Professional Documents
Culture Documents
A Novel Approach To Separable Reversible Data Hiding
Uploaded by
Carmel MaryOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
A Novel Approach To Separable Reversible Data Hiding
Uploaded by
Carmel MaryCopyright:
Available Formats
A Novel Approach Towards Separable Reversible
Data Hiding Technique
Vinit Agham
Tareek Pattewar
Department of Computer Engineering
R C Patel Institute of Technology,Shirpur.
Dist.Dhule, Maharashtra, India
vinitagham@gmail.com
Department of Information Technology
R C Patel Institute of Technology,Shirpur.
Dist.Dhule, Maharashtra, India
tareekpattewar@gmail.com
Abstract- Internet is
medium
now
days
the
but
most
message
popular
communication
communication
over
the
internet is facing some problem such as data security, copyright
control, data size capacity, authentication etc. There are so many
research
is
progressing
on
the
field
like
internet
security,
steganography, cryptography. When it is desired to send the
confidential/important/secure
data
over
an
insecure
and
application of reversible data hiding technique is in IPR
(Intellectual Property Rights) protection, authentication. In
some application scenarios it is essential to provide security,
authentication and privacy during communication or
transferring data. That's why to hide the data or to provide the
data security we need some new approach in communication.
bandwidth-constrained channel it is customary to encrypt as well
as
compress
the
cover
data
and
then
embed
paper introduces the new way of originating the existing concept
i.e. separable reversible data hiding. Actually the concept of
separable
reversible
data
hiding
technique
is
based
on
steganography and related with internet security. The chief
objectives of this literature is to work on the concept in which we
used text as a hidden data, no plain spatial domain is used,
attempt to increase the amount of data which is to be hide,
evaluating quality by different interpretations. The principal
SEPARABLE REVERSIBLE DATA HIDING TECHNIQUE
II.
the
confidential/important/secure data into that cover data. This
The term "reversible data hiding" means getting the exact
recovery of the data after performing the process like
encryption-decryption and data hiding. Now the question is;
what is mean by "separable reversible data hiding technique"?
The word separable means it separates two major activities in
the scheme. These two activities are getting the exact recovery
of the secure hidden data and exact recovery of cover data
which is used to hide as shown in Fig.l.
notion of separable reversible data hiding is consist of three key
procedures. First encrypt the cover media second hide the data
and third get the data as well as cover media as per provisions.
Keywords- Image encryption, image recovery, reversible data
.II!!!!!!!II
!I ..l
hiding, separable reversible data hiding, embedded data,data-hiding
key,qllality index,PSNR.
Original
I.
'm .g. -...
OVERVIEW
Now a day the data security and data integrity are the two
challenging areas for research. There are so many research is
progressing on the field like internet security, steganography,
cryptography. Sometimes we found certain distortion in images
used in military, medical science which is un-acceptable.
Hence for data hiding we have a technique using which we can
extract data correctly and after that original cover content can
be perfectly recovered. This technique is known as reversible
data hiding. This technique is also called as lossless, distortion
free, or invertible data hiding technique [1]-[2]. Reference [3]
presented a unique reversible (Iossless) data hiding technique
which enables the exact recovery of the original signal with the
extraction of the embedded information. And this exact
recovery with lossless data is nothing but the reversible data
hiding. Usually the well-known LSB (least significant bits)
method is used as the data embedding method. Reversible data
hiding is a technique that is mainly used for the authentication
of data like images, videos, electronic documents etc. The chief
978-1-4799-2900-9/14/$31.00 2014 IEEE
Encrypted image containing embedded
Rec.overed
image
..w;;;..
s-..
'+-
"IU
extracted
bits
Fig.
L The scheme of separable reversible data hiding [4].
The Author in [4] uses image as a cover medium. The
scheme is divided into three steps in the first step; a sender or
content owner encrypts the cover image using an encryption
key. Then, a data-hider compresses the least significant bits of
771
the encrypted image using a data-hiding key to create enough
space to accommodate some additional data (Secure data).Now
at receiver side it occurs three cases as shown in Fig. 2 case
one is if a receiver has the data-hiding key only he can take out
the secure data even he does not know the cover media i.e.
cover image content. In second case if the receiver has the
encryption key only, he can decrypt the received data to obtain
an image similar to the original one, but he cannot extract the
additional data. If the receiver has both the keys i.e. data-hiding
key and the encryption key he can extract the additional data
and recover the original image. Thus we are separating the two
actions i.e. exact recovery of the hidden data and recovery of
the cover media. That's why it is termed as "Separable
Reversible Data Hiding Technique" which is reversible as well
as separable in nature.
III.
MOTIVATION AND RELATED WORK
Most of the reversible data hiding techniques are not
separable, not based on encryption-decryption domain, not
based on RGB-LSB steganography. Here presents the small
survey that reveals what techniques have been used for
compression-decompression,
encryption-decryption,
data
embedding etc.
Reversible data hiding technique includes following
actions
like
compression-decompression,
encryption
decryption, data embedding-data extracting, creating space at
LSB of the pixels of the image, providing security,
authentication using automatic key generation and etc. The
traditional way of transmitting redundant data is to first
compress the data to reduce the redundancy and then to
encrypt the compressed data. At the receiver side the
decryption and decompression operations are orderly
performed to recover the original cover data. However in
some applications a sender needs to transmit some data to the
receiver and wishes to keep the information confidential to a
network operator who provides the channel resource for the
transmission, means the sender should encrypt the original
data i.e. image in this case and the network provider compress
the encrypted data without any knowledge of the
cryptographic key and the original data. At receiver side to
reconstruct the original data, a decoder integrating
decompression and decryption functions will be used.
There
are
several
techniques
for
compressing/decompressing encrypted data have been
developed. When it is desired to transmit redundant data over
an insecure and bandwidth-constrained channel, it is usual to
first compress the data and then encrypt it. In [5] these steps
are in reverse order of that is first encrypting and then
compressing without compromising either the compression
efficiency or the security. They have examined the possibility
of first encrypting a data stream and then compressing it, such
that the compressor does not have knowledge of the
encryption key.
Reference [6] suggested a lossless compression method for
encrypted gray image using resolution progressive
decomposition in which there is much better coding efficiency
and less computational complexity. In this paper [6] resolution
progressive compression scheme was implemented which
compresses an encrypted image progressively in resolution
such that the decoder can observe a low-resolution version of
the image, studies the statistics based on it and use this
statistics to decode the next resolution level and this process
iterates until last level of resolution. Here the image
undergoes
stream-cipher
based
encryption
before
compression.
In paper [7] there is a buyer-seller watermarking protocol
which is the concept of digital watermarking. In this protocol
the seller does not get to know the exact watermarked copy
that the buyer receives.Hence seller cannot create duplicates of
EKternal data/pay
the keys
Case 3
::]
::::::::
c.:a:s:e2-------------------1t-------17f:re :c a:-v:erh:as------------
If re c: e.i ver has
encrvp
'0'
cad
If .- e.ce l ver has bo
key o n l ..,
Decryption
...
data h id i n g
kevonlv
+
wi t h hidden dot ..
original cover Image
EKternal d ata/ p a y load
Fig. 2. Separable reversible data hiding with three cases.
772
2014 International Conference on Issues and Challenges in Intelligent Computing Techniques (ICICT)
the original content containing the buyer watermark. However,
in case the seller finds an unauthorized copy, he can identify
the buyer from whom this unauthorized copy has originated.
The watermark embedding protocol is based on public key
cryptography and has little overhead in terms of the total data
communicated between the buyer and the seller. This scheme
also stated the concept of hiding the data in encrypted form of
the data. Here seller is doing data (fingerprint/Watermark in
this case) embedding while he does not know the original data
content thus invisible watermarking. The original data content
is in the encrypted form [7] .
Most o f the work on reversible data hiding focuses on the
data embedding/extracting on the plain spatial domain. But in
some applications it is important to append some additional
message within the encrypted image however data hider does
not know the original image content. And it is also expected
that the original content should be recovered without any error
after image decryption and message extraction at receiver side.
It leads to the strong security based reversible data hiding that
it should work in encryption-decryption domain.
Reference [3] offered a practical scheme satisfying
the above-mentioned requirements. A content owner encrypts
the original cover image using an encryption key and a data
hider could embed additional data into the encrypted image
using a data-hiding key although he does not know the
original content. Having an encrypted image containing
additional data a receiver first decrypts it according to the
encryption key, and then extracts the embedded data and
recovers the original image according to the data-hiding key.
In the scheme the procedure of data extraction is not separable
from the content decryption. In other words, the principal
content of original image is revealed before payload
extraction, and, if someone has the data-hiding key only but
not the encryption key he is unable to extract any information
from the encrypted image containing additional data [3].
much text can be hiding into the image. For these reasons it is
important to take these issues into consideration.
As shown in Fig.l, in separable scheme, the content owner
encrypts the original uncompressed image using an encryption
key to produce an encrypted image. Then using a data-hiding
key the data-hider compresses the least significant bits (LSB)
of the encrypted image to create some space to accommodate
the additional data. At the receiver side the data embedded can
be easily retrieved from the encrypted image containing
additional data according to the data-hiding key. Because the
data embedding only affects the LSB of the cover image;
decryption may result in an image similar to the original
version. Here at the receiver side there exists three cases as
shown in Fig.2, case one is when the receiver has only the
data- hiding key, he is able to extract the additional data even
if he does not know the image content. Case two is if he has
only the encryption key, he can decrypt the received data i.e.
encrypted image to obtain an image similar to the original
cover media, but cannot extract the embedded additional data.
Case three is if the receiver has both the keys i.e. data-hiding
key and the encryption key, he can extract the additional data
and recovers the original image without any error. This new
approach of separable reversible data hiding method consists
of three main procedures,
A.
Selecting the cover image and make it encrypted
B.
Hiding the data
C.
Data extraction/image recovery process
A. Selecting the cover image and make it encrypted
Select the appropriate cover image in which we want to add
the data. The cover image can be of any format like jpg, jpeg,
png, gif, bmp etc. Assume that the pixels of original selected
image is ranging into [0,255] is represented by 8 bits. Denote
these bits of a pixel as seven bits. That implies
hi.j.k,u
IV.
METHODOLOGY
In common there are two kinds of reversible data hiding
techniques (according to key distribution) separable reversible
data hiding technique and non-separable reversible data hiding
technique (also called as reversible data hiding).As we know in
separable reversible data hiding we are separating two
activities i.e. cover image decryption and pay load data
lPi,j.kl2U JIIDd 2
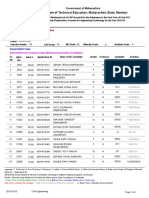
DATA CAPACITY TO EMBED IN THE IMAGE AND RELATED
PSNR
Sr.No.
Payload (In
Approximate text
PSNR
number
file size
recovered
words)
500
2
3
4
of
(in
KB)
of
image
45.8573
1000
6.41
42.9012
1500
9.61
41.1306
2000
13. 3
39.946
0 , 1 , 2. . . .... 7
(I)
(2)
pi,j,k Lbi,j,k.". 2"
=
11=0
In this encryption phase, the exclusive-or results of the
original bits and pseudo-random bits are calculated as
=
(3)
bi,}, k,lI (f) ri,}, k,lI
Where ri,},k,u are determined by an encryption key using a
standard stream cipher.
after
decryption(in dB)
3.20
and
Bi,}, k,u
TABLE l.
extraction. In addition to this there are some further issues
related with existing separable data hiding method.
The domain used for data hiding in this new approach is
based on an image Encryption-Decryption domain. That is the
cover image in which the secure data is to be hide is encrypted
first or make it distorted. And then the data hider compresses
that encrypted version of the cover image to make a room for
additional data (Secured data).
The secure data which is to be hide used in this new
approach is large enough text data. Table I shows the how
B. Hiding the data
In this step of data embedding; data is converted into
binary
form
so
that
bits
of
the
data
i.e.
B(c1,I),B(c1,2),....., B(c1,8),......., B(cn,8) can be embedded into
LSB of the cover image. Here the data we embedded is text so
c1 is single character in the text and en means numbers of
characters are there in the text. Actually the characters in the
text are represented by their ASCII value and that value is
converted into binary format thus we get the bits of the text.
According to a data-hiding key, the data-hider randomly
selects encrypted pixels. For each pixel least significant bits
and indicate them as Bi,},k,u where u 5,6,7,8 these are the
bits used to carry the bits of the text. Here actually it requires
two pixels to store eight bits or single character. Because we
are storing the text bits only into LSB of the image pixels that
last four bits per pixel in this case. Now replace the LSB of
=
20J4 Internationai Conference on Issues and Challenges in Intelligent Computing Techniques (ICICT)
773
randomly selected encrypted pixels with the bits of the
text B(el,I),B(el,2),....., B(el,8), ......., B(cn,8) .
The embedding rate, a ratio between the data amount of
net payload and the total number of cover pixels, is
ER=
total no characters in the text(payloadj
total_no_of _cover _pixels
(4)
C. Data extraction/image recovery process
In this step, we will consider the three cases at the receiver
side that a receiver has the data-hiding key only, the encryption
key only, and both the data-hiding as well as encryption keys
respectively.
Case one is with an encrypted image containing the
embedded data if the receiver knows only a data-hiding key, he
first get the values of the LSB of the encrypted image
containing secure text. Now these bits contains the bits of the
text so extract the two group of LSB of the image pixel each
having four bits then make a group of eight bits i.e. a byte then
convert that byte into equivalent value since this is the ASCII
value of the character of the text. Finally transfer that value
into equivalent character so that we get the complete text as a
string.
Note that since the random pixel selection, any attacker
without the knowledge data-hiding key cannot obtain the
values and the statistics about pixel-groups, for that reason he
cannot extract the embedded data. Furthermore, while the
receiver having the data-hiding key can successfully extract the
embedded data, he is unable get any information about the
original image content.
Consider the second case in which the receiver has the
encryption key but does not know the data-hiding key. Clearly,
he cannot extract the embedded data. But, the original image
content can be roughly recovered at the receiver. Denoting the
bits of pixels in the image containing embedded data as
B'i,j,k,O, B'i,j.k.I,.B'i,j,k,2,......... ..... B'i,j,k,7 the receiver can decrypt
the received data
h'i,j,k,l/
B'i,j,k,l/ iCBri,j,k,l/
(5)
Since the data-embedding operation does not alter any
MSB of encrypted image, the decrypted MSB must be same as
the original MSB. So the content of decrypted image is similar
to that of original cover image. The Mean Square Error for that
decrypted image is
V.
EVALUATION METHODOLOGY
In this new approach we are concentrating on how the
performance of the current scheme can be increased by
considering few issues like
A.Increase the amount of data to be hide
The present scope of the technique is that the author in [4]
has suggested the method of separable reversible data hiding
when the amount of secure data is not too large. Size of the
data must be small. So we need such approach which will
overcome this size limitation. Here in proposed system we are
trying to embed large amount of data into encrypted version of
the cover image. By observing Table 1 it is clear that the
proposed separable scheme can handle enough data for
security.
B. Getting higher PSNR of the decrypted version of the cover
image
The proposed scheme's main advantage is that we recover
the original cover image successfully without error and having
minimum or zero distortion. Here we are interested in PSNR
of the decrypted cover image after performing encryption
decryption, data hiding and data extracting process. As shown
in Fig. 3 it is clear that there is very negligible loss in
decrypted image since we get the high PSNR values. How the
quality is maintained even after performing encryption
decryption, data hiding and data extracting process on the
image is shown in Fig. 3.
60
__ PSNR of decrypted image
50
<C
...
;;:
40
c:
:z
(I)
c..
30
20
10
0
0
0.05
0.1
0 .15
0.2
0.25
Embedded rate
(6)
Fig. 3. Achieving higher PSNR of decrypted version of the cover image.
1.005
Where D is the difference of original cover image contains
and
the
decrypted
cover
image
contains.
So, the value of PSNR in the directly decrypted image is
PSNR=20.10g12551 MSE)
0.995
(7)
Consider the third case in which the receiver has both the
data-hiding and the encryption keys, he may aim to extract the
embedded data i.e. text and recover the original image. Here
according to the data-hiding key the receiver first get the values
of the LSB of the encrypted image containing secure text since
the further procedure is same as in case one. Similar to the case
two if the receiver has encryption key he can easily get the
original cover image.
.Orange.jpg
..
0.99
.S:
Leaves. jpg
.....
-
a 0.985
"
..,..
-Lena.jpg
0.98
;; 0.975
..
a
0.97
0.965
0
0.02 0 .040.06 0.08 0.1 0.12 0.140.16 0.18 0.2 0.22 0.24
embedded rate
Fig. 4. Observing high quality index.
774
2014 International Conference on Issues and Challenges in Intelligent Computing Techniques (ICICT)
C.
scheme. Sometime the secure data can be in any form rather
Observing high quality index.
The normal range of universal quality index is -1 to
I.Higher quality index hints to better quality. It is observed
that
we get the unit quality index
than text for example an image. So in such situation we will
have to hide an image data into cover image.
for various possible
embedded rate and for various images as shown in Fig. 4.1t
also shows how the quality index ranges from 0.98 to l.00 .
So it is concluded that the quality is not compromising in any
REFERENCES
[I ]
Z. Ni, Y.-Q. Shi, N. Ansari, and W. Su, "Reversible data hiding," IEEE
Trans. Circuits Syst. Video Techno!., vo!' 16, no. 3, pp. 354-362,
Mar.2006.
way.
[2 ]
CONCLUSION
The main objective of this study is to describe the concept
of separable reversible data hiding using new approach. This
new approach describes how we can maintain the performance
after increasing the amount of payload. So after studying this
Aug. 2003.
[3 ]
X. Zhang, "Reversible data hiding in encrypted image," IEEE Signal
[4 ]
X Zhang, "Separable Reversible Data Hiding in Encrypted Image",
pp. 826-832,Apr.2012.
[5 ]
as well as quality of the cover image. In this scheme we are not
degrading the quality of the cover media as we get the unit
quality index of original cover image and the image after
encryption-decryption, data hiding and data extracting process
M. Johnson, P. Ishwar, V. M. Prabhakaran, D. Schonberg, and K.
Ramchandran, "On compressing encrypted data," IEEE Trans. Signal
Process., vo!. 52, no. 10, pp. 2992-3006, Oct. 2004.
[6 ]
encryption-decryption, data hiding process. Also higher PSNR
of the decrypted cover image is observed after performing
Process. Lett., vo!. 18, no. 4, pp. 255-258, Apr. 20I I.
IEEE transactions on information forensics and security, vo!. 7, no. 2,
novel technique it has been concluded that it is possible to hide
enough or large amount of data without compromising security
J. Tian, "Reversible data embedding using a difference expansion,"
IEEE Trans. Circuits Syst. Video Techno!., vo!' 13, no. 8, pp. 890-896,
W. Liu, W. Zeng, L. Dong, and Q. Yao, "Efficient compression of
encrypted grayscale images," IEEE Trans. Image Process., vol. 19, no.
4,pp. 1097-1102, Apr. 2010.
[7]
N. Memon and P. W. Wong, "A buyer-seller watermarking protocol,"
IEEE Trans. Image Process., vo!. 10, no. 4, pp. 643-649, Apr. 2001.
on cover image. Still there can be more future aspects in this
20J4 Internationai Conference on Issues and Challenges in Intelligent Computing Techniques (ICICT)
775
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (345)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (121)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (400)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- DIGOO DG-Series User ManualDocument17 pagesDIGOO DG-Series User ManualLoon K50% (2)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Site Acceptance Test PlanDocument12 pagesSite Acceptance Test PlanUmar Adamu83% (6)
- Rotax Karting - Repair Manual, FR 125 MaxDocument54 pagesRotax Karting - Repair Manual, FR 125 MaxToniNo ratings yet
- Scada Compone NTS: Prepared By:-Animesh Ghosh Roll No - 4 M.Tech (EE)Document28 pagesScada Compone NTS: Prepared By:-Animesh Ghosh Roll No - 4 M.Tech (EE)Animesh GhoshNo ratings yet
- Diploma - VIII Fabrication Engg SyllabusDocument52 pagesDiploma - VIII Fabrication Engg Syllabusprashant4455No ratings yet
- ABAP Proxy (Complete Developments On SAP-PI &am..Document7 pagesABAP Proxy (Complete Developments On SAP-PI &am..saranpcNo ratings yet
- STM32F4 Discovery ProjectsDocument11 pagesSTM32F4 Discovery ProjectsAkhmad MuntakoNo ratings yet
- Water Pipe Robot With Soft Inflatable ActuatorsDocument7 pagesWater Pipe Robot With Soft Inflatable ActuatorseyaoNo ratings yet
- CNG Relief Valve v5.1 PDFDocument2 pagesCNG Relief Valve v5.1 PDFDavid EspinozaNo ratings yet
- Vipul Bansal: Career ObjectiveDocument3 pagesVipul Bansal: Career ObjectiveVipul BansalNo ratings yet
- Toc Adrm 10thed 3rd Release 20150901Document4 pagesToc Adrm 10thed 3rd Release 20150901Bảo Đức0% (1)
- 424 Amardeep SinghDocument2 pages424 Amardeep SinghJuhi ShahNo ratings yet
- DeeptiDocument40 pagesDeeptiVini VinayNo ratings yet
- Core Switch Sbx908 - Gen2Document8 pagesCore Switch Sbx908 - Gen2naveedfndNo ratings yet
- Eee (Ece) f311 2022 HandoutDocument3 pagesEee (Ece) f311 2022 HandoutSubhash GowaniNo ratings yet
- AWS Cost OptimisationDocument49 pagesAWS Cost OptimisationeraviraltiwariNo ratings yet
- Cisco NCS 540Document12 pagesCisco NCS 540Samir Ben Hassen0% (1)
- EmpTech11 Q1 Mod2 Productivity-Tools Ver3Document74 pagesEmpTech11 Q1 Mod2 Productivity-Tools Ver3Frances A. PalecNo ratings yet
- BSC Card Overview and FunctionDocument35 pagesBSC Card Overview and Functionkamal100% (1)
- Interplay of Legal Frameworks and Artificial Intelligence (AI) : A Global PerspectiveDocument25 pagesInterplay of Legal Frameworks and Artificial Intelligence (AI) : A Global PerspectiveLAW & POLICY REVIEWNo ratings yet
- CM ConditionerDocument2 pagesCM ConditionerCarlos Luis Acosta CastellanoNo ratings yet
- Capr-Ii 2013Document46 pagesCapr-Ii 2013Pramod DhaigudeNo ratings yet
- War Zone (2) .GPCDocument10 pagesWar Zone (2) .GPCimahdi0707No ratings yet
- Butt (0.1.28) Manual: Daniel NöthenDocument11 pagesButt (0.1.28) Manual: Daniel NöthenDiego León Giraldo GNo ratings yet
- MTZ Worldwide April 2011 PDFDocument63 pagesMTZ Worldwide April 2011 PDFTamara SiqueiraNo ratings yet
- Professional Talk Summary ReportDocument2 pagesProfessional Talk Summary ReportUstaziyatul Alam0% (1)
- Termostato Analogico Siemens Raa31 XaDocument6 pagesTermostato Analogico Siemens Raa31 XaIsaNo ratings yet
- Ngconf 2018 - RoutingDocument50 pagesNgconf 2018 - RoutingκβηξκλκξηNo ratings yet
- 9.1.13.5 Dry Type Transformer User ManualDocument6 pages9.1.13.5 Dry Type Transformer User ManualDindie GarvidaNo ratings yet
- Notes-Chapter 1Document5 pagesNotes-Chapter 1Echa LassimNo ratings yet