Professional Documents
Culture Documents
Wireless Networked Security System Based On Zigbee
Uploaded by
khajarasool_skOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Wireless Networked Security System Based On Zigbee
Uploaded by
khajarasool_skCopyright:
Available Formats
Wireless Networked Security System Based on
ZigBee Technology
Liting Cao, Yanxia Liu and Shuo Yang
College of Automation
Beijing Union University
Beijing, China
caoliting0618@163.com
Abstract—The existing security systems show many shortcomings • It’s high energy-consuming system.
such as difficult to extend and severe time-consuming because it
is based on wiring network technology. In this paper, we present • The aftereffect is very serious if the cable be cut.
a wireless networked security system based on ZigBee technology.
Wireless sensor networks are the combinative production of
The system adopts hybrid topology structure based on cluster,
computer technology, communication technology and network
which consists of many micro-sensor nodes, network coordinator
nodes, network gateway (router), communication network and
technology. Wireless sensor networks are consisting of a great
monitor centre (computer). For short distance transmission, the lot of a large number of cheap micro-sensors which possess
micro-sensor nodes collect data from the monitoring surroundings computation function and communication function. The
and transmit to the gateway using ZigBee communication. For micro-sensors can real time monitor, apperceive and collect the
long distance transmission, from the gateway to the monitor environmental information [1].
centre, system uses TCP/IP protocol. The gateway in this system is ZigBee bend itself to realize a short distant double direction
the protocol conversion used to transform a data package in
wireless communication protocol which is lower complexity,
ZigBee protocol to TCP/IP protocol before transmitting. A
modified routing protocol based on LEACH is adopted in the
lower cost and lower speed. ZigBee works in three free
system. The simulation result shows that the modified LEACH frequency segments, they are 2.4 GHz allover international,
protocol has superiority on survival time. The wireless 868MHz in Europe and 915 MHz in America. It has many
micro-sensor can be scattered to the surroundings that human advantages such as safe data transmission, agile organization
unable enter. Then the sensor nodes self-organizing networked and long life when compared with the other wireless
security system and realize security monitor task. The system also communication technology.
can be used to forest fireproofing and environment pollution
In this paper, we present a security system based on
inspection after modification.
wireless sensor networks. In this system, ZigBee technology
Keywords-security system; wireless sensor networks; ZigBee which works in internatinal free freqency segment and
technology; hybrid network topology; LEACH routing arithmetic possesses self-orgnization function is adopted to solving the
problems existed in the existing security system. The structure
I. INTRODUCTION of system employs distributed structure, which consists of
many micro-sensor nodes, network coordinator nodes, network
Safety is the guarantee for the most essential existent of gateway (router), communication network and monitor centre
human beings. A security system is necessary for a building or (computer). For a short distance transmission, the micro-sensor
an area to guarantee the safety of the residents and property. nodes collect data from the monitoring surrounding and
The security system has gone through single-route monitor transmit to the gateway using ZigBee communication. For a
system, control loop monitor system, and processor plus long distance transmission, from the gateway to the monitor
multimedia monitor system eras in the past twenty years. The centre, system uses TCP/IP protocol. The gateway in this
digital monitor system which used abroad today is the fourth system is the protocol conversion used to transform a data
era production of the security system. It’s very annoying that package in ZigBee protocol to TCP/IP protocol before
all of the security systems show many shortcomings as follows. transmitting.
• The signals transmitted through cable network. Wiring The wireless micro-sensor can be scattered to the
network is a severe time-consuming and high-load surroundings that human unable enter. Then the sensor nodes
work, and it always blocks the progress of the self-organizing networked security system and realize security
engineering. monitor task. The system also can be used to forest fireproofing
and environment pollution inspection after modification.
• The information can be watched only in monitoring
chamber.
• It’s very difficult to extend system, because the wire
connection is fixed.
978-1-4244-2108-4/08/$25.00 © 2008 IEEE 1
Authorized licensed use limited to: VELLORE INSTITUTE OF TECHNOLOGY. Downloaded on August 2, 2009 at 01:54 from IEEE Xplore. Restrictions apply.
II. TOPOLOGY STRUCTURE OF SYSTEM B. Gateway Design
ZigBee network supports three network topology structure; The gateway is the protocol conversion based on transport
they are star network, mesh network and hybrid network layer. It’s used to connect more than one absolute network. It
(cluster network). can transform a data package in one kind protocol in another
kind protocol before transmitting.
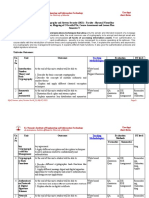
In this article, we took a hybrid network topology based on
cluster which is showed in Fig. 1[2]. The gateway in this system adopted modularization
scheme. It is made up of hardware layer, software layer and
application layer, which is showed in Fig.3. In the hardware
layer, hardware designing is described. In the software layer,
the kernel of real time operation system μC/OS- Ⅱ , the
protocols shed of ZigBee and TCP/IP are transplanted; so the
transition of protocols of ZigBee and TCP/IP is realized in
the software layer. In the application layer, the user can design
the application program according the need.
Figure 1. Topology structure of system.
In this network topology structure, the sensor nodes
delaminated into many layers. All nodes self-organized into
various absolute clusters, and one cluster head node will be
choose in every cluster, the other sensor nodes are non cluster
head nodes. The hybrid network topology based on cluster
possesses the distributing processing ability, and the cluster Figure 3. Structure of ZigBee gateway.
head node is just the distributing processing center. The cluster
head node with responsibility for controlling the non cluster The gateway is composed of ARM MPU S344B0X as its
head nodes in the same cluster, processing and fusion the data hardware core and some succinct periphery circuits. The
collected from non cluster head nodes, and then transforming hardware block diagram is showed in Fig.4. It consists of
the data to the coordinator directly or multi-hop via the other processing unit, storage unit, communication unit, display unit
cluster heads. and power support unit.
The hybrid network topology in this system has many
advantages. The long distance information exchange between
sensor nodes and coordinator and the complexity of
establishing the wireless network reduced.
III. HARDWARE DESIGN OF SYSTEM
The basis work in establishing a self-organizing wireless
sensor network is to design the hardware of network nodes.
A. Wireless Sensor Node Design
The wireless sensor node is a data-acquisition organ, which
used to acquire data in disunion forms from surroundings and
translate the data into unify data framework. The hardware
block diagram is showed in Fig.2. It consists of processing unit,
sensing unit, control unit, communication unit and power Figure 4. Block diagram of gateway.
support unit.
Embedded Microprocessor Unit (EMPU) is the hardware
core of embedded system. We select Samsung’s
S3C44B0X32-bit RISC microprocessor in this system depend
on the high ratio of quality and price.
S3C44B0X microprocessor is designed to provide a
Figure 2. Block diagram of wireless sensor node
cost-effective and high performance micro-controller solution
for hand-held devices and general applications.
978-1-4244-2108-4/08/$25.00 © 2008 IEEE 2
Authorized licensed use limited to: VELLORE INSTITUTE OF TECHNOLOGY. Downloaded on August 2, 2009 at 01:54 from IEEE Xplore. Restrictions apply.
We select Atmel’s AT45DCB008 as DataFlash in this energy of the network in each bout. The essential thought of
system. It has 36 sectors when work in double-bytes model. It’s this routing protocol is choosing the best number n of cluster
used to save the data in the case of network fault. head to ensure the lowest exhausting energy of the network in
each bout.
Hyundai’s HY57V641620 SDRAM is adopted in order to
running a embedded operating system. The capacitance of For the facility of calculating, we suppose that the number
HY57V641620 is 16x4Mbit,and the total width of data is of sensor nodes in each cluster is equal firstly. If the number of
8MB. sensor nodes is T , the number of cluster is N , and then the
number of sensor nodes in each cluster is T N .
The display device is SHARP’s LQ084V1DG21 LCD in
this system. The differentiate ratio is 640×480.
Realtek’s RTL8201BL is adopted as the PHY layer chip in
Ethernet communication. It’s a physical layer transceiver with ( 2 ⎛T ⎞
Ehead = k Estatic + ε ampdbroadcast + ⎜ − 1⎟kEstatic + )
single port. The Ethernet communication can be realized at ⎝N ⎠
10/100M. ⎛T ⎞
( 2
⎜ − 1⎟k E static + ε amp d head _ rcver + )
CC2420 is a RF transceiver that according with 2.4 GHz ⎝N ⎠
IEEE 802.15.4 and ZigBee standard produced by TI. CC2420
adopts O-QPSK modulate mode, and the work frequency wide (
k Estatic + ε amp d head _ rcver − 1
2
) ⑴
is 2.400-2.4835 GHz. The inception sensitivity is -94 dBm, and The exhausting energy of each cluster head node includes
it supports quickly meshing. the energy used to transmitting broadcast data package,
IV. ROUTING PROTOCOL incepting data packages from the other nodes, re- transmitting
the receipt data packages and transmitting its own data
There are many typical routing protocols for wireless package. It can be described as (1).
network based on hybrid topology structure, such as
LEACH[3](low energy adaptive clustering hierarchy), In ⑴, k is the data bytes of package transmitted and
PEGAGIS[4](power-efficient gathering in sensor information
system), TEEN[5](threshold sensitive energy efficient sensor
ε amp
incepted by sensor node; is the gain of signal amplifier;
network protocol), and so on. LEACH is a protocol system has d head _ rcver
power-efficient optimization. We adopted a modified routing is the furthest distant that can be covered by cluster
protocol based on LEACH. In the new protocol, the exhausting E
energy used to transmitting broadcast package was calculated head node; static are the energy exhausted by transmitting
when measuring the best number of cluster head that leaved out and incepting circuits which are equal in this pattern; and
by LEACH protocol. d head _ rcver
is the distant from the cluster head node to the
LEACH routing arithmetic includes distributed clustering coordinator
hierarchy, self-adaptive clustering arithmetic and alternation
arithmetic of cluster head position. Distributed clustering Meanwhile the exhausting energy of each non cluster head
hierarchy technology ensures the self-organizing of a large node in the same cluster includes the energy used to incepting
number of sensor nodes. In LEACH routing arithmetic, the broadcast data packages from N cluster head nodes and
operation is divided into some bout. It is begin with organizing transmitting its own data package. It can be described as ⑵.
cluster in one bout, and then is transmitting data from non
cluster head nodes to cluster head node and then to the
coordinator
(
Enon _ head = NkEstatic + k Estatic + ε amp d p _ head
2
) ⑵
The sensor nodes self-organized into disparate cluster, there d
In (2), p _ head is the distant from the non cluster head
has a node acted as cluster head in every cluster. All non node to the cluster head node.
cluster head nodes send their data to the cluster head node in
the same cluster, the cluster head node take charge of receiving [
E d p _ head
2
] can be described as ⑶ according to
all the data, doing some processes (such as data fusion), and reference [5].
transmitting the data to the coordinator The exhausting energy
is much more than the other non cluster head nodes. If the
cluster head node is changeless during the whole operation
[ 2
E d p _ head = ] M2
2πN
⑶
period, the limited energy of cluster head node will be So (2) can be rewrite as (4).
exhausted quickly and then it will not work anymore. As the
result, the other non cluster head nodes in the same cluster will ⎛ M2 ⎞
Enon _ head = NkE static + k ⎜⎜ Estatic + ε amp ⎟ ⑷
not work too. ⎝ 2πN ⎟⎠
A modified routing protocol based on LEACH is adopted in The exhausting energy of every cluster in each bout can be
this system. The measuring method of the best number of T
−1≈
T
cluster head is ameliorated in this routing protocol. The best described as (5) consideringN N .
number of cluster head is obtained by analyzing the exhausting
978-1-4244-2108-4/08/$25.00 © 2008 IEEE 3
Authorized licensed use limited to: VELLORE INSTITUTE OF TECHNOLOGY. Downloaded on August 2, 2009 at 01:54 from IEEE Xplore. Restrictions apply.
T package will be desert and the report will be sent to the monitor
Ecluster = E head + Enon _ head computer if the aim is not exist or communication failed.
N ⑸
Finally, the exhausting energy of whole network in each VI. EXPERIMENT
bout can be described as ⑹ deduced by above formulas. A simulation experiment environment of routing protocol
( )
designed by C++ was adopted in this system. According to the
2
Etotal = NEcluster = Nk Estatic + ε amp dbroadcast + convention of many references, we select 100 sensor nodes in
simulation. The simulation result in Fig. 6 shows that the
M2 survival time of modified LEACH protocol is longest, and the
TNkEstatic + kε amp +K number of bouts is most when the number of efficiency nodes
2πN ⑹ is 65. The system adopt modified LEACH protocol has
K is a constant irrespective to N in (6),so that the superiority on survival time, despite the outside factors which
can cause the node disable are ignored in this simulation.
best N can be determined by ⑺.
Tε amp M 2
N=
(
2π TEstatic + ε amp d broadcast
2
) ⑺
By choosing the best number n of cluster head to ensure
the lowest exhausting energy of the network in each bout and
the whole network. And the subsistence time of network
increased effectively.
V. DATA TRANSMISSION FLOW
In this system, the communication structure of monitor Figure 6. Simulation result of modified LEACH protocol.
centre (computer) and the sensor nodes is one host and
multi-slave. The data transmission flow is described as Fig. 5. VII. CONCLUSION
The intelligent security system designed in this paper
adopted wireless communication technology. The functions of
the system are presented as follows. Wireless remote control of
setting and withdrawing defense; remote operation and
monitor; self-organizing networked security system; it is
extended and movable, so especially suit for temporary task.
The system have many significant excellences, such as
networked, wireless, moveable, high-veracity and lower
energy-consuming. The using of embedded system improves
the stability of wireless data transmission. The system can be
applied to the hospital, the school the high speed way and
anywhere needed detect.
REFERENCES
[1] REN F Y, HUANG H N, LIN C, “Wireless sensor networks,” Journal of
Software, 14(7) , pp. 1282--1291, 2003
[2] YU Y, GOVINDAN R, ESTRIN D, “Geographical and Energy-Aware
Routing: a Recursive Data Dissemination Protocol for Wireless Sensor
Networks,” Rome, Italy: Proceedings of the Seventh Annual ACM/IEEE
Figure 5. Data transmission flow. International Conference on Mobile Computing and Networking
(MobiCom’01), pp. 85-96, 2001
The monitor computer sent command to the network [3] Heinzelman W, Chandrakasan A, Balakrishnanh, “An
Application-Specific Protocol Architecture for Wireless Micro sensor
gateway (router) via Internet. The router transmits the Networks,” IEEE Transactions on Wireless Communications, 1(4),
command to the aim coordinator node according to the routing pp.660-667, 2002.
table. The aim coordinator node awake the corresponding [4] LINDSEY S, RAGHAVENDRA C S. PEGASIS, “Power-Efficient
cluster head node by broadcasting the command to all cluster Gathering in Sensor Information Systems,” Proceedings of the IEEE
head nodes, and then the cluster head node awake the Aerospace Conference, pp.1125-1130, 2002.
corresponding sensor node by broadcasting the command to all [5] Manjeshwar A, Agrawal D. Teen, “A Routing Protocol for Enhanced
sensor nodes in the same cluster. The sensor node sent Efficiency in Wireless Sensor Networks,” Proceedings of the 15th
Parallel and Distributed Processing Symposium, pp.2009-2015, 2001.
information collect from surroundings to the cluster head node,
and then the cluster head node process and transmits the data
back to the monitor computer follow the former route. The
978-1-4244-2108-4/08/$25.00 © 2008 IEEE 4
Authorized licensed use limited to: VELLORE INSTITUTE OF TECHNOLOGY. Downloaded on August 2, 2009 at 01:54 from IEEE Xplore. Restrictions apply.
You might also like
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- IMP - Synchronization, Channel Estimation, and Equalization in MB-OfDM SystemsDocument12 pagesIMP - Synchronization, Channel Estimation, and Equalization in MB-OfDM Systemskhajarasool_skNo ratings yet
- Space Shift Keying Modulation For MIMO ChannelsDocument12 pagesSpace Shift Keying Modulation For MIMO Channelskhajarasool_skNo ratings yet
- Selective Level MappingDocument5 pagesSelective Level Mappingkhajarasool_skNo ratings yet
- Queueing Analysis For OFDM Sub Carrier AllocationDocument11 pagesQueueing Analysis For OFDM Sub Carrier Allocationkhajarasool_skNo ratings yet
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (400)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (345)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (121)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- w6100 Ethernet Shield Ds V100eDocument9 pagesw6100 Ethernet Shield Ds V100eLikitha Reddy100% (1)
- IEEE IoT Towards Definition Internet of Things Revision1 27MAY15Document86 pagesIEEE IoT Towards Definition Internet of Things Revision1 27MAY15Arun ThomasNo ratings yet
- Network - RepairedDocument157 pagesNetwork - RepairedNasir KhanNo ratings yet
- Routing Inter Vlan - Svi - DHCPDocument20 pagesRouting Inter Vlan - Svi - DHCPĐinh TúNo ratings yet
- Networking & TCP IPDocument2 pagesNetworking & TCP IPGuruKPONo ratings yet
- Spek RohillDocument5 pagesSpek RohillRiky FitriadiNo ratings yet
- Training Course 5g Sa ArchitectureDocument39 pagesTraining Course 5g Sa ArchitectureHilal LakhbatNo ratings yet
- ME440 Handheld Power Analyzer Modbus Tcp/Ip Communication ProtocolDocument21 pagesME440 Handheld Power Analyzer Modbus Tcp/Ip Communication ProtocolLuis GonzalezNo ratings yet
- Section 13730 Security Access Part 1Document132 pagesSection 13730 Security Access Part 1jacksondcplNo ratings yet
- Niagara Workbench Guide-LITEDocument63 pagesNiagara Workbench Guide-LITEAbsolute Media HydNo ratings yet
- NotaDocument29 pagesNotaJavier Soto LedezmaNo ratings yet
- Lecture 2Document14 pagesLecture 2clely fernandesNo ratings yet
- Chapter 1 Introduction To Data CommunicationsDocument4 pagesChapter 1 Introduction To Data Communicationslalitha88% (8)
- Cryptography and System Security: K J Somaiya Institute of Engineering and Information TechnologyDocument11 pagesCryptography and System Security: K J Somaiya Institute of Engineering and Information TechnologyWhatNo ratings yet
- Quick Setup Guide: Altai C1N Super Wifi CpeDocument8 pagesQuick Setup Guide: Altai C1N Super Wifi CpeMd. Mannan sikder ronyNo ratings yet
- Larscom Access-T User ManualDocument338 pagesLarscom Access-T User ManualtimttyNo ratings yet
- Unicast Routing Protocols: Rip, Ospf, and BGPDocument82 pagesUnicast Routing Protocols: Rip, Ospf, and BGPYazanAlomariNo ratings yet
- CSE 5G Technology Report PDFDocument42 pagesCSE 5G Technology Report PDFSamarth SnehNo ratings yet
- GB0-191 Exam Syllabus For The Constructing Small - and Medium-Sized Enterprise Networks V7.0Document5 pagesGB0-191 Exam Syllabus For The Constructing Small - and Medium-Sized Enterprise Networks V7.0deryNo ratings yet
- SG7000 V200R005 Function DescriptionsDocument37 pagesSG7000 V200R005 Function DescriptionsShara Jamal100% (1)
- Configuring A Full Fledged "Red Hat Enterprise Linux Server"Document36 pagesConfiguring A Full Fledged "Red Hat Enterprise Linux Server"ronald_123No ratings yet
- TCP/IP Protocol Suite:: 25.1 Review QuestionsDocument2 pagesTCP/IP Protocol Suite:: 25.1 Review QuestionsOso PolNo ratings yet
- What Is Network DiagramDocument7 pagesWhat Is Network DiagramOundo SamNo ratings yet
- High Performance Kernel Mode Web Server For WindowsDocument57 pagesHigh Performance Kernel Mode Web Server For WindowsPufos_Carol_4281No ratings yet
- Izar Center Usermanual enDocument52 pagesIzar Center Usermanual enStefano SerafiniNo ratings yet
- CJ1W-ETN21: Organically Connect The Production Site and ManagementDocument8 pagesCJ1W-ETN21: Organically Connect The Production Site and ManagementTonyNo ratings yet
- Interview Questions 2023Document12 pagesInterview Questions 2023Mahesh KumarNo ratings yet
- Chapter One (History and Overview)Document36 pagesChapter One (History and Overview)mesfinNo ratings yet
- Diploma Examination, 2011: 130. Logic and Distributed Control SystemDocument5 pagesDiploma Examination, 2011: 130. Logic and Distributed Control SystemMuthuLakshmi RajendranNo ratings yet
- 7 Common Network Issues and How To Resolve Them Fast CBT NuggetsDocument11 pages7 Common Network Issues and How To Resolve Them Fast CBT NuggetsFree TingzNo ratings yet