Professional Documents
Culture Documents
Campus Information System
Uploaded by
Ghumare SachinCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Campus Information System
Uploaded by
Ghumare SachinCopyright:
Available Formats
PROJECT REPORT
GreenWich
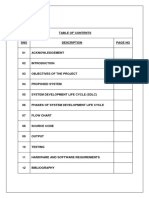
CONTENTS
DESCRIPTION
PAGENO
ABSTRACT
INTRODUCTION
ORGANIZATION PROFILE
MODULE DESCRIPTION
TECHNOLOGY
DATAFLOW DIAGRAMS
SOFTWARE REQUIREMENTS
HARDWARE REQUIREMENTS
OVERVIEW OF .NET TECHNOLOGY
OUTPUTS
CONCLUSION
BIBLIOGRAPHY
-1-
PROJECT REPORT
GreenWich
ABSTRACT
Advances in technology and the growth of Integrated Collage Management System to
provide educators and trainers with unique opportunities to enhance learning and
teaching in corporate, government, healthcare, and higher education. This application
serves as a forum to facilitate the exchange of information on the current research,
development, and practice of Integrated Collage Management System in the sectors.
It includes the research, development, and practice of Integrated Collage
Management System related to the following multi-dimensional topics and sub-topics.
GreenWich comes in different configurations that dictate the depth of a needs
assessment. The simple Integrated Collage Management System implementations,
such as those following an application service provider (ASP) model, won't
necessarily look any different from a resource requirement perspective than traditional
classroom training. That's GreenWich.
GreenWich can be an enormous undertaking and, require significantly more
preparation due to its increased scope, higher interdependence, and visibility. These
factors--described below--are the reason a needs assessment for an Integrated
Collage Management System initiative looks different from one for a traditional
classroom program.
Scope. Developing an Integrated Collage Management System initiative is a
typically much larger endeavor than that of an instructor-led training (ILT)
program. Consider the increased expenses, number of people involved,
development time, technological requirements, and delivery options.
-2-
PROJECT REPORT
GreenWich
Interdependence. It's possible, even common, for an ILT program to be
conducted without the knowledge of anyone but the participants, their
immediate managers, and the training provider. In contrast, even the smallest
Integrated Collage Management System program requires a wider group of
people. Ranging from (at a minimum) representatives from the IT and HR
departments to (more commonly) an organization-wide task force, the scope of
the project often dictates that there are more decision makers, more
stakeholders, and more links between previously unrelated departments.
Visibility. When a traditional training program goes bad, a participant's
dissatisfaction is usually voiced by word of mouth. And the people who express
dissatisfaction, in most cases, are the participants and, maybe later, the people
directly affected by their work. Again, due to the scope of the undertaking
(especially the high budget and number of resources required), the efficacy of
an Integrated Collage Management System program will be delivered to a
larger group of people and through a wider variety of channels than an ILT
program. Typically, a CEO can tap into a training database and view
participants' course comments, exam results, and the courses taken. It's easier
to determine whether an Integrated Collage Management System program is
unpopular or ineffective than to rely on word of mouth about a questionable ILT
program.
INTRODUCTION
In order for a needs assessment to have a successful outcome, it must accomplish
many things--improving performance being just one. It must also
determine how to achieve the high-level goals of the organization (such as
increasing sales and fostering innovation)
-3-
PROJECT REPORT
GreenWich
determine what system obstacles (other than training) need to be removed
point to an intervention that will balance the conflicting needs of different
stakeholders (IT versus HR, participants versus managers, budget versus
vendor costs, and so on)
Pave the way for a new program.
Organizations implementing Integrated Collage Management System programs need
to expand the usual needs assessment process by creating a high-level requirements
document that includes
objectives (macro organizational objectives and micro target learner population
objectives)
an Integrated Collage Management System readiness score
a list of advantages and potential obstacles to Integrated Collage Management
System adoption
a list of possible Integrated Collage Management System configurations.
We apply technology with innovation and responsibility to achieve two broad
objectives:
Effectively address the business issues our customers face today
Generate new opportunities that will help them stay ahead in the future
This approach rests on:
A strategy where we Architect, Integrate and Manage technology services and
solutions we call it AIM for success.
-4-
PROJECT REPORT
GreenWich
A robust offshore development methodology and reduced demand on customer
resources
A focus on the use of reusable frameworks to provide cost and time benefits
We combine the best people, processes and technology to achieve excellent results
consistently. We offer customers the advantages of:
Speed : We understand the importance of timing, of getting there before the
competition. A rich portfolio of reusable, modular frameworks helps jump-start
projects. Tried and tested methodology ensures that we follow a predictable, low-risk
path to achieve results. Our track record is testimony to complex projects delivered
within and even before schedule.
Expertise : Our teams combine cutting edge technology skills with rich domain
expertise. What's equally important we share a strong customer orientation that
means we actually start by listening to the customer. We're focused on coming up
with solutions that serve customer requirements today and anticipate future needs.
A Full Service Portfolio: We offer customers the advantage of being able to
Architect, Integrate and Manage technology services. This means that they can rely
on one, fully accountable source instead of trying to integrate disparate multi-vendor
solutions.
Services:GSS is providing its services to Sain medicaments Pvt. Ltd, Grace drugs
and pharmaceuticals pvt ltd alka drugs and pharmaceuticals pvt ltd to name just a few
with out rich experience and expertise in Information Technology we are in the best
position to provide software solutions to distinct business requirements.
-5-
PROJECT REPORT
GreenWich
MODULES
Administration
User Management
Content Management
Evaluation
MODULE DESCRIPTION
Administration:
Uploading the content permanently
Uploading the content temporally
Removing the content permanently
Removing the content temporally
Working options
o Caching Feature
o Content length for each Category
User Management:
User Information
User Session Maintenance
Updating User Information
Content Management:
-6-
PROJECT REPORT
GreenWich
These are the pages that are associated with the logic pages, and
contain content specific to that page.
Organizing the topics according to the category
Organizing the subtopics according to the subcategory
Providing appropriate links to specified category
Evaluation
Preparing the question paper randomly according to the category
Spot result evaluation
Specifying level of evaluation
TECHNOLOGY
Technology Used:
.Net
IIS
Oracle
Operating System:
o Windows
DATA FLOW DIAGRAMS
Data flow diagram is a structure analysis tool that is used for graphical
representation of Data processes through any organization . the data flow approach
-7-
PROJECT REPORT
GreenWich
emphasis on the logic underlying the system, by using combination of only 4 symbols.
It follows a top down approach. A full description of a system actually consists of set
of DFD s , which comprises of various levels. And initial over view model is exploded
lower level diagrams that show additional feature of the system. Further each process
can be broken down into a more detailed DFD. This occurs repeatedly until sufficient
details is described.
DFD symbols
square
it defines a source (originator ) or destination of system data.
Arrow
It indicates data flow-data in motion. It is a pipeline through which
information flows.
Circle or Bubble
It represents a process that transforms incoming data flow(s) into outgoing data
flow(s).
-8-
PROJECT REPORT
GreenWich
Open Rectangle
it is a data store-data at rest, or a temporary repository of data. Here I am giving only
the Data Flow Diagram.
They are explained by
GANE and SARON method
DEMACRO YORDAN method
-9-
PROJECT REPORT
GreenWich
GANE
AND
DATA FLOW
DATA STRUCTURE
EXTERNAL ENTITY
OR
DATA LINK
PROCESS
- 10 -
SARSON NOTATION
PROJECT REPORT
GreenWich
DATA BASE
DEMACRO YORDAN NOTATION
DATA FLOW
DATA STRUCTURE
EXTERNAL ENTITY
OR
DATA LINK
PROCESS
- 11 -
PROJECT REPORT
GreenWich
DATA BASE
CONTEXT LEVEL DIAGRAM
- 12 -
PROJECT REPORT
GreenWich
- 13 -
PROJECT REPORT
GreenWich
E R DIAGRAMS.
- 14 -
PROJECT REPORT
GreenWich
- 15 -
PROJECT REPORT
GreenWich
- 16 -
PROJECT REPORT
GreenWich
UML ANALYSIS
- 17 -
PROJECT REPORT
GreenWich
Courses
Course
Reg
New course
Examination
Staff
appointment
Student
Content mgmt
Registration
Administrator
Staff Details
Qestions
- 18 -
PROJECT REPORT
GreenWich
Sequence Diagram
Admin
Student
Courses
Register A New Course
Modify of
Students Session
Modification of
Courses
Cancellation of
Courses / Staff
Register a Course ()
Accepted / Rejected the
Registration of Course()
Request for Staff ( )
Result evaluations of
Request for Extension
Accepted / Rejected the
of the Scheduled Time ()
Request of the Student()
`
Updating on Courses
- 19 -
the
Student
Staff
PROJECT REPORT
GreenWich
GUI Component
Menu
Report
Options
<<instantiates>>
Data Store
Input Screen
Greenwich
<<uses>>
User_Sub
User_Main
students
Stafff
Data Manipulator
Student det
Staff det
Profile Manipulation Search by course
Course det
evaluation
- 20 -
Questions
Content dev
Discussions
PROJECT REPORT
GreenWich
State diagram for registration process
Validate
User Input Accept User Details User/Admin
- 21 -
Specify user/Admin
PROJECT REPORT
GreenWich
DATA DICTIONARY.
Database Design:
T_Admin
T_CourseReg
T_Courses
T_Emp_Personal
- 22 -
PROJECT REPORT
GreenWich
Staff_Master
- 23 -
PROJECT REPORT
GreenWich
HARDWARE & SOFTWARE SPECIFICATIONS
HARDWARE REQUIREMENTS:
PIII
500MHZ or above
128MB RAM
100MB Free Hard disk space
STD Color Monitor
Network interface card or Modem (For Remote Access)
LAN Network (For Remote Aources)
SOFTWARE REQUIREMENTS:
WINDOWS NT 4 | 2000 | 9.X | ME
Visual Studio .Net 2002 Enterprise Edition
Visual Studio .Net Framework (Minimal for Deployment)
- 24 -
PROJECT REPORT
GreenWich
STUDY OF THE SYSTEM
Creating Database:
Microsoft SQL Server server management comprises a wide variety of
administration tasks, including:
Registering servers and assigning passwords.
Reconfiguring network connectivity.
Configuring standby servers.
Setting server configuration options.
Managing SQL Server messages. Etc
In most cases, you do not need to reconfigure the server. The default settings
for the server components, configured during SQL Server Setup, allow you to
run SQL Server immediately after it is installed. However, server management
is necessary in those situations where you want to add new servers, set up
special server configurations, change the network connections, or set server
configuration options to improve SQL Server performance.
Creating a Database
To create a database determine the name of the database, its owner (the user
who creates the database), its size, and the files and filegroups used to store
it.
Before creating a database, consider that:
- 25 -
PROJECT REPORT
GreenWich
Permission to create a database defaults to members of the sysadmin
and dbcreator fixed server roles, although permissions can be granted
to other users.
The user who creates the database becomes the owner of the database.
A maximum of 32,767 databases can be created on a server.
The name of the database must follow the rules for identifiers.
Three types of files are used to store a database:
Primary files
These files contain the startup information for the database. The
primary files are also used to store data. Every database has one
primary file.
Secondary files
These files hold all the data that does not fit in the primary data file.
Databases do not need secondary data files if the primary file is large
enough to hold all the data in the database. Some databases may be
large enough to need multiple secondary data files, or they may use
secondary files on separate disk drives to spread the data across
multiple disks.
Transaction log
- 26 -
PROJECT REPORT
GreenWich
These files hold the log information used to recover the database. There
must be at least one transaction log file for each database, although
there may be more than one. The minimum size for a log file is 512
kilobytes (KB).
When a database is created, all the files that comprise the database are filled
with zeros to overwrite any existing data left on the disk by previously deleted
files. Although this means that the files take longer to create, this action
prevents the operating system from having to fill the files with zeros when
data is written to the files for the first time during usual database operations.
This improves the performance of day-to-day operations.
Create a database using the Create Database Wizard (Enterprise Manager)
To create a database using the Create Database Wizard
1. Expand a server group, and then expand the server in which to create a database.
2.
3.
4.
5.
On the Tools menu, click Wizards.
Expand Database.
Double-click Create Database Wizard.
Complete the steps in the wizard.
Creating and Modifying a Table
- 27 -
PROJECT REPORT
GreenWich
After you have designed the database , the tables that will store the data in
the database can be created. The data is usually stored in permanent tables.
Tables are stored in the database files until they are deleted and are available
to any user who has the appropriate permissions.
Temporary Tables
You can also create temporary tables. Temporary tables are similar to
permanent tables, except temporary tables are stored in tempdb and are
deleted automatically when no longer in use.
The two types of temporary tables, local and global, differ from each other in
their names, their visibility, and their availability. Local temporary tables
have a single number sign (#) as the first character of their names; they are
visible only to the current connection for the user; and they are deleted when
the user disconnects from instances of Microsoft SQL Server 2000. Global
temporary tables have two number signs (##) as the first characters of their
names; they are visible to any user after they are created; and they are
deleted when all users referencing the table disconnect from SQL Server.
For example, if you create a table named employees, the table can be used
by any person who has the security permissions in the database to use it,
until the table is deleted. If you create a local temporary table named
#employees, you are the only person who can work with the table, and it is
deleted when you disconnect. If you create a global temporary table named
##employees, any user in the database can work with this table. If no other
- 28 -
PROJECT REPORT
GreenWich
user works with this table after you create it, the table is deleted when you
disconnect. If another user works with the table after you create it, SQL
Server deletes it when both of you disconnect.
Table Properties
You can define up to 1,024 columns per table. Table and column names must
follow the rules for identifiers; they must be unique within a given table, but
you can use the same column name in different tables in the same database.
You must also define a data type for each column.
Although table names must be unique for each owner within a database, you
can create multiple tables with the same name if you specify different owners
for each. You can create two tables named employees and designate Jonah
as the owner of one and Sally as the owner of the other. When you need to
work with one of the employees tables, you can distinguish between the two
tables by specifying the owner with the name of the table.
The
above
task
can
be
achieved
by
using
the
component
ASPEnterprisemanager which is part of the application. The component
provides various methods in which a user can interact with the sql server
resources located on a remote computer.
Before using the component the component has to attached to the
application which can be done by double clicking on the solution name on
the solution explorer. Browse the component and attach to the solution. Once
- 29 -
PROJECT REPORT
GreenWich
the component is attached. The component can be used by importing it into
the application as.
Imports system.aspenterprisemanager
By importing the component all the methods of the component can be
used to interact with the SQL server.
- 30 -
PROJECT REPORT
GreenWich
SELECTED SOFTWARE
Microsoft.NET Framework
The .NET Framework is a new computing platform that simplifies
application development in the highly distributed environment of the
- 31 -
PROJECT REPORT
GreenWich
Internet. The .NET Framework is designed to fulfill the following
objectives:
To provide a consistent object-oriented programming environment
whether object code is stored and executed locally, executed locally
but Internet-distributed, or executed remotely.
To provide a code-execution environment that minimizes software
deployment and versioning conflicts.
To provide a code-execution environment that guarantees safe
execution of code, including code created by an unknown or semitrusted third party.
To provide a code-execution environment that eliminates the
performance problems of scripted or interpreted environments.
To make the developer experience consistent across widely varying
types of applications, such as Windows-based applications and
Web-based applications.
To build all communication on industry standards to ensure that
code based on the .NET Framework can integrate with any other
code.
The .NET Framework has two main components: the common language
runtime and the .NET Framework class library. The common language
runtime is the foundation of the .NET Framework. You can think of the
- 32 -
PROJECT REPORT
GreenWich
runtime as an agent that manages code at execution time, providing
core services such as memory management, thread management, and
remoting, while also enforcing strict type safety and other forms of code
accuracy that ensure security and robustness. In fact, the concept of
code management is a fundamental principle of the runtime. Code that
targets the runtime is known as managed code, while code that does
not target the runtime is known as unmanaged code. The class library,
the other main component of the .NET Framework, is a comprehensive,
object-oriented collection of reusable types that you can use to develop
applications ranging from traditional command-line or graphical user
interface (GUI) applications to applications based on the latest
innovations provided by ASP.NET, such as Web Forms and XML Web
services.
The .NET Framework can be hosted by unmanaged components that
load the common language runtime into their processes and initiate the
execution of managed code, thereby creating a software environment
that can exploit both managed and unmanaged features. The .NET
- 33 -
PROJECT REPORT
GreenWich
Framework not only provides several runtime hosts, but also supports
the development of third-party runtime hosts.
For example, ASP.NET hosts the runtime to provide a scalable, serverside environment for managed code. ASP.NET works directly with the
runtime to enable Web Forms applications and XML Web services, both
of which are discussed later in this topic.
Internet Explorer is an example of an unmanaged application that hosts
the runtime (in the form of a MIME type extension). Using Internet
Explorer to host the runtime enables you to embed managed
components or Windows Forms controls in HTML documents. Hosting
the runtime in this way makes managed mobile code (similar to
Microsoft
ActiveX
controls)
possible,
but
with
significant
improvements that only managed code can offer, such as semi-trusted
execution and secure isolated file storage.
The following illustration shows the relationship of the common
language runtime and the class library to your applications and to the
- 34 -
PROJECT REPORT
GreenWich
overall system. The illustration also shows how managed code operates
within a larger architecture.
Features of the Common Language Runtime
The common language runtime manages memory, thread execution,
code execution, code safety verification, compilation, and other system
services. These features are intrinsic to the managed code that runs on
the common language runtime.
With regards to security, managed components are awarded varying
degrees of trust, depending on a number of factors that include their
origin (such as the Internet, enterprise network, or local computer).
This means that a managed component might or might not be able to
perform file-access operations, registry-access operations, or other
sensitive functions, even if it is being used in the same active
application.
The runtime enforces code access security. For example, users can trust
that an executable embedded in a Web page can play an animation on
- 35 -
PROJECT REPORT
GreenWich
screen or sing a song, but cannot access their personal data, file
system, or network. The security features of the runtime thus enable
legitimate Internet-deployed software to be exceptionally feature rich.
The runtime also enforces code robustness by implementing a strict
type- and code-verification infrastructure called the common type
system (CTS). The CTS ensures that all managed code is selfdescribing. The various Microsoft and third-party language compilers
generate managed code that conforms to the CTS. This means that
managed code can consume other managed types and instances, while
strictly enforcing type fidelity and type safety.
In addition, the managed environment of the runtime eliminates many
common software issues. For example, the runtime automatically
handles object layout and manages references to objects, releasing them
when they are no longer being used. This automatic memory
- 36 -
PROJECT REPORT
GreenWich
management resolves the two most common application errors, memory
leaks and invalid memory references.
The runtime also accelerates developer productivity. For example,
programmers can write applications in their development language of
choice, yet take full advantage of the runtime, the class library, and
components written in other languages by other developers. Any
compiler vendor who chooses to target the runtime can do so. Language
compilers that target the .NET Framework make the features of the
.NET Framework available to existing code written in that language,
greatly easing the migration process for existing applications.
While the runtime is designed for the software of the future, it also
supports software of today and yesterday. Interoperability between
managed and unmanaged code enables developers to continue to use
necessary COM components and DLLs.
The runtime is designed to enhance performance. Although the
common language runtime provides many standard runtime services,
- 37 -
PROJECT REPORT
GreenWich
managed code is never interpreted. A feature called just-in-time (JIT)
compiling enables all managed code to run in the native machine
language of the system on which it is executing. Meanwhile, the
memory manager removes the possibilities of fragmented memory and
increases memory locality-of-reference to further increase performance.
Finally, the runtime can be hosted by high-performance, server-side
applications, such as Microsoft SQL Server and Internet Information
Services (IIS). This infrastructure enables you to use managed code to
write your business logic, while still enjoying the superior performance
of the industry's best enterprise servers that support runtime hosting.
.NET Framework Class Library
The .NET Framework class library is a collection of reusable types that
tightly integrate with the common language runtime. The class library
is object oriented, providing types from which your own managed code
- 38 -
PROJECT REPORT
GreenWich
can derive functionality. This not only makes the .NET Framework types
easy to use, but also reduces the time associated with learning new
features of the .NET Framework. In addition, third-party components
can integrate seamlessly with classes in the .NET Framework.
For example, the .NET Framework collection classes implement a set of
interfaces that you can use to develop your own collection classes. Your
collection classes will blend seamlessly with the classes in the .NET
Framework.
As you would expect from an object-oriented class library, the .NET
Framework types enable you to accomplish a range of common
programming tasks, including tasks such as string management, data
collection, database connectivity, and file access. In addition to these
common tasks, the class library includes types that support a variety of
specialized development scenarios. For example, you can use the .NET
Framework to develop the following types of applications and services:
Console applications.
- 39 -
PROJECT REPORT
GreenWich
Scripted or hosted applications.
Windows GUI applications (Windows Forms).
ASP.NET applications.
XML Web services.
Windows services.
For example, the Windows Forms classes are a comprehensive set of
reusable types that vastly simplify Windows GUI development. If you
write an ASP.NET Web Form application, you can use the Web Forms
classes.
Client Application Development
Client applications are the closest to a traditional style of application in
Windows-based programming. These are the types of applications that
display windows or forms on the desktop, enabling a user to perform a
task. Client applications include applications such as word processors
and spreadsheets, as well as custom business applications such as
data-entry tools, reporting tools, and so on. Client applications usually
employ windows, menus, buttons, and other GUI elements, and they
- 40 -
PROJECT REPORT
GreenWich
likely access local resources such as the file system and peripherals
such as printers.
Another kind of client application is the traditional ActiveX control (now
replaced by the managed Windows Forms control) deployed over the
Internet as a Web page. This application is much like other client
applications: it is executed natively, has access to local resources, and
includes graphical elements.
In the past, developers created such applications using C/C++ in
conjunction with the Microsoft Foundation Classes (MFC) or with a
rapid application development (RAD) environment such as Microsoft
Visual Basic. The .NET Framework incorporates aspects of these
existing products into a single, consistent development environment
that drastically simplifies the development of client applications.
- 41 -
PROJECT REPORT
GreenWich
The Windows Forms classes contained in the .NET Framework are
designed to be used for GUI development. You can easily create
command windows, buttons, menus, toolbars, and other screen
elements with the flexibility necessary to accommodate shifting
business needs.
For example, the .NET Framework provides simple properties to adjust
visual attributes associated with forms. In some cases the underlying
operating system does not support changing these attributes directly,
and in these cases the .NET Framework automatically recreates the
forms. This is one of many ways in which the .NET Framework
integrates the developer interface, making coding simpler and more
consistent.
Unlike ActiveX controls, Windows Forms controls have semi-trusted
access to a user's computer. This means that binary or natively
executing code can access some of the resources on the user's system
(such as GUI elements and limited file access) without being able to
access or compromise other resources. Because of code access security,
- 42 -
PROJECT REPORT
GreenWich
many applications that once needed to be installed on a user's system
can now be safely deployed through the Web. Your applications can
implement the features of a local application while being deployed like a
Web page.
Client Application Development
Client applications are the closest to a traditional style of application in
Windows-based programming. These are the types of applications that
display windows or forms on the desktop, enabling a user to perform a
task. Client applications include applications such as word processors
and spreadsheets, as well as custom business applications such as
data-entry tools, reporting tools, and so on. Client applications usually
employ windows, menus, buttons, and other GUI elements, and they
likely access local resources such as the file system and peripherals
such as printers.
Another kind of client application is the traditional ActiveX control (now
replaced by the managed Windows Forms control) deployed over the
Internet as a Web page. This application is much like other client
applications: it is executed natively, has access to local resources, and
includes graphical elements.
- 43 -
PROJECT REPORT
GreenWich
In the past, developers created such applications using C/C++ in
conjunction with the Microsoft Foundation Classes (MFC) or with a
rapid application development (RAD) environment such as Microsoft
Visual Basic. The .NET Framework incorporates aspects of these
existing products into a single, consistent development environment
that drastically simplifies the development of client applications.
The Windows Forms classes contained in the .NET Framework are
designed to be used for GUI development. You can easily create
command windows, buttons, menus, toolbars, and other screen
elements with the flexibility necessary to accommodate shifting
business needs.
For example, the .NET Framework provides simple properties to adjust
visual attributes associated with forms. In some cases the underlying
operating system does not support changing these attributes directly,
and in these cases the .NET Framework automatically recreates the
forms. This is one of many ways in which the .NET Framework
integrates the developer interface, making coding simpler and more
consistent.
Unlike ActiveX controls, Windows Forms controls have semi-trusted
access to a user's computer. This means that binary or natively
executing code can access some of the resources on the user's system
- 44 -
PROJECT REPORT
GreenWich
(such as GUI elements and limited file access) without being able to
access or compromise other resources. Because of code access security,
many applications that once needed to be installed on a user's system
can now be safely deployed through the Web. Your applications can
implement the features of a local application while being deployed like a
Web page.
Server Application Development
Server-side applications in the managed world are implemented through
runtime hosts. Unmanaged applications host the common language
runtime, which allows your custom managed code to control the
behavior of the server. This model provides you with all the features of
the common language runtime and class library while gaining the
performance and scalability of the host server.
The following illustration shows a basic network schema with managed
code running in different server environments. Servers such as IIS and
SQL Server can perform standard operations while your application
logic executes through the managed code.
Server-side managed code
ASP.NET is the hosting environment that enables developers to use
the .NET Framework to target Web-based applications. However,
- 45 -
PROJECT REPORT
GreenWich
ASP.NET is more than just a runtime host; it is a complete architecture
for developing Web sites and Internet-distributed objects using managed
code. Both Web Forms and XML Web services use IIS and ASP.NET as
the publishing mechanism for applications, and both have a collection
of supporting classes in the .NET Framework.
XML Web services, an important evolution in Web-based technology, are
distributed, server-side application components similar to common Web
sites. However, unlike Web-based applications, XML Web services
components have no UI and are not targeted for browsers such as
Internet Explorer and Netscape Navigator. Instead, XML Web services
consist of reusable software components designed to be consumed by
other applications, such as traditional client applications, Web-based
applications, or even other XML Web services. As a result, XML Web
services technology is rapidly moving application development and
deployment into the highly distributed environment of the Internet.
If you have used earlier versions of ASP technology, you will immediately
notice the improvements that ASP.NET and Web Forms offers. For
example, you can develop Web Forms pages in any language that
supports the .NET Framework. In addition, your code no longer needs
to share the same file with your HTTP text (although it can continue to
do so if you prefer). Web Forms pages execute in native machine
language because, like any other managed application, they take full
- 46 -
PROJECT REPORT
GreenWich
advantage of the runtime. In contrast, unmanaged ASP pages are
always scripted and interpreted. ASP.NET pages are faster, more
functional, and easier to develop than unmanaged ASP pages because
they interact with the runtime like any managed application.
The .NET Framework also provides a collection of classes and tools to
aid in development and consumption of XML Web services applications.
XML Web services are built on standards such as SOAP (a remote
procedure-call protocol), XML (an extensible data format), and WSDL
( the Web Services Description Language). The .NET Framework is built
on these standards to promote interoperability with non-Microsoft
solutions.
For example, the Web Services Description Language tool included with
the .NET Framework SDK can query an XML Web service published on
the Web, parse its WSDL description, and produce C# or Visual Basic
source code that your application can use to become a client of the XML
Web service. The source code can create classes derived from classes in
the class library that handle all the underlying communication using
SOAP and XML parsing. Although you can use the class library to
consume XML Web services directly, the Web Services Description
Language tool and the other tools contained in the SDK facilitate your
development efforts with the .NET Framework.
- 47 -
PROJECT REPORT
GreenWich
If you develop and publish your own XML Web service, the .NET
Framework provides a set of classes that conform to all the underlying
communication standards, such as SOAP, WSDL, and XML. Using those
classes enables you to focus on the logic of your service, without
concerning yourself with the communications infrastructure required
by distributed software development.
Finally, like Web Forms pages in the managed environment, your XML
Web service will run with the speed of native machine language using
the scalable communication of IIS.
SCREENS
- 48 -
PROJECT REPORT
GreenWich
- 49 -
PROJECT REPORT
GreenWich
- 50 -
PROJECT REPORT
GreenWich
- 51 -
PROJECT REPORT
GreenWich
- 52 -
PROJECT REPORT
GreenWich
- 53 -
PROJECT REPORT
GreenWich
- 54 -
PROJECT REPORT
GreenWich
- 55 -
PROJECT REPORT
GreenWich
- 56 -
PROJECT REPORT
GreenWich
- 57 -
PROJECT REPORT
GreenWich
- 58 -
PROJECT REPORT
GreenWich
- 59 -
PROJECT REPORT
GreenWich
- 60 -
PROJECT REPORT
GreenWich
- 61 -
PROJECT REPORT
GreenWich
- 62 -
PROJECT REPORT
GreenWich
PROJECT TESTING
1) COMPILATION TEST:
It was a good idea to do our stress testing early on, because it gave
us time to fix some of the unexpected deadlocks and stability
- 63 -
PROJECT REPORT
GreenWich
problems that only occurred when components were exposed to
very high transaction volumes.
2) EXECUTION TEST:
This program was successfully loaded and executed. Because of
good programming there were no execution error.
3) OUTPUT TEST:
The successful output screens are placed in the output screens
section.
- 64 -
PROJECT REPORT
GreenWich
CONCLUSION
The project has been appreciated by all the users in the
organization.
It is easy to use, since it uses the GUI provided in the user dialog.
User friendly screens are provided.
The usage of software increases the efficiency, decreases the effort.
It has been efficiently employed as a tool for SQL Enterprise
Manager.
It also provides the user with variable options in administering.
It has been thoroughly tested and implemented.
BIBLIOGRAPHY
- 65 -
PROJECT REPORT
GreenWich
SOFTWARE ENGINEERING
By Mr.HariNath
Professional ASP.NET 1.1
By Wrox
MSDN 2002
By Microsoft
- 66 -
You might also like
- Ideal DocumentationDocument97 pagesIdeal Documentation927 Vignesh MoopanarNo ratings yet
- VIGNESHDocument32 pagesVIGNESHDharshanNo ratings yet
- VanshDocument26 pagesVanshtheycallmevanshNo ratings yet
- Human Resource Management Systems HRMSDocument81 pagesHuman Resource Management Systems HRMSgovindarajn67% (3)
- Mobile Store Management SystemDocument34 pagesMobile Store Management SystemVickram JainNo ratings yet
- Cost Estimation in Agile Software Development: Utilizing Functional Size Measurement MethodsFrom EverandCost Estimation in Agile Software Development: Utilizing Functional Size Measurement MethodsNo ratings yet
- Assignment of Project Management On Cloud Computing UploadDocument7 pagesAssignment of Project Management On Cloud Computing Uploadshalu raniNo ratings yet
- Hospital Management System PDFDocument26 pagesHospital Management System PDFPriyanshu BhardwajNo ratings yet
- IP Investigatory Project on Grocery Shop Management SystemDocument30 pagesIP Investigatory Project on Grocery Shop Management SystemPrem GuptaNo ratings yet
- Online Delivery System ThesisDocument6 pagesOnline Delivery System Thesisfc2thaq4100% (2)
- Introduction GroceryDocument5 pagesIntroduction Grocery11F10 RUCHITA MAARANNo ratings yet
- Project 36Document33 pagesProject 36mukesh lannaNo ratings yet
- Hospital Management System Project DocumentationDocument23 pagesHospital Management System Project DocumentationpertinenteNo ratings yet
- MIS Planning and Implementation GuideDocument9 pagesMIS Planning and Implementation GuideRedwan FerdousNo ratings yet
- Bank ManagementsystemDocument52 pagesBank ManagementsystemanshumanNo ratings yet
- Aamir CS 3Document31 pagesAamir CS 3aswanthbalaa612No ratings yet
- Online Advertising SystemDocument42 pagesOnline Advertising Systemfaizan khan67% (3)
- Sales Management SystemDocument28 pagesSales Management SystemramyaNo ratings yet
- Term Paper OF Object Oriented Programming: Railway Reservation SystemDocument45 pagesTerm Paper OF Object Oriented Programming: Railway Reservation SystemAjeet RajpootNo ratings yet
- Cosmetic Shop Management SystemDocument27 pagesCosmetic Shop Management Systemcloakedknight456No ratings yet
- Hospital Management System - 013913Document23 pagesHospital Management System - 013913Aayush RaikwarNo ratings yet
- Agile Customer Engagement A Longitudinal Qualitative Case StudyDocument10 pagesAgile Customer Engagement A Longitudinal Qualitative Case StudyOdnooMgmrNo ratings yet
- Hospital Management System Project ReportDocument33 pagesHospital Management System Project ReportAnanya D RNo ratings yet
- Activity 2Document3 pagesActivity 2Jay Rome AborotNo ratings yet
- New SoftwareDocument9 pagesNew Softwarenashondan22No ratings yet
- Railway Reservation SystemDocument38 pagesRailway Reservation SystemI'M POPZSHA GAMERNo ratings yet
- Project Report On Railway Reservation System by Amit MittalDocument54 pagesProject Report On Railway Reservation System by Amit MittalRajan SinghNo ratings yet
- A New RAD-based Approach To Commercial Information Systems Development: The Dynamic System Development MethodDocument5 pagesA New RAD-based Approach To Commercial Information Systems Development: The Dynamic System Development Methodwriting dweebNo ratings yet
- CS ProjectDocument33 pagesCS Project37 Sunny Kumar MehtaNo ratings yet
- Hotel Management System: All India Senior School Certificate Examination Term 1 2021-22Document25 pagesHotel Management System: All India Senior School Certificate Examination Term 1 2021-22mitshu shreya100% (1)
- Electronic Shop Management SystemDocument28 pagesElectronic Shop Management Systemcloakedknight456No ratings yet
- ACKNOWLEDGEMENTDocument21 pagesACKNOWLEDGEMENTkartiksingh46648No ratings yet
- Hotel ManagementDocument44 pagesHotel ManagementKinjal Keya86% (22)
- SuiiiDocument26 pagesSuiiiDhruv JainNo ratings yet
- Group Ii - June 2021Document69 pagesGroup Ii - June 2021ANISH KAFLENo ratings yet
- Cloth Store Management SystemDocument27 pagesCloth Store Management SystemAshwinNo ratings yet
- BEA Enterprise AppsDocument76 pagesBEA Enterprise AppsPukhrajNo ratings yet
- Vegan Spoon (Project File)Document142 pagesVegan Spoon (Project File)jatin khandelwalNo ratings yet
- 6178!swiggyDocument23 pages6178!swiggyAnkit RajNo ratings yet
- Project 21Document19 pagesProject 21mukesh lannaNo ratings yet
- Comprehensive Case Study In TOGAF® 10: Case Studies in Software Architecture & Design, #1From EverandComprehensive Case Study In TOGAF® 10: Case Studies in Software Architecture & Design, #1No ratings yet
- Sales Management SystemDocument29 pagesSales Management SystemAshwinNo ratings yet
- Computer Institute Management System ProjectDocument31 pagesComputer Institute Management System ProjectBhavy SharmaNo ratings yet
- Railway Reservation System SDLCDocument45 pagesRailway Reservation System SDLCChetan RajuNo ratings yet
- Atm MachineDocument36 pagesAtm MachineAjitesh AwasthiNo ratings yet
- Chapter 4 System Analysis and Design (SAD) NoteDocument6 pagesChapter 4 System Analysis and Design (SAD) NoteAden Kheire MohamedNo ratings yet
- Hospital Management Class Xii Kashis and RiyaDocument33 pagesHospital Management Class Xii Kashis and RiyaAjitesh AwasthiNo ratings yet
- Computer Sales and Service SystemDocument37 pagesComputer Sales and Service Systemguruprasaaths.22cseNo ratings yet
- Hospital Management SystemDocument19 pagesHospital Management SystemDineshNo ratings yet
- Hospital Management Class Xii Kashis and RiyaDocument33 pagesHospital Management Class Xii Kashis and RiyaAjitesh AwasthiNo ratings yet
- Project 23Document21 pagesProject 23mukesh lannaNo ratings yet
- Data Warehouse Development Management: Facta UniversitatisDocument8 pagesData Warehouse Development Management: Facta UniversitatisSUNGNo ratings yet
- Computer Science (Project File)Document38 pagesComputer Science (Project File)sanchitNo ratings yet
- Process (Pius Pinto S) :: Among The Demonstrated Outcomes AreDocument5 pagesProcess (Pius Pinto S) :: Among The Demonstrated Outcomes Arepius pintoNo ratings yet
- Marketing System and Sales SystemDocument22 pagesMarketing System and Sales SystemVictor DawsonNo ratings yet
- Rigi File 06vmrwnijtschool Management-1Document30 pagesRigi File 06vmrwnijtschool Management-1Amir Mohammad FayyazNo ratings yet
- Chapter 4 - Requirement Modeling (CS31)Document45 pagesChapter 4 - Requirement Modeling (CS31)Vienna Corrine Q. AbucejoNo ratings yet
- D-G4-L4-050 Target Operating Model DesignDocument15 pagesD-G4-L4-050 Target Operating Model DesignDJ100% (1)
- Project On Marriage BeuroDocument32 pagesProject On Marriage BeuroROHITH KANCHERLANo ratings yet
- Table of ContentsDocument15 pagesTable of ContentsJyoti SavitaNo ratings yet
- Installing and Configuring Oracle GRC Using WeblogicDocument34 pagesInstalling and Configuring Oracle GRC Using Weblogicmohammed akbar aliNo ratings yet
- IJAER Body Mass Index Device PDFDocument7 pagesIJAER Body Mass Index Device PDFA HlaingNo ratings yet
- Practica de Base de DatosDocument73 pagesPractica de Base de DatosMarco Antonio AraujoNo ratings yet
- Delimited Report Output Using Report BuilderDocument20 pagesDelimited Report Output Using Report BuilderPritesh Mogane0% (1)
- Android Advisor Latest Smartphone PDFDocument140 pagesAndroid Advisor Latest Smartphone PDFAlfa Fredrick Yosep LieputraNo ratings yet
- Computer-Aided Analysis of Mechanisms Using ChExcelDocument53 pagesComputer-Aided Analysis of Mechanisms Using ChExcelAhmet FidanNo ratings yet
- Riscv Presentation PDFDocument71 pagesRiscv Presentation PDFkotresh tNo ratings yet
- GLI 21 v2 2 Standard FinalDocument26 pagesGLI 21 v2 2 Standard FinalHector VillarrealNo ratings yet
- CS333 Midterm Exam from Alexandria UniversityDocument4 pagesCS333 Midterm Exam from Alexandria UniversityRofaelEmil100% (2)
- Maximum connections in Squid proxy serverDocument6 pagesMaximum connections in Squid proxy serverJavierNo ratings yet
- Red Dart Arrow Hitting PowerPoint TemplatesDocument48 pagesRed Dart Arrow Hitting PowerPoint TemplatesmasterNo ratings yet
- Lab Report EC201 INTRODUCTION OF PROGRAMMINGDocument10 pagesLab Report EC201 INTRODUCTION OF PROGRAMMINGFakrul Fajeri100% (1)
- Unit 4 Git Branching and MergingDocument21 pagesUnit 4 Git Branching and MergingKalyani Asha RajeshNo ratings yet
- Install and customize OrangeHRMDocument12 pagesInstall and customize OrangeHRMAbhra Basak100% (1)
- Red Hat Advanced Cluster Security For KubernetesDocument3 pagesRed Hat Advanced Cluster Security For KubernetesSivakumar BakthavachalamNo ratings yet
- SAP R/3 Fundamentals: Unit 1: Introducing The R/3 SystemDocument8 pagesSAP R/3 Fundamentals: Unit 1: Introducing The R/3 SystembogasrinuNo ratings yet
- EVE Comm BOOK 5.0 2022Document150 pagesEVE Comm BOOK 5.0 2022teamleaderNo ratings yet
- ZHR Trigger HR ActionsDocument22 pagesZHR Trigger HR Actionsswadhin14No ratings yet
- Cloud Computing Reference McqsDocument49 pagesCloud Computing Reference Mcqsrajeshkotha214No ratings yet
- SQL Server Installation Checklist2Document3 pagesSQL Server Installation Checklist2praveenmpkNo ratings yet
- Pwmaneng PactwareDocument86 pagesPwmaneng PactwareRafael Martin Anaya FigueroaNo ratings yet
- MCA Seeking Computer Skills PositionDocument2 pagesMCA Seeking Computer Skills Positionbamar_frndNo ratings yet
- SAP HANA Database SQL Command Network Protocol enDocument53 pagesSAP HANA Database SQL Command Network Protocol ennotmelbrooksNo ratings yet
- Configure LDAP Authentication in GLPIDocument7 pagesConfigure LDAP Authentication in GLPIAriel Morodo100% (1)
- Bacula Backup TutorialDocument40 pagesBacula Backup TutorialVenkatesh VenkatNo ratings yet
- Jabra Panacast DatasheetDocument2 pagesJabra Panacast Datasheetikponmwosa olotuNo ratings yet
- Oracle Payroll 'Subledger Accounting (SLA) ' Frequently Asked Questions (FAQ) (Doc ID 605635.1)Document4 pagesOracle Payroll 'Subledger Accounting (SLA) ' Frequently Asked Questions (FAQ) (Doc ID 605635.1)Hadi AamirNo ratings yet
- DPKGDocument16 pagesDPKGeldanidanNo ratings yet
- 2012 Word CalendarDocument12 pages2012 Word CalendarCandice Michelle GoldsmithNo ratings yet
- BPA DBMS Chapter1 - DBMS OverviewDocument45 pagesBPA DBMS Chapter1 - DBMS OverviewCD PANo ratings yet