBMB - 007gg.ganapathyNo ratings yet
- Bitstream Modification Attack On SNOW 3GDocument10 pagesBitstream Modification Attack On SNOW 3GHui ZhangNo ratings yet
- What Is A Microcontroller?: MicrocontrollersDocument16 pagesWhat Is A Microcontroller?: MicrocontrollersJeanNo ratings yet
- Lockitall LockIT Pro User GuideDocument19 pagesLockitall LockIT Pro User GuideLju LjuNo ratings yet
- IBM Progess LED CodesDocument126 pagesIBM Progess LED Codesyogeshj84No ratings yet
- Williams PDFDocument14 pagesWilliams PDFsonNo ratings yet
- A Secure, Configurable and Customized Multimode Bulk EncryptorDocument4 pagesA Secure, Configurable and Customized Multimode Bulk EncryptorHassaan AlsyedNo ratings yet
- 6.3.2.7 Lab - Exploring Router Physical Characteristics PDFDocument7 pages6.3.2.7 Lab - Exploring Router Physical Characteristics PDFMcDominiNo ratings yet
- CC2540 Bluetooth LE USB DongleDocument11 pagesCC2540 Bluetooth LE USB Donglea.anugrahNo ratings yet
- Jtagjet-C2000: Emulator For The C2000 Family of Mcu/Dsps From Texas InstrumentsDocument3 pagesJtagjet-C2000: Emulator For The C2000 Family of Mcu/Dsps From Texas Instrumentsreza yousefiNo ratings yet
- F W: Transparent Dynamic Analysis For Cellular Baseband FirmwareDocument19 pagesF W: Transparent Dynamic Analysis For Cellular Baseband Firmwarechess991No ratings yet
- C/OS-II Real Time Kernel Port For Cirrus Logic EP93xx PlatformDocument4 pagesC/OS-II Real Time Kernel Port For Cirrus Logic EP93xx PlatformSrinivasulu_My_835No ratings yet
- Advantages of CISC PDFDocument3 pagesAdvantages of CISC PDFArghyadeep HazraNo ratings yet
- Barco Service Bulletin: 1. Security Note - Green BCM Affected by SpectreDocument2 pagesBarco Service Bulletin: 1. Security Note - Green BCM Affected by SpectreDiego BernalNo ratings yet
- Imec Reveals Sub-1nm Transistor Roadmap, 3D-Stacked CMOS 2.0 Plans - Tom's HardwareDocument10 pagesImec Reveals Sub-1nm Transistor Roadmap, 3D-Stacked CMOS 2.0 Plans - Tom's Hardwareandresgarcia500No ratings yet
- Lte Basic Knowledge For DesignDocument24 pagesLte Basic Knowledge For DesignKuldeep SharmaNo ratings yet
- Actividad 2Document4 pagesActividad 2Carlo André Cuellar AguileraNo ratings yet
- W00tsec Unpacking Firmware Images From Cable ModemsDocument10 pagesW00tsec Unpacking Firmware Images From Cable ModemsSebastian QuaroneNo ratings yet
- Implementing A Custom X86 EncoderDocument25 pagesImplementing A Custom X86 EncoderazpoeiNo ratings yet
- Tuesday, April 2, 2019 WWW - Iiu.edu - PK 1Document22 pagesTuesday, April 2, 2019 WWW - Iiu.edu - PK 1mickyNo ratings yet
- MRT Rom Programmer 3Document8 pagesMRT Rom Programmer 3Sergio OrtegaNo ratings yet
- 0605 DvbshopDocument2 pages0605 DvbshopAlexander WieseNo ratings yet
- System On A Chip Design - The Future of VlsiDocument11 pagesSystem On A Chip Design - The Future of Vlsiapi-20008301No ratings yet
- Secmo-Cp: DN0566734 Issue 1-0 en # Nokia Siemens Networks 1Document21 pagesSecmo-Cp: DN0566734 Issue 1-0 en # Nokia Siemens Networks 1maglic.samsungNo ratings yet
- How Does The AT24CM02-SSHM-B EEPROM Memory FunctionDocument6 pagesHow Does The AT24CM02-SSHM-B EEPROM Memory FunctionjackNo ratings yet
- HID iCLASS SecurityDocument13 pagesHID iCLASS SecurityMrJohnGalt09No ratings yet
- ACPI and SMI Handlers Some Limits To Trusted ComputingDocument22 pagesACPI and SMI Handlers Some Limits To Trusted Computingphoebus almasyNo ratings yet
- Etherlinklmc: Micro Channel Ethernet Adapter Technical Reference ManualDocument21 pagesEtherlinklmc: Micro Channel Ethernet Adapter Technical Reference ManualMehmed MuhicNo ratings yet
- PE3514 - Technical Summary For USB-ML-ACPDocument4 pagesPE3514 - Technical Summary For USB-ML-ACPEduardo FernandezNo ratings yet
- Atmel 8390 WIRELESS AVR2054 Serial Bootloader User Guide Application NoteDocument23 pagesAtmel 8390 WIRELESS AVR2054 Serial Bootloader User Guide Application NoteDorel Contrra100% (1)
- Mossinger 2016Document6 pagesMossinger 2016M VijayalakshmiNo ratings yet
- Application Portability For 32-Bit Microcontrollers - Reality or Myth?Document6 pagesApplication Portability For 32-Bit Microcontrollers - Reality or Myth?Dario Darius100% (1)
- ARTIK 055s Module DatasheetDocument34 pagesARTIK 055s Module DatasheetchencswNo ratings yet
- Module 2 AVR ATMega32 ArchitectureDocument44 pagesModule 2 AVR ATMega32 ArchitectureehsanNo ratings yet
- BRKSEC-2002 Understanding and Preventing Layer 2 Attacks PDFDocument103 pagesBRKSEC-2002 Understanding and Preventing Layer 2 Attacks PDFBerrezeg MahieddineNo ratings yet
- V3R1 Progress CodeDocument126 pagesV3R1 Progress CodeBalan LanNo ratings yet
- AS400 - Progress Codes PDFDocument126 pagesAS400 - Progress Codes PDFGuido ZagnoniNo ratings yet
- Dragonboard™ 410C Based On Qualcomm Snapdragon™ 410E ProcessorDocument9 pagesDragonboard™ 410C Based On Qualcomm Snapdragon™ 410E Processorburdun777No ratings yet
- 001 LS 3.0.00 PRNDocument11 pages001 LS 3.0.00 PRNgerson846No ratings yet
- Gain-Cell Embedded DRAMs for Low-Power VLSI Systems-on-ChipFrom EverandGain-Cell Embedded DRAMs for Low-Power VLSI Systems-on-ChipNo ratings yet
- Echo on a Chip - Secure Embedded Systems in Cryptography: A New Perception for the Next Generation of Micro-Controllers handling Encryption for Mobile MessagingFrom EverandEcho on a Chip - Secure Embedded Systems in Cryptography: A New Perception for the Next Generation of Micro-Controllers handling Encryption for Mobile MessagingNo ratings yet
- PLC: Programmable Logic Controller – Arktika.: EXPERIMENTAL PRODUCT BASED ON CPLD.From EverandPLC: Programmable Logic Controller – Arktika.: EXPERIMENTAL PRODUCT BASED ON CPLD.No ratings yet
- Secretary Chu Grid WeekDocument36 pagesSecretary Chu Grid WeekcjwangNo ratings yet
- Harnessing IoT Global DevelopmentDocument61 pagesHarnessing IoT Global Developmentcjwang50% (2)
- MICS Newsletter Jan10Document13 pagesMICS Newsletter Jan10cjwangNo ratings yet
- Nist Security 2nd DraftDocument305 pagesNist Security 2nd DraftcjwangNo ratings yet
- Killerbee: Practical Zigbee Exploitation Framework: Joshua WrightDocument39 pagesKillerbee: Practical Zigbee Exploitation Framework: Joshua Wrightalpeshpatel128No ratings yet
- Iot Forum v0 SanitizedDocument21 pagesIot Forum v0 SanitizedcjwangNo ratings yet
- Sensinode wp5 AmiDocument2 pagesSensinode wp5 AmicjwangNo ratings yet
- 6lowapp Intro v2Document20 pages6lowapp Intro v2cjwang100% (2)
- Boano Thesis 2009Document172 pagesBoano Thesis 2009cjwangNo ratings yet
- BLE Push IR RetireDocument5 pagesBLE Push IR RetirecjwangNo ratings yet
- MICS Newsletter May09Document9 pagesMICS Newsletter May09cjwangNo ratings yet
- 6 LowpanDocument17 pages6 LowpanPriyankar RoychowdhuryNo ratings yet
- MICS Newsletter Sept09Document17 pagesMICS Newsletter Sept09cjwangNo ratings yet
- WSN For Resources TrackingDocument6 pagesWSN For Resources TrackingcjwangNo ratings yet
- MICS Newsletter Mar09Document10 pagesMICS Newsletter Mar09cjwangNo ratings yet
- WSN For HealthcareDocument15 pagesWSN For Healthcarecjwang100% (1)
- FERC NARUC CollaborativeDocument4 pagesFERC NARUC CollaborativecjwangNo ratings yet
- Smart Grid ProgressDocument6 pagesSmart Grid ProgresscjwangNo ratings yet
- The Smart Grid - An IntroductionDocument48 pagesThe Smart Grid - An IntroductionHans De Keulenaer88% (8)
- Cymbet SensorsDocument8 pagesCymbet SensorscjwangNo ratings yet
- 132 March 2009Document4 pages132 March 2009cjwangNo ratings yet
- 1.074 MarnayDocument10 pages1.074 MarnaycjwangNo ratings yet
- Contiki KTH 2008 AbstractsDocument39 pagesContiki KTH 2008 Abstractscjwang100% (1)
- A Mi Press Release 032309Document2 pagesA Mi Press Release 032309cjwangNo ratings yet
- MICS Newsletter - January 2009Document10 pagesMICS Newsletter - January 2009cjwangNo ratings yet
- Sensing The World With Mobile DevicesDocument4 pagesSensing The World With Mobile Devicescjwang100% (1)
- Gibbons SenSys08 KeynoteDocument70 pagesGibbons SenSys08 KeynotecjwangNo ratings yet
- Lightweight Ipv6 Stacks For Smart Objects: The Experience of Three Independent and Interoperable ImplementationsDocument7 pagesLightweight Ipv6 Stacks For Smart Objects: The Experience of Three Independent and Interoperable ImplementationscjwangNo ratings yet
- EN76 WebDocument72 pagesEN76 Webcjwang100% (1)
- Finaniial AsceptsDocument280 pagesFinaniial AsceptsKshipra PrakashNo ratings yet
- BSL-3 Training-1Document22 pagesBSL-3 Training-1Dayanandhi ElangovanNo ratings yet
- Dbms UPDATED MANUAL EWITDocument75 pagesDbms UPDATED MANUAL EWITMadhukesh .kNo ratings yet
- Ucbackup Faq - Commvault: GeneralDocument8 pagesUcbackup Faq - Commvault: GeneralhherNo ratings yet
- BS As On 23-09-2023Document28 pagesBS As On 23-09-2023Farooq MaqboolNo ratings yet
- ODF-2 - Learning MaterialDocument24 pagesODF-2 - Learning MateriallevychafsNo ratings yet
- Jainithesh - Docx CorrectedDocument54 pagesJainithesh - Docx CorrectedBala MuruganNo ratings yet
- Ground Vibration1Document15 pagesGround Vibration1MezamMohammedCherifNo ratings yet
- Well Stimulation TechniquesDocument165 pagesWell Stimulation TechniquesRafael MorenoNo ratings yet
- Company Law Handout 3Document10 pagesCompany Law Handout 3nicoleclleeNo ratings yet
- Relay Interface ModulesDocument2 pagesRelay Interface Modulesmahdi aghamohamadiNo ratings yet
- Indirect Teaching Strategy??: Name: Topic: Under SupervisionDocument9 pagesIndirect Teaching Strategy??: Name: Topic: Under SupervisionSeham FouadNo ratings yet
- CENT - Company Presentation Q1 2020 PDFDocument22 pagesCENT - Company Presentation Q1 2020 PDFsabrina rahmawatiNo ratings yet
- BS en 118-2013-11Document22 pagesBS en 118-2013-11Abey VettoorNo ratings yet
- DevelopersDocument88 pagesDevelopersdiegoesNo ratings yet
- It14 Belotti PDFDocument37 pagesIt14 Belotti PDFHolis AdeNo ratings yet
- Manual Generador KohlerDocument72 pagesManual Generador KohlerEdrazGonzalezNo ratings yet
- SPIE Oil & Gas Services: Pressure VesselsDocument56 pagesSPIE Oil & Gas Services: Pressure VesselsSadashiw PatilNo ratings yet
- Math 1 6Document45 pagesMath 1 6Dhamar Hanania Ashari100% (1)
- 14 CE Chapter 14 - Developing Pricing StrategiesDocument34 pages14 CE Chapter 14 - Developing Pricing StrategiesAsha JaylalNo ratings yet
- Scheme Bidirectional DC-DC ConverterDocument16 pagesScheme Bidirectional DC-DC ConverterNguyễn Quang KhoaNo ratings yet
- A Study On Effective Training Programmes in Auto Mobile IndustryDocument7 pagesA Study On Effective Training Programmes in Auto Mobile IndustrySAURABH SINGHNo ratings yet
- SCHEDULE OF FEES - FinalDocument1 pageSCHEDULE OF FEES - FinalAbhishek SunaNo ratings yet
- Financial StatementDocument8 pagesFinancial StatementDarwin Dionisio ClementeNo ratings yet
- Central Banking and Monetary PolicyDocument13 pagesCentral Banking and Monetary PolicyLuisaNo ratings yet
- Is 10719 (Iso 1302) - 1Document1 pageIs 10719 (Iso 1302) - 1Svapnesh ParikhNo ratings yet
- Dreamfoil Creations & Nemeth DesignsDocument22 pagesDreamfoil Creations & Nemeth DesignsManoel ValentimNo ratings yet
- Rules On Evidence PDFDocument35 pagesRules On Evidence PDFEuodia HodeshNo ratings yet