Professional Documents
Culture Documents
Trusted Attestation Key With Windows Management Using Direct Anonymous Attestation Protocol
Uploaded by
Integrated Intelligent ResearchOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Trusted Attestation Key With Windows Management Using Direct Anonymous Attestation Protocol
Uploaded by
Integrated Intelligent ResearchCopyright:
Available Formats
International Conference on Computing and Intelligence Systems
Pages: 1242 1245
Volume: 04, Special Issue: March 2015
ISSN: 2278-2397
Trusted Attestation Key with Windows
Management using Direct Anonymous
Attestation Protocol
E.Padma1, S.Rajalakshmi2
1
Research Scholar, SCSVMV, University, Enathur Kanchipuram, TamilNadu.
Director, SJCAC, SCSVMV, University, Enathur, Kanchipuram, Tamil Nadu.
Email: mailtopadma@kanchiuniv.ac.in rajalakshmi.s@kanchiuniv.ac.in
Abstract-The Trusted Platform Module (TPM)
is a hardware chip designed to enable computers
to achieve a greater level of security. The TPM is
at the heart of the Trusted Computing initiative,
and thus it provides the root of trust for many
applications. In the Distributed Environment all
the systems are connected together with a limited
bandwidth.The security feature deals with the root
of trust using Trusted Attestation Key. The
Trusted Attestation Key will increase the security
feature by the concept of DAA protocol. Direct
anonymous attestation (DAA) protocol is a special
digital signature primitive, which provides a
balance between signer, authentication and system
privacy. An issuer is in charge of verifying the
legitimacy of users and DAA credential issued to
each signer. Trusted Attestation Key can be used
as a tool for authenticity. The TAK is the
authenticated key generated for each individual
and holds the secret signing key in the remote
server database. Authentication can be applied at
the
level
of
Windows
Management
Instrumentation (WMI) for accessing the
information through remote connection. WMI
tools can be implemented using Distributed
Management Task Force (DMTF). The
authentication to the distributed system
environment with Distributed Shared Memory
(DSM) can be modeled with the Trusted Platform
Technology.
Keywords - Trusted Platform Module, Trusted
Attestation Key, Direct Anonymous Attestation,
Authentication, Distributed Shared Memory
I. INTRODUCTION
The distributed environment and network
computing are widely used in the organization of
computer system. The security feature for the remote
accessing system has become an important problem
for various users. To provide more security for the
verification and authentication of the user Trusting
Computing can be widely used [3]. The Trusted
Computing as a hardware chip enables the security
feature with limited exemptions. The TPM is designed
to protect against or mitigate the probable damage
International Journal of Computing Algorithm (IJCOA)
created by various kinds of threats and attacks.
Trusted Computing in the field of software using the
Direct Anonymous Attestation protocol [16] will
prove the model to be more secure. The security for
the distributed systems will be provided enormously
using the verification and attestation key.
The DAA credentials have to be assigned to each
individual. In the distributed environment, Digital
Signature deals with coordination of different
resources [13]. Trusted Attestation Key provides a
facility for accessing large number of users remotely
using Windows Management Instrumentation. The
Trusted Computing Platform (TCP) has to be
integrated with Trusted Platform Module (TPM), in
order to protect the sensitive information [9].The TCP
can improve the security feature of Virtual Private
Environment by providing proper authentication using
the Attestation Key with Shared memory space.
Windows Driver Model provides set of extensions for
the
concept
of
Windows
Management
Instrumentation.
The driver model provides an operating system
interface for the information and notification provided
by the instrumented components. Web-Based
Enterprise Management (WBEM) and Common
Information Model (CIM)is the implementation tool
of Windows Management Instrumentation which has
been basically designed from the Distributed
Management Task Force (DMTF) [18]. The
Authenticity can be matched using Machine
Authentication Code. The purpose of WMI is to
define a proprietary set of environment-independent
specifications which allow management information
to be shared between management applications. The
Authentication code can be generated using the Secure
Hashing Key. Windows Management Instrumentation
Tool such as MOF compiler MOFComp.exe compiler,
WMI Administrative Tools, WBEMTest.exe, WMI
command line tool (WMIC), WBEMDump.exe,
WMIDiag.vbs serve as an authentication provider for
remote calling [18].
1242
International Conference on Computing and Intelligence Systems
Pages: 1242 1245
II. WORK RELATED TO TPM AND
DISTRIBUTED COMPUTING ENVIRONMENT
A. Current Security Model of Distributed Computing
The existing Trusted Platform Module with
distributed system gives less performance feature[17].
The Trusted Computing Group provides large number
of services for more number of distributed systems to
be accessed. The Security model of Distributed
System alone deals with Secrecy, Integrity,
Availability and Accountability. The Secrecy feature
deals with controlling the read information. Integrity
deals with how Information changes are used. The
term Availability prompts access to information and
resources. The Accountability service provides
information about the individual users who had
accessingright [11]. The Security of Information is
concerned with human user authentication, and peerto-peer
authentication.
In
the
distribution
environment, the communication demands more
security between entities. The Security messages with
full protection can be transported. The process of
cryptographic computing reduces the performance of
the system.In the distributed computing environment,
the protection given to the certificates are not secured
[3]. In the current scenario, the distributed system
does not define the root of trust. The Challenges of
the exempted performance can be defined in future
using the attestation and verification for each user
individually.
B. Challenges of Distributed Computing Environment
The challenges for distributed computing with
growingdemands for various applications are
increasing. Apart from reliability, performance,
availability and many other entities such as security,
privacy, trustworthiness, situation awareness,
flexibility and rapid development of various
applications have also become important [2].
Research in security, storage systems, simplifying
management, and reliability is likely to lead to the
creation of important new knowledge and design
[10].The Security policies for the distributed users
using their resources are limited. The scope of the
security mechanism has to be implemented with
proper services. Each individual user has to maintain
their own verifiers for accessing any available
resources with the prescribed mechanism. The
requirements for the distributed users are to be
enhanced with the feature of Attestation.
III. TRUSTED COMPUTING TECHNOLOGY
The basic features of TPM include configuration
management and basic cryptographic operation. The
configuration management is the main design goal of
TPM [9]. The hierarchical policies of security
features are enforced by Trusted Platform
Module.The various confidence and trustworthiness
levels for authenticated platform are focused by
International Journal of Computing Algorithm (IJCOA)
Volume: 04, Special Issue: March 2015
ISSN: 2278-2397
trusted computing system.In the proposed work WMI
concept combined with Trusted Computing Group
(TCG) has been adopted for higher security.The
distinguishing feature of TCG technology is arguably
the incorporation of roots of trust into computer
platforms[3].In turn, the trusted software services are
concerned with the authenticated features for various
system modules.Platform Configuration Registers
(PCR) with more security feature can be adopted to
evaluate each componentof the system [1 & 4]. The
trusted computing can be combined with Windows
Management Instrumentation to provide security for
remote connection. The information can be remotely
stored using Common Information Model.
IV. PROPOSED METHODOLOGY
In the proposed methodology, the attestation
key algorithm plays a role of attesting the authorized
user to access the data remotely and to maintain the
integrity with proper Efficiency Factor. Remote
connections can be established between various users
for accessing the information by issuing attested key.
The key will be generated using Secure Hash Code.
The generated key will be used by each individual to
share the distributed resources and database for
remote users. Therole of Distributed Management
Task Force is to manage remote calls in a server. The
information can be stored in Distributed Shared
Virtual Memory (DSVM) for various users as each
individual has separate local shared memory. The
attestation algorithm checks for the authorization and
then grants the right for accessing the information
temporarily stored as buffered data. The algorithm
then checks for the verification phase by the trusted
user with the encrypted attested key. In this phase, the
signature of the trusted party will be verified using the
cryptographic cryptosystem. The TAK Algorithm
along with Direct Anonymous Attestation protocol
can measure the efficiency of resources that are
accessed from the virtual memory for large scale of
memory access. Remote server maintains all
information about each individual user. WMI tools
use Common Information Model to store the
information more secure. WMI administrative tool
then manages separate identification for the users to
access the necessary information. The security
features for the integrity and trustworthiness can be
measured using the algorithm.
A.Algorithm
Begin
Step 1: Enter the login information
Step 2: Check for the Intruders
If password matches with encrypted data
Go to step 3
Else
Go to step1
End if
Step 3: Allocation of space in distributed shared
memory
1243
International Conference on Computing and Intelligence Systems
Pages: 1242 1245
Step 4: grant permission from WMI
Step 5: check for the size of information to be
accessed
If size exceeds the relevant fixed size
Go to step3
Else
Go to step6
End if
Step6: Access information
End
Volume: 04, Special Issue: March 2015
ISSN: 2278-2397
TPM
Distributed
Environment
DAA
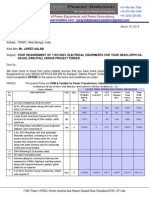
FIG 2: DISTRIBUTED ENVIRONMENTWITH DAA
Computer
A
A connectstoB
Computer
B
,,
FIG1:REMOTE
CONNECTION
B.Algorithm Explanation
The proposed algorithm first allows the user to
login to the system. It then checks for the intruders. If
intruders try to access the information it will not
permit to proceed. Again it will check for the
authorization of the user. After checking the system
will allocate space in distributed shared memory and
also it grants permission from windows management
instrumentation. The information tobe accessed by the
user should not exceed the fixed size. The encrypted
data stored in the server will check for the Machine
Authentication Code before it allows to access the
information.
V. ROLE OF DAA IN DISTRIBUTED
COMPUTING ENVIRONMENT
Direct Anonymous Attestation (DAA) is a scheme
developed by Brickell, Camenisch, and Chen [12] for
remote authentication of a security hardware module
called Trusted Platform Module (TPM) which is the
core component of trusted computing platform [7].
The remote authenticity can be verified using security
in Windows Management Instrumentation (WMI).
The Distributed Component Object Model handles
remote calls for Trusted Attestation Key. TAK plays
a major role in designing the verifier and signer
authenticity. The password based authentication can
be generated as an anonymous permission to all
authenticated users. Distributed Environment has the
capacity of Fault Tolerance rather than network
operating environment [6 & 8]. In distributed
environment the local memory of different machines
can be integrated into a single logical entity by
cooperating processes on multiple sites. The shared
memory exists virtually for each process.
International Journal of Computing Algorithm (IJCOA)
DAA Algorithm deals with the concept of
Attestation key. The keys involved in DAA provide
signing and verifying authority for all the distributed
users. The Algorithm contains full protection with
password based authentication. The Distributed
Computing Environment needs more security feature
to protect from the intruders [14& 15]. As a view the
Trusted Attestation Key has been designated as a
protected key for remote access. DAA Algorithm
deals with distributed resource sharing in the form of
allocating each system a privacy enhancing measure.
The counter value is kept for easy identification of
each and every system using Trusted Attestation Key
(TAK). The Trusted party alone can have the access
with the shared resource. The Algorithm finds the
intruder while signing in. Remotely the Authorisation
can be verified using the Concept of Distributed
Management Task Force. When large number of
distributed users sign in at the moment and access the
system, the DMTF will grant permission only to the
authenticated users. To track the efficiency factor a
register is maintained separately called Efficient
Configuration Register (ECR). The ECR will maintain
the record of individual user from the distributed
environment and work with full trustiness feature. The
Efficiency factor can be calculated using the register
value along with the counter value that has been
generated. All the system remotely accessed can be
given identification to know the trustworthiness.
Trusted
Attestation Key
Distributed
Shared
Memory
Distributed
Environment
FIG 3: ARCHITECTURE OF DISTRIBUTED
ENVIRONMENT WITH DSM AND
TRUSTEDATTESTATION KEY
1244
International Conference on Computing and Intelligence Systems
Pages: 1242 1245
VI. BUILD TRUSTED ENVIRONMENT WITH
ATTESTATION KEY
[2]
The trusted computing mechanism provides a way
to establish a secure environment. The trusted
computing model is designed to provide privacy and
trust for authenticated users [3]. Distributed
computing should involve a large amount of entities,
such as users and resources from different sources.
The attestation process is important for
authentication. The model for direct anonymous
attestation is varied based on the signature. Each
system is digitized with verification and signing. In
this paper the new concept of DAA with Trusted
Attestation Key as a security feature has been adopted
for the distributed system to work without any
interruption of the intruders. Theroot of trust for all
the users and how far the accessing varies with one
user to another user can also be measured with the
Attestation. The ECR will maintain separate register
for all the users who are connected together to access
the system. There are some pitfalls with the generated
attested keys which are stored in the server for
Distributed Shared Memory security. The DAA plays
a role to rectify the vast amount of unauthorized
authorities to access the system [5]. The trusted
environment can be build with the authentication
protocol which can be exchanged between the user
and the server.
[3]
VII. CONCLUSION
In this paper Attestation key for DAA scheme
called Trusted Attestation Key has been defined to
measure the usage of authorized remote users for
accessing the information stored in Distributed
Shared Memory. The Authentication can be
confirmed with the signing model. The limitation of
this work is allocating Distributed Shared Virtual
Memory and bandwidth for more number of users
which can be taken up as future work. The distributed
computing environment works with heterogeneity
feature. The DSM systems built for single user
environment need not address the heterogeneity
issues. The Trusted Computing environment has the
root of trust with the DAA protocol. The performance
feature of the distributed system has to be further
redesigned as a future work. The security mechanism
for Trusted Attestation Key has to be further
measured
with
Windows
Management
Instrumentation. The Efficiency Factor for distributed
shared memory with large scale performance has to
be configured with Distributed Component Object
Model as a future work.
[1]
[4]
[5]
[6]
[7]
[8]
[9]
[10]
[11]
[12]
[13]
[14]
[15]
[16]
[17]
[18]
Volume: 04, Special Issue: March 2015
ISSN: 2278-2397
Yau, Stephen S , High Performance Computing and
Communications (HPCC), 2011 IEEE 13th International
Conference on 2-4 Sept. 2011.
Zhidong Shen, Qiang Tong ,The Security of Cloud
Computing System enabled by Trusted Computing
Technology, 2010 2nd International Conference on Signal
Processing Systems (ICSPS)
Stueble C, Zaerin A. TSS A simplified trusted software
stack. Proceedings of the 3rd International Conference on
Trust and Trustworthy Computing (TRUST 2010), no. 6101 in
LNCS, Springer Verlag, 2010.
C. Latze, U. Ultes-Nitsche, F. Baumgartner, Extensible
Authentication Protocol Method for Trusted Computing
Groups (TCG) Trusted Platform Modules, Work in
Progress, 2009.
Pirker M, Toegl R, Hein D, Danner P. A Privacy CAfor
anonymity and trust. Proc. Trust 09, LNCS, Vol.
5471.Springer, 2009.
CHEN Xiaofeng and FENG Dengguo, Direct Anonymous
Attestation for Next Generation TPM JOURNAL OF
COMPUTERS, VOL.3, NO. 12, DECEMBER 2008.
Microsoft. TPM Base Services. Microsoft Developer
Network, 2007. http://msdn.microsoft.com/en-us/library/
aa446796(VS.85).aspx [27 May 2011]
Tian Haibo, Wang YuminThe Future Network Security,
China Communications August 2006.
M. Frans Kaashoek Barbara Liskov David Andersen Mike
Dahlin Carla Ellis Steve Gribble Anthony Joseph Hank Levy
Andrew Myers Jeff Mogul Ion Stoica Amin Vahdat, Report
of the NSF Workshop on Research Challenges in Distributed
Computer Systems, Dec 4 2005.
Claus Fritzner,Leif Nilsen And smund Skomedal ,Protecting
SecurityInformationinDistributedSystems,GH29868\91/000
0/0245$01.00@1991 IEEE.
Ernest F. Brickell, Jan Camenisch, Liqun Chen: Direct
anonymous attestation. ACM Conference on Computer and
Communications Security 2004: 132-145.
Elaine Shi, Adrian Perrig, Leendert Van Doorn BIND: A
Fine-grained Attestation Service forSecure Distributed
Systems 2013.
E.Padma, Dr.S.Rajalakshmi The Privacy Feature of Trusted
Computing Technology using the Concept of Direct
Anonymous Attestation with Cloud as a Technique
International Journal of Computer Engineering and
Technology(IJCET), ISSN 0976-6367(Print), ISSN 09766375(Online) Volume 5, Issue 2, February 2014 pp 140-144.
E.Padma, Dr.S.Rajalakshmi An Effective Approach for
Trusted Attestation Key in Distributed Computing
Environment using TPM International Journal of Applied
Engineering Research(IJAER), ISSN 0973-4562 Volume 9,
Number 22(2014) pp 12087-12096
Marwan Ibrahim Alshare, Rossilawati Sulaiman, Mohd
Rosmadi Mukhtar and Abdullah Mohd Zin, A User
Protection Model for the Trusted Computing Environment,
Journal of Computer Science 10(9): 1692-1702, 2014.
Klenk, A., H. Kinkelin, C. Eunicke and G. Carle, Preventing
identity theft with electronic identity cards and the trusted
platform module, Proceedings of the 2nd European
Workshop on System Security, Mar. 31-31, ACM,
Nuremburg,
Germany,
pp:
4451.
DOI:
10.1145/1519144.1519151, 2009.
http://en.wikipedia.org/wiki/Windows_Management_Instrum
entation.
REFERENCES
Ronald Toegl, Thomas Winkler, Mohammad Nauman and
Theodore W. Hong Specification and Standardization of a
Java Trusted Computing API SOFTWARE PRACTICE
AND EXPERIENCESoftw. Pract. Exper. 2011 Published
online in Wiley Online Library (wileyonlinelibrary.com).
International Journal of Computing Algorithm (IJCOA)
1245
You might also like
- AZURE AZ 500 STUDY GUIDE-1: Microsoft Certified Associate Azure Security Engineer: Exam-AZ 500From EverandAZURE AZ 500 STUDY GUIDE-1: Microsoft Certified Associate Azure Security Engineer: Exam-AZ 500No ratings yet
- CYBER SECURITY HANDBOOK Part-2: Lock, Stock, and Cyber: A Comprehensive Security HandbookFrom EverandCYBER SECURITY HANDBOOK Part-2: Lock, Stock, and Cyber: A Comprehensive Security HandbookNo ratings yet
- Integrating The Trusted Computing Platform Into The Security of Cloud Computing SystemDocument5 pagesIntegrating The Trusted Computing Platform Into The Security of Cloud Computing Systemeditor_ijarcsseNo ratings yet
- Clustering Cloud ComputingDocument85 pagesClustering Cloud ComputingSahil YadavNo ratings yet
- Cloud SecurityDocument5 pagesCloud SecuritymanojraydNo ratings yet
- Trusted Computing in Mobile Action: Nicolai Kuntze, and Andreas U. SchmidtDocument12 pagesTrusted Computing in Mobile Action: Nicolai Kuntze, and Andreas U. SchmidtNaveen ReddyNo ratings yet
- Data Security in Cloud ComputingDocument22 pagesData Security in Cloud ComputingPiyush MittalNo ratings yet
- Cloud Security Mechanisms GuideDocument6 pagesCloud Security Mechanisms GuideMoktar AmmarNo ratings yet
- Achieving Secure Network Authentication in Cloud Computing via ECDSADocument10 pagesAchieving Secure Network Authentication in Cloud Computing via ECDSATahir HussainNo ratings yet
- Study of Authentication and Authorization in Cloud ComputingDocument3 pagesStudy of Authentication and Authorization in Cloud ComputingEditor IJRITCCNo ratings yet
- Adopting Trusted Third Party Services For Multi-Level Authentication Accessing CloudDocument7 pagesAdopting Trusted Third Party Services For Multi-Level Authentication Accessing CloudInternational Journal of computational Engineering research (IJCER)No ratings yet
- Final Report ChaptersDocument56 pagesFinal Report ChaptersJai Deep PonnamNo ratings yet
- Architectural Design of A Strong Bi-Factor ReAuthentication Paradigm in Cloud EnvironmentDocument6 pagesArchitectural Design of A Strong Bi-Factor ReAuthentication Paradigm in Cloud EnvironmentJyotika LalwaniNo ratings yet
- Cloud Computing Security Problems and TechniquesDocument6 pagesCloud Computing Security Problems and TechniquesHëmańťh ŁucķýNo ratings yet
- Csol 520Document13 pagesCsol 520api-615679676No ratings yet
- An Effective Privacy-Preserving Blockchain-Assisted Security Protocol For Cloud-Based Digital Twin EnvironmentDocument5 pagesAn Effective Privacy-Preserving Blockchain-Assisted Security Protocol For Cloud-Based Digital Twin EnvironmentDhineshNo ratings yet
- Security Framework For Cloud ComputingDocument9 pagesSecurity Framework For Cloud Computingjack s99No ratings yet
- Cloudnet Security Technical White PaperDocument17 pagesCloudnet Security Technical White PaperEduardoChavezNo ratings yet
- DR - Subbiah RR 07.09.2020Document3 pagesDR - Subbiah RR 07.09.2020Subbiah SNo ratings yet
- Secure Sensitive Data Sharing FrameworkDocument9 pagesSecure Sensitive Data Sharing FrameworkMarcos MoriconiNo ratings yet
- Chapter10 Module3Document28 pagesChapter10 Module3Just Watch ItNo ratings yet
- Data Security in Cloud Using Key Aggregate Cryptosystem: I J I R C C EDocument17 pagesData Security in Cloud Using Key Aggregate Cryptosystem: I J I R C C EAnonymous etpj6GNo ratings yet
- Ijret - Enhanced Security Framework To Ensure Data Security in Cloud Using Security Blanket AlgorithmDocument5 pagesIjret - Enhanced Security Framework To Ensure Data Security in Cloud Using Security Blanket AlgorithmInternational Journal of Research in Engineering and TechnologyNo ratings yet
- Unit - V Cloud Security - Part1Document24 pagesUnit - V Cloud Security - Part1shinderohann02No ratings yet
- A Capable and Constructed Plan To Share Data For Mobile Cloud ComputingDocument5 pagesA Capable and Constructed Plan To Share Data For Mobile Cloud ComputingPeter HeinNo ratings yet
- Security Trusted ComputingDocument7 pagesSecurity Trusted ComputingUmm e LailaNo ratings yet
- Cloud Security MechanismsDocument31 pagesCloud Security MechanismsVidushi SoodNo ratings yet
- Enabling Public Auditability For Cloud Data Storage SecurityDocument5 pagesEnabling Public Auditability For Cloud Data Storage SecurityRakeshconclaveNo ratings yet
- Applied SciencesDocument15 pagesApplied SciencesRini AngrainiNo ratings yet
- Authorization and Authentication in Mobile DevicesDocument8 pagesAuthorization and Authentication in Mobile DevicesIJRASETPublicationsNo ratings yet
- Icas 2015 5 10 20025Document7 pagesIcas 2015 5 10 20025zakariaNo ratings yet
- Unit 5Document28 pagesUnit 5Dharmik SuchakNo ratings yet
- DataSheet UAS E2EEDocument2 pagesDataSheet UAS E2EEDark KnightNo ratings yet
- Key Cloud Security MechanismsDocument4 pagesKey Cloud Security MechanismsAshutoshNo ratings yet
- Cloud ComputingDocument9 pagesCloud ComputingJohn NyachubaNo ratings yet
- Authorization and Authentication in Mobile Devices!Document7 pagesAuthorization and Authentication in Mobile Devices!IJRASETPublicationsNo ratings yet
- An Authentication Scheme Based On Multiple Trusted Third PartyDocument3 pagesAn Authentication Scheme Based On Multiple Trusted Third PartyerpublicationNo ratings yet
- Security Assurance of An In-Vehicle HMI Manager: David Cerdeira Henrique SantosDocument4 pagesSecurity Assurance of An In-Vehicle HMI Manager: David Cerdeira Henrique SantosMircea PetrescuNo ratings yet
- IEEE 2017 Enhanced RSA Algorithm With Varying Key Sizes For Data Security in CloudDocument4 pagesIEEE 2017 Enhanced RSA Algorithm With Varying Key Sizes For Data Security in Cloudakash rawatNo ratings yet
- Key-Aggregate Cryptosystem For Scalable Data Sharing in Cloud Storage-A ReviewDocument5 pagesKey-Aggregate Cryptosystem For Scalable Data Sharing in Cloud Storage-A ReviewSiddhartha BashettyNo ratings yet
- Ism Cat 1Document88 pagesIsm Cat 1AAKASH GOPALNo ratings yet
- Cloud Data Production For MassesDocument4 pagesCloud Data Production For MassesPooja BanNo ratings yet
- Chapter FourDocument6 pagesChapter Fouruthmannazir2627No ratings yet
- Virtual IzationDocument6 pagesVirtual IzationPrateek SharmaNo ratings yet
- Information System ControlDocument3 pagesInformation System ControlWubishet WegeneNo ratings yet
- "Security": Developing Effective Design Strategies For Today's Wearable DevicesDocument7 pages"Security": Developing Effective Design Strategies For Today's Wearable DevicesDomingos Savio Silva CarneiroNo ratings yet
- Improving Efficiency of Security in Multi-CloudDocument4 pagesImproving Efficiency of Security in Multi-CloudijtetjournalNo ratings yet
- Unit-3 E-CommerceDocument18 pagesUnit-3 E-CommercegowthamniftchennaiNo ratings yet
- A30 PDFDocument4 pagesA30 PDFSuresh Reddy PolinatiNo ratings yet
- MICROSERVICES SECURITY AND PRIVACY CHALLENGESDocument7 pagesMICROSERVICES SECURITY AND PRIVACY CHALLENGESahmadNo ratings yet
- (IJCST-V9I3P18) :steffy Francis, Dr. G. KiruthigaDocument8 pages(IJCST-V9I3P18) :steffy Francis, Dr. G. KiruthigaEighthSenseGroupNo ratings yet
- PP 216-221 A Conceptual Architecture For Securing Public Cloud Moving FromDocument6 pagesPP 216-221 A Conceptual Architecture For Securing Public Cloud Moving FromEditorijset IjsetNo ratings yet
- Token-Based Cloud Computing: Secure Outsourcing of Data and Arbitrary Computations With Lower LatencyDocument13 pagesToken-Based Cloud Computing: Secure Outsourcing of Data and Arbitrary Computations With Lower LatencyVishnu TejaNo ratings yet
- Cryptography and Cloud SecurityDocument2 pagesCryptography and Cloud SecurityAbdourahmane KaneNo ratings yet
- A Survey of Security in Hybrid P2P Networks Using SAAS and Multicast Key ManagementDocument4 pagesA Survey of Security in Hybrid P2P Networks Using SAAS and Multicast Key ManagementShrutiNo ratings yet
- Securing Your Computer NetworkDocument52 pagesSecuring Your Computer Networkاحمد سالمNo ratings yet
- Detecting SecretsDocument27 pagesDetecting SecretsvmadhuriNo ratings yet
- Algorithm For Secured KeyDocument8 pagesAlgorithm For Secured Keypratiksha mishraNo ratings yet
- reviewDocument74 pagesreviewsethumadhavansasi2002No ratings yet
- Mitigating Software Integrity Attacks With Trusted Computing in a Time Distribution NetworkDocument17 pagesMitigating Software Integrity Attacks With Trusted Computing in a Time Distribution NetworkgeethakaniNo ratings yet
- A Survey On The Simulation Models and Results of Routing Protocols in Mobile Ad-Hoc NetworksDocument6 pagesA Survey On The Simulation Models and Results of Routing Protocols in Mobile Ad-Hoc NetworksIntegrated Intelligent ResearchNo ratings yet
- A Review On Role of Software-Defined Networking (SDN) in Cloud InfrastructureDocument6 pagesA Review On Role of Software-Defined Networking (SDN) in Cloud InfrastructureIntegrated Intelligent ResearchNo ratings yet
- Investigating Performance and Quality in Electronic Industry Via Data Mining TechniquesDocument5 pagesInvestigating Performance and Quality in Electronic Industry Via Data Mining TechniquesIntegrated Intelligent ResearchNo ratings yet
- Three Phase Five Level Diode Clamped Inverter Controlled by Atmel MicrocontrollerDocument5 pagesThree Phase Five Level Diode Clamped Inverter Controlled by Atmel MicrocontrollerIntegrated Intelligent ResearchNo ratings yet
- Impact of Stress On Software Engineers Knowledge Sharing and Creativity (A Pakistani Perspective)Document5 pagesImpact of Stress On Software Engineers Knowledge Sharing and Creativity (A Pakistani Perspective)Integrated Intelligent ResearchNo ratings yet
- A New Computer Oriented Technique To Solve Sum of Ratios Non-Linear Fractional Programming ProblemsDocument1 pageA New Computer Oriented Technique To Solve Sum of Ratios Non-Linear Fractional Programming ProblemsIntegrated Intelligent ResearchNo ratings yet
- Prediction of Tumor in Classifying Mammogram Images by K-Means, J48 and CART AlgorithmsDocument6 pagesPrediction of Tumor in Classifying Mammogram Images by K-Means, J48 and CART AlgorithmsIntegrated Intelligent ResearchNo ratings yet
- Slow Intelligence Based Learner Centric Information Discovery SystemDocument3 pagesSlow Intelligence Based Learner Centric Information Discovery SystemIntegrated Intelligent ResearchNo ratings yet
- Effective Approaches of Classification Algorithms For Text Mining ApplicationsDocument5 pagesEffective Approaches of Classification Algorithms For Text Mining ApplicationsIntegrated Intelligent ResearchNo ratings yet
- Applying Clustering Techniques For Efficient Text Mining in Twitter DataDocument4 pagesApplying Clustering Techniques For Efficient Text Mining in Twitter DataIntegrated Intelligent ResearchNo ratings yet
- Classification of Retinal Images For Diabetic Retinopathy at Non-Proliferative Stage Using ANFISDocument6 pagesClassification of Retinal Images For Diabetic Retinopathy at Non-Proliferative Stage Using ANFISIntegrated Intelligent ResearchNo ratings yet
- A New Arithmetic Encoding Algorithm Approach For Text ClusteringDocument4 pagesA New Arithmetic Encoding Algorithm Approach For Text ClusteringIntegrated Intelligent ResearchNo ratings yet
- Associative Analysis of Software Development Phase DependencyDocument9 pagesAssociative Analysis of Software Development Phase DependencyIntegrated Intelligent ResearchNo ratings yet
- A Survey On Analyzing and Processing Data Faster Based On Balanced Partitioning - IIR - IJDMTA - V4 - I2 - 006Document4 pagesA Survey On Analyzing and Processing Data Faster Based On Balanced Partitioning - IIR - IJDMTA - V4 - I2 - 006Integrated Intelligent ResearchNo ratings yet
- A Framework To Discover Association Rules Using Frequent Pattern MiningDocument6 pagesA Framework To Discover Association Rules Using Frequent Pattern MiningIntegrated Intelligent ResearchNo ratings yet
- A Framework To Discover Association Rules Using Frequent Pattern MiningDocument6 pagesA Framework To Discover Association Rules Using Frequent Pattern MiningIntegrated Intelligent ResearchNo ratings yet
- A Study For The Discovery of Web Usage Patterns Using Soft Computing Based Data Clustering TechniquesDocument14 pagesA Study For The Discovery of Web Usage Patterns Using Soft Computing Based Data Clustering TechniquesIntegrated Intelligent ResearchNo ratings yet
- RobustClustering Algorithm Based On Complete LinkApplied To Selection Ofbio - Basis Foramino Acid Sequence AnalysisDocument10 pagesRobustClustering Algorithm Based On Complete LinkApplied To Selection Ofbio - Basis Foramino Acid Sequence AnalysisIntegrated Intelligent ResearchNo ratings yet
- A Study For The Discovery of Web Usage Patterns Using Soft Computing Based Data Clustering TechniquesDocument7 pagesA Study For The Discovery of Web Usage Patterns Using Soft Computing Based Data Clustering TechniquesIntegrated Intelligent ResearchNo ratings yet
- A Framework To Discover Association Rules Using Frequent Pattern MiningDocument6 pagesA Framework To Discover Association Rules Using Frequent Pattern MiningIntegrated Intelligent ResearchNo ratings yet
- A Review Paper On Outlier Detection Using Two-Phase SVM Classifiers With Cross Training Approach For Multi - Disease DiagnosisDocument7 pagesA Review Paper On Outlier Detection Using Two-Phase SVM Classifiers With Cross Training Approach For Multi - Disease DiagnosisIntegrated Intelligent ResearchNo ratings yet
- A Study For The Discovery of Web Usage Patterns Using Soft Computing Based Data Clustering TechniquesDocument7 pagesA Study For The Discovery of Web Usage Patterns Using Soft Computing Based Data Clustering TechniquesIntegrated Intelligent ResearchNo ratings yet
- Paper13 PDFDocument8 pagesPaper13 PDFIntegrated Intelligent ResearchNo ratings yet
- Multidimensional Suppression For KAnonymity in Public Dataset Using See5Document5 pagesMultidimensional Suppression For KAnonymity in Public Dataset Using See5Integrated Intelligent ResearchNo ratings yet
- A Comparative Analysis On Credit Card Fraud Techniques Using Data MiningDocument3 pagesA Comparative Analysis On Credit Card Fraud Techniques Using Data MiningIntegrated Intelligent ResearchNo ratings yet
- Paper11 PDFDocument5 pagesPaper11 PDFIntegrated Intelligent ResearchNo ratings yet
- Significance of Similarity Measures in Textual Knowledge MiningDocument4 pagesSignificance of Similarity Measures in Textual Knowledge MiningIntegrated Intelligent ResearchNo ratings yet
- Agricultural Data Mining - Exploratory and Predictive Model For Finding Agricultural Product PatternsDocument8 pagesAgricultural Data Mining - Exploratory and Predictive Model For Finding Agricultural Product PatternsIntegrated Intelligent ResearchNo ratings yet
- Paper13 PDFDocument8 pagesPaper13 PDFIntegrated Intelligent ResearchNo ratings yet
- Paper13 PDFDocument8 pagesPaper13 PDFIntegrated Intelligent ResearchNo ratings yet
- Tablero de Control Micro SLXDocument4 pagesTablero de Control Micro SLXprimarioNo ratings yet
- ZOS 1.12 JES2 New FunctionsDocument53 pagesZOS 1.12 JES2 New FunctionsPatrícia RosaNo ratings yet
- HDPE Pipe Joining System PDFDocument22 pagesHDPE Pipe Joining System PDFVasilica Barbarasa50% (2)
- Bus ArbitrationDocument18 pagesBus ArbitrationANSHIKA VASHISTHA 21GCEBIT115No ratings yet
- Brosjyreark Particle-DSP OKDocument2 pagesBrosjyreark Particle-DSP OKangeljosNo ratings yet
- Audio SpotlightingDocument24 pagesAudio SpotlightingSai Chaitanya0% (1)
- Power Equipment Suppliers for NTPC ProjectDocument17 pagesPower Equipment Suppliers for NTPC ProjectSharafat AliNo ratings yet
- Technical Engineering PEEDocument3 pagesTechnical Engineering PEEMariano Acosta Landicho Jr.No ratings yet
- Manual h110m Pro VH PlusDocument1 pageManual h110m Pro VH Plushora22No ratings yet
- Epson Stylus TX121Document2 pagesEpson Stylus TX121manmca1986No ratings yet
- S&S Make: RRM For 6000 RPMDocument16 pagesS&S Make: RRM For 6000 RPMABVSAI100% (1)
- Convert Seismological Data and Analyze WaveformsDocument72 pagesConvert Seismological Data and Analyze WaveformsYayanMi'rojulHusniNo ratings yet
- NotePerformer - Users GuideDocument56 pagesNotePerformer - Users GuideDan Sannich100% (1)
- ADMS 2009 ImplementationGuideDocument113 pagesADMS 2009 ImplementationGuideGhita-Mehedintu GheorgheNo ratings yet
- FIBROTOR® EM. and EM - NC PDFDocument83 pagesFIBROTOR® EM. and EM - NC PDFionuttomaNo ratings yet
- Mainboard 17MB120DSDocument64 pagesMainboard 17MB120DSatomo333No ratings yet
- HP ProLiant ML110 G7 DatasheetDocument4 pagesHP ProLiant ML110 G7 DatasheetDeepak Gupta (DG)No ratings yet
- Getting Started With Exchange Server 2013Document11 pagesGetting Started With Exchange Server 2013henriquecongoNo ratings yet
- Instrumentationtools Com PLC Program Water Level ControlDocument7 pagesInstrumentationtools Com PLC Program Water Level ControlAlex SalesNo ratings yet
- Scribner - 1988 - Investigation of The Collapse of L'Ambiance PlazaDocument22 pagesScribner - 1988 - Investigation of The Collapse of L'Ambiance PlazaLuciano GuttierrezNo ratings yet
- Libratherm 32-Channel Temperature ScannerDocument3 pagesLibratherm 32-Channel Temperature ScannerYogesh GowdaNo ratings yet
- Extract Text PDF GsviewDocument2 pagesExtract Text PDF GsviewAllanNo ratings yet
- M12L64164Document45 pagesM12L64164brahimNo ratings yet
- Introduction To DSA Chapter 1Document20 pagesIntroduction To DSA Chapter 1Abdiaziz Qabile100% (3)
- Can D500Document12 pagesCan D500Khaleel KhanNo ratings yet
- BSC6900 Commissioning ChecklistDocument6 pagesBSC6900 Commissioning ChecklistJorgIVariuSNo ratings yet
- Upgrade Database Using OEM 12C Cloud Control DBACLASSDocument9 pagesUpgrade Database Using OEM 12C Cloud Control DBACLASSVinod KumarNo ratings yet
- Milling machine cutter holding arborDocument100 pagesMilling machine cutter holding arborTempla KentNo ratings yet