Professional Documents
Culture Documents
Bba401 SLM Unit 07
Uploaded by
Badder DanbadOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Bba401 SLM Unit 07
Uploaded by
Badder DanbadCopyright:
Available Formats
Unit 7
Security in Electronic Business
Structure
7.1 Introduction
Objectives
7.2 Intranet and Extranet Security: Threats and Protection
7.3 Protection Methods
7.4 Data and Message Security
7.5 Firewalls
7.6 Summary
7.7 Glossary
7.8 Terminal Questions
7.9 Answers
References
7.1 Introduction
In the earlier units, you learnt that a considerable volume of business today is
conducted over public networks. There is exchange of large volumes of
confidential data such as credit card details, financial records and other important
information. So, security and confidentiality should be ensured before businesses
can conduct financial transactions over the Internet.
At a time when e-commerce is growing at a fast pace, the lack of data
security on the Internet has become a complex issue. Hence, e-security has
become a major concern. In this unit, you will learn about security threats, client
server security, messagedata security, network security and Web security.
Objectives
After studying this unit, you should be able to:
Asses the security concerns of intranet and extranet
Differentiate between various security problems in a clientserver
environment
Compare the two broad categories of clientserver security threats
Evaluate the various protection methods adopted by organizations
State how data and message security is ensured over the Net
Summarize the components, types and limitations of firewalls
E-Commerce
Unit 7
7.2 Intranet and Extranet Security: Threats and Protection
Over the last four years, the use of intranets and extranets by organizations has
increased tremendously. The reasons for this are many:
Intranet and extranet are more economical than leased line networks
or WANs.
They enable more cost-effective and productive means of working.
They can help organizations distribute information more economically
and faster.
They are effective tools for developing self-service applications,
reducing administrative costs and improving collaboration with
employees within the organization and with business partners.
With this increased use of intranet and extranet transactions comes its
associated security threats. A security threat is a circumstance, condition, or an
event that causes a loss of or harm to data or network resources. This loss/
harm can be in the form of destruction, disclosure and modification of data;
denial of services; fraud and waste. These can be caused by unauthorized
access, tampering and eavesdropping.
It is therefore important that organizations and businesses must secure
themselves against such threats. In order to do this, they must put in place
strong network security solutions which can transparently and automatically
control the access of corporate intranets and extranets. The solutions must be
in the form of identification and authentication of users, encryption of all traffic
from the application to the user, and access control to all information.
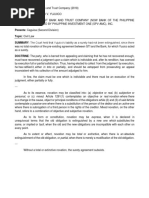
Prospective customers
Rest of the World
Community of Interest
Industry Associations
Business Partners
Customers
Suppliers
Internet
Community
Employees
Extranet
Trusted Services
Trusted Transactions
Trusted ID & Authentication
Intranet
Figure 7.1 The Expanding Network
Sikkim Manipal University
Page No. 114
E-Commerce
Unit 7
7.2.1 Security Concerns of Intranet and Extranet
With the increased use of intranets and extranets, the need for security of
networks and computer systems has also gone up. TCP/IP protocol is an open
technology as it is a connectionless protocol. Here, data is broken up into
packets which then travel freely over the network to reach their final destination
by the best possible route. Unless proper precautions are taken, these data
packets can easily be intercepted and/or altered.
Unfortunately, this can often happen without either the sender or the
receiver being aware of the security breach. Since dedicated links between the
parties in a communication usually are not established in advance, it is easy for
one party to impersonate another party.
Firewall
PO3/Mail
Server
Hacker
Corporate
Intranet
HR/
Finance
Mobile Worker
Contractors
Customer
Web Site
Employees
Supplier
Manufacturing
Engineering
Svr
Hacker
Hacker
Branch Office
Figure 7.2 Expanding Networks Increase Possible Points of Attack
Figure 7.2 is a diagrammatic representation of the security threats to a network
from both within and outside an organization.
Security risks encountered on intranets and extranets
There are many ways of breaching an intranet or extranet network. A breach
may occur in the following ways:
An unauthorized person, who does not belong to an organization, gains
wrongful access to the companys computer system.
Sikkim Manipal University
Page No. 115
E-Commerce
Unit 7
An employee or a supplier who is authorized to use the system for a
particular purpose actually uses it for any other purpose(s). To take an
example, an HR person may break into a marketing database to access
sales figures.
Confidential information may be intercepted when in transit; for
example, an intruder can attach a network sniffing device to the
network. While sniffers are generally used for network diagnostics,
they can also be used to intercept data coming over the wire.
Users may share documents over the intranet or extranet between
offices in different geographical locations.
Sensitive data which is sent over the wire can be exposed by
telecommuters accessing the corporate intranet from their home
computers.
E-mails can also be intercepted in transit.
7.2.2 ClientServer Network Security
Client-server security ensures that only authorized users can access the
information. Such mechanisms include password protection, encrypted smart
cards, biometrics and firewalls. Following are the security problems in a client
server environment:
1. Physical Security: This is a common problem which is caused by an
unauthorized user, say a hacker, who gains physical access to computers
by guessing the passwords of the various users.
2. Software Security: A software security breach occurs when programs/
software are compromised and made to execute operations which they
should not legally be doing.
Example: The rlogin hole in the IBM RS-6000 workstation, which enables
a cracker to create a root shell or super user access mode, can be used
to delete an entire file system or a password file or create a new account.
3. Inconsistent Usage: A security lapse of this nature is caused by the
assembling of a combination of hardware and software by a system
administrator. Due to the increasing complexity of software, such type of
assembling is a growing problem and compromises the security of any
system.
Sikkim Manipal University
Page No. 116
E-Commerce
Unit 7
7.2.3 ClientServer Security Threats
Clientserver security threats are largely divided into two categories:
Threats to client
Threats to server
1. Threats to clients
Client threats mostly arise from malicious data or code, malicious code being
viruses, worms and Trojan horses.
Virus: A virus is a code segment that replicates by attaching copies of
itself to existing executable (EXE) files. The new copy of the virus is
executed whenever a user executes the host program. Every virus
does a different thing; one virus may display some particular text string
on the monitor while another may delete all files on a hard disk on a
particular date.
Worm: A worm is also a self-replicating program but it differs from a
virus in that it does not require any host program. Clients must regularly
scan for malicious data and executable program fragments that are
transferred from the server to the client. Examples of worms include
VBS/Loveletter and Happy99.
Trojan Horse: This is a program that performs a desired task as well
as other unexpected functions. An example would be an editing
program for a multi-user system that could be modified to randomly
delete another users file(s). Examples of a trojan horse would include
BackOrifice, VBS/Freelink and Backdoor G.
2. Threats to servers
Threats to servers include:
Unauthorized eavesdropping
Denial of services
Modification of incoming data packets
(a) Eavesdropping
Hackers can use electronic eavesdropping to trap user names and unencrypted
passwords sent over a network. Encryption can prevent eavesdropping on data
travelling over unsecured networks.
Sikkim Manipal University
Page No. 117
E-Commerce
Unit 7
(b) Denial of services
A denial of service attack is a type of security threat wherein legitimate users
are prevented from using a particular service to the deliberate actions of
attackers. Examples of such a threat are:
Preventing legitimate traffic on a network by flooding it
Preventing access to a service by disrupting a server by sending more
requests than the server can handle
Preventing a particular individual from accessing a service
Disrupting service to a specific system or person
Services can be denied by service overloading or message overloading
Service overloading: You can easily overload a web server by writing
a small looping program to send requests continually for a particular
file; for example, to display a home page.
Message overloading: This happens when someone sends a very
large file to a message box every few minutes. The message box
rapidly grows in size, soon occupying all the space on the disk. The
repeated receiving process on the recipients machine can cause
the disk to crash.
(c) Packet modification
This is an integrity threat that involves modifying or destroying a message packet.
IP Spoofing: Internet Protocol is the elementary protocol which sends data
over the internet and other computer networks. The header of each packet that
is to be transmitted contains the source and destination addresses called IP
addresses. An IP address would look like this: 192.30.233.0
The creation of an IP packet with a copied IP source is called IP address
spoofing. In such a case, the intention is to disguise the senders identity or to
impersonate another computing system. It is one among the many common
forms of online disguises. How it works is that an attacker spoofs the IP address
of a senders machine and then sends a malicious message. Since this appears
to have come from a trusted machine, an attacker thereby gains unauthorized
access to a computer or a network.
Sikkim Manipal University
Page No. 118
E-Commerce
Unit 7
Table 7.1 Average Losses from Various Types of Attacks
Type of Attack
Average Loss
Unauthorized Insider Access
1,363,915
Theft of Proprietary Info
1,307146
Financial Fraud
656,927
Telecom Fraud
595,766
Sabotage of data or networks
164,817
Spoofing
128,000
System penetration by outside
110,944
Telecom Eavesdropping
96,833
Denial of Service
77,417
Virus
65,997
Active Wiretapping
49,000
Inside Abuse of Net Access
38,744
Laptop Theft
35,348
Average Loss
215,753
Source: Computer Security Institute (USA)/FBI 1998 Survey of Computer Security
A survey conducted by the Computer Security Institute in 1998 in the US
classified the different types of attacks and put a value to them. Based on the
survey it was deduced that unauthorized access by insiders was resulting in the
most serious financial losses.
Activity 1
Prepare a chart showing the various stages of development of the security
solutions and the causes that led to the development of each type.
Self-Assessment Questions
1. State whether the following statements are true or false.
(a) Intranets and extranets are more economical than WANs.
(b) It is impossible to intercept data over the network using TCP/IP.
(c) A Trojan horse will perform only the desired task.
Sikkim Manipal University
Page No. 119
E-Commerce
Unit 7
2. Fill in the blanks with the appropriate word.
(a) Client server security ensures that only________users can access
the information.
(b) A _______is a code segment that replicates by attaching copies of
itself to existing executable files.
(c) A _____ does not require a host program to replicate itself.
7.3 Protection Methods
In order to reduce the different types of security threats, various protection
methods can be used. These include:
(a) Trust-based security
(b) Security through obscurity
(c) Password schemes
(d) Biometric system
(a) Trust-based security: Trust-based security trusts everyone, and
therefore, does nothing extra to protect the network or restrict access to
any data on that network. All users working in a network can share
information. This approach assumes that no user will break into the system
illegally or delete any files or indulge in unauthorized access of data. In
the past, this approach was successful, but not any more.
(b) Security through obscurity: Any network can be secure as long as
nobody outside its management group is allowed to find out anything
about its operational details. This can be done by hiding account passwords
in binary files or scripts so that nobody will ever find them.
But its usefulness is minimal in the UNIX world where users are free to
move around the file system and have a good understanding of
programming techniques. They can easily guess the bits of knowledge
considered confidential. These bypass the whole basis of Security Though
Obsecurity and make this method of security quite ineffective.
(c) Password schemes: Yet another form of security is password schemes.
However, it can also break down when some common words or names
are used as passwords.
The simplest method used by most hackers is dictionary comparison.
This is done by comparing a list of encryption user passwords against a
Sikkim Manipal University
Page No. 120
E-Commerce
Unit 7
dictionary of common encryption words. This scheme often works because
users tend to chose relatively simple or familiar words as passwords.
As a solution, you can use mixed-case passwords containing at least one
non-alphanumeric character and changing passwords every sixtyninety
days.
You can also include one-time passwords or smart card randomized
tokens. This scheme provides a high level of security.
(d) Biometric system: The biometric system involves some identification
aspects which are related to the human body, such as comparing
(fingerprints), palm prints and voice recognition. The biometric system
uses one-to-one and one-to-many relationships. However, these systems
are expensive to implement.
Activity 2
Find out the types of protection methods adopted by your organization/
institution. How effective are they?
Self-Assessment Questions
3. State whether the following statements true or false.
(a) In a trust-based security, all users working in a network can share
information.
(b) Biometric systems are cheap.
4. Fill in the blanks with the appropriate word.
(a) The simplest method adopted by password hackers is..
(b) Biometric systems involve some identification aspects related to the.
7.4 Data and Message Security
Data security
Data security generally suffers from packet sniffing. A sniffing attack begins
when a computer is compromised to share some data or program. A cracker
starts by installing a packet sniffer into the network. The sniffer program attacks
the network traffic, telnet or FTP session that a legitimate user initiates to gain
access to another system. The session contains the login ID, password and
Sikkim Manipal University
Page No. 121
E-Commerce
Unit 7
user number of the person logging into other machines. This is the information
a sniffer needs to log in to a machine.
Message security
Threats to message security fall into three categories:
Confidentiality
Integrity
Authentication
(a) Message confidentiality
Message confidentiality means when a message passes between the client
and the server on a public network, third parties cannot view and intercept this
data. Confidentiality is important for user-sensitive data such as credit card
number. This requirement will be amplified when other kinds of data, such as
employee records, government files and social security number, begin traversing
the Net.
(b) Message integrity
The contents of transaction must be unmodified during transit. It must be clear
that no one has added, deleted or modified any part of the message. Error
detection codes or checksum, sequence number and encryption techniques
are methods to enhance information integrity. Sequence numbers prevent
recording, losing or replaying of messages by an attacker. Encryption techniques,
such as digital signature, can detect any modification of a message.
(c) Message sender authentication
In an e-commerce environment, it is important that clients authenticate
themselves to servers, that servers authenticate themselves to clients and that
both authenticate themselves to each other. Authentication in e-commerce
basically requires the user to prove his or her identity for each requested service.
Third-party authentication services must exist within a distribution network
environment where a sender cannot be trusted to identify itself correctly to a
receiver. A digital certificate is used for this (authentication) purpose.
7.5 Firewalls
One of the most common security measures in use today is the firewall. A
firewall is meant to act as a defence mechanism. It prevents unauthorized people
Sikkim Manipal University
Page No. 122
E-Commerce
Unit 7
that do not belong to an organization from gaining access to data that is
considered sensitive.
A firewall is simply a barrier between two networks usually a trusted
internal network and an external network which is untrusted. The system
administrator defines a set of policies. Based on these policies, the firewall
decides whether to let incoming and outgoing packets go through or whether to
block them. Figure 7.3 shows how a firewall works.
Internet
40,000
networks;
number of
hackers?
Enterprise
LAN
or
WAN
Firewall
bypass should
not be allowed
Figure 7.3 Schematic Diagram of a Firewall
Importance of a firewall
A firewall can monitor incoming and outgoing security alerts and record
and track down an intrusion attempt depending on the severity.
Some firewalls, but not all, can delete viruses, worms, Trojan horses or
data collectors.
A firewall can also be used to prevent employees from accessing selected
sites on WWW.
Sikkim Manipal University
Page No. 123
E-Commerce
Unit 7
7.5.1 Components of a Firewall
Following are the hardware and software components of a firewall:
1. Hardware: Firewall hardware usually consists of a separate computer
dedicated to running the firewall software functions.
2. Software: Firewall software can consist of some or all of these
applications:
Packet Filters
Proxy Servers
SOCKS Servers
Network address translation (NAT) services
Logging and monitoring software
Virtual private network (VPN) services
7.5.2 Types of Firewalls
All firewalls can be divided broadly into two categories static and dynamic.
Let us try and understand the features of these two categories of firewalls.
(a) Static firewall
These firewalls are generally pre-configured and they allow or deny access
from outside by default. In a Default Allow policy, all inbound traffic is unrestricted;
only specified users are denied access to the network of enterprises. In the
Default Deny policy, only those specific users who display their authentication
are permitted to access a network.
(b) Dynamic firewall
A dynamic firewall uses allowance and denial of services policy with regard to
the network on the basis of time. Some service on the network may be allowed
and others denied for a specific time period. The configuration of such a firewall
is slightly more complex.
Different types of firewalls are used depending upon the requirements of
organizations. Some of these are:
IP Packet Filtering Firewall
Application-Level Firewalls
1. IP packet filtering firewall
This firewall uses a router or any other suitably configured device to filter incoming
and outgoing data packets. It does so by examining the information contained
Sikkim Manipal University
Page No. 124
E-Commerce
Unit 7
in the TCP/IP packet header. The filters can be configured to accept or discard
a packet on the basis of the following information given in the packet header:
Source address
Destination address
Application or protocol
Source port number
Destination port number
This router stores a table containing rules specified for security purposes.
While examining a packet header, the firewall compares the information in it
with the rules stored in the access control table (these rules are the parameters
for blocking a packet or allowing it to pass through the router). If the information
in the packet header does not match with any of the specified rules, the firewall
applies the default rule.
Now, what is a default rule? The default rule generally follows the allow
all or deny all model. For strict security; the firewall default rule should be the
deny all model which most packet filters actually follow. (See Figure 4.8.)
Public Internet
IP Packet screening router
Sample Screening Rules:
Protocols (TCP, UDP)
Source IP address (Domain.edu)
Target TCP port 80 (WWW only)
Figure 7.4 IP Packet Filter Firewall
Disadvantages
Packet filters cannot support user authentication and blocking based on
contents at the application level.
For complex protocols that specify return data ports dynamically, the
filtering protocol becomes difficult and complex.
The creation of packet-filtering rules can become tedious when used for
filtering all the permutations and combinations of packet attributes.
Sikkim Manipal University
Page No. 125
E-Commerce
Unit 7
It is susceptible to IP spoofing; hackers can change IP addresses in packet
headers to those that are acceptable and thereby get access to a corporate
network.
A more sophisticated and secure type of firewall is an application-level
gateway, such as a proxy application gateway.
2. Application-level firewalls
An application-level firewall intercepts incoming and outgoing packets; runs
proxies that copy and forward information across the firewall, and functions as
a proxy server. As a result, a direct connection between a client or a server that
is trusted and an untrusted host is prevented.
A proxy server application gateway is a special server that typically runs
on a firewall machine. Instead of directly talking to external WWW servers,
each request from the client is routed to a proxy on the firewall that is defined by
the users. This is how it works: (i) the proxy server waits for a request from
inside the firewall, (ii) it then forwards the request to the remote server outside
the firewall and (iii) reads the response and then returns it to the client.
Application-level proxies are designed for individual applications. If, for
example, an application-level firewall runs, WWW and SMTP (e-mail) traffic will
pass through the firewall, while all other services such as Telnet and FTP would
be blocked.
Public Internet
Web HTTP
Server
Secure subnet inside
the firewall security
perimeter
Client
inside the
firewall
FTP
Server
Proxy server
on the
firewall
machine that
connects to
external
Internet
Gopher
Server
Telnet
Server
USENET
News Server
Figure 7.5 Application-Level Firewall
Sikkim Manipal University
Page No. 126
E-Commerce
Unit 7
7.5.3 Factors to Consider in a Firewall
When selecting a firewall, the following factors should be considered:
Ease of use
Level and quality of protection
Whether it is free
Its level of intelligence
Its technique/strategy for coping with Internet connection sharing
Ease of use
The firewall must be easy to install, run and use. Take the example of Windows
SP2firewall; it is quite good, but not user friendly.
How good is the protection?
Does the firewall block outgoing security threats, as it does with incoming ones?
Is it free? If not, why should I purchase as opposed to a free solution?
It is important to check out if the firewall software is free. If it is being offered
free, chances are it will be a basic, cut-down version of the complete package.
Most vendors allow a thirty day trial for the complete package, after which which
they offer the cut-down version free of cost (if you wish to purchase). However,
given the nature and extent of cyber threats prevalent today, it may be worth the
cost to buy the complete version.
How intelligent is it?
Some firewall software may be more intelligent than others. An intelligent firewall
will recognize a genuine Windows application when it tries to access the Internet,
while another (which is not intelligent) will need to be prompted on whether
access should be denied or not.
How does it cope with Internet connection sharing?
Those that use Internet Connection Sharing (ICS) through Windows XP, a firewall
that blocks the user from identifying an IP address or from making use of an
internet connection can be a botheration. However, it is definitely not advisable
to frequent the net without the assistance of a firewall. You will probably have to
do a trial and error before you find the firewall best suited to your needs.
7.5.4 Firewall Policy
A firewall generally implements one of two basic design policies:
Permissive Approach
Restrictive Approach
Sikkim Manipal University
Page No. 127
E-Commerce
Unit 7
(a) Permissive Approach
In this approach, all services are by default allowed to pass the site. Only
those which have been specifically identified by the network services
access policy as disallowed, are blocked. It is a desirable policy because
it allows for more ways to get around the firewall. Certain services, such
as FTP, Archie and RPC, are difficult to filter. In such cases, a firewall of
this nature is suitable.
(b) Restrictive Approach
A restrictive firewall denies all services by default, and allows only those
services that have been identified as allowed, to pass. This policy follows
the classic access model used in all areas of information security. The
second policy is stronger and safer, but it is more restrictive for users.
7.5.5 Limitations of Firewalls
Firewalls also have limitations:
A firewall is unable to offer protection from those threats that do not pass
through it.
It does not protect a network system against threats that emanate from
within the network that is, from internal users.
A firewall monitors the traffic in a network, permitting only authenticated
and legitimate traffic flow. It does not concern itself with integrity issues
related to applications and data.
A firewall is concerned with the controlled flow of data traffic and not with
confidentiality of data. However, application proxies at the firewall machine
can provide encryption and decryption of all the data passing through as
it becomes a single access point to the application.
A firewall cannot protect very well against viruses. In general, a firewall
cannot provide protection against a data-driven attack an attack in which
something is mailed or copied to an internal host, from where it is then
executed.
Self-Assessment Questions
5. State whether the following statements are true or false.
(a) A sniffer program attacks the network traffic, telnet or FTP session
that a legitimate user initiates to gain access to another system.
Sikkim Manipal University
Page No. 128
E-Commerce
Unit 7
(b) Authentication is e-commerce requires the user to provide his or her
identity.
6. Fill in the blanks with the appropriate words.
(a) Data security generally suffers from________.
(b) ________prevent recording, losing or replaying of messages by an
attacker.
Factors to Consider in a Firewall
When selecting a firewall, the following factors should be considered:
Ease of use
Level and quality of protection
Whether it is free
Its level of intelligence
Its technique/strategy for coping with Internet connection sharing
Ease of use
The firewall must be easy to install, run and use. Take the example of Windows
SP2firewall; it is quite good, but not user-friendly.
How good is the protection?
Does the firewall block outgoing security threats, as it does with incoming ones?
Is it free? If not, why should I purchase as opposed to a free solution?
It is important to check out if the firewall software is free. If it is being offered
free, chances are it will be a basic, cut-down version of the complete package.
Most vendors allow a thirty-day trial for the complete package, after which which
they offer the cut-down version free of cost (if you wish to purchase). However,
given the nature and extent of cyber threats prevalent today, it may be worth the
cost to buy the complete version.
How intelligent is it?
Some firewall software may be more intelligent than others. An intelligent firewall
will recognize a genuine Windows application when it tries to access the Internet,
while another (which is not intelligent) will need to be prompted on whether
access should be denied or not.
How does it cope with Internet connection sharing?
Those that use Internet Connection Sharing (ICS) through Windows XP, a firewall
that blocks the user from identifying an IP address or from making use of an
internet connection can be a botheration. However, it is definitely not advisable
Sikkim Manipal University
Page No. 129
E-Commerce
Unit 7
to frequent the Net without the assistance of a firewall. You will probably have to
do a trial and error before you find the firewall best suited to your needs.
Self-Assessment Questions
7. State whether the following statements are true or false.
(a) A firewall prevents unauthorized people from gaining access to
sensitive data.
(b) All firewalls can delete worms and viruses.
(c) The firewall must be easy to install, run and use.
8. Fill in the blanks with the appropriate word.
(a) Firewall ______consists of a separate computer dedicated to running
the firewall software functions.
(b) A firewall cannot offer protection against those threats that______.
(c) A firewall cannot protect well against_______.
7.6 Summary
Let us recapitulate the important concepts discussed in this unit:
Security threats refer to circumstances or occasions that result in the
destruction, disclosure or modification of data thereby causing economic
harm to network resources.
The client-server security threats can be divided into two broad
categoriesthreats to client and threats to server.
Threats to clients arise from virus, worm and Trojan horse.
To take care of this, a security threat solution is essential which can
transparently and automatically control access to corporate intranets or
extranets.
Some of the popular methods adopted by organizations to reduce security
threats include trust-based security, security through obscurity, password
schemes and biometric system.
Firewalls are important to control and monitor traffic between the outside
world and a local network. A firewall places a device, a computer or a
router between the Internet and the network.
Sikkim Manipal University
Page No. 130
E-Commerce
Unit 7
7.7 Glossary
Security threat: A circumstance, condition, or an event that causes
economic loss to data or network resources in the form of destruction,
disclosure, and modification of data, denial of services, fraud and waste
Clientserver security: Ensures that only authorized users access the
information and includes such mechanisms as password protection,
encrypted smart cards, biometrics and firewalls
Biometric system: Involves some identical aspects that are related to
the human body, such as fingerprints, palm prints and voice recognition
Virus: A code segment that replicates by attaching copies of itself to
existing executable files
Trojan horse: A program that performs a desired task and also includes
unexpected functions
Worm: A self-replicating program that is self-continued and does not
require any host program.
Firewall: A barrier between two networks and includes an internal network
often called the trusted network and an external network called untrusted
network
7.8 Terminal Questions
1. Explain the security concerns of intranet and extranet.
2. Discuss the different security problems in a clientserver environment.
3. Describe the two broad categories of clientserver security threats.
4. Evaluate the various protection methods adopted by organizations.
5. Explain how data and message security are ensured over the Net.
6. Summarize the components, types and limitations of firewalls.
Sikkim Manipal University
Page No. 131
E-Commerce
Unit 7
7.9 Answers
Answers to Self-Assessment Questions
1. (a) True; (b) False; (c) False
2. (a) authorized; (b) virus; (c) worm
3. (a) True; (b) False
4. (a) dictionary comparison; (b) human body
5. (a) True; (b) True
6. (a) packet sniffing; (b) Sequence numbers
7. (a) True; (b) False; (c) True
8. (a) hardware; (b) do not pass through it; (c) viruses
Answers to Terminal Questions
1. Refer to Section 7.2
2. Refer to Sections 7.2.1 and 7.2.2
3. Refer to Section 7.2.3
4. Refer to Section 7.3
5. Refer to Section 7.4
6. Refer to Section 7.5
References
1. Laudon, Kenneth C. and Carol Guercio Traver. E-Commerce: Business,
Technology, Society. N.J: Prentice Hall, 2004.
2. Turban, Efraim, Jae Kuy Lee and Michael Chung. Electronic Commerce:
A Managerial Perspective. Prentice-Hall, 1999.
3. Whitley, David. E-Commerce: Strategy, Technologies and Applications.
Tata McGraw-Hill, 1998.
Sikkim Manipal University
Page No. 132
You might also like
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (120)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- From: Elisha Goodman Friday, 3 A.M. Dear Overcomer in Christ Calvary Greetings..Document5 pagesFrom: Elisha Goodman Friday, 3 A.M. Dear Overcomer in Christ Calvary Greetings..Badder Danbad90% (10)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- 5S TrainingDocument81 pages5S Trainingamresh kumar tiwari100% (1)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- ACFE Fraud Examination Report (Short)Document8 pagesACFE Fraud Examination Report (Short)Basit Sattar100% (1)
- Critically Discuss The Extent of Directors Duties and The Changes Made by The Companies Act 2006Document14 pagesCritically Discuss The Extent of Directors Duties and The Changes Made by The Companies Act 2006Lingru WenNo ratings yet
- The Power of Early Contractor Involvement Volume 12 Issue 2Document4 pagesThe Power of Early Contractor Involvement Volume 12 Issue 2Odilon KongoloNo ratings yet
- Ch.4 - Cash and Receivables - MHDocument75 pagesCh.4 - Cash and Receivables - MHSamZhaoNo ratings yet
- Top 10 Agile Techniques v14Document24 pagesTop 10 Agile Techniques v14fsato1100% (1)
- NOTICE: This Order Was Filed Under Supreme Court Rule 23 and May Not Be Cited As PrecedentDocument20 pagesNOTICE: This Order Was Filed Under Supreme Court Rule 23 and May Not Be Cited As PrecedentmikekvolpeNo ratings yet
- MKT 566 Quiz 2Document16 pagesMKT 566 Quiz 2kaz92No ratings yet
- Yujuico vs. Far East Bank and Trust Company DigestDocument4 pagesYujuico vs. Far East Bank and Trust Company DigestEmir MendozaNo ratings yet
- Tuition Fees For Entry in 2016Document5 pagesTuition Fees For Entry in 2016Badder DanbadNo ratings yet
- Strategic Planning Project Business: Opportunities, and Threats Involved in ADocument3 pagesStrategic Planning Project Business: Opportunities, and Threats Involved in ABadder Danbad100% (1)
- Time Zone ManualDocument5 pagesTime Zone ManualBadder DanbadNo ratings yet
- Meta DataDocument2 pagesMeta DataBadder DanbadNo ratings yet
- Java & Console TotDocument2 pagesJava & Console TotBadder DanbadNo ratings yet
- Operating Systems: System Software, or Systems Software, IsDocument2 pagesOperating Systems: System Software, or Systems Software, IsBadder DanbadNo ratings yet
- Aniline DefinitionDocument2 pagesAniline DefinitionBadder DanbadNo ratings yet
- Policies Processes Procedures Organization: Management SystemDocument3 pagesPolicies Processes Procedures Organization: Management SystemBadder DanbadNo ratings yet
- Policies Processes Procedures Organization: Management SystemDocument3 pagesPolicies Processes Procedures Organization: Management SystemBadder DanbadNo ratings yet
- Scholarships Notes 2016Document4 pagesScholarships Notes 2016Badder DanbadNo ratings yet
- Tuition Fees For Entry in 2016Document5 pagesTuition Fees For Entry in 2016Badder DanbadNo ratings yet
- Bba401 SLM Unit 05Document22 pagesBba401 SLM Unit 05Badder DanbadNo ratings yet
- Policies Processes Procedures Organization: Management SystemDocument3 pagesPolicies Processes Procedures Organization: Management SystemBadder DanbadNo ratings yet
- The TechnologyDocument3 pagesThe TechnologyBadder DanbadNo ratings yet
- Nick 7Document1 pageNick 7Badder DanbadNo ratings yet
- Quantitative TechniqueDocument3 pagesQuantitative TechniqueBadder DanbadNo ratings yet
- Information SystemsDocument2 pagesInformation SystemsBadder DanbadNo ratings yet
- Workplace Stress Survey QuestionnaireDocument1 pageWorkplace Stress Survey QuestionnaireBadder DanbadNo ratings yet
- Approximately of 400 Words. Each Question Is Followed by Evaluation SchemeDocument2 pagesApproximately of 400 Words. Each Question Is Followed by Evaluation SchemeBadder DanbadNo ratings yet
- A1 DIKAR Model in ICT Strategic PlanningDocument3 pagesA1 DIKAR Model in ICT Strategic PlanningBadder Danbad67% (3)
- Bba401 SLM Unit 10Document22 pagesBba401 SLM Unit 10Badder DanbadNo ratings yet
- SC - Part 3Document1 pageSC - Part 3Badder DanbadNo ratings yet
- Taxation Text BookDocument3 pagesTaxation Text BookBadder DanbadNo ratings yet
- Bba401 SLM Unit 06Document14 pagesBba401 SLM Unit 06Badder DanbadNo ratings yet
- Bba401 SLM Unit 08Document15 pagesBba401 SLM Unit 08Badder DanbadNo ratings yet
- Bba401 SLM Unit 09Document22 pagesBba401 SLM Unit 09Badder DanbadNo ratings yet
- Bba401 SLM Unit 03Document22 pagesBba401 SLM Unit 03Badder DanbadNo ratings yet
- Bba401 SLM Unit 04Document17 pagesBba401 SLM Unit 04Badder DanbadNo ratings yet
- English 8 - Q3 - Las 1 RTP PDFDocument4 pagesEnglish 8 - Q3 - Las 1 RTP PDFKim Elyssa SalamatNo ratings yet
- Modern OfficeDocument10 pagesModern OfficesonuNo ratings yet
- Entrepreneurship Internal Assessment Health Industry IaDocument10 pagesEntrepreneurship Internal Assessment Health Industry IaCalm DownNo ratings yet
- Convergence JournalismDocument34 pagesConvergence Journalismali3800No ratings yet
- Organization Chart UpdatedDocument1 pageOrganization Chart UpdatedganrashNo ratings yet
- Industrial Relation of LawDocument3 pagesIndustrial Relation of LawArunNo ratings yet
- Staffing - Responsibilities, Tools and Methods of SelectionDocument30 pagesStaffing - Responsibilities, Tools and Methods of SelectionAmreen KhanNo ratings yet
- Tez PortalDocument1 pageTez Portalkiran BawadkarNo ratings yet
- NSTP Group5Document14 pagesNSTP Group5Princess Kiszia A DuaNo ratings yet
- FRANCHISEDocument2 pagesFRANCHISEadieNo ratings yet
- 73 220 Lecture07Document10 pages73 220 Lecture07api-26315128No ratings yet
- Gujarat Technological University: Comprehensive Project ReportDocument32 pagesGujarat Technological University: Comprehensive Project ReportDharmesh PatelNo ratings yet
- Black White and Teal Minimal Abstract Patterns Finance Report Finance PresentationDocument15 pagesBlack White and Teal Minimal Abstract Patterns Finance Report Finance PresentationamirulNo ratings yet
- Upload 1 - Heirs of Tan Eng Kee v. CADocument4 pagesUpload 1 - Heirs of Tan Eng Kee v. CAPatricia VillamilNo ratings yet
- Uber Final PPT - Targeting and Positioning MissingDocument14 pagesUber Final PPT - Targeting and Positioning MissingAquarius Anum0% (1)
- ALKO Case StudyDocument13 pagesALKO Case StudyAnass MessaoudiNo ratings yet
- Ranjana Kumar, Former CEO Indian Bank Ranjana Kumar Was The First Woman CEO ofDocument5 pagesRanjana Kumar, Former CEO Indian Bank Ranjana Kumar Was The First Woman CEO ofAkansha RathoreNo ratings yet
- Break Even Point (Bep) Analysis of Tomato Farming Business in Taraitak I Village, Langowan District, Minahasa DistrictDocument8 pagesBreak Even Point (Bep) Analysis of Tomato Farming Business in Taraitak I Village, Langowan District, Minahasa Districtrenita lishandiNo ratings yet
- Pizza Choice: Submitted By: Submitted ToDocument11 pagesPizza Choice: Submitted By: Submitted ToNeha SharmaNo ratings yet
- 7 Financial Management Part 4Document7 pages7 Financial Management Part 4Riz CanoyNo ratings yet
- G2 Group5 FMCG Products Fair & Lovely - Ver1.1Document20 pagesG2 Group5 FMCG Products Fair & Lovely - Ver1.1intesharmemonNo ratings yet