Professional Documents
Culture Documents
598 3156 1 PB
Uploaded by
stephenlim7986Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
598 3156 1 PB
Uploaded by
stephenlim7986Copyright:
Available Formats
Institute of Advanced Engineering and Science
International Journal of Information & Network Security (IJINS)
Vol.1, No.4, October 2012, pp. 313~320
ISSN: 2089-3299
313
Novel Cipher Technique Using Substitution Method
Shobha Vatsa, Tanmeya Mohan, A. K. Vatsa
Shobhit University, Meerut, U.P., INDIA
Article Info
ABSTRACT
Article history:
Cryptography plays a very vital role in the field of Network Security. It is a
complex and mathematically challenging field of study. Always there exists a
need for confidentiality and integrity of all information being transmitted on
the network that is very important for certain communicating parties. The
data being transmitted needs to be kept secure and out of reach for
unauthorized access. In this paper, we propose a new symmetric substitution
cipher technique using a mechanism on vowel, consonants of English
language and numeric digits, which exploits the disadvantages of the
symmetric substitution techniques previously known to us. Also certain new
aspects of encryption and decryption have been explored.
Received Jun 05th, 2012
Revised Jul 30th, 2012
Accepted Aug 28th, 2012
Keyword:
Vowels,
Consonants,
Substitution cipher,
Cryptography,
Security.
Copyright @ 2012 Institute of Advanced Engineering and Science.
All rights reserved.
Corresponding Author:
First Author,
Shobhit University, Meerut, U.P., INDIA.
Email: shobha778@gmail.com
1.
INTRODUCTION
In this age of universal electronic connectivity, of viruses and hackers, of electronic eavesdropping
and electronic fraud, there is indeed no time at which security does not matter. The explosive growth in
computer systems and their interconnection via network has increased the dependence of both organizations
and individuals on the information stored and communicated using these systems which intern has led to a
heightened awareness of the need to protect data and resources from disclosure, to guarantee the authenticity
of data and messages, and to protect systems from network-based attacks.
Also the disciplines of cryptography and network security have matured, leading to the development
of practical, readily available applications to enforce network security. Cryptography is the design of certain
techniques for ensuring the secrecy and/or authenticity of information. Earlier the requirement of information
security within an organization was primarily provided by physical and administrative means [1]. But the
concept of network security became quite evident with the introduction of computers and later with
introduction of distributed systems. The need of cryptographic algorithm is to avoid threat to integrity,
confidentiality and availability.
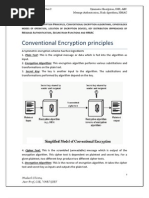
Symmetric Cipher Technique is also known as Conventional, Single key, Secret Key, One key and
classical encryption techniques. This technique is based on the encryption of plain-text to cipher-text which is
safe to transmit and from unauthorized access, by using a secret key in a specific encryption algorithm.
It uses the following ingredients:
a. Plain-text: This in an intelligible piece of information i.e. original text that needs to transferred safely to
the receiver. It is the main input to the encryption algorithm.
b. Secret Key: This is another input to the encryption and decryption algorithm, which is the main component
used for converting the plain-text to cipher-text i.e. an unintelligible form which has the useful content
hidden in a way.
Journal homepage: http://iaesjournal.com/online/index.php/ IJINS
w w w . i a e s j o u r n a l . c o m
314
ISSN: 2089-3299
c. Encryption Algorithm: This is the actual process by which we are converting the plain-text into ciphertext.
d. Cipher-text: This is the output of encryption process in which we are taking plain-text and secret key as
input and processed by encryption algorithm. The cipher-text can be understood as a scrambled piece of text
which has useful information in secret form.
e. Decryption Algorithm: This algorithm is the reverse of the encryption algorithm which takes in cipher-text
and secret key as inputs and produces plain-text as the output.
The receiver on receipt of this unintelligible text, called cipher-text uses the secret key and with the
decryption algorithm extracts the useful hidden information sent by the source. the process is depicted in
figure 1.1. The secret key can either be shared between the source and destination by a secure channel or by a
trusted third party. The requirements for secure use of conventional encryption are that the opponent should be
unable to decrypt cipher-text or discover the key even if he/she is in possession of a number of cipher-texts
together with the plain-text that produced each cipher-text. Also the sender and receiver must have obtained
copies of the secret key in a secure fashion and must keep the key secure. With the use of symmetric
encryption, the principal security problem is maintaining the secrecy of the key.
Figure 1: Model of Conventional Cryptosystem
A substitution technique is one in which the letters of plain-text are replaced by letters or numbers
or symbols. If plain-text is viewed as a sequence of bits, then substitution involves replacing plain-text bit
patterns with cipher-text bit patterns. The substitution technique either involves single alphabet replacement or
multiple alphabet replacements, respectively known as mono-alphabetic substitution technique and polyalphabetic substitution technique.
Mono-alphabetic substitution is a system of encryption where every occurrence of a particular plaintext letter is replaced by a cipher-text letter. the definition of a monoalphabetic substitution allows for the
possibility that two distinct plain-text letters are replaced by the same cipher-text letter. However, to break this
system using a known plain-text attack, we will require that any two distinct plain-text letters are replaced by
two distinct cipher-text letters [2]. The Monoalphabetic Cipher (often referred to as a cryptogram) uses a KEY
which is the rearrangement of the letters of the alphabet. These different letters are then substituted for the
letters in the message to create a secret message. That KEY is needed to decipher the secret message [3]. A
monoalphabetic substitution is one where a letter of plain-text always produces the same letter of cipher-text.
The simplest examples of monoalphabetic substitutions are probably the Caesar Cipher and Atbash [4]. The
problem with messages encrypted with a monoalphabetic substitution cipher is that it is very easy to break
using frequency analysis [5].
In polyalphabetic substitution the cleartext letters are enciphered differently depending upon their
placement in the text. As the name polyalphabetic suggests this is achieved by using several cryptoalphabets
instead of just one, as is the case in most of the simpler crypto systems. Which cryptoalphabet to use at a given
time is usually guided by a key of some kind, or the agreement can be to swich alphabet after each word
encrypted (which, of course, presumes that the word boundaries are kept intact or indicated in some way), but
the latter is seldom practiced in real life [6]. Polyalphabetic substitution ciphers are useful because they are
less easily broken by frequency analysis, however if an attacker knows for instance that the message has a
IJINS Vol. 1, No. 4, October 2012 : 313 320
IJINS
ISSN: 2089-3299
315
period n, then he simply can individually frequency analyze each cipher alphabet. The number of letters
encrypted before a polyalphabetic substitution cipher returns to its first cipher alphabet is called its period. The
larger is the period, the stronger is the cipher. Of course, this method of encryption is certainly not secure by
any definition and should not be applied to any real-life scenarios [7].
On basis of literature review the following problem identified with all other available substitution
techniques codes can be broken either by means of brute force or character frequencies or by another way of
cryptanalysis. Therefore, the purposed cipher technique is efficient and secure symmetric substitution cipher
technique using a mechanism on vowel and consonants of alphabets, which exploits the disadvantages of the
symmetric substitution techniques previously known to us. Also certain new aspects of encryption and
decryption have been explored. It has been analyzed that there are two types of cryptanalysis attacks namely
Brute-Force cryptanalysis, and Relative frequency analysis. In cryptography, a brute force attack or exhaustive
key search is a strategy that can in theory be used against any encrypted data by an attacker who is unable to
take advantage of any weakness in an encryption system that would otherwise make his task easier. It involves
systematically checking all possible keys until the correct key is found. In the worst case, this would involve
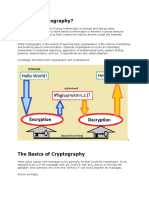
traversing the entire search space [21]. Frequency analysis is a methodology for "breaking" simple
substitution ciphers, like the Caesar cipher. These ciphers replace one letter of the plain-text with another to
produce the cipher-text, and any particular letter in the plain-text will always, in the simplest and most easily
breakable of these cyphers, turn into the same letter in the cipher. Frequency analysis as shown in figure 1.2, is
based on the fact that certain letters, and combinations of letters, appear with characteristic frequency in
essentially all texts in a particular language [22].
Relative frequency
14
12
10
8
6
4
2
0
A B C D E F G H I J K L M N O P Q R S T U V W X Y Z
Figure 2. Relative frequency in English alphabets
This paper is organized into sections, introduction section familiarizes us to the basics of network
security, and previously known techniques. It also emphasizes on the problem identification, due to the
disadvantages of earlier known cipher techniques. The two cryptanalysis attacks have been discussed. The
next section describes the related work that has been discovered by many scholars in the field of cryptography
like Caesar cipher, Play Fair cipher, Hill cipher, Poly-alphabetic cipher, One time padding, Homophonic
cipher and Aryabhatas Mathematics. Next is a detailed description of the algorithm that is being proposed in
this paper with an example of the entire encryption and decryption process followed by conclusion of this
paper and future scope. The related references have also been mentioned.
2.
RESEARCH METHOD
The algorithm proposed in this paper uses some earlier proposed techniques and is based on some
cryptographic facts. The following section describes the similar work proposed earlier and the facts on which
it is based. Caesar Cipher is One of the simplest examples of a substitution cipher is the Caesar cipher, which
is said to have been used by Julius Caesar to communicate with his army. Caesar is considered to be one of the
first persons to have ever employed encryption for the sake of securing messages. Caesar decided that shifting
each letter in the message would be his standard algorithm, and so he informed all of his generals of his
Novel Cipher Technique Using Substitution Method (Shobha Vatsa)
316
ISSN: 2089-3299
decision, and was then able to send them secured messages. The Caesar cipher is a shift cipher since the
cipher-text alphabet is derived from the plain-text alphabet by shifting each letter a certain number of spaces.
To encipher a message, we perform a simple substitution by looking up each of the message's letters in the top
row and writing down the corresponding letter from the bottom row [9].
Play Fair Cipher, Despite its invention by Wheatstone, became known as the Play fair cipher
after Lord Playfair, who heavily promoted its use. The Playfair cipher uses a 5 by 5 table containing a key
word or phrase. Memorization of the keyword and 4 simple rules was all that was required to create the 5 by
5 table and use the cipher. To generate the key table, one would first fill in the spaces in the table with the
letters of the keyword (dropping any duplicate letters), then fill the remaining spaces with the rest of the
letters of the alphabet in order (usually omitting "Q" to reduce the alphabet to fit, other versions put both "I"
and "J" in the same space). The key can be written in the top rows of the table, from left to right, or in some
other pattern, such as a spiral beginning in the upper-left-hand corner and ending in the centre. The keyword
together with the conventions for filling in the 5 by 5 table constitutes the cipher key [10].
Hill Cipher, In classical cryptography, is a polygraphic substitution cipher based on linear algebra.
Invented by Lester S. Hill in 1929, it was the first polygraphic cipher in which it was practical (though
barely) to operate on more than three symbols at once. Each letter is first encoded as a number. Often the
simplest scheme is used: A = 0, B =1, ..., Z=25, but this is not an essential feature of the cipher. A block
of n letters is then considered as a vector of n dimensions, and multiplied by an n n matrix, modulo 26. (If
one uses a larger number than 26 for the modular base, then a different number scheme can be used to encode
the letters, and spaces or punctuation can also be used.) The whole matrix is considered the cipher key, and
should be random provided that the matrix is invertible in
(to ensure decryption is possible) [12]. A
Hill cipher is another way of working out the equation of a matrix [11].
A polyalphabetic cipher is any cipher based on substitution, using multiple substitution alphabets.
The Vigenre cipher is probably the best-known example of a polyalphabetic cipher, though it is a simplified
special case. The Enigma machine is more complex but still fundamentally a polyalphabetic substitution
cipher [13]. Polyalphabetic substitution cipher designers seem to have concentrated on obscuring the choice
of a few such alphabets (repeating as needed), not on the increased security possible by using many and
never repeating any [14]. The Alberti cipher by Leon Battista Alberti around 1467 was believed to be the first
polyalphabetic cipher. Alberti used a mixed alphabet to encrypt a message, but whenever he wanted to, he
would switch to a different alphabet, indicating that he had done so by including an uppercase letter or a
number in the cryptogram [15].
The one-time pad (OTP) is a type of encryption, which has been proven to be impossible to crack if
used correctly. Each bit or character from the plain-text is encrypted by a modular addition with a bit or
character from a secret random key (or pad) of the same length as the plain-text, resulting in a cipher-text. If
the key is truly random, as large as or greater than the plain-text, never reused in whole or part, and
kept secret, the cipher-text will be impossible to decrypt or break without knowing the key [16]. The two
main problems in one time padding are key distribution and true randomness. Distributing very long one-time
pad keys is inconvenient and usually poses a significant security risk. Also high-quality random numbers are
difficult to generate. The random number generation functions in most programming language libraries are
not suitable for cryptographic use [17].
Figure 3: A simple homophonic substitution cipher
IJINS Vol. 1, No. 4, October 2012 : 313 320
IJINS
ISSN: 2089-3299
317
A homophonic cipher is a substitution cipher in which a character may have any of a number of
different representations. Figure 1.3 gives one such cipher and a sample message using it [18]. The
Homophonic Substitution Cipher involves replacing each letter with a variety of substitutes, the number of
potential substitutes being proportional to the frequency of the letter. The point of offering several
substitution options for popular letters is to balance out the frequencies of symbols in the cipher-text [19]. It
can also be defined as a venerable technique for converting a clear-text sequence into a random sequence
[20].
Aryabhatas Mathematics, A small resemblance of this new cipher technique has been found in
research paper presented as Aryabhatas Mathematics. Vatsyayanas Kama-sutra describes cryptographic
writing as mlecchita-viklapa. In his commentary on the Kama-sutra, Yasodhara describes two kinds of this
writing:
Kautiliyam. In this letter substitutions are based on phonetic relations, such as vowels becoming
consonants. A simplification of this form is called durbodha.
Muladeviya. Its cipher alphabet consists of pairing letters and using the reciprocal ones:
a kh gh c t n r l y
kgpmss
with all the other letters remaining unchanged. These codes can serve as sub-units in cryptographic
transformations [8].
3.
PROPOSED WORK
It is discussed in following steps.
[Step I] This algorithm uses a key which comprises of two parts:
a. A 5-digit key- This part of the key contains numeric digits {1,2,3,4,5} arranged in some random
order. This part of the key is used for further arrangements if substitution matrices.
b. A keyword- This part of the key either contains the keyword UP or DOWN. UP refers
previous and DOWN refers next.
[Step II] The arrangement of the numeric digits, intern forms two more keys, one is the arrangement
of vowels {a,e,i,o,u} and the numbers {6,7,8,9,0} in the same sequence as that of the key
digits. Ex. If the key digit is 53142, then the other two keys become u i a o e and
08697.
[Step III] The consonant Z is never included in any encryption-decryption procedure.
[Step IV] The existence of keyword UP indicates that the consonants occurring previous to
vowels are not included in matrix formation for encryption-decryption procedure, upon
considering the alphabets to be connected in a circular manner. So UP means that
consonants Y,D,H,N&T are not included in matrix formations.
[Step V] The existence of keyword DOWN indicates that the consonants occurring next to vowels
are not included in matrix formation for encryption-decryption procedure, upon
considering the alphabets to be connected in a circular manner. So DOWN means that
consonants B,F,J,P&V are not included in matrix formations.
[Step VI] The matrices for vowel-to-consonant encryption/decryption are formed as under:
A
B
K
R
A
C
L
S
For keyword UP
E I
O U
C F G J
L
M P
Q
S
V W X
For keyword DOWN
E
I
O U
D
G
H K
M
N
Q R
T
W X Y
Novel Cipher Technique Using Substitution Method (Shobha Vatsa)
318
ISSN: 2089-3299
[Step VII] The above matrices are used is a special way. To avoid same substitution for each vowel,
the nth occurrence of a vowel in a plain-text is replaced by nth consonant lying beneath
that vowel in its column. That means for keyword UP, the 1 st occurrence of a in
plain-text is replaced by the consonant b; 2nd occurrence is replaced by the consonant
k; 15th occurrence is replaced by the consonant r; and so on. Similar procedure is
followed for keyword DOWN.
[Step VIII] For consonant-to-vowel encryption/decryption, the three keys mutually constructed,
comprising of two sets of digits and one set of vowels are used in following way:
For keyword UP
B
C
F
G
5
3
1
4
J
2
K
0
L
8
M
6
P
9
Q
7
R
U
S
I
T
A
W
E
X
O
For keyword DOWN
C
D
G
H
5
3
1
4
K
2
L
0
M
8
N
6
Q
9
R
7
S
U
T
I
W
A
X
E
Y
O
4. RESULTS
Plain-text: meet me after the toga party
Secret key: 53142 UP
Encryption Phase:
Step 1: The occurrence of vowels is numbered as follows:
M
E
1
E
2
E
3
E
4
E
5
A
1
A
2
A
3
O
1
Step 2: The vowels are converted to consonants as follows:
M
E
C
E
L
E
S
E
C
E
L
A
B
A
K
A
R
O
G
H
H
T
T
G
4
P
9
R
U
T
T
Y
Y
H
H
E
L
T
T
O
G
G
4
A
K
P
9
A
R
R
U
T
T
Y
Y
Step 3: The consonants are converted to vowels as follows:
M
6
T
T
M
6
F
1
T
T
R
U
T
T
Step 4: So the cipher-text produced equivalent to plain-text is:
M
6
E
C
E
L
T
T
M
6
E
S
A
B
F
1
T
T
E
C
R
U
T
T
PLAIN-TEXT:
MEET ME AFTER THE TOGA PARTY
CIPHER-TEXT: 6CLT 6S B1TCU THL TG4K 9RUTY
IJINS Vol. 1, No. 4, October 2012 : 313 320
IJINS
ISSN: 2089-3299
319
Step 5: The above generated cipher-text is sent to the receiver after omitting all the spaces.
Cipher-text sent: 6CLT6SB1TCUTHLTG4K9RUTY
Decryption Phase:
Cipher-text: 6CLT6SB1TCUTHLTG4K9RUTY
Secret key: 53142 UP
Step 1: The cipher-text is analyzed for consonants first and consonants to vowel conversion is done as
follows:
6
C
E
L
E
S
E
B
A
C
E
L
E
G
O
K
A
R
A
Step 2: The cipher-text is the analyzed for vowels and digits to convert them to consonants as follows:
6
M
6
M
1
F
U
R
4
G
9
P
U
R
Step 3: The cipher-text is the analyzed for those consonants that are not allowed to participate in the
encryption/decryption process as follows:
6
T
T
T
T
T
T
H
H
T
T
T
T
Y
Y
R
A
U
R
T
T
Y
Y
Step 4: The results from above three steps are combined to obtain the plain-text as follows:
6
M
C
E
L
E
T
T
6
M
S
E
B
A
1
F
T
T
C
E
U
R
T
T
H
H
L
E
T
T
G
O
4
G
K
A
9
P
Plain-text computed: meetmeafterthetogaparty
The above plain-text obtained at the receivers end upon decryption can be easily read and
understood by the human brain.
5.
Conclusion
In this paper after analyzing the different existing symmetric substitution cipher techniques and their
disadvantages, The proposed new cipher technique which is quite secure and efficient. The technique is
indifferent to Brute Force attack and Relative Frequency attack. This algorithm may hold a wide usage for
commercial and low scale purposes depending upon the cost of implementing the algorithm.
FUTURE WORK
With the literature review and study of all substitution techniques known to us, we found some
problems that have been solved to some extent by our proposed algorithm. Certain aspects have still been left
for future extension, as both the cipher-text and the plain-text skip on blank spaces, so a convention may be
developed to handle the occurrence of spaces. The algorithm is based on the position wise occurrence of each
vowel, so it may be difficult to keep track of their position in large text. So the usage of this algorithm is
confined to small pieces of text. A convention for encrypting numbers and symbols may be developed, since
no such mechanism has been implemented presently in this algorithm.
REFERENCES
[1] William Stallings, Cryptography and Network Security, Fourth Edition, Pearson Education.
[2] http://math.ucsd.edu/~crypto/java/EARLYCIPHERS/Monoalphabetic.html
[3] http:// www.secretcodebreaker.com/scbsolvr.html
[4] http://www.murky.org/blg/2004/09/monoalphabeticsubstitution/everything2.com/title/monoalphabetic+substitution
[6] http:// www.cvni.net/radio/nsnl/nsnl010/nsnl10poly.html
[7] http:// en.wikibooks.org/wiki/Cryptography/Polyalphabetic_substitution
[8] http:// Aryabhatas Mathematics by Subhash Kak, RSA Conference, San Jose, Feb. 13-17, 2006
[9] Chris Savarese and Brian Hart, The Caesar Cipher, Trinity College,Last updated: Mon, 26 Apr 2010 02:46:57 GMT
Novel Cipher Technique Using Substitution Method (Shobha Vatsa)
320
ISSN: 2089-3299
[10] Smith, Michael, Station X: The Codebreakers of Bletchley Park, Channel 4 Books/Macmillan, London) ISBN 0
7522 2189 2, 1998.
[11] Lester S. Hill, Cryptography in an Algebraic Alphabet,The American Mathematical Monthly, Vol. 36, No. 6. (Jun.
- Jul., 1929), pp. 306-312.
[12] http://en.wikipedia.org/wiki/Hill_cipher
[13] http://en.wikipedia.org/wiki/Polyalphabetic_cipher
[14] Helen Fouch Gaines, "Cryptanalysis", Dover. ISBN 0-486-20097-3, 1939.
[15] Leon Battista Alberti, A. Zaccagnini, A Treatise on Ciphers, trans,Torino 1997.
[16] Erskine, Ralph, "Enigma's Security: What the Germans Really Knew", in "Action this Day", pp 370386, 2001.
[17] http://en.wikipedia.org/wiki/One-time_pad#Key_distribution
[18] F. A. Stahl, "A homophonic cipher for computational cryptography," afips, pp.565, 1973 Proceedings of the
National Computer Conference, 1973
[19] http://www.simonsingh.net/The_Black_Chamber/homophoniccipher.htm
[20] valdemar c. rocha jr, cid b. Dearajo, Homophonic Substitution,Departamento de Eletrnica e Sistemas, UFPE,
Recife, PE, Brazil.
[21] http://en.wikipedia.org/wiki/Brute_force_attack
[22] http://en.wikibooks.org/wiki/Cryptography/Frequency_analysis
BIOGRAPHY OF AUTHORS
Shobha Vatsa obtained her M.Tech in Computer Engineering from Shobhit University,
Meerut (U.P). and MCA from U.P. Technical University, Lucknow, (U.P). She has
conducted various events and seminars. She has attended several seminars, workshops
and National conferences. Her area of research include Data mining, MANET (Mobile
adhoc Network), Network security, Web Crawler, Software Engineering, DBMS.
Avimanyou Kumar Vatsa is working as Assistant Professor and Coordinator - CSE
at Shobhit University, Meerut, (U.P.), INDIA. He obtained his M-Tech (Computer
Engineering) with Hons. from Shobhit University and B-Tech(I.T.) from V.B.S.
Purvanchal University, Jaunpur (U.P.). He has worked as software engineer in
software industry. He has been in teaching from more than one decade. During this
short period of time, he has been supervised several dissertation of M.Tech. students.
He is on the editorial board and reviewers of several international and national
journals in networks and security field. He has been member of several academic and
administrative bodies. During his teaching he has been coordinated many Technical fests and National
Conferences at Institute and University Level. He has attended several seminars, workshops and
conferences at various levels. His many papers are published in various national, international journals and
conferences. His area of research includes MANET (Mobile Ad-Hoc network), Network Security,
Congestion Control and VOIP-SIP (Voice over IP).
Tanmeya Mohan was Bachelor of Technology in Computer Engineering at the School
of Computer Engineering & Information Technology, Shobhit University, Meerut.
Presently working as software engineer in software industry.
IJINS Vol. 1, No. 4, October 2012 : 313 320
You might also like
- IT General Control Audit ProgramDocument20 pagesIT General Control Audit ProgramMohamad JbrNo ratings yet
- Demo Company - Security Assessment Findings ReportDocument14 pagesDemo Company - Security Assessment Findings ReportShashankRaghavNo ratings yet
- Nomenclatura - Encyclopedia of modern Cryptography and Internet Security: From AutoCrypt and Exponential Encryption to Zero-Knowledge-Proof Keys [Paperback]From EverandNomenclatura - Encyclopedia of modern Cryptography and Internet Security: From AutoCrypt and Exponential Encryption to Zero-Knowledge-Proof Keys [Paperback]No ratings yet
- Network Design and Security ManagementDocument52 pagesNetwork Design and Security ManagementmehraDpaNo ratings yet
- Network Security VAPT ChecklistDocument7 pagesNetwork Security VAPT ChecklistvybiNo ratings yet
- Cryptography Course WorkDocument27 pagesCryptography Course WorkSovan PalNo ratings yet
- Mini Project ReportDocument11 pagesMini Project ReportKiran BogamNo ratings yet
- Chapter 3 Encryption Principles and AlgorithmsDocument25 pagesChapter 3 Encryption Principles and AlgorithmsHiziki TareNo ratings yet
- Cryptography AssignmentDocument7 pagesCryptography Assignmentarijitsinha99No ratings yet
- Symmetric Encryption, DES, AES, MAC, Hash Algorithms, HMACDocument76 pagesSymmetric Encryption, DES, AES, MAC, Hash Algorithms, HMACMukesh86% (7)
- U21CS601 CT Unit 123 Part B QADocument13 pagesU21CS601 CT Unit 123 Part B QASanthosh kannaNo ratings yet
- Chapter 2 & 3Document20 pagesChapter 2 & 3Yakubu AliuNo ratings yet
- CS8792 CNS Two Marks Questions With AnswersDocument15 pagesCS8792 CNS Two Marks Questions With Answerslavanyaraju4985No ratings yet
- Secret MessagingDocument45 pagesSecret MessagingAsha SumithaNo ratings yet
- NSC Unit - 1 - 221218 - 100945Document19 pagesNSC Unit - 1 - 221218 - 100945SurenderNo ratings yet
- Encryption StandardsDocument76 pagesEncryption Standardsbhasker7100% (1)
- Cryptography and Network SecurityDocument13 pagesCryptography and Network SecurityNagendra KumarNo ratings yet
- Report PDFDocument35 pagesReport PDFPramod KumarNo ratings yet
- IT1352 Cryptography and Network SecurityDocument29 pagesIT1352 Cryptography and Network SecurityVishnupriya OmprakashNo ratings yet
- Bca505 NotesDocument55 pagesBca505 NotesShubhamNo ratings yet
- Ijettcs 2014 08 25 137Document6 pagesIjettcs 2014 08 25 137International Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- MCA41Document2 pagesMCA41SK TecHPortNo ratings yet
- Lecture 2 CryptographyDocument10 pagesLecture 2 Cryptographyxtviper33No ratings yet
- NSC Word All Unit QBDocument45 pagesNSC Word All Unit QByuvaraaj aletiNo ratings yet
- Is Lab ManualDocument114 pagesIs Lab ManualprathamgunjNo ratings yet
- Cubical CrytographyDocument6 pagesCubical CrytographyAkanksha RaoNo ratings yet
- Unit - Ii: Traditional Symmetric-Key CiphersDocument124 pagesUnit - Ii: Traditional Symmetric-Key Cipherssanthosh RNo ratings yet
- Latest Paper On CryptographyDocument14 pagesLatest Paper On Cryptographysundarrajan1068100% (7)
- Ch3 CryptoDocument90 pagesCh3 CryptoArif AbdulelamNo ratings yet
- Cryptography and Network Security Two Marks Unit-1 Network Security 1. Specify The Four Categories of Security Threads?Document11 pagesCryptography and Network Security Two Marks Unit-1 Network Security 1. Specify The Four Categories of Security Threads?PiriyangaNo ratings yet
- Chapter 3 FinalDocument80 pagesChapter 3 FinalMihretu BekeleNo ratings yet
- Topic: Network Security CRYPTOGRAPHY (One of Its Possible Solution)Document9 pagesTopic: Network Security CRYPTOGRAPHY (One of Its Possible Solution)api-19799369No ratings yet
- Business Mathematics 1Document5 pagesBusiness Mathematics 1Mohit SharmaNo ratings yet
- Unit 3Document47 pagesUnit 3Andualem BegunoNo ratings yet
- Ijret - Enhancing Security of Caesar Cipher Using Different MethodsDocument6 pagesIjret - Enhancing Security of Caesar Cipher Using Different MethodsInternational Journal of Research in Engineering and TechnologyNo ratings yet
- Is PTSSSS: AxssanboyDocument3 pagesIs PTSSSS: AxssanboyCabdi Fitaax KulmiyeNo ratings yet
- Computer Security: Computer Threats and EncryptionDocument21 pagesComputer Security: Computer Threats and EncryptionPro NebyuNo ratings yet
- Ijett V4i5p155Document5 pagesIjett V4i5p155VinitKharkarNo ratings yet
- 8920731afc1f33f15f9ba1311ba02babDocument35 pages8920731afc1f33f15f9ba1311ba02babKamrul HasanNo ratings yet
- Computer Security AsDocument4 pagesComputer Security AsHagos gebreslasieNo ratings yet
- Notes of Unit-1 Information SecurityDocument18 pagesNotes of Unit-1 Information SecurityAbhishek NarwariyaNo ratings yet
- What Is Cryptography?: Cryptography Is The Science of Using Mathematics To Encrypt and Decrypt DataDocument10 pagesWhat Is Cryptography?: Cryptography Is The Science of Using Mathematics To Encrypt and Decrypt Datadivya6990No ratings yet
- Security TechnologyDocument8 pagesSecurity Technologyangelica perezNo ratings yet
- Implementation of Aes and Blowfish AlgorithmDocument4 pagesImplementation of Aes and Blowfish AlgorithmInternational Journal of Research in Engineering and TechnologyNo ratings yet
- Tugas Kelompok Teknologi Artificial Intelligence PresentasiDocument35 pagesTugas Kelompok Teknologi Artificial Intelligence PresentasiInas Rahma AlifiaNo ratings yet
- Information Security: By: Muhammad HanifDocument20 pagesInformation Security: By: Muhammad HanifMuhammad UsmanNo ratings yet
- CryptographyDocument7 pagesCryptographyZonia NillNo ratings yet
- New Security Lectures FinallyDocument87 pagesNew Security Lectures Finallyطيبه محمد احمد حمد هندسة تقنيات الحاسوبNo ratings yet
- ECCDocument39 pagesECCYashwanth ReddyNo ratings yet
- Midterm Assignment 101016653Document6 pagesMidterm Assignment 101016653vasanthmeNo ratings yet
- Unit IDocument24 pagesUnit IPapithaNo ratings yet
- Question Paper With Some ProjectsDocument37 pagesQuestion Paper With Some ProjectsBASHYAM PNo ratings yet
- Cryptography and Network Security - Test - 1 - R177219023Document4 pagesCryptography and Network Security - Test - 1 - R177219023singhal9549akashNo ratings yet
- Types of CiphersDocument9 pagesTypes of CiphersEng-Mushtaq HejairaNo ratings yet
- Various Ciphers in Classical CryptographyDocument8 pagesVarious Ciphers in Classical CryptographySHAURYA SINGHNo ratings yet
- Image Masking and Compression Using User Private Key GenerationDocument5 pagesImage Masking and Compression Using User Private Key GenerationInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- The Art of Cryptography - RespDocument24 pagesThe Art of Cryptography - RespIgorJalesNo ratings yet
- Unit 3 PDFDocument11 pagesUnit 3 PDFashwanimpec20No ratings yet
- Unit 3: Basic ConceptsDocument11 pagesUnit 3: Basic Conceptsashwanimpec20No ratings yet
- Transformation of Cryptography: Fundamental concepts of Encryption, Milestones, Mega-Trends and sustainable Change in regard to Secret Communications and its NomenclaturaFrom EverandTransformation of Cryptography: Fundamental concepts of Encryption, Milestones, Mega-Trends and sustainable Change in regard to Secret Communications and its NomenclaturaNo ratings yet
- For Further Information, Kindly Contact:: The TRSM SecretariatDocument2 pagesFor Further Information, Kindly Contact:: The TRSM Secretariatstephenlim7986No ratings yet
- Research Agreement Flow Chart Universiti Putra Malaysia: StartDocument1 pageResearch Agreement Flow Chart Universiti Putra Malaysia: Startstephenlim7986No ratings yet
- Science and Technology Foundation (MSTF) : M ST FDocument21 pagesScience and Technology Foundation (MSTF) : M ST Fstephenlim7986No ratings yet
- Country Report IranDocument34 pagesCountry Report Iranstephenlim7986No ratings yet
- Statement of STEP Malaysian Chapter Nanoscience and Nanotechnology Development ForumDocument3 pagesStatement of STEP Malaysian Chapter Nanoscience and Nanotechnology Development Forumstephenlim7986No ratings yet
- National Nanotechnology Activities and Development ProgramDocument36 pagesNational Nanotechnology Activities and Development Programstephenlim7986No ratings yet
- Application Guidelines For The ASEAN-ROK Award For Excellence in Science, Technology and Innovation 2021 - ASEAN-ROK STI PioneerDocument4 pagesApplication Guidelines For The ASEAN-ROK Award For Excellence in Science, Technology and Innovation 2021 - ASEAN-ROK STI Pioneerstephenlim7986No ratings yet
- ASEAN-ROK Award For Excellence in Science, Technology and Innovation 2021 ASEAN-ROK STI PioneerDocument5 pagesASEAN-ROK Award For Excellence in Science, Technology and Innovation 2021 ASEAN-ROK STI Pioneerstephenlim7986No ratings yet
- UPM Invitation Top Research Scientists Malaysia 2019 Call For Input Data Into TRSM DatabaseDocument5 pagesUPM Invitation Top Research Scientists Malaysia 2019 Call For Input Data Into TRSM Databasestephenlim7986No ratings yet
- 20210708175720asean-Rok Sti Award Application Form Asean-Rok Sti Pioneer 2021Document4 pages20210708175720asean-Rok Sti Award Application Form Asean-Rok Sti Pioneer 2021stephenlim7986No ratings yet
- ASEAN-ROK Award For Excellence in Science, Technology and Innovation 2021 ASEAN-ROK STI PioneerDocument5 pagesASEAN-ROK Award For Excellence in Science, Technology and Innovation 2021 ASEAN-ROK STI Pioneerstephenlim7986No ratings yet
- JCR Top 10% Journal Publications: Tan C.P Tan C.PDocument1 pageJCR Top 10% Journal Publications: Tan C.P Tan C.Pstephenlim7986No ratings yet
- ASEAN-ROK Award For Excellence in Science, Technology and Innovation 2020 ASEAN-ROK STI PioneerDocument2 pagesASEAN-ROK Award For Excellence in Science, Technology and Innovation 2020 ASEAN-ROK STI Pioneerstephenlim7986No ratings yet
- 20210708175720asean-Rok Sti Award Application Form Asean-Rok Sti Pioneer 2021Document4 pages20210708175720asean-Rok Sti Award Application Form Asean-Rok Sti Pioneer 2021stephenlim7986No ratings yet
- 2019 May Q1 & Q2 Journal PublicationsDocument3 pages2019 May Q1 & Q2 Journal Publicationsstephenlim7986No ratings yet
- 2019 December JCR Top 1% and Top 10% Journal PublicationsDocument5 pages2019 December JCR Top 1% and Top 10% Journal Publicationsstephenlim7986No ratings yet
- Application Guidelines For The ASEAN-ROK Award For Excellence in Science, Technology and Innovation 2021 - Next ASEAN InnovatorDocument4 pagesApplication Guidelines For The ASEAN-ROK Award For Excellence in Science, Technology and Innovation 2021 - Next ASEAN Innovatorstephenlim7986No ratings yet
- 2019 August Q1 and Q2 Journal PublicationsDocument2 pages2019 August Q1 and Q2 Journal Publicationsstephenlim7986No ratings yet
- 2019 September Q1 and Q2 Journal PublicationsDocument4 pages2019 September Q1 and Q2 Journal Publicationsstephenlim7986No ratings yet
- 2019 October Q1 and Q2 Journal PublicationsDocument3 pages2019 October Q1 and Q2 Journal Publicationsstephenlim7986No ratings yet
- 2019 April Q1 and Q2 Journal PublicationsDocument3 pages2019 April Q1 and Q2 Journal Publicationsstephenlim7986No ratings yet
- 20210408153821top - Publication - Disember - 2 - 2020Document1 page20210408153821top - Publication - Disember - 2 - 2020stephenlim7986No ratings yet
- JCR Top 10% Journal Publications: Roda J.-M. Tan W.SDocument2 pagesJCR Top 10% Journal Publications: Roda J.-M. Tan W.Sstephenlim7986No ratings yet
- 2019 November Q1 and Q2 Journal PublicationsDocument3 pages2019 November Q1 and Q2 Journal Publicationsstephenlim7986No ratings yet
- 2019 June Q1 & Q2 Journal PublicationsDocument3 pages2019 June Q1 & Q2 Journal Publicationsstephenlim7986No ratings yet
- Top Publications - Ogos 2020 V4Document1 pageTop Publications - Ogos 2020 V4stephenlim7986No ratings yet
- Top Publications - September 2020Document1 pageTop Publications - September 2020stephenlim7986No ratings yet
- Top Publications - May 2020Document2 pagesTop Publications - May 2020stephenlim7986No ratings yet
- Top Publications - April 2020Document1 pageTop Publications - April 2020stephenlim7986No ratings yet
- Top Publications - April 2020Document1 pageTop Publications - April 2020stephenlim7986No ratings yet
- Cryptography and Network SecurityDocument12 pagesCryptography and Network SecurityWiedy Tira PratamaNo ratings yet
- Disadvantages of IctDocument17 pagesDisadvantages of IctLiezel Tolentino ArmadaNo ratings yet
- Baseline Information Security and Privacy Requirements For Suppliers - 19032018Document15 pagesBaseline Information Security and Privacy Requirements For Suppliers - 19032018ezioNo ratings yet
- Akshay AadharDocument1 pageAkshay Aadharsachinsinghofficial55No ratings yet
- Reset A Computer AccountDocument2 pagesReset A Computer AccountM3iatNo ratings yet
- CTSA White PaperDocument15 pagesCTSA White Papermail4290No ratings yet
- Intrusion ToleranceDocument19 pagesIntrusion ToleranceswedapattaliNo ratings yet
- Caesar CipherDocument3 pagesCaesar Cipherangie coNo ratings yet
- Securing Passwords Against Dictionary Attacks: Benny Pinkas Tomas SanderDocument14 pagesSecuring Passwords Against Dictionary Attacks: Benny Pinkas Tomas Sandera4315829No ratings yet
- Management Micro-Project Report - SurajDocument26 pagesManagement Micro-Project Report - SurajMorris jonsonNo ratings yet
- Learning Guide VU21990 Recognise The Need For Cyber Security in An Organisation v9.1Document55 pagesLearning Guide VU21990 Recognise The Need For Cyber Security in An Organisation v9.1MD NASIR UDDINNo ratings yet
- VLSI Implementation of Advanced Encryption Standard Using Rijndael AlgorithmDocument6 pagesVLSI Implementation of Advanced Encryption Standard Using Rijndael AlgorithmInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- CMP - by MSDocument80 pagesCMP - by MSMahendra SutharNo ratings yet
- CASE Java Course OutlineDocument23 pagesCASE Java Course Outlineram ramNo ratings yet
- Practical 1: TheoryDocument72 pagesPractical 1: TheoryprogrammerNo ratings yet
- Security Analysis of TETRADocument102 pagesSecurity Analysis of TETRAkondorosNo ratings yet
- SAP Cloud Platform Identity AuthenticationDocument35 pagesSAP Cloud Platform Identity AuthenticationAnk1313No ratings yet
- Finals Exam in Information Assurance and SecurityDocument3 pagesFinals Exam in Information Assurance and SecurityJovanna Lagradilla OcampoNo ratings yet
- Lecture 02 - The Need For Security-2Document48 pagesLecture 02 - The Need For Security-2Umair AmjadNo ratings yet
- 2CCNPv7 ROUTE Lab8-1 Secure Management Plane StudentDocument10 pages2CCNPv7 ROUTE Lab8-1 Secure Management Plane StudentJenny Zambrano Tramites de VisasNo ratings yet
- A Dvanced E Ncryption S TandardDocument48 pagesA Dvanced E Ncryption S TandardJa KovNo ratings yet
- Securable Network in 3 Party NetworkDocument12 pagesSecurable Network in 3 Party NetworkAmjad ShaikNo ratings yet
- Rapport Fayssal PhishingDocument5 pagesRapport Fayssal Phishingفيصل بن داودNo ratings yet
- AeslibDocument3 pagesAeslibhayers849No ratings yet
- Certified Ethical Hacking Module 5 MapDocument1 pageCertified Ethical Hacking Module 5 MapRismal Ray VaughanNo ratings yet
- Context Level DFDDocument7 pagesContext Level DFDnikhil sharmaNo ratings yet
- Encryption and HashingDocument2 pagesEncryption and HashingSeri FinaNo ratings yet


![Nomenclatura - Encyclopedia of modern Cryptography and Internet Security: From AutoCrypt and Exponential Encryption to Zero-Knowledge-Proof Keys [Paperback]](https://imgv2-1-f.scribdassets.com/img/word_document/421844479/149x198/e9c664736d/1617232007?v=1)