Professional Documents
Culture Documents
Scrutinizing Vulnerable Attacks in Cloud Infrastructure
Uploaded by
ijsret0 ratings0% found this document useful (0 votes)
11 views4 pagesSecurity in wireless network faces depreciation due to far-reaching Distributed Denial-of-Service (DDoS). DDoS attacks normally engage early on stage actions such as multistep utilization, low-frequency vulnerability scanning, and compromising notorious suspect able virtual machines as zombies, and to end with DDoS attacks in the course of the compromised zombies. We propose an Enhanced Network Intrusion Detection System using IDS Framework to overcome the DDoS attack. The proposed system builds a monitoring and control mechanism
over the scattered nodes and mitigates attack consequences using relay nodes. The attacker zone is isolated forming an attack path from the normal transmission path using the relay nodes.
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentSecurity in wireless network faces depreciation due to far-reaching Distributed Denial-of-Service (DDoS). DDoS attacks normally engage early on stage actions such as multistep utilization, low-frequency vulnerability scanning, and compromising notorious suspect able virtual machines as zombies, and to end with DDoS attacks in the course of the compromised zombies. We propose an Enhanced Network Intrusion Detection System using IDS Framework to overcome the DDoS attack. The proposed system builds a monitoring and control mechanism
over the scattered nodes and mitigates attack consequences using relay nodes. The attacker zone is isolated forming an attack path from the normal transmission path using the relay nodes.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
11 views4 pagesScrutinizing Vulnerable Attacks in Cloud Infrastructure
Uploaded by
ijsretSecurity in wireless network faces depreciation due to far-reaching Distributed Denial-of-Service (DDoS). DDoS attacks normally engage early on stage actions such as multistep utilization, low-frequency vulnerability scanning, and compromising notorious suspect able virtual machines as zombies, and to end with DDoS attacks in the course of the compromised zombies. We propose an Enhanced Network Intrusion Detection System using IDS Framework to overcome the DDoS attack. The proposed system builds a monitoring and control mechanism
over the scattered nodes and mitigates attack consequences using relay nodes. The attacker zone is isolated forming an attack path from the normal transmission path using the relay nodes.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 4
International Journal of Scientific Research Engineering & Technology (IJSRET)
Volume 2 Issue 10 pp 623-626 January 2014 www.ijsret.org ISSN 2278 0882
IJSRET @ 2014
Scrutinizing Vulnerable Attacks in Cloud Infrastructure
Mrs.Rajasri.K *, Kanimozhi.S **,Dhivya Bharathi.Dja ***,Shankari.R ****
*Senior Assistant Professor, CSE, Christ College of Engg & Tech, Pondicherry, India
** Student, CSE, Christ College of Engg & Tech, Pondicherry, India
***Student, CSE, Christ College of Engg & Tech, Pondicherry, India
****Student, CSE, Christ College of Engg & Tech, Pondicherry, India
Abstract
Security in wireless network faces depreciation due
to far-reaching Distributed Denial-of-Service (DDoS).
DDoS attacks normally engage early on stage actions
such as multistep utilization, low-frequency vulnerability
scanning, and compromising notorious suspect able
virtual machines as zombies, and to end with DDoS
attacks in the course of the compromised zombies. We
propose an Enhanced Network Intrusion Detection
System using IDS Framework to overcome the DDoS
attack. The proposed system builds a monitoring and
control mechanism
over the scattered nodes and mitigates attack
consequences using relay nodes. The attacker zone is
isolated forming an attack path from the normal
transmission path using the relay nodes.
Keywords Attack graph, Cloud computing, D.O.S,
NICE-A, Spam
1 Introduction
A mobile ad-hoc network is an autonomous network
system of routers and hosts connected by wireless links.
They can be setup somewhere without any need for
external transportation like wires or base stations. The
routers are gratis to move arbitrarily and systematize
themselves capriciously. Acronym is MANET. Each
device in the network is called an NODE.
We address the problem of packet inspection and
security towards eves dropping attack in this paper. The
past works have concentrated in port monitoring in a
centralized system where a server takes control over the
hardware and communicating links of the network. We
propose a secure relay based IDS (SR-IDS) where re-
locatable relay nodes serve the purpose. These relays are
placed based on the shortest distance by which a relay
node can cover a maximum number of nodes at its zone.
1.1 Cloud computing
Cloud computing has become the novel hum word
driven largely by advertising and service contributions
from large corporate players like Google, IBM and
Amazon. Cloud computing is the use of network .Cloud
computing is the use of computing resources (hardware
and software) that are delivered as a service over a
network. Computing resources (hardware and software)
that are delivered as a service over a network.
Fig 1.1 Working of cloud
Here are mainly three form of cloud computing:
Public Cloud: IT resources on hand as a
service and collective across multiple
organizations, managed by an external service
provider
Private Cloud: IT resources devoted to a single
organization and obtainable on demand
Hybrid Cloud: a combine of private and public
clouds manage as a single entity to expand
capacity across clouds as needed.
International Journal of Scientific Research Engineering & Technology (IJSRET)
Volume 2 Issue 10 pp 623-626 January 2014 www.ijsret.org ISSN 2278 0882
IJSRET @ 2014
Fig 1.2 Cloud computing types
1.2 Distributed Deniel-Of-Service
In computing,a denial-of-service attack (DoS attack)
or distributed denial- of-service attack (DDoS attack) is
an attempt to create a machine or network resource
engaged to its intended users. Although the means to
perform, motives for, and targets of a DoS attack can
vary, it normally consists of efforts to temporarily or
indefinitely interrupt or suspend services of
a host connected to the Internet. Perpetrators of DoS
attacks typically target sites or services hosted on high-
profile web servers such as banks, credit card payment
gateways, and even root name servers.
2 Existing System
Initially they have used to identify an intrusion in a
Centralized Network .Here the attack is only found out if
they have attacked the server. If there is attack in the
host it is never found out. The proposed structure
leverages Open Flow network encoding APIs to build a
observe and control plane over scattered programmable
virtual switches to considerability improve attack
detection and alleviate attack consequences. The system
and security evaluations reveal the competence and
effectiveness of the proposed solution. NICE is Network
Intrusion Detection and Counter measure Selection in
Virtual Network Systems, builds a graph based model in
it and a framework is been designed, which monitor and
control the entire network. It is done in three phases
PHASE 1
Deploy a lightweight mirroring-based network
intrusion detection agent (NICE-A) on every cloud
server to confine and scrutinize cloud traffic. A NICE-A
regularly scan the virtual system vulnerabilities
surrounded by a cloud server to establish Scenario
Attack Graph (SAGs), and then based on the severity of
identified vulnerability toward the mutual attack goals,
NICE will choose whether or not to set a VM in network
examination state.
PHASE 2
On one occasion, a VM enter inspection state, Deep
Packet Inspection (DPI) is applied, and/or implicit
network reconfigurations can be deploy to the inspect
VM to compose the potential attack behaviors
prominent. NICE significantly advances the current
network IDS/IPS solutions by employing programmable
virtual networking loom that allows the system to
construct a dynamic reconfigurable IDS system. By
using software switching techniques, NICE constructs a
mirroring-based traffic capture framework to minimize
the interference on users traffic compared to traditional
bump-in-the-wire IDS/IPS. The programmable virtual
networking structural design of NICE enables the cloud
to establish assessment and quarantine modes for
suspicious VMs according to their current vulnerability
state in the current SAG.
PHASE 3
Countermeasure Selection is very important method
in which it is based on two features namely, (i)Hardware
oriented: It includes the Attack analyzer and VM
profiling method. (ii)Network oriented: It includes the
Network controller, which is used to know what type of
protocol used, how much time it is been activated and
how many data transfer is been done by the protocol.
2.2 Countermeasure-Selection Algorithm
Algorithm2: Countermeasure Selection
Require: Alert; GE; V ; CM
1: Let vAlert Source node of the Alert
2.1 Alert Co-Relation Algorithm
Algorithm 1:Alert_Correlation
Require: alert ac, SAG, ACG
1: if (ac is a original alert) then
2: generate node ac in ACG
3: n1 vc 2 mapac
4: for all n2 2 parentn1 do
5: create edges (n2:alert; ac)
6: for all Si contain a do
7: if a is the last element in Si then
8: append ac to Si
9: else
10: create path Si1 fsubsetSi; a; acg
11: end if
12: end for
13: add ac to n1:alert
14: end for
15: end if
16: return S
2.2 Countermeasure Selection Algorithm
International Journal of Scientific Research Engineering & Technology (IJSRET)
Volume 2 Issue 10 pp 623-626 January 2014 www.ijsret.org ISSN 2278 0882
IJSRET @ 2014
Algorithm2: Countermeasure Selection
Require: Alert;GE; V ; CM
1: Let vAlert Source node of the Alert
2: if Distance to TargetvAlert > threshold then
3: Update ACG
4: return
5: end if
6: Let T DescendantvAlert [ vAlert
7: Set PrvAlert 1
8: Generate_Risk_Problem(T)
9: Let benefitjTj; jCMj_ ;
10: for each t 2 T do
11: for each cm 2 CM do
12: if cm:conditiont then
13: Prt Prt _ 1 _ cm:effectiveness
14: Estimate_Risk_Problem(Descendantt)
15: benefitt; cm_ _Prtarget node. (7)
16: end if
17: end for
18: end for
19: Let ROIjTj; jCMj_ ;
20: for each t 2 T do
21: for each cm 2 CM do
22: ROIt; cm_ benefitt;cm_ cost:
cmintrusiveness:cm . (8)
23: end for
24: end for
25: Update SAG and Update ACG
26: return Select Optimal CMROI
2.3 DRAWBACKS IN EXISTING SYSTEM
Nice is limited to centralized architecture
VM profiling consumes additional delay.
Attackers link failures are not addressed
Data consistency levels are low.
3 Proposed System
In the proposed system we choose a relay node and
the number of active nodes. Here the relay nodes are
mainly chooses to isolate the secured and non secured
nodes and this is done based on the distance of
connecting paths between nodes. We can easily replace
or move the relay nodes. If one node is out of range, then
we can replace it by relay nodes. And by isolating secure
and non secure nodes we can avoid transferring data in
non-secured nodes. And attacks are been reduced.
Choosing a relay node depends on:
TTL of the Node
Number of active links
Mobility
Let M be the nodes mobility and L be the active links
the node serves/ served, then
Mi<Mj<Mk<..Mn such that
Mi is inversely proportional to B.
Where, B is the bandwidth operated.
For a constant throughput the number of data
transferred must be constant.
Mi*B ~= 1 +/- E
Where,
E is the error correction while the
bandwidth is adjusted.
R1, R2, Rn must satisfy the above condition to
be a re-locatable IDS relay.
Calculating the maximum transmission distance:
Pr/Pt= Ft*((B/4piR)^2)
Where,B- bandwidth of the end node
Pt- Transmitter power of the sender
Pr- Receiver power of the end node
Ft- Loss factor
R- End nodes transmission radius
Number of active connections is calculated by checking
if ,BR range of the end nodes lies within BR of the
Relay Node.
The communicating radius:
r= (BR1 + BR2 + BRn)/ BRr
BR- Broadcasting Range
Mark each r1, r2, rn such that all active nodes are taken
into account.
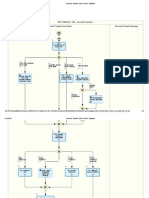
Figure 3.1 Network structure using reliable nodes
International Journal of Scientific Research Engineering & Technology (IJSRET)
Volume 2 Issue 10 pp 623-626 January 2014 www.ijsret.org ISSN 2278 0882
IJSRET @ 2014
3.1 ADVANTAGE OF PROPOSED SYSTEM
Attacker's link failures are addressed.
Secured paths are identified for data transfer.
Streamless communication is possible.
Fastware redirection can be done by the use of
relay nodes.
Low wait and hold.
4 Conclusions and Future Work
Our project is about, detecting attacks. Eves
dropping attack is isolated from the network by forming
a secure and non-secure zone using dynamic IDS relays.
The zone is differentiated using secure path and non
secure path based on maximum connectivity and the
distance at which the end node communicates at each
instance, reducing the possibility of the attackers.
Acknowledgement
This work is supported by Hewlett-Packard Labs
Innovation Research Program Grant and the Office of
Naval Research Young Investigator Program Awards.
REFERENCES
[1] Coud Sercurity Alliance, Top Threats to Cloud
Computing v1.0,
https://cloudsecurityalliance.org/topthreats/csathreats.
v1.0.pdf,Mar. 2010 .
2] H. Takabi, J.B. Joshi, and G. Ahn, Security and
Privacy
Challenges in Cloud Computing Environments, IEEE
Securityand Privacy, vol. 8, no. 6, pp. 24-31, Dec. 2010.
[3]Open vSwitch Project, http://openvswitch.org, May
2012.
[4] Z. Duan, P. Chen, F. Sanchez, Y. Dong, M.
Stephenson, and J. Barker, Detecting Spam Zombies by
Monitoring Outgoing Messages, IEEE Trans.
Dependable and Secure Computing, vol. 9, no. 2, pp.
198-210, Apr. 2012.
[5] G. Gu, P. Porras, V. Yegneswaran, M. Fong, and W.
Lee,BotHunter: Detecting Malware Infection through
IDS-drivenDialog Correlation, Proc. 16th USENIX
Security Symp. (SS 07),pp. 12:1-12:16, Aug. 2007.
[6] X. Ou, S. Govindavajhala, and A.W. Appel,
MulVAL: A Logic-Based Network Security Analyzer,
Proc. 14th USENIX Security Symp., pp. 113-128, 2005.
[7] R. Sadoddin and A. Ghorbani, Alert Correlation
Survey: Framework and Techniques, Proc. ACM Intl
Conf. Privacy, Security and Trust: Bridge the Gap
between PST Technologies and Business Services
(PST 06), pp. 37:1-37:10, 2006
[8] S. Roschke, F. Cheng, and C. Meinel, A New Alert
Correlation Algorithm Based on Attack Graph, Proc.
Fourth Intl Conf.Computational Intelligence in Security
for Information Systems,pp. 58-67, 2011.
[9] Mitre Corporation, Common Vulnerabilities and
Exposures,CVE, http://cve.mitre.org/, 2012
[10] O.Database,Open Source Vulnerability Database
(OVSDB),
http://osvdb.org/, 2012.
[11] Metasploit http://www.metasploit.com, 2012.
[12] Armitage,http://www.fastandeasyhacking.com,
2012.
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (345)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (121)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (400)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Consruction of A Direct Solar Dryer For Perishable Farm ProductsDocument9 pagesConsruction of A Direct Solar Dryer For Perishable Farm ProductsijsretNo ratings yet
- Thermal Analysis On Characterization of Polycaprolactone (PCL) - Chitosan Scaffold For Tissue EngineeringDocument5 pagesThermal Analysis On Characterization of Polycaprolactone (PCL) - Chitosan Scaffold For Tissue Engineeringijsret100% (1)
- Mechanical and Fracture Toughness Analysis of Woven Carbon Fibre Reinforced Epoxy CompositesDocument6 pagesMechanical and Fracture Toughness Analysis of Woven Carbon Fibre Reinforced Epoxy CompositesijsretNo ratings yet
- CHANGES IN ANTI OXIDANT ENZYME ACTIVITIES IN Pseudomonas Syringae PV Syringae (BACTERIAL BROWN SPOT) INFECTED SEEDLINGS OF Vigna Radiata L.Document5 pagesCHANGES IN ANTI OXIDANT ENZYME ACTIVITIES IN Pseudomonas Syringae PV Syringae (BACTERIAL BROWN SPOT) INFECTED SEEDLINGS OF Vigna Radiata L.ijsretNo ratings yet
- A Distinct Method To Find The Critical Path and Total Float Under Fuzzy EnvironmentDocument5 pagesA Distinct Method To Find The Critical Path and Total Float Under Fuzzy EnvironmentijsretNo ratings yet
- A Review On Natural Fibre Polymer CompositesDocument6 pagesA Review On Natural Fibre Polymer CompositesijsretNo ratings yet
- Blending Behavior of Cotton and Polyester Fibers On Different Spinning Systems in Relation To Physical Properties of Blended YarnsDocument11 pagesBlending Behavior of Cotton and Polyester Fibers On Different Spinning Systems in Relation To Physical Properties of Blended YarnsijsretNo ratings yet
- Comparative Study and Review On Object Oriented Design MetricsDocument4 pagesComparative Study and Review On Object Oriented Design MetricsijsretNo ratings yet
- Comparative Study and Review On Object Oriented Design MetricsDocument4 pagesComparative Study and Review On Object Oriented Design MetricsijsretNo ratings yet
- Comparison of Workpiece Geometry and Its Effects On ECAP Process by FEADocument5 pagesComparison of Workpiece Geometry and Its Effects On ECAP Process by FEAijsretNo ratings yet
- A Review On Fingerprint Detection and Recognization TechniquesDocument4 pagesA Review On Fingerprint Detection and Recognization TechniquesijsretNo ratings yet
- Echo Cancellation System in VOIP Using MATLABDocument3 pagesEcho Cancellation System in VOIP Using MATLABijsretNo ratings yet
- Content Based Image Retrieval Using Color FeatureDocument6 pagesContent Based Image Retrieval Using Color FeatureijsretNo ratings yet
- Treatment of Dairy Waste Water Using Low Cost AdsorbentsDocument2 pagesTreatment of Dairy Waste Water Using Low Cost AdsorbentsijsretNo ratings yet
- Energy Production in Public Transport Using Piezoelectric MaterialDocument4 pagesEnergy Production in Public Transport Using Piezoelectric MaterialijsretNo ratings yet
- Strategies of Effective Teaching and Learning Practical Skills in Technical and Vocational Training Programmes in NigeriaDocument6 pagesStrategies of Effective Teaching and Learning Practical Skills in Technical and Vocational Training Programmes in NigeriaijsretNo ratings yet
- A Review On Ash Agglomeration Phenomenon in Fluidised Bed Combustion BoilerDocument9 pagesA Review On Ash Agglomeration Phenomenon in Fluidised Bed Combustion BoilerijsretNo ratings yet
- Application of Modified Euler's Method in Obtaining Numerical Solution of Swing EquationDocument7 pagesApplication of Modified Euler's Method in Obtaining Numerical Solution of Swing Equationijsret100% (1)
- Compact Printed Dipole Antenna With Low Return Loss and VSWRDocument2 pagesCompact Printed Dipole Antenna With Low Return Loss and VSWRijsretNo ratings yet
- Removal of Reactive Dye From Aqueous Solutions Using Orange and Lemon Peel As Bio - AdsorbentDocument8 pagesRemoval of Reactive Dye From Aqueous Solutions Using Orange and Lemon Peel As Bio - AdsorbentijsretNo ratings yet
- E-Readiness Assessment: A Standard To Uplift Digital India ProgramDocument5 pagesE-Readiness Assessment: A Standard To Uplift Digital India ProgramijsretNo ratings yet
- Heat Transfer Behaviors in A Parabolic Trough Solar Collector Tube With Compound TechniqueDocument8 pagesHeat Transfer Behaviors in A Parabolic Trough Solar Collector Tube With Compound TechniqueijsretNo ratings yet
- Vandana New ResumeDocument1 pageVandana New ResumeVandu KNo ratings yet
- Z Remy SpaanDocument87 pagesZ Remy SpaanAlexandra AdrianaNo ratings yet
- Block Diagram and Signal Flow GraphDocument15 pagesBlock Diagram and Signal Flow GraphAngelus Vincent GuilalasNo ratings yet
- C++ SummaryDocument2 pagesC++ SummaryramakantsawantNo ratings yet
- Ling v. Microsoft Corporation - Document No. 1Document17 pagesLing v. Microsoft Corporation - Document No. 1Justia.comNo ratings yet
- LM78S40 Switching Voltage Regulator Applications: National Semiconductor Application Note 711 March 2000Document17 pagesLM78S40 Switching Voltage Regulator Applications: National Semiconductor Application Note 711 March 2000Pravin MevadaNo ratings yet
- Meraki Datasheet mt12 - en 2Document2 pagesMeraki Datasheet mt12 - en 2sipster2020No ratings yet
- (PPT) Digital Electronics 2 For StudentsDocument6 pages(PPT) Digital Electronics 2 For StudentsJONNA ACABONo ratings yet
- Peter Manning Electronic Music and CompuDocument570 pagesPeter Manning Electronic Music and CompuEmptyRoom Alejandro Bello100% (1)
- Account Statement From 13 Jun 2021 To 13 Dec 2021Document10 pagesAccount Statement From 13 Jun 2021 To 13 Dec 2021Syamprasad P BNo ratings yet
- Red Hat Enterprise Linux-6-6.8 Release Notes-En-UsDocument65 pagesRed Hat Enterprise Linux-6-6.8 Release Notes-En-Uskamel najjarNo ratings yet
- Huawei AC6805 Wireless Access Controller Datasheet - 2Document16 pagesHuawei AC6805 Wireless Access Controller Datasheet - 2irfanNo ratings yet
- Barneys Dream Cruise WalkthroughDocument3 pagesBarneys Dream Cruise WalkthroughnoelzizonNo ratings yet
- Management Information SystemDocument4 pagesManagement Information SystemPratiksha Baid DagaNo ratings yet
- Ebook PDF Using Sage 300 Erp 2017 by Chris Heaney PDFDocument41 pagesEbook PDF Using Sage 300 Erp 2017 by Chris Heaney PDFmartha.keener953100% (39)
- STBDDI3725: Product Data SheetDocument5 pagesSTBDDI3725: Product Data SheetMatheus AlvesNo ratings yet
- Python BasicsDocument43 pagesPython BasicsbokbokreonalNo ratings yet
- Accounts Payable (J60) - Process DiagramsDocument16 pagesAccounts Payable (J60) - Process Diagramsgobasha100% (1)
- BCMT Module 5 - Monitoring and Evaluating Tech4ED CentersDocument30 pagesBCMT Module 5 - Monitoring and Evaluating Tech4ED CentersCabaluay NHS0% (1)
- Proton White Paper enDocument11 pagesProton White Paper enhendri prasNo ratings yet
- Find The Coordinates of Every Square: Naval Grid CalculatorDocument2 pagesFind The Coordinates of Every Square: Naval Grid CalculatorMarie MythosNo ratings yet
- ATB Business Start-Up GuideDocument19 pagesATB Business Start-Up GuideHilkyahuNo ratings yet
- Fuzzy SetsDocument3 pagesFuzzy SetsShugal On HaiNo ratings yet
- Rockwell Automation TechED 2018 - PR26 - Endress+HauserDocument33 pagesRockwell Automation TechED 2018 - PR26 - Endress+HauserAlex Rivas100% (1)
- Design and Implementation The LLC Resonant TransformerDocument3 pagesDesign and Implementation The LLC Resonant TransformerMathe ZsoltNo ratings yet
- Science Technology and SocietyDocument18 pagesScience Technology and SocietyRowena HinumlaNo ratings yet
- Design App Themes With Theme EditorDocument4 pagesDesign App Themes With Theme Editorsenze_shin3No ratings yet
- 25+ Tricky SAP BODS Interview Questions 3Document1 page25+ Tricky SAP BODS Interview Questions 3pattabhikvNo ratings yet
- Electrical and Electronic EngineeringDocument34 pagesElectrical and Electronic EngineeringANo ratings yet
- Listening and Speaking 3 Q: Skills For Success Unit 3 Student Book Answer KeyDocument4 pagesListening and Speaking 3 Q: Skills For Success Unit 3 Student Book Answer KeyFahd AbdullahNo ratings yet