Professional Documents
Culture Documents
Name Netid Group Number: Website Link: Tutorial Details Time Spent On Assignment
Uploaded by
jkim4060 ratings0% found this document useful (0 votes)
46 views12 pagesjkim406
Original Title
INFOSYS110 2014 Deliverable 02
Copyright
© © All Rights Reserved
Available Formats
DOCX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this Documentjkim406
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
46 views12 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignment
Uploaded by
jkim406jkim406
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
You are on page 1of 12
1
INFOSYS.110 BUSINESS SYSTEMS:
DELIVERABLE 2: BUSINESS SECTION
2014
Name Juhyung Kim
NetID jkim406
Group Number: 308
Website Link: http:// infosys1102014s1group308.blogspot.co.nz/
Tutorial Details
Tutor: Day: Time:
Yvonne Hong Thursday 11am
Time Spent on
Assignment:
25 hours Word Count: 1530
2
2
WIPE OUT KEYBOARD WARRIORS
INTRODUCTION
Cyberbullying, the use of information technology to harass, threaten or humiliate other
people, has become a serious social problem. Unlike traditional bullying, anonymity and
easy access allow extended reach in terms of geography and frequency for bullies. The
repeated nature of cyberbullying results in dangerous consequences for victims; they have
low-self esteem, depression or even suicide ideation. One of the main problems is the
teengers reluctance to report to parents or an authority about occurrences which causes
supervision functionally impotent. In order to solve such problem, a mobile application
software is needed that detects any possible threat that arrives at a smartphone. It includes
an automated reporting system which enables parents or authorities to detect cyberbullying
instances and to engage in appropriate actions toward them. This can also discourage
cyberbullying at the outset with the bullies knowledge about the existence of such
application. This introduction of this mobile application will allow the use of technology to
solve the problem of cyberbullying.3. BUSINESS SECTION
3.1 Vision
Declaration of war on cyberbullying.
3.2 Industry Analysis: Mobile Application Software Industry
Industry: Mobile Application Software Industry. Mobile application software, or app that
is designed to operate on smartphones, tablets and other mobile devices.
Force: High/Low: Justification:
Buyer power: High In the application market, buyers are ultimate
consumers. Switching costs between different
developers are almost non-existent due to low
differentiation (Pappas, 2013). Such
3
3
circumstance allows a high negotiating position
for customers thus buyers have high power.
Supplier power: High The suppliers in the industry consist of platform
manufacturers such as Apple App Store, Google
Play Store and so on (Lella, 2010). Mobile
applications are mostly platform-specific which
means that an application purchased from
Google Play Store cannot operate on Apple App
Store. This leads to high supplier power.
Threat of new entrants: High Developers have relatively easy access to the
distribution channel and need relatively low
level of capital; no inventory is required and
fixed costs to remain in the marketplace is
relatively low (XiaXiao, 2013), so they have high
threat of new entrants.
Threat of substitutes: High Although major companies provide applications
on several platforms, similar content and
features are also available on web browsers on
smartphones (Feldman, 2011).
Rivalry among existing
competitors:
High 80% of application developers are small
businesses (Tiarawut, 2013); numerous and
fairly equal-sized developers illustrate
competitor balance with fierce rivarly. Also the
lack of diversity or low differentiation in the
application market increases rivarly because
customers can easily switch between
4
4
competitors.
Overall attractiveness of the industry: Highly unattractive
3.3 Customers and Thei r Needs
The target group of customers of this application is the parents of teenagers.
Despite numerous law enforcements already in action to help victimised teenagers, only
one in ten report cyberbullying to parents or authorities (11 Facts About Cyber Bullying).
Indeed, this reluctance of victims to tell others leaves supervision virtually impotent.
These unreported instances have significant mental damages for teenagers: lower self-
esteem, antisocial personality disorder and even suicide. Moreover, this psychological abuse
can cause victims to suffer mental disorder more than twice more likely than traditional
bullying (Cyberthreat: How to protect yourself from online bullying, 2011). Accordingly,
appropriate measures are required to manage the new form of bullying.
3.4 The Product and Service
This mobile application features an automated reporting system; once installed in a
students smartphone, the application screens all the messages received. Using the
database of the bullys pattern, the application detects any threatening messages and
automatically report to the students parents and relevant authority.
This eliminates the shortcomings of the current supervision system and ensures more
appropriate and timely resolution.
3.5 Suppliers and Partners
Suppliers for this business include distribution channels such as Google Play Store or Apple
App Store. These distribution channels provides the application available for consumers to
use.
Another supplier is software developers. Their works include research and development,
such as designing and testing the softwares. This allows applications usable for customers.
5
5
Partners include governments and related authorities.
The partnership with governments is crucial for providing law enforcements. The application
alone cannot achieve the desired vision and synergies are expected from this partnership.
Related authorities include police which can impose actual punishment to bullies and
protection for victims.
3.6 Strategy: Focused High Cost Strategy
Competitive Scope: Narrow market
The firm focuses its target on the narrow market of parents of teenagers. The mobile
application will be tailored to the needs of this distinct segment of worried parents.
Cost Strategy: High cost
The application requires a high level of R&D for, such as, its database for detecting function.
In order to provide an exclusive service that is sufficiently valued by parents, the firm will
pursue a high cost strategy.
The overall strategy is therefore Focused High Cost Strategy.
3.7 Value Chain Activity: Service after sale
The most important value chain activity for this business is Service after Sale
It is crucially important to enhance or maintain the value of the application. The competitive
advantage of the business derives from the applications superiority to detect threatening
messages that is valued by the parents, the focused target segment of customers. The
business needs to deploy more customer feedback system in order to capture customer
wants and needs which will also extend the product life cycle.
So as to wipe out cyberbullies, the continuous updating of the application is critical. The
database of the writing patterns of bullies must be updated in accordance with the
cyberbullies, and the aim of the updates must be strictly performance-based for customer
satisfaction.
6
6
Service value chain activity shall provide higher perceived benefits for customers of high
cost strategy; it also provides not only superior product, but also reliability.
3.8 Business Processes
3.8.1. WARRANTY MANAGEMENT PROCESS It is necessary that parents continuously perceive a high
level of benefits from the application so that the business maintains the premium price strategy. The
application must ensure so that not a single threatening message can go through the firewall, in accordance
with the business assurance. Therefore, the warranty management process is crucial.
The business must first deploy high level of feedback systems and alarms in order to obtain customer
feedbacks. If customers feel their expectations are met and satisfied with the product quality, the business
successfully blocked cyberbullies from other teenagers.
However, if the product failed to meet the promised expectations, the business must analyse why some
customers were dissatisfied. In doing so, time and precision is a crucial importance to avoid decision latency.
Once the dissatisfying factors are analysed, the business must overhaul and mend any shortcomings of the
application software at a level that the parents perceive confidence and reliability.
By keeping the business promises, customers perceive a higher level of benefits therefore it can maintain its
high cost strategy.
7
7
8
8
3.8.2. SOFTWARE UPDATE PROCESS - The precision of the censorship is the critical value for the business.
In order to maintain the high standard of the censorship, the software update process is important.
Firstly, the business must analyse the censored result to see whether the messages were appropriately
blocked and reported to parents or authorities. The business would lose its competitive advantage if the
appropriate messages were wrongly blocked. In addition, the use of bullying language may change in
accordance with the teenager trend, so accurately recognising the patterns of language is also important.
If there were no mistaken censors, the business achieved its goal. However, if there were any, the business
must maintain, repair and overhaul its database to ensure its up-to-date version of language, in accordance
with the latest trend.
The next step is to assess the updated database and ensure the application is operating expectedly.
9
9
10
10
3.9 Functionalities
3.9.1. WARRANTY MANAGEMENT PROCESS
Obtain Customer feedbacks
Mend/ overhaul dissatisfying factors
3.9.2. SOFTWARE UPDATE PROCESS
Analyse censored data
Maintenance, Repair and Overhaul of the database
3.10 Systems
3.10. 1. WARRANTY MANAGEMENT SYSTEM -
3.10. 2. DATA ANALYSI S SYSTEM -
3.10. 3. SOFTWARE UPDATES SYSTEM -
11
11
3.11. Summary Table: Value Chain to Systems
Value Chain
Activity
Processes Functionalities Specific Information
System(s)
Broad Information
System(s)
Bavarian
bergkase
fromage
queso
1. Warranty
management
process
1. Obtain customer feedbacks.
2. Mend/overhaul dissatisfactory factors
Customer complaints system
Defects repair system
Transaction processing
cheese system
Decision support system
2. Software
Updates
process
1. Analyse censored data.
2. Maintain, repair and overhaul of the
database.
Data analysis system
Database MRO system
Transaction processing
cheese system
Decision support system
12
12
CONCLUSION
In conclusion, the application software is an innovative solution to the cyberbullying problem. It provides a
solution to the problem of teenagers reluctance to report incidents by providing an automated reporting
system to enable timely actions. Although the Five Force analysis illustrates the highly unattractive market of
the mobile application software industry, Focused High Cost strategy shall target the focused consumer group
of worried parents. Differentiated attributes that are valued by customers is important; in order to obtain and
maintain the competitive advantage of the business, Service value chain activity plays a critical role. Through
Software Update process and Warranty Management process the customers gain high perceived-value to
allow premium price strategy. By the virtue of continuous updates for customer satisfaction and precise
protection system, the business declaration of war on cyberbullying shall gain victory and wipe out bullies
from the earth.
REFERENCES
11 Facts About Cyber Bullying. (n.d.). Retrieved May 20, 2014, from DoSomething:
https://www.dosomething.org/facts/11-facts-about-cyber-bullying
Cyberthreat: How to protect yourself from online bullying. (2011). Ideas and Discoveries, 76.
Feldman, B. (2011, March). The mobile app vs. mobile web debate--do you really need to pick just one?
RESPONSE, 19(6), 48.
Lella, A. (2010, September 15). comScore Reports July 2010 U.S. Mobile Subscriber Market Share. Retrieved
from comScore:
http://www.comscore.com/Insights/Press_Releases/2010/9/comScore_Reports_July_2010_US_Mobi
le_Subscriber_Market_Share
Pappas, A. (2013, July 22). Developer Economics: App market forecasts 2013-2016. Retrieved from Vision
Mobile: http://www.visionmobile.com/blog/2013/07/developer-economics-app-market-forecasts-
2013-2016/
Tiarawut, S. (2013, April 1). Mobile Technology: Opportunity for Entrepreneurship. Wireless Personal
Communications, 69(3), 1025-1031.
XiaXiao. (2013). Measuring the Mobile App Market: A Complex Network Approach. Information Technology
Journal, 12, 2090-2100.
You might also like
- App Marketing: Top Mobile App Monetization and Promotion StrategiesFrom EverandApp Marketing: Top Mobile App Monetization and Promotion StrategiesRating: 3 out of 5 stars3/5 (5)
- INFOSYS 110 Deliverable 2 2014 by Moh257Document13 pagesINFOSYS 110 Deliverable 2 2014 by Moh257zumi2020No ratings yet
- Apps Army: Get All The Support And Guidance You Need To Be A Success At Marketing Your Apps!From EverandApps Army: Get All The Support And Guidance You Need To Be A Success At Marketing Your Apps!No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentMichael CallahanNo ratings yet
- A Best Practices Guide for Comprehensive Employee Awareness ProgramsFrom EverandA Best Practices Guide for Comprehensive Employee Awareness ProgramsNo ratings yet
- Student ShopWise ApplicationDocument10 pagesStudent ShopWise ApplicationconniemaclNo ratings yet
- INFOSYS110-2014 Deliverable02 Jackson YapDocument10 pagesINFOSYS110-2014 Deliverable02 Jackson YapJacksonYapNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentAveesaaNo ratings yet
- S.110 Business Systems: Deliverable 2: Business Section 2014 Name Marthalena Heather Netid Group Number: Website Link: Tutorial Details Tutor: Day: Time: Time Spent On Assignment: Word Count: 1641Document11 pagesS.110 Business Systems: Deliverable 2: Business Section 2014 Name Marthalena Heather Netid Group Number: Website Link: Tutorial Details Tutor: Day: Time: Time Spent On Assignment: Word Count: 1641mhea048No ratings yet
- Name Netid Group Number: Website Link:: Timothy HowlettDocument10 pagesName Netid Group Number: Website Link:: Timothy HowlettTimhowlettNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument9 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmentdgai300No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument9 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmentdgai300No ratings yet
- FinlaticsDocument5 pagesFinlaticsDrake RamoorayNo ratings yet
- Tye954 Deliverable 2Document10 pagesTye954 Deliverable 2tiffanyyeNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmenttfou747No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument9 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentjonnocatoNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument11 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmentdgai300No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentSungwookHwangNo ratings yet
- INFOSYS 110 2014 Deliverable 02Document9 pagesINFOSYS 110 2014 Deliverable 02Tsib716No ratings yet
- Infosys D2 AssignmentDocument11 pagesInfosys D2 AssignmentJoanna GuNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument12 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmenttfou747No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmentmsai509No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmenttbra705No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument12 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentRyan GreavesNo ratings yet
- Finlatics 2Document6 pagesFinlatics 2Harshita SethiyaNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument11 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentStephanieZhangNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmentrie21No ratings yet
- InfoSys D2 Assignment Lbla545Document12 pagesInfoSys D2 Assignment Lbla545lbla545No ratings yet
- Name Louise Glyde Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument12 pagesName Louise Glyde Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentLouise GlydeNo ratings yet
- Finlatics 2Document3 pagesFinlatics 2Divya MNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentNkha544No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument14 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmentrwak370No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentChaeRyungJeonNo ratings yet
- Critical Issues:: Issue 1: Building Secure AppsDocument5 pagesCritical Issues:: Issue 1: Building Secure Appsarafat susanNo ratings yet
- Jonathan Michael Keen's Deliverable 2Document10 pagesJonathan Michael Keen's Deliverable 2jkee392No ratings yet
- X Lin WHFSNPRW 1650908904771Document5 pagesX Lin WHFSNPRW 1650908904771Avi ShekNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument11 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmentsfai826No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument11 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmentrzha536No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument9 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentTaniraFisher-MaramaNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument11 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmentaval651No ratings yet
- INFOSYS110 2014 Deliverable 02Document12 pagesINFOSYS110 2014 Deliverable 02Cara BoydNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument13 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentHuijiao PengNo ratings yet
- Fintech (Hyper Delivery)Document6 pagesFintech (Hyper Delivery)John CriseNo ratings yet
- Name Ryan Dion Eastham Netid Group Number: Website Link: Tutorial Details Tutor: Day: Time: Time Spent On Assignment: Word Count: 1649Document10 pagesName Ryan Dion Eastham Netid Group Number: Website Link: Tutorial Details Tutor: Day: Time: Time Spent On Assignment: Word Count: 1649reas927No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentcaylacatNo ratings yet
- Harry West D2 Hwes362Document10 pagesHarry West D2 Hwes362hwes362No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentArvin CortesNo ratings yet
- Utest Ebook Mobile Testing PDFDocument48 pagesUtest Ebook Mobile Testing PDFFrancisco AlvesNo ratings yet
- Name: Xinxiu Sun Netid: Xsun104 Group Number: 66 Website Link: Turotial DetailsDocument8 pagesName: Xinxiu Sun Netid: Xsun104 Group Number: 66 Website Link: Turotial DetailsCiuXiuNo ratings yet
- Capegemini On MobilityDocument14 pagesCapegemini On MobilityShaileshAgrawalNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument12 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentZane CrawfordNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details: Tanira Fisher-MaramaDocument9 pagesName Netid Group Number: Website Link: Tutorial Details: Tanira Fisher-MaramaTaniraFisher-MaramaNo ratings yet
- Infosys.110 Business Systems: Deliverable 2: Business Section 2014Document10 pagesInfosys.110 Business Systems: Deliverable 2: Business Section 2014Hyip413No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmenthannahmajureyNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmentjhan343No ratings yet
- Name: Xinxiu Sun Netid: Xsun104 Group Number: 66 Website Link: Word Count 1632Document8 pagesName: Xinxiu Sun Netid: Xsun104 Group Number: 66 Website Link: Word Count 1632CiuXiuNo ratings yet
- Tiru Tezazu: Ttez170 502Document12 pagesTiru Tezazu: Ttez170 502ttez170No ratings yet
- Mobile Commerce ThesisDocument7 pagesMobile Commerce ThesisHelpWritingCollegePapersSingapore100% (2)
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmentcall933No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument11 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentRileykoeNo ratings yet
- Log Cat 1658547670022Document227 pagesLog Cat 1658547670022eko setyadiNo ratings yet
- NXP Semiconductor Embedded Linux PDFDocument2 pagesNXP Semiconductor Embedded Linux PDFaashray bNo ratings yet
- Epiplex500 OverviewDocument6 pagesEpiplex500 Overviewespl_shajahanNo ratings yet
- Ddl. Paiza: EXPERIMENT-1: Develop Relational Database Schema For Boat Club Database UsingDocument3 pagesDdl. Paiza: EXPERIMENT-1: Develop Relational Database Schema For Boat Club Database UsingKONDRAGUNTA SAI GANESHNo ratings yet
- 1e843f17a1ac273c62c13eb1ce9745ccDocument1,087 pages1e843f17a1ac273c62c13eb1ce9745ccJaisal FrancisNo ratings yet
- AZURE SQL DatabaseDocument23 pagesAZURE SQL DatabaseprashanthbhatNo ratings yet
- JAVA - Mini Projects ListDocument5 pagesJAVA - Mini Projects ListManishNo ratings yet
- Application ManualDocument70 pagesApplication ManualRafael SchroerNo ratings yet
- Screenshot Whole Page Iphone 13 Pro Max - GoogleDocument1 pageScreenshot Whole Page Iphone 13 Pro Max - Googleesti yolandaNo ratings yet
- Python Online Compiler & Interpreter - ReplitDocument1 pagePython Online Compiler & Interpreter - Replitalan jesus lasso reyesNo ratings yet
- Satellite L655 S5112BNDocument4 pagesSatellite L655 S5112BNJesús BárcenaNo ratings yet
- Summary Chapter 1 - Database ConceptsDocument15 pagesSummary Chapter 1 - Database ConceptsMUHAMMAD AKMAL MOHD ZAHARNo ratings yet
- CL03 - Studio 5000 Logix Designer Basics Lab - Lab ManualDocument110 pagesCL03 - Studio 5000 Logix Designer Basics Lab - Lab Manualjack100% (4)
- How BIOS WorksDocument1 pageHow BIOS WorksNikunj JainNo ratings yet
- Reflection PaperDocument3 pagesReflection Paperapi-455115030No ratings yet
- Salesforce Admin Certification Complete Exam Actual Practice Material New Update 2022Document16 pagesSalesforce Admin Certification Complete Exam Actual Practice Material New Update 2022tesla samNo ratings yet
- Authoring ToolsDocument28 pagesAuthoring ToolsMuhd ZahinNo ratings yet
- r20 4-1 Open Elective III Syllabus Final WsDocument29 pagesr20 4-1 Open Elective III Syllabus Final WsDharmik Pawan KumarNo ratings yet
- Ansys Elastic Currency Software Consumption Rate Table v317Document2 pagesAnsys Elastic Currency Software Consumption Rate Table v317Enrique de AguileraNo ratings yet
- Learning Management SystemDocument17 pagesLearning Management SystemMagesa M. MwitaNo ratings yet
- Hardware Sales and Servicing Information SystemDocument39 pagesHardware Sales and Servicing Information SystemSayeeda Anjum0% (1)
- Autosar PDFDocument125 pagesAutosar PDFChethan100% (1)
- User Manual Abrites Commander For ToyotaDocument27 pagesUser Manual Abrites Commander For ToyotaJame Eduardo100% (1)
- GD MCQDocument29 pagesGD MCQpoweredgofficial77No ratings yet
- 5431 Titanium Console Manual TT1.0 2.0 3.0 ENGLISH PRINTDocument19 pages5431 Titanium Console Manual TT1.0 2.0 3.0 ENGLISH PRINTMilos VujasinovicNo ratings yet
- Avinash R Erupaka ResumeDocument4 pagesAvinash R Erupaka ResumeNainika KedarisettiNo ratings yet
- Interactive Excel Dashboard Course Resources PDFDocument2 pagesInteractive Excel Dashboard Course Resources PDFshuklaNo ratings yet
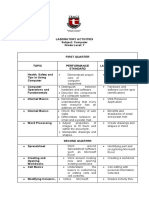
- Laboratory Activities - Computer 7Document2 pagesLaboratory Activities - Computer 7John Marvin CanariaNo ratings yet
- INTEGRATIVE PROGRAMMING Lesson1Document44 pagesINTEGRATIVE PROGRAMMING Lesson1jad be100% (1)
- Exhibit A Confidentiality and Non-Disclosure Agreement: January 2021 1Document4 pagesExhibit A Confidentiality and Non-Disclosure Agreement: January 2021 1PAOLA GUTIÉRREZ MEDRANONo ratings yet