Professional Documents
Culture Documents
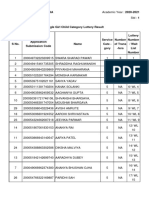
0V.Dsuh %Kdj/Dvkul 6 Vhqlru /HFW 0 0 &roohjh Ri (Qjlqhhulqj 1Dqghg Ekdj/Dvkulndsuh#Jpdlofrp
Uploaded by
amit_saxena_10Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
0V.Dsuh %Kdj/Dvkul 6 Vhqlru /HFW 0 0 &roohjh Ri (Qjlqhhulqj 1Dqghg Ekdj/Dvkulndsuh#Jpdlofrp
Uploaded by
amit_saxena_10Copyright:
Available Formats
Ms.Kapre Bhagyashri S (senior Lect.
)
MGM` College oI Engineering, Nanded
bhagyashrikapre24gmail.com
$EVWUDFW Due Due Due Due to to to to the the the the advancement advancement advancement advancement in in in in Computer Computer Computer Computer
technology technology technology technology and and and and readily readily readily readily available available available available tools, tools, tools, tools, it it it it is is is is very very very very easy easy easy easy for for for for
the the the the unknown unknown unknown unknown users users users users to to to to produce produce produce produce illegal illegal illegal illegal copies copies copies copies of of of of
multimedia multimedia multimedia multimedia data data data data which which which which are are are are floating floating floating floating across across across across the the the the
Internet.In Internet.In Internet.In Internet.In order order order order to to to to protect protect protect protect those those those those multimedia multimedia multimedia multimedia data data data data on on on on
the the the the Internet Internet Internet Internet many many many many techniques techniques techniques techniques are are are are available available available available including including including including
various various various various encryption encryption encryption encryption techniques, techniques, techniques, techniques, steganography steganography steganography steganography
techniques, techniques, techniques, techniques, watermarking watermarking watermarking watermarking techniques techniques techniques techniques and and and and information information information information
hiding hiding hiding hiding techniques. techniques. techniques. techniques. Digital Digital Digital Digital watermarking watermarking watermarking watermarking is is is is aaaa technique technique technique technique
in in in in which which which which a aaa piece piece piece piece of of of of digital digital digital digital information information information information is is is is embedded embedded embedded embedded into into into into
an an an an image image image image and and and and extracted extracted extracted extracted later later later later for for for for ownership ownership ownership ownership verification. verification. verification. verification.
Secret Secret Secret Secret digital digital digital digital data data data data can can can can be be be be embedded embedded embedded embedded either either either either in in in in spatial spatial spatial spatial
domain domain domain domain or or or or in in in in frequency frequency frequency frequency domain domain domain domain of of of of the the the the cover cover cover cover data. data. data. data. In In In In
this this this this paper, paper, paper, paper, a aaa new new new new singular singular singular singular value value value value decomposition decomposition decomposition decomposition (SVD) (SVD) (SVD) (SVD)
and and and and discrete discrete discrete discrete wavelet wavelet wavelet wavelet transformation transformation transformation transformation (DWT) (DWT) (DWT) (DWT) based based based based
technique technique technique technique is is is is proposed proposed proposed proposed for for for for hiding hiding hiding hiding watermark watermark watermark watermark in in in in full full full full
frequency frequency frequency frequency band band band band of of of of color color color color images images images images (DSFW). (DSFW). (DSFW). (DSFW). The The The The quality quality quality quality of of of of
the the the the watermarked watermarked watermarked watermarked image image image image and and and and extracted extracted extracted extracted watermark watermark watermark watermark is is is is
measured measured measured measured using using using using peak peak peak peak signal signal signal signal to to to to noise noise noise noise ratio ratio ratio ratio (PSNR) (PSNR) (PSNR) (PSNR) and and and and
normalized normalized normalized normalized correlation correlation correlation correlation (NC) (NC) (NC) (NC) respectively. respectively. respectively. respectively. It It It It is is is is observed observed observed observed
that that that that the the the the quality quality quality quality of of of of the the the the watermarked watermarked watermarked watermarked image image image image is is is is
maintained maintained maintained maintained with with with with the the the the value value value value of of of of 36dB. 36dB. 36dB. 36dB. Robustness Robustness Robustness Robustness of of of of
proposed proposed proposed proposed algorithm algorithm algorithm algorithm is is is is tested tested tested tested for for for for various various various various attacks attacks attacks attacks
including including including including salt salt salt salt and and and and pepper pepper pepper pepper noise noise noise noise and and and and Gaussian Gaussian Gaussian Gaussian noise, noise, noise, noise,
cropping cropping cropping cropping and and and and 1PEG 1PEG 1PEG 1PEG compression. compression. compression. compression.
Keywords- Digital Digital Digital Digital watermarking, watermarking, watermarking, watermarking, Discrete Discrete Discrete Discrete Wavelet Wavelet Wavelet Wavelet
transformation transformation transformation transformation technique, technique, technique, technique, SVD-Watermarking, SVD-Watermarking, SVD-Watermarking, SVD-Watermarking,
Transform Transform Transform Transform Domain Domain Domain Domain watermarking. watermarking. watermarking. watermarking.
I. I. I. I. INTRODUCTION INTRODUCTION INTRODUCTION INTRODUCTION
In recent days, usage oI computer networks Ior
communication and Ior inIormation sharing leads to
increase in size oI Internet. As the size oI the Internet
grows, the volume oI multimedia data (images, text,
video / audio) Iloating around also increases day by
day. As many advanced tools are readily available to
duplicate and modiIy those data in the Internet easily,
security is the major concern, which requires some
mechanisms to protect digital multimedia data. Thus
watermarking is a technique which supports with
Ieasible solution. Digital Watermarking is deIined as
the process oI hiding a piece oI digital data in the
cover data which is to be protected and extracted later
Ior ownership veriIication |1|. Some oI the important
applications oI watermarking technique are copyright
protection, ownership veriIication, Iinger printing,
and broadcast monitoring. The Ieatures oI
watermarking include robustness and perceptibility.
Robustness indicates the resistivity oI watermark
against diIIerent types oI attacks such as cropping,
rotating, scaling, low pass Iiltering, resizing, addition
oI
Mrs. Joshi M.Y. (Asst. ProI.)
MGM` College oI Engineering, Nanded
manisha.y.joshigmail.com
noise, JPEG compression, sharpness, histogram
equalization and contrast adjustment. Those attacks
are either intentional or unintentional. Robustness is
the property which is important Ior ownership
veriIication whereas the Iragility is important Ior
image authentication. Robustness oI watermarking
algorithm is obtained to a maximum level when
inIormation is hidden in robust components oI cover
data. The increasing perceptibility will also decrease
the quality oI watermarked image.
General y inIormation could be hidden,
directly by modiIying the intensity value or pixel
value oI an image or its Irequency components |2|.
The Iormer technique is called spatial domain
technique and later is cal ed Irequency domain
technique. To obtain Irequency components oI an
image, it needs to be transIormed using any one oI
the transIormation techniques such as Discrete
Fourier TransIormation (DFT), Discrete short Fourier
transIormation (DSFT), Discrete Cosine
TransIormation (DCT) |3||4|, Walsh Hadamard
transIormation (DHT) |5||6|, and Discrete wavelet
TransIormation (DWT)|7||8||9||10|. In TransIorm
domain casting oI watermark can be done in Iull
Irequency band oI an image or in speciIic Irequency
band such as in low Irequency band or in high
Irequency band or in middle Irequency band.
In the proposed method DSFW, inIormation is
hidden in YUV space oI a color image. The Ieatures
oI SVD technique|11| are combined with DWT to
embed data in Irequency domain oI cover data. The
review oI related work is given in section II. In
section III overview oI singular value decomposition
is given. The proposed algorithm is discussed in
detail in section IV. Results and analysis oI proposed
algorithm is discussed in section V.
II. II. II. II. REVIEW REVIEW REVIEW REVIEW OF OF OF OF RELATED RELATED RELATED RELATED WORKS WORKS WORKS WORKS
Review oI literature survey has been conducted on
discrete wavelet transIormation combined with singular
value decomposition techniques Ior hiding image
into bands oI diIIerent Irequency and a particular
band is converted into blocks oI size 4x4 Ior
embedding data. Each oI those blocks is SVD
transIormed and watermark is hidden into diagonal
matrix oI every block. The similarity between the
All All All All Frequency Frequency Frequency Frequency Band Band Band Band DWT-SVD DWT-SVD DWT-SVD DWT-SVD Robust Robust Robust Robust
Watermarking Watermarking Watermarking Watermarking Technique Technique Technique Technique for for for for Color Color Color Color Images Images Images Images in in in in
YUV YUV YUV YUV Color Color Color Color Space Space Space Space
___________________________________
978-1-4244-8728-8/11/$26.00 2011 IEEE
original watermark and the extracted watermark Irom
the attacked image is measured using the correlation
Iactor NC. The algorithm shows that when DWT is
combined with SVD technique the watermarking
algorithm outperIorms than the conventional DWT
algorithm with respect to robustness against Gaussian
noise, compression and cropping attacks. In |9| the
DWT is combined with SVD technique to hide data
in high Irequency band oI an image. This scheme
perIorms well Ior variety oI image processing
operations. In |10| Image is transIormed by DWT
technique to K level. The middle Irequency band LH
and HL are SVD transIormed and watermark is
hidden.Similarly in low Irequency and high
Irequency band the watermark is embedded using
distributed discrete wavelet transIorm method
(DDWT). Both algorithms are tested against attacks
and proved that they are robust against cropping
attacks. For at acks such as Gaussian Noise, contrast
adjustment, sharpness, histogram equalization, and
rotation, the proposed scheme is robust by exploiting
the advantage oI the SVD watermarking technique.
In |12| both cover image and watermark image are
pre processed to hide watermark in transIorm
domain. The perIormance evaluation shows that the
algorithm is robust against at acks such as cropping,
Gaussian noise, JPEG compression and low pass
Iiltering. In |14|, three level decomposition oI DWT
is applied on an image to get ten bands oI
Irequencies. Al ten bands oI Irequency coeIIicients
are SVD transIormed to embed watermark. A new
watermarking scheme Ior images based on Human
Visual System (HVS) and Singular Value
Decomposition (SVD) in the wavelet domain is
discussed |15|.Experimental results show its better
perIormance Ior compression, cropping and scaling
attack. As per the review many algorithms are
available to hide watermark in intensity images rather
than color images. In DSFW, color image is taken as
cover data in which al the pixel color components are
highly correlated, so the cover data in RGB color domain is
converted into YUV domain where intensity(Y) and
chrominance (UV) components are decorreleted. Secret
data can be hidden either in intensity components or in
color components. The quality oI watermarked data and
extracted.
III. III. III. III. OVERVIEW OVERVIEW OVERVIEW OVERVIEW OF OF OF OF SINGULAR SINGULAR SINGULAR SINGULAR VALUE VALUE VALUE VALUE
DECOMPOSITION DECOMPOSITION DECOMPOSITION DECOMPOSITION
Singular value decomposition is a linear algebra
technique sed to solve many mathematical problems |11|.
The theoretical background oI SVD technique in image
processing applications to be noticed is |15|:
a) The SVs (Singular Values) oI an image has very
good stability, which means that when a smal value is
added to an image, this does not aIIect the quality with
great variation.
b) SVD is able to eIIiciently represent the intrinsic
algebraic properties oI an image, where singular values
correspond to the brightness oI the image and singular
vectors reIlect geometry characteristics oI the image.
c) An image matrix has many small singular values
compared with the Iirst singular value. Even ignoring these
small singular values in the reconstruction oI the image
does not aIIect the quality oI the reconstructed image
Any image can be considered as a square matrix
without loss oI generality. So SVD technique can be
applied to any kind oI images. II it is a gray scale image the
matrix values are considered as intensity values and it
could be modiIied directly or changes could be done aIter
transIorming images into Irequency domain. The SVD
belongs to orthogonal transIorm which decompose the
given matrix into three matrices oI same size |3|. To
decompose the matrix using SVD technique it need not be a
square matrix. Let us denote the image as matrix A.The
SVD decomposition oI matrix A is given using (1)
AAAA USV USV USV USV
TTTT
(1) (1) (1) (1)
U and V are unitary matrices such that UU
T
I,
VV
T
I, where I is an Identity matrix. U|u1,u2,u3,..un|
V|v1,v2,v3,..vn| , U matrix is called leIt singular
values and V matrix is called right singular values. The
decomposition oI matrix A is obtained using (2
such that all the elements in main diagonal
are in decreasing order like 1 23 ... n0,
where S is the diagonal matrix having in its main
diagonal all positive singular values oI A. Number oI
nonzero values equals the rank oI the matrix. These
positive singular values can be used to embed
watermark. The order oI singular matrix is same as A,
and hence the resultant matrix is also square. Hence
images oI equal size can be taken as cover
object.
IV. IV. IV. IV. PROPOSED PROPOSED PROPOSED PROPOSED SYSTEM SYSTEM SYSTEM SYSTEM DSFW DSFW DSFW DSFW
$ $ $ $ (PEHGGLQJ (PEHGGLQJ (PEHGGLQJ (PEHGGLQJ 3URFHGXUH 3URFHGXUH 3URFHGXUH 3URFHGXUH
The block diagram Ior embedding watermark in
transIorm domain using SVD technique is shown in Fig.1.
As color image is used as cover data in the proposed
system DSFW, the RGB value oI each pixel is converted
into RGB color spaces |13| |12| in which only R
components constitute R color space, G components
constitute G color space and B components constitute B
color space. Watermark can be hidden in any one or in the
three color channels. Since pixel values are highly
correlated in RGB color spaces, inIormation can be hidden
in YUV color spaces. The RGB components oI color
image is converted into RG color spaces which in turn is
converted into YUV color spaces using (3).The YUV color
spaces consists oI luminance (intensity) and chrominance
(color) components. The input image in YUV domain is
shown in Fig.3. The Y component consists oI
intensity values whereas the UV components consist oI
chrominance values oI color image. The energy content oI
Y component is higher than the chrominance components
oI U and V. In DSFW, YUV color spaces are used Ior
embedding secret data aIter transIormed into Irequency
coeIIicients using Haar wavelet. The Haar wavelet is a tool
which is used to convert given image into Iour band oI
Irequency by decompose it. In each level oI decomposition
the input image is decomposed into Iour band oI
Irequencies named LL, LH, HL and HH band. Each band
oI Irequency is SVD transIormed and watermark is hidden
in the singular values (diagonal elements) oI singular
matrix. Then inverse SVD technique and inverse wavelet
transIormation technique is applied to get the watermarked
image.
(a)RGB Image (b)Y Component (c)U Component (d) V
Component
Fig.1 Fig.1 Fig.1 Fig.1 RGB RGB RGB RGB Image Image Image Image Transformed Transformed Transformed Transformed into into into into YUV YUV YUV YUV Color Color Color Color Space Space Space Space
Fig.2. Fig.2. Fig.2. Fig.2. Process Process Process Process of of of of Embedding Embedding Embedding Embedding Watermark Watermark Watermark Watermark in in in in an an an an Image Image Image Image
% % % % $OJRULWKP $OJRULWKP $OJRULWKP $OJRULWKP IRU IRU IRU IRU (PEHGGLQJ (PEHGGLQJ (PEHGGLQJ (PEHGGLQJ :DWHUPDUN :DWHUPDUN :DWHUPDUN :DWHUPDUN
In the proposed method, Iull band Irequency is
selected to hide watermark in al the three channel oI YUV
color space. The embedding Iactor or control Iactor is used
to control the energy oI the watermark and it is denoted as
and its value range Irom 0 to 1 (0__1). The
algorithm Ior hiding inIormation is given below:
Step Step Step Step 1 111 RGB components oI color image A is converted
into YUV color spaces using (3)
y (0.275*R)(0.504*G)(0.098*B)16
v(0.439*R)-(0.368*G)-(0.071*B)128
u(0.148*R)-(0.291*G)(0.439*B)128
Step Step Step Step 2222 Discrete wavelet transIormation technique is applied
to YUV matrices to decompose it into diIIerent range oI
Irequency bands. For each level oI decomposition, input
image matrix Y is transIormed into Iour bandoI
Irequency named LLY,LHY,HLY,HHY(5). Similarly U
and V image matrices are also transIormed into Iour band
oI Irequencies using (5)
LL,LH,HL,HH]DWT(Y,U,V) LL,LH,HL,HH]DWT(Y,U,V) LL,LH,HL,HH]DWT(Y,U,V) LL,LH,HL,HH]DWT(Y,U,V) (5) (5) (5) (5)
Step Step Step Step 3 333 SVD technique is applied on each band oI YUV
color spaces oI cover data as well as on watermark using
(6).
U U U U SSSS V]SVD( V]SVD( V]SVD( V]SVD(%DQG %DQG %DQG %DQG))))
U U U U` ``` S SSS```` VVVV````]SVD(W) ]SVD(W) ]SVD(W) ]SVD(W) (6)
Let 8 9 be orthogonal matrices, 6 is a diagonal
matrix. The diagonal matrix 6 is used to embed watermark
in its diagonal elements using (7). Here Band represents
any one oI the Irequency band suchas LL, LH, HL and HH.
SSSS`` `` `` ``S+ S+ S+ S+ssss```` (7) (7) (7) (7)
The watermark S` is embedded into the non zero
elements oI the diagonal matrix 6 to obtain the
watermarked
Diagonal matrix S``.
Step Step Step Step 4444 Inverse SVD is applied on watermarked S`` matrix
to get the modiIied Image Band using (8)
%DQG %DQG %DQG %DQG```` UUUU ` ``` SSSS`` `` `` `` `V] `V] `V] `V] (8) (8) (8) (8)
Step Step Step Step 5555 Inverse transIormation Technique is applied to get
the watermarked image matrices oI Y,U,V using (9)
Y Y Y Y````,U ,U ,U ,U` ```,V ,V ,V ,V` ```]DWT(LL ]DWT(LL ]DWT(LL ]DWT(LL````,LH ,LH ,LH ,LH` ```,HL ,HL ,HL ,HL` ```HH HH HH HH````) ))) (9) (9) (9) (9)
Step Step Step Step 6666 YUV color spaces are converted into R`G`B` color
spaces by (10)
AAAA````YUV(R YUV(R YUV(R YUV(R````G GGG` ```B BBB````) ))) (10) (10) (10) (10)
Where A` is an watermarked Image
& & & & $OJRULWKP $OJRULWKP $OJRULWKP $OJRULWKP IRU IRU IRU IRU ([WUDFWLQJ ([WUDFWLQJ ([WUDFWLQJ ([WUDFWLQJ :DWHUPDUN :DWHUPDUN :DWHUPDUN :DWHUPDUN
During Extraction process, the RGB components oI
the watermarked color image are converted into YUV color
spaces which in turn can be converted into Irequency
coeIIicients oI Iour bands. Each band oI Irequency is SVD
transIormed to extract watermark Irom the diagonal
elements. The block diagram oI watermark extraction
procedure is shown in Fig.3.
Fig.3. Fig.3. Fig.3. Fig.3. Process Process Process Process of of of of Extracting Extracting Extracting Extracting Watermark Watermark Watermark Watermark from from from froman an an an Image Image Image Image
Step Step Step Step 1111 Let $ be a watermarked image matrix, apply
transIormation technique to convert RGB color space
into YUV color space using (11)
YYYY````U UUU````V VVV````RGB(A RGB(A RGB(A RGB(A````) ))) (11)
Step Step Step Step 2222 Wavelet ransIormation Technique is applied
to YUV matrices to decompose it into diIIerent range
oI Irequency bands in (12).
LL LL LL LL````,LH ,LH ,LH ,LH````,HL ,HL ,HL ,HL` ```HH HH HH HH` ```]DWT(Y ]DWT(Y ]DWT(Y ]DWT(Y` ```U UUU` ```V VVV````) ))) (12)
Step Step Step Step 3333 SVD transIormation is applied on Iull band oI
wavelet transIormed YUV matrices
U U U U S SSS V]SVD( V]SVD( V]SVD( V]SVD(%DQG %DQG %DQG %DQG````) ))) (13 (13 (13 (13)
Where %DQG %DQG %DQG %DQG```` means one oI wavelet transIormed
Irequency bands oI YUV matrices
Step Step Step Step 4444 Watermark is extracted using (14)
SSSS` ```(S (S (S (S-S)/ -S)/ -S)/ -S)/ (14)
Step Step Step Step 5555 Apply inverse SVD on retrieved watermark
using unitary matrices U and V
W`U S` V
Step Step Step Step 6666 The similarity oI original watermark and
extracted watermark is measured using (15).
where W and We are original and extracted
watermark.
V. V. V. V. PPPPERFORMANCE ERFORMANCE ERFORMANCE ERFORMANCE AAAANALYSIS NALYSIS NALYSIS NALYSIS
The perIormance oI algorithm DSFW is analyzed
through the results which are obtained by embedding
large sized watermark in all the three channels oI
cover image in YUV space. The quality oI the
watermarked image can be measured either
subjectively or objectively and it is observed that
both subjective and objective quality oI watermarked
image is good. The PSNR is the objective criteria
used to measure the quality oI the watermarked image.
Similarly the quality oI the extracted watermark is
measured by comparing it with the original watermark
and is called similarity measure. The peak signal to
noise ratio and normalized correlation are obtained
using (15) and (16) respectively.
host image and the watermarked image respectively
and parameters PQ speciIy row and column size oI
images respectively.
In the DSFW the boat image oI size 256 X 256 is
taken as watermark whereas the lena image oI size
512 X 512 is taken as cover image and watermark is
hidden in Iull band oI Y, U and V channels oI cover
data. The original image, watermark image and
watermarked is shown in Fig.4. The quality oI the
watermarked image is measured through PSNR and
calculated values are tabulated in Table.1. Similarly
the measured normalized correlation values are
tabulated in Table.2
Fig.4 (c) shows that the watermarked image
quality is not degraded and also the watermark is
imperceptible, so the proposed algorithm is
characterized as imperceptible algorithm. The
proposed algorithm is tested in YUV channels. The
extracted watermark Irom three channels (YUV)
under normal condition without any attack is shown
Fig 5. Which shows that watermark could be
embedded in any one oI the channel iI computer
network is highly secured. But normally the
communication networks are not secured and also
noisy in nature. It is required to identiIy a good
channel to embed watermark such that it should
withstand maximum possible attacks which may be
intentional or unintentional. The extracted watermark
aIter salt and pepper noise, Gaussian noise, cropping
and histogram equalization attacks are shown in Fig.6,
Fig.7, Fig. 8 and Fig.9 respectively. Table 1 shows the
quality oI the watermarked image through peak signal
to noise ratio.
Fig.5 Fig.5 Fig.5 Fig.5 Extracted Extracted Extracted Extracted Watermark Watermark Watermark Watermark from from from fromYUV YUV YUV YUV Channel Channel Channel Channel without without without without attack attack attack attack
The calculated value oI PSNR is above 36 decibels in
Y channel and 33decibals in U channel and 30 in V
channel respectively. The PSNR value shows that
the quality oI the watermarked image is good and not
degraded much when inIormation is added in the Y
channel than U and V channel.
Table.1 Table.1 Table.1 Table.1
PSNR PSNR PSNR PSNRvalues values values values of of of of Watermarked Watermarked Watermarked Watermarked image image image image Under Under Under Under normal normal normal normal
condition condition condition condition
Table.2 Table.2 Table.2 Table.2
Similarity Similarity Similarity Similarity Measure Measure Measure Measure of of of of Extracted Extracted Extracted Extracted and and and and Original Original Original Original
Watermark Watermark Watermark Watermark (NC) (NC) (NC) (NC)
Normalized correlation oI extracted watermark is
measured Ior non-tampered image and tabulated in
Table.2.It shows that the quality oI the extracted
watermark Irom U channel is good as its NC is
0.9994 compared to calculated NC oI Y and V
channels. Thus the algorithm shows that the
watermark can be hidden in U channel than Y and V.
The robustness oI DSFW algorithm is tested
against various attacks such as addition oI salt and
pepper noise, Gaussian noise, cropping and histogram
equalization. The original and extracted watermark
aIter attacks Irom Y U and V channels are shown in
Fig.6-9. The calculated values oI normalized
correlation coeIIicients are tabulated in Table 3 and
Table 4.As per the observation the quality oI both
watermarked image and extracted watermark quality
is high Ior additive noise attack when watermark is
hidden into Y channel compared to U and V channel.
For cropping attack the quality oI the extracted
watermark Irom V channel is better the quality oI Y
and U channel. The DSFW algorithm is robust to
cropping attack as watermark is hidden into Iull band
oI Irequency oI cover image.
Fig.6 Fig.6 Fig.6 Fig.6 Extracted Extracted Extracted Extracted watermark watermark watermark watermark after after after after salt salt salt salt and and and and pepper pepper pepper pepper noise noise noise noise
attack attack attack attack from from from fromY, Y, Y, Y, UUUU and and and and VVVV channels channels channels channels (Variance (Variance (Variance (Variance 0.001) 0.001) 0.001) 0.001)
Fig.7 Fig.7 Fig.7 Fig.7 Extracted Extracted Extracted Extracted watermark watermark watermark watermark after after after after Gaussian Gaussian Gaussian Gaussian noise noise noise noise attack attack attack attack
from from from fromY, Y, Y, Y, UUUUand and and and VVVV channel channel channel channel (Variance (Variance (Variance (Variance 0.01) 0.01) 0.01) 0.01)
Fig.8 Fig.8 Fig.8 Fig.8 Extracted Extracted Extracted Extracted watermark watermark watermark watermark after after after after cropping cropping cropping cropping attack attack attack attack from from from fromY, Y, Y, Y, UUUU
and and and and VVVV channel channel channel channel
Fig.9 Fig.9 Fig.9 Fig.9 Extracted Extracted Extracted Extracted watermark watermark watermark watermark after after after after Histogram Histogram Histogram HistogramEqualization Equalization Equalization Equalization
attack attack attack attack from from from fromY, Y, Y, Y, UUUU and and and and VVVVchannel channel channel channel
Similarity Measure oI Extracted and Original Watermark
aIter noise addition attack
Table Table Table Table 3333
Similarity Measure oI Extracted and Original atermark
aIter cropping and HISTOGRAM EQUALIZATION attack
Table Table Table Table 4 444
VI. VI. VI. VI. C CCCONCLUSION ONCLUSION ONCLUSION ONCLUSION AND AND AND AND FFFFUTURE UTURE UTURE UTURE WWWWORK ORK ORK ORK
DWT-SVD combined Iull band robust watermarking
technique DSFW Ior color images in YUV color
space is discussed in this paper. In this algorithm the
multi-resolution capability oI wavelet transIormation
technique is combined with singular value
decomposition technique to make it robust. Since the
watermark is hidden in Iull band oI YUV channel
algorithm DSFW is highly robust against common
attacks such as addition oI noise, histogram
equalization and cropping, which are considered as
one oI the serious attacks. The quality oI the
extracted watermark shows that the new proposed
algorithm is robust and also the quality oI cover
image is not degraded. In Iuture, DSFW algorithm
can be extended
REFERENCES
|1| F. Hartung and M. Kutter, "Multimedia Watermarking
Techniques," in Proc. oI the IEEE, vol. 87, no. 7, pp. 1079-1107,
July 1999.
|2| V. Potdar, et al "A Survey oI Digital Image Watermarking
Techniques", in Proc.oI the EEE International ConIerence on
Industrial InIormatics, Australia Perth, pp. 709-716, 2005.
|3| Liu Quan, AI Qingsong 'A combination oI DCT based and
SVD based watermarking, ICSP proceedings oI IEEE International
conIerence on signal processing, pp. 873-876, 2004.
|4| Feng Liu, et al. 'A Watermarking Algorithm Ior Digital Image
Based on DCT and SVD Congress on Image and Signal
Processing, 2008.
|5| Emad E. Abdallah, et al. 'A robust block-based image
watermarking scheme using Iast Hadamard transIorm and singular
value decomposition proceedings oI The 18th International
ConIerence on Pattern Recognition, pp:673 - 676 , 2006.
|6| Tang Xianghong, Yang Lianjie, Yue Hengli, Yin Zhongke, 'A
Watermarking Algorithm Based on the SVD and Hadamard
TransIorm, Proceedings oI International ConIerence on
Communications, Circuits and Systems,Volume 2, pp. 874-877 ,
27-30 May 2005.
|7| Ali Al-Haj, 'A Hybrid Digital Image Watermarking
Algorithm, 4th International ConIerence on Innovations in
InIormation Technology. pp: 690 - 694 Nov. 2007.
|8| Liu Liang and Sun Qi 'A new SVD-DWT composite
watermarking,ICSP proceedings oI IEEE International conIerence
on signal processing .2006
|9| Jung-Chun Liu, Chu-Hsing Lin, and Li-Ching Kuo A Robust
Iull band image watermarking scheme Proceedings on
IEEE .2006
|10| Qiang Li, et al, 'Adaptive DWT-SVD Domain Image
Watermarking Using Human Visual Model proceedings oI 9th
international conIerence on advanced communication Technology,
Volume 3, pp:1947 - 1951, Feb.2007.
|11| H. Andrews and C. Patterson, "Singular Value
decompositions and Digital Image Processing," IEEE Trans. on
Acoustics, Speech ,and Signal Processing, vol. 24, no. 1, pp. 26-53,
Feb. 1976.
|12| Ruth Buse Dili, Elijah Mwangi, 'An Image Watermarking
method based on the singular value transIormation and the wavelet
transIormation 'Proceedings on IEEE. 2007
|13| Cheng-qun Yin, Li Li, An-qiang Lv and Li Qu, 'Color Image
Watermarking Algorithm Based on DWT-SVD Proceedings oI the
IEEE International ConIerence on Automation and Logistics,
Page(s):2607 2611, August 18 - 21, 2007,Aug. 2007
|14| Ali Al-Haj, et al 'Non-Invertible Copyright Protection oI
Digital Images Using DWT and SVD Proceedings oI
International ConIerence on Digital InIormation anagement,
Volume 1, 28-31 Page(s):448 - 453 2007.
|15| Ke-Ieng he, et al , 'Watermarking Ior images using the HVS
and SVD in the wavelet domain Proceedings oI IEEE
International ConIerence on Mechatronics and Automation,
pp.2352- 2356, 2006.
You might also like
- A Semi-Blind Reference Video Watermarking Using: Satyanarayana Murty. P K. Venkatesh Rajesh Kumar. PDocument11 pagesA Semi-Blind Reference Video Watermarking Using: Satyanarayana Murty. P K. Venkatesh Rajesh Kumar. PMaharani MeidyNo ratings yet
- Anjaneyulu Base PaperDocument28 pagesAnjaneyulu Base PaperRevanthkumarNo ratings yet
- Digital Watermarking Thesis PDFDocument5 pagesDigital Watermarking Thesis PDFCustomizedPaperUK100% (2)
- A Block Based Novel Digital Video Watermarking Scheme Using DCTDocument11 pagesA Block Based Novel Digital Video Watermarking Scheme Using DCTInternational Organization of Scientific Research (IOSR)No ratings yet
- Study of 5 Level DWT and Comparative Performance Analysis of Digital Video Watermarking Techniques Using 3-L-DWT and 5-L-DWTDocument7 pagesStudy of 5 Level DWT and Comparative Performance Analysis of Digital Video Watermarking Techniques Using 3-L-DWT and 5-L-DWTerpublicationNo ratings yet
- Towards Optimal Copyright Protection Using Neural Networks Based Digital Image WatermarkingDocument7 pagesTowards Optimal Copyright Protection Using Neural Networks Based Digital Image WatermarkingEditor IJRITCCNo ratings yet
- Double Coding Mechanism For Robust Audio Data Hiding in VideosDocument5 pagesDouble Coding Mechanism For Robust Audio Data Hiding in Videosrohit.rotegaoNo ratings yet
- Cts Image Watermarking Based On DWT and Des: Issue 03, Volume 4 (March 2017)Document8 pagesCts Image Watermarking Based On DWT and Des: Issue 03, Volume 4 (March 2017)sparsh jainNo ratings yet
- Digital Watermarking TrendsDocument7 pagesDigital Watermarking TrendsWhite Globe Publications (IJORCS)No ratings yet
- Digital Image Watermarking Using 3 Level Discrete Wavelet TransformDocument5 pagesDigital Image Watermarking Using 3 Level Discrete Wavelet Transformtjdandin1No ratings yet
- Extended Performance of Digital Video Watermarking Using Hybrid Wavelet Transform With Haar, Cosine, Kekre, Walsh, Slant and Sine TransformsDocument6 pagesExtended Performance of Digital Video Watermarking Using Hybrid Wavelet Transform With Haar, Cosine, Kekre, Walsh, Slant and Sine TransformsekaNo ratings yet
- Efficient HEVC Steganography Approach Based On AudDocument36 pagesEfficient HEVC Steganography Approach Based On AudelmannaiNo ratings yet
- Dual Image Watermarking Scheme Based On DWT-SVD: D. M. Gaikwad A. R. KarwankarDocument6 pagesDual Image Watermarking Scheme Based On DWT-SVD: D. M. Gaikwad A. R. Karwankarrahul sharmaNo ratings yet
- Rupesh SynoDocument8 pagesRupesh SynoAshokupadhye1955No ratings yet
- DWT-SVD and DCT Based Robust and Blind: Durgesh Singh Sanjay K. SinghDocument24 pagesDWT-SVD and DCT Based Robust and Blind: Durgesh Singh Sanjay K. SinghWalid El-ShafaiNo ratings yet
- A Survey: Digital Image Watermarking TechniquesDocument14 pagesA Survey: Digital Image Watermarking Techniquesvidhyasree123No ratings yet
- Image Watermarking Using Diffie Hellman Key ExchangeDocument8 pagesImage Watermarking Using Diffie Hellman Key ExchangeAnurag TiwariNo ratings yet
- DCT Based Video Watermarking in MATLAB PDFDocument11 pagesDCT Based Video Watermarking in MATLAB PDFKamlesh DahiyaNo ratings yet
- 7.1 Classification of Digital Watermarking TechniquesDocument30 pages7.1 Classification of Digital Watermarking TechniquesLong Đào HảiNo ratings yet
- Real Time Watermarking For Professional PhotographyDocument7 pagesReal Time Watermarking For Professional PhotographyInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Secure Dissemination and Protection of Multispectral Images Using Crypto-Watermarking 2015Document7 pagesSecure Dissemination and Protection of Multispectral Images Using Crypto-Watermarking 2015Archana TiwariNo ratings yet
- International Journal of Engineering Research and Development (IJERD)Document6 pagesInternational Journal of Engineering Research and Development (IJERD)IJERDNo ratings yet
- Digital Watermarking Using Machine LearningDocument7 pagesDigital Watermarking Using Machine LearningIJRASETPublicationsNo ratings yet
- An Imperceptible Blind Image Watermarking Scheme For Image Authentication Using DNA Encoding and Multi-Resolution Wavelet DecompositionDocument8 pagesAn Imperceptible Blind Image Watermarking Scheme For Image Authentication Using DNA Encoding and Multi-Resolution Wavelet DecompositionInternational Journal of Engineering Inventions (IJEI)No ratings yet
- Digital Watermarking Based On DWT (Discrete Wavelet Transform)Document22 pagesDigital Watermarking Based On DWT (Discrete Wavelet Transform)VasuNo ratings yet
- Digital WatermarkingDocument6 pagesDigital WatermarkingMa SeenivasanNo ratings yet
- Thesis Video WatermarkingDocument6 pagesThesis Video WatermarkingPayToWriteAPaperLubbock100% (4)
- Performance Evaluation of RDWT-SVD and DWT-SVD Watermarking SchemesDocument10 pagesPerformance Evaluation of RDWT-SVD and DWT-SVD Watermarking SchemesNaga Raju GNo ratings yet
- Digital Watermarking: o o o oDocument8 pagesDigital Watermarking: o o o oselvadpm5No ratings yet
- Survey On Digital Video Watermarking Techniques, Attacks and ApplicationsDocument6 pagesSurvey On Digital Video Watermarking Techniques, Attacks and ApplicationsEditor IJTSRDNo ratings yet
- A Review On Digital Image Watermarking Using 3-Level Discrete Wavelet TransformDocument7 pagesA Review On Digital Image Watermarking Using 3-Level Discrete Wavelet TransformShahid RanaNo ratings yet
- Ijset 2014 803Document4 pagesIjset 2014 803Editorijset IjsetNo ratings yet
- 18bce2392 Kajal Sharma 18bce2397 Medhavi Singh: J-Component Information Security Analysis and Audit Final ReportDocument12 pages18bce2392 Kajal Sharma 18bce2397 Medhavi Singh: J-Component Information Security Analysis and Audit Final Reportsparsh jainNo ratings yet
- Watermarking Thesis PDFDocument6 pagesWatermarking Thesis PDFCanYouWriteMyPaperForMeSingapore100% (1)
- Mini Project PPT Review-2Document46 pagesMini Project PPT Review-2198W1A05D7-SEC-C CHANDRAPATLA DEDEEPYANo ratings yet
- Thesis WatermarkingDocument7 pagesThesis Watermarkingsheilaguyfargo100% (2)
- Thesis On Digital WatermarkingDocument8 pagesThesis On Digital Watermarkingstephaniejohnsonsyracuse100% (2)
- 10.1007@978 3 319 23950 77 PDFDocument30 pages10.1007@978 3 319 23950 77 PDFDinh Hoang OanhNo ratings yet
- Digital Watermarking: First A. Author, Second B. Author, JR., and Third C. Author, Member, IEEEDocument2 pagesDigital Watermarking: First A. Author, Second B. Author, JR., and Third C. Author, Member, IEEENishanthShanmugamNo ratings yet
- Digital Water MarkingDocument7 pagesDigital Water Marking4ndr01d0n3No ratings yet
- Digital Watermarking: Ankush K RDocument34 pagesDigital Watermarking: Ankush K RJaya AgrawalNo ratings yet
- Implementation of Adaptive Digital Image Watermarking Technique in Discrete Wavelet Transform For Copyright ProtectionDocument6 pagesImplementation of Adaptive Digital Image Watermarking Technique in Discrete Wavelet Transform For Copyright ProtectionEditor IJRITCCNo ratings yet
- Hurrah 2017Document5 pagesHurrah 2017ناصرھرەNo ratings yet
- A Robust Non-Blind Algorithm For Watermarking Color Images Using Multi-Resolution Wavelet DecompositionDocument7 pagesA Robust Non-Blind Algorithm For Watermarking Color Images Using Multi-Resolution Wavelet Decompositionismailhussain22No ratings yet
- Digital Watermarking: A TutorialDocument12 pagesDigital Watermarking: A TutorialJiawei LinNo ratings yet
- Tai Lieu FFTDocument12 pagesTai Lieu FFTviti_93No ratings yet
- Data Hiding in Audio Signals: Presented By-Jakera Parvin Choudhury HT NO:08H81A0417 Internal Guide - Arshiya NooriDocument19 pagesData Hiding in Audio Signals: Presented By-Jakera Parvin Choudhury HT NO:08H81A0417 Internal Guide - Arshiya NooriBharath Kumar PatruduNo ratings yet
- HH 3Document23 pagesHH 3hmm raniaNo ratings yet
- An Adaptive Watermarking Scheme For E-Government Document ImagesDocument19 pagesAn Adaptive Watermarking Scheme For E-Government Document ImagesAarthi JanakiramanNo ratings yet
- Digital Signal Processing: Lina Zhang, Deyun WeiDocument12 pagesDigital Signal Processing: Lina Zhang, Deyun WeiGuillermo Botella JuanNo ratings yet
- Thesis Report On WatermarkingDocument5 pagesThesis Report On Watermarkingafktgoaaeynepd100% (2)
- DCT-DWT Based Digital Watermarking and Extraction Using Neural NetworksDocument5 pagesDCT-DWT Based Digital Watermarking and Extraction Using Neural Networkshmm raniaNo ratings yet
- Ijcet: International Journal of Computer Engineering & Technology (Ijcet)Document12 pagesIjcet: International Journal of Computer Engineering & Technology (Ijcet)IAEME PublicationNo ratings yet
- Digital Watermarking For Big DataDocument15 pagesDigital Watermarking For Big DataArun NathNo ratings yet
- A Novel Robust Crypto Watermarking Scheme Based On Hybrid TransformersDocument10 pagesA Novel Robust Crypto Watermarking Scheme Based On Hybrid TransformersSmit PatelNo ratings yet
- A New Steganography Algorithm Based On Video Sparse RepresentationDocument26 pagesA New Steganography Algorithm Based On Video Sparse RepresentationesrNo ratings yet
- Digital Water MarkingDocument6 pagesDigital Water Markingsiri831No ratings yet
- 3 108-3 PDFDocument8 pages3 108-3 PDFSabhya SharmaNo ratings yet
- Ijaiem 2014 06 04 1Document6 pagesIjaiem 2014 06 04 1International Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Introduction to Multimedia Communications: Applications, Middleware, NetworkingFrom EverandIntroduction to Multimedia Communications: Applications, Middleware, NetworkingNo ratings yet
- SGC Lottery Post ShuffleDocument2 pagesSGC Lottery Post Shuffleamit_saxena_10No ratings yet
- Rte Lottery Post ShuffleDocument5 pagesRte Lottery Post Shuffleamit_saxena_10No ratings yet
- Wa0002.Document21 pagesWa0002.amit_saxena_10No ratings yet
- Category 3 Lottery Post ShuffleDocument1 pageCategory 3 Lottery Post Shuffleamit_saxena_10No ratings yet
- Category 5 Lottery Post ShuffleDocument11 pagesCategory 5 Lottery Post Shuffleamit_saxena_10No ratings yet
- ST Lottery Post ShuffleDocument1 pageST Lottery Post Shuffleamit_saxena_10No ratings yet
- Service Category 4 Lottery Result: School Name: KV BANGRASIA Academic Year: 2020-2021 Region: BHOPAL STD: 1Document1 pageService Category 4 Lottery Result: School Name: KV BANGRASIA Academic Year: 2020-2021 Region: BHOPAL STD: 1amit_saxena_10No ratings yet
- Result Analysis CLASS XII & (CLASS XA and Class X B)Document24 pagesResult Analysis CLASS XII & (CLASS XA and Class X B)amit_saxena_10No ratings yet
- Differently Abledgeneral Lottery Result: School Name: KV Bangrasia Academic Year: 2020-2021 Region: Bhopal STD: 1Document1 pageDifferently Abledgeneral Lottery Result: School Name: KV Bangrasia Academic Year: 2020-2021 Region: Bhopal STD: 1amit_saxena_10No ratings yet
- SC Lottery Post ShuffleDocument3 pagesSC Lottery Post Shuffleamit_saxena_10No ratings yet
- Amit Saxena - Diet ChartDocument3 pagesAmit Saxena - Diet Chartamit_saxena_10No ratings yet
- OBC Lottery Post ShuffleDocument6 pagesOBC Lottery Post Shuffleamit_saxena_10No ratings yet
- Category 1 Lottery Post ShuffleDocument2 pagesCategory 1 Lottery Post Shuffleamit_saxena_10No ratings yet
- Category 2 Lottery Post ShuffleDocument1 pageCategory 2 Lottery Post Shuffleamit_saxena_10No ratings yet
- 10406-1R Main48 RotatedDocument1 page10406-1R Main48 Rotatedamit_saxena_10No ratings yet
- Cost Comparison of RCC and PT Beam NewDocument1 pageCost Comparison of RCC and PT Beam Newamit_saxena_10No ratings yet
- DROP & CST Reinforcment CalculationDocument3 pagesDROP & CST Reinforcment Calculationamit_saxena_10No ratings yet
- Statement of Voluntary Contribution Under National Pension System (NPS)Document1 pageStatement of Voluntary Contribution Under National Pension System (NPS)amit_saxena_10No ratings yet
- Marriage Garden Community Hall (STRDocument1 pageMarriage Garden Community Hall (STRamit_saxena_10No ratings yet
- Bridge Sressing FormentDocument2 pagesBridge Sressing Formentamit_saxena_10No ratings yet
- Two Way Slab Load Distribution On BeamDocument4 pagesTwo Way Slab Load Distribution On Beamamit_saxena_10No ratings yet
- Homeloancertificate 26514247Document1 pageHomeloancertificate 26514247amit_saxena_10No ratings yet
- Tan PierwellDocument64 pagesTan Pierwellamit_saxena_10No ratings yet
- Amit Home LoanDocument2 pagesAmit Home Loanamit_saxena_10No ratings yet
- SPAN Architects MR Anand Maroo 9826726002 (Design@spanarchitects - In) 220, Telephone Nagar, IndoreDocument2 pagesSPAN Architects MR Anand Maroo 9826726002 (Design@spanarchitects - In) 220, Telephone Nagar, Indoreamit_saxena_10No ratings yet
- p4 & P6-Pier Well & Well CapDocument74 pagesp4 & P6-Pier Well & Well Capamit_saxena_10No ratings yet
- New Company ProfileDocument8 pagesNew Company Profileamit_saxena_10No ratings yet
- 15.8 M PT BeamDocument4 pages15.8 M PT Beamamit_saxena_10No ratings yet
- G A Bhilare Consultants: 5. A. R. Chaudhari Architect, Interior DesignerDocument6 pagesG A Bhilare Consultants: 5. A. R. Chaudhari Architect, Interior Designeramit_saxena_10No ratings yet
- C Abutment Well 2Document138 pagesC Abutment Well 2amit_saxena_10No ratings yet
- 450i User ManualDocument54 pages450i User ManualThượng Lê Văn0% (2)
- Richards Laura - The Golden WindowsDocument147 pagesRichards Laura - The Golden Windowsmars3942No ratings yet
- Algorithmique Et Programmation en C: Cours Avec 200 Exercices CorrigésDocument298 pagesAlgorithmique Et Programmation en C: Cours Avec 200 Exercices CorrigésSerges KeouNo ratings yet
- Weekly Learning PlanDocument2 pagesWeekly Learning PlanJunrick DalaguitNo ratings yet
- Efs151 Parts ManualDocument78 pagesEfs151 Parts ManualRafael VanegasNo ratings yet
- Year 9 - Justrice System Civil LawDocument12 pagesYear 9 - Justrice System Civil Lawapi-301001591No ratings yet
- Gardner Denver PZ-11revF3Document66 pagesGardner Denver PZ-11revF3Luciano GarridoNo ratings yet
- Dry Canyon Artillery RangeDocument133 pagesDry Canyon Artillery RangeCAP History LibraryNo ratings yet
- Brochure Ref 670Document4 pagesBrochure Ref 670veerabossNo ratings yet
- Final ExamSOMFinal 2016 FinalDocument11 pagesFinal ExamSOMFinal 2016 Finalkhalil alhatabNo ratings yet
- Engineering Notation 1. 2. 3. 4. 5.: T Solution:fDocument2 pagesEngineering Notation 1. 2. 3. 4. 5.: T Solution:fJeannie ReguyaNo ratings yet
- Elastic Modulus SFRCDocument9 pagesElastic Modulus SFRCRatul ChopraNo ratings yet
- 21st Bomber Command Tactical Mission Report 178, OcrDocument49 pages21st Bomber Command Tactical Mission Report 178, OcrJapanAirRaidsNo ratings yet
- Allan ToddDocument28 pagesAllan ToddBilly SorianoNo ratings yet
- Epidemiologi DialipidemiaDocument5 pagesEpidemiologi DialipidemianurfitrizuhurhurNo ratings yet
- Proceedings of SpieDocument7 pagesProceedings of SpieNintoku82No ratings yet
- CHAPTER 3 Social Responsibility and EthicsDocument54 pagesCHAPTER 3 Social Responsibility and EthicsSantiya Subramaniam100% (4)
- Course Specifications: Fire Investigation and Failure Analysis (E901313)Document2 pagesCourse Specifications: Fire Investigation and Failure Analysis (E901313)danateoNo ratings yet
- Environmental Auditing For Building Construction: Energy and Air Pollution Indices For Building MaterialsDocument8 pagesEnvironmental Auditing For Building Construction: Energy and Air Pollution Indices For Building MaterialsAhmad Zubair Hj YahayaNo ratings yet
- Anaphylaxis Wallchart 2022Document1 pageAnaphylaxis Wallchart 2022Aymane El KandoussiNo ratings yet
- Building New Boxes WorkbookDocument8 pagesBuilding New Boxes Workbookakhileshkm786No ratings yet
- Prachi AgarwalDocument1 pagePrachi AgarwalAnees ReddyNo ratings yet
- TAB Procedures From An Engineering FirmDocument18 pagesTAB Procedures From An Engineering Firmtestuser180No ratings yet
- Section 8 Illustrations and Parts List: Sullair CorporationDocument1 pageSection 8 Illustrations and Parts List: Sullair CorporationBisma MasoodNo ratings yet
- SCDT0315 PDFDocument80 pagesSCDT0315 PDFGCMediaNo ratings yet
- Continue: Rudolf Bultmann Theology of The New Testament PDFDocument3 pagesContinue: Rudolf Bultmann Theology of The New Testament PDFpishoi gerges0% (1)
- CLAT 2014 Previous Year Question Paper Answer KeyDocument41 pagesCLAT 2014 Previous Year Question Paper Answer Keyakhil SrinadhuNo ratings yet
- QA/QC Checklist - Installation of MDB Panel BoardsDocument6 pagesQA/QC Checklist - Installation of MDB Panel Boardsehtesham100% (1)
- 500 Logo Design Inspirations Download #1 (E-Book)Document52 pages500 Logo Design Inspirations Download #1 (E-Book)Detak Studio DesainNo ratings yet
- PC210 8M0Document8 pagesPC210 8M0Vamshidhar Reddy KundurNo ratings yet