Professional Documents
Culture Documents
Aca Complete
Uploaded by
sharmaarakeyshCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Aca Complete
Uploaded by
sharmaarakeyshCopyright:
Available Formats
Ideal Institute of Technology
Department of Computer Science &
Engineering
IDEAL INSTITUTE
Of Technology, Ghaziabad
(AN ISO 9001 2000 CERTIFIED INSTITUTE)
LAB MANUAL
ADVANCED COMPUTER ARCHITECTURE
(TCS-851)
DEPARTMENT OF COMPUTER
SCIENCE & ENGINEERING
Advanced Computer Architecture Lab (TCS-851)
Page | 1
Ideal Institute of Technology
Department of Computer Science &
Engineering
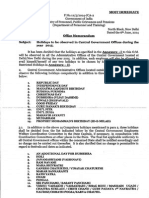
IDEAL INSTITUTE OF TECHNOLOGY, GHAZIABAD
DEPARTMENT OF COMPUTER SCIENCE & ENGINEERING
CN Lab (ECS-651)
INDEX
S. No.
Documents
Page No.
01
Dos & Donts
02
Syllabus
03
List of Programs
04
H/W & S/W Requirements
05
Program No -01
06
Program No. -02
13
07
Program No. -03
16
08
Program No. -04
09
Program No. -05
10
Program No. -06
11
Program No. -07
12
Program No. -08
13
Program No. -09
14
Program No. -10
Advanced Computer Architecture Lab (TCS-851)
19
23
27
30
32
35
37
Page | 2
Ideal Institute of Technology
Department of Computer Science &
Engineering
Lab In-charge
HOD (CS)
GENERAL INSTRUCTIONS
DOs:
1. Switch off mobiles in the lab.
2. Bring your lab record with you.
3. Always come to the lab on time.
4. Maintain silence and be attentive.
5. Keep individual records of observations.
6. Always turn off the computer before leaving the lab.
7. Return all the materials issued to you before leaving
the lab.
8. Read the instruction manual carefully before
performing any experiment.
DONTs:
1. Change current setting.
2. Overcrowed near any equipment.
3. Make any mark on instruction manual.
4. Drag the stool and chair inside the lab.
5. Leave the lab till the class has concluded.
6. Take any material outside the lab with you.
Advanced Computer Architecture Lab (TCS-851)
Page | 3
Ideal Institute of Technology
Department of Computer Science &
Engineering
7.
Touch any machine / equipment/ model without
supervision.
SYLLABUS
ADVANCED COMPUTER ARCHITECTURE LAB
(TCS-851)
The following programs should be developed in C language
preferably on UNIX platform.
Programs (3-7) require usage of Parallel Computing APIs:
1. Write a program to execute three POSIX Threads (PThreads)
simultaneously for updating a text file.
2. Write a program for synchronizing POSIX Threads
(PThreads) using (a) Semaphore (b)Mutex
3. Implement the PRAM Algorithm for (a) Parallel Reduction
(b) Prefix Sums (c) Preorder Tree Traversal
4. Implement Parallel Matrix Multiplication using (a) RowColumn oriented Algorithm (b)Block-Oriented Algorithm
5. Implement Solution of Linear Systems using (a) Gaussian
Elimination (b) Jacobi Algorithm
6. Implement (a) Parallel Quick Sort (b) Hyper Quicksort
7. Implement Parallel Fast Fourier Transform Algorithm.
Advanced Computer Architecture Lab (TCS-851)
Page | 4
Ideal Institute of Technology
Department of Computer Science &
Engineering
IDEAL INSTITUTE OF TECHNOLOGY, GHAZIABAD
DEPARTMENT OF COMPUTER SCIENCE & ENGINEERING
Advanced Computer Architecture Lab (TCS-851)
LIST OF PROGRAM
S. No.
Program
No.
NAME OF THE EXPERIMENT
1.
Prog.-1
Basics of UNIX in terms of commands.
2.
Prog.-2
Write a program to implement execution of pthreads.
3.
Prog.-3
Write a Program for synchronizing POSIX thread using
Semaphores.
4.
Prog.-4
Write a Program for synchronizing POSIX thread using Mutex
variable.
5.
Prog.-5
Write a program to find solution of linear system using Gaussian
Elimination.
6.
Prog.-6
7.
Prog.-7
Write a program to find solution of linear system using Jacobi
method.
Write a program to implement parallel quick sort.
8.
Prog.-8
Write a program to implement Fast Fourier transformation
algorithm.
Beyond Syllabus
9.
Prog.-9
10.
Prog.-10
Write a program to implement Newton forward difference
method.
Write a program to implement Lagrange method.
Advanced Computer Architecture Lab (TCS-851)
Page | 5
Ideal Institute of Technology
Department of Computer Science &
Engineering
Lab In-Charge
HOD (CS)
IDEAL INSTITUTE OF TECHNPLOGY, GHAZIABAD
DEPARTMENT OF COMPUTER SCIENCE & ENGINEERING
Advanced Computer Architecture Lab (TCS-851)
Hardware and Software requirements
Hardware
Pentium P4 1.5 G Hz CPU
256 MB RAM
14 Monitor
Keyboard
Mouse
CD Drive
Software
Linux
Advanced Computer Architecture Lab (TCS-851)
Page | 6
Ideal Institute of Technology
Department of Computer Science &
Engineering
ADVANCED COMPUTER ARCHITECTURE
(TCS-851)
PROGRAM NO: 01
DEPARTMENT OF COMPUTER
SCIENCE & ENGINEERING
Advanced Computer Architecture Lab (TCS-851)
Page | 7
IDEAL INSTITUTE OF TECHNOLOGY, GHAZIABAD
Ideal Institute of Technology
Department of Computer Science &
Engineering
Program No: 1
TITLE- Basics of UNIX command
1.1 Objective 1.2 Theory
1.1 OBJECTIVE: Basics of Unix in terms of commands.
1.2 THEORY:
1.
cat
This is one of the most flexible Unix commands. We can use to create, view and
concatenate files. For our first example we create a three-item English-Spanish dictionary
in a file called "dict."
% cat >dict
red rojo
green verde
blue azul
<control-D>
%
<control-D> stands for "hold the control key down, then tap 'd'". The symbol > tells the
computer that what is typed is to be put into the file dict. To view a file we use cat in a
different way:
2.
chmod
This command is used to change the permissions of a file or directory. For example to
make a file essay.001 readable by everyone, we do this:
% chmod a+r essay.001
To make a file, e.g., a shell script mycommand executable, we do this
Advanced Computer Architecture Lab (TCS-851)
Page | 8
Ideal Institute of Technology
Department of Computer Science &
Engineering
% chmod +x mycommand
Now we can run mycommand as a command.
To check the permissions of a file, use ls -l . For more information on chmod, use man
chmod.
3.
cd
Use cd to change directory. Use pwd to see what directory you are in.
% cd english
% pwd
% /u/ma/jeremy/english
% ls
novel poems
% cd novel
% pwd
% /u/ma/jeremy/english/novel
% ls
ch1 ch2 ch3 journal scrapbook
4.
cp
Use cp to copy files or directories.
% cp foo foo.2
This makes a copy of the file foo.
% cp ~/poems/jabber .
This copies the file jabber in the directory poems to the current directory. The symbol "."
stands for the current directory. The symbol "~" stands for the home directory.
5.
date
Use this command to check the date and time.
% date
Fri Jan 6 08:52:42 MST 1995
6.
grep
Use this command to search for information in a file or files. For example, suppose that
we have a file dict whose contents are
red rojo
green verde
blue azul
white blanco
black negro
Then we can look up items in our file like this;
Advanced Computer Architecture Lab (TCS-851)
Page | 9
Ideal Institute of Technology
Department of Computer Science &
Engineering
% grep red dict
red rojo
% grep blanco dict
white blanco
% grep brown dict
%
7.
head
Use this command to look at the head of a file. For example,
% head essay.001
displays the first 10 lines of the file essay.001 To see a specific number of lines, do this:
% head -20 essay.001
This displays the first 20 lines of the file.
ls
Use ls to see what files you have. Your files are kept in something called a directory.
% ls
foo
foobar
letter1
%
letter2
letter3
maple-assignment1
Note that you have six files. There are some useful variants of the ls command:
% ls l*
letter1 letter2 letter3
%
Note what happened: all the files whose name begins with "l" are listed. The asterisk (*)
is the " wildcard" character. It matches any string.
8.
lpr
This is the standard Unix command for printing a file. It stands for the ancient "line
printer." See
% man lpr
Advanced Computer Architecture Lab (TCS-851)
Page | 10
Ideal Institute of Technology
Department of Computer Science &
Engineering
9.
more
More is a command used to read text files. For example, we could do this:
% more poems
The effect of this to let you read the file "poems ". It probably will not fit in one screen,
so you need to know how to "turn pages". Here are the basic commands:
q --- quit more
spacebar --- read next page
return key --- read next line
b --- go back one page
For still more information, use the command man more.
10.
mv
Use this command to change the name of file and directories.
% mv foo foobar
The file that was named foo is now named foobar
11.
pwd
Use this command to find out what directory you are working in.
% pwd
/u/ma/jeremy
% cd homework
% pwd
/u/ma/jeremy/homework
% ls
assign-1 assign-2 assign-3
% cd
% pwd
/u/ma/jeremy
%
12.
rsh
Use this command if you want to work on a computer different from the one you are
currently working on. One reason to do this is that the remote machine might be faster.
For example, the command
% rsh solitude
Advanced Computer Architecture Lab (TCS-851)
Page | 11
Ideal Institute of Technology
Department of Computer Science &
Engineering
connects you to the machine solitude. This is one of our public workstations and is
fairly fast.
13.
tail
Use this command to look at the tail of a file. For example,
% head essay.001
displays the last 10 lines of the file essay.001 To see a specific number of lines, do this:
% head -20 essay.001
This displays the last 20 lines of the file.
14.
tar
Use create compressed archives of directories and files, and also to extract directories and
files from an archive. Example:
% tar -tvzf foo.tar.gz
displays the file names in the compressed archive foo.tar.gz while
% tar -xvzf foo.tar.gz
extracts the files.
15.
wc
Use this command to count the number of characters, words, and lines in a file. Suppose,
for example, that we have a file dict with contents
red rojo
green verde
blue azul
white blanco
black negro
Then we can do this
% wc dict
5
10
56 tmp
Advanced Computer Architecture Lab (TCS-851)
Page | 12
Ideal Institute of Technology
Department of Computer Science &
Engineering
ADVANCED COMPUTER ARCHITECTURE
(TCS-851)
PROGRAM NO: 02
DEPARTMENT OF COMPUTER
SCIENCE & ENGINEERINGPage | 13
Advanced Computer Architecture Lab (TCS-851)
IDEAL INSTITUTE OF TECHNOLOGY, GHAZIABAD
Ideal Institute of Technology
Department of Computer Science &
Engineering
Program No: 2
TITLE Execution of Pthreads
1.1 Objective 1.2 Theory 1.3 Flow chart /Algorithm 1.4. Coding .1.5 Output 1.6
Questions
1.1 OBJECTIVE: Write a program to implement execution of pthreads.
1.2 THEORY:
Pthreads:
The Pthreads library is a POSIX C API thread library that has standardized functions for
using threads across different platforms. Historically, hardware vendors have
implemented their own proprietary versions of threads. These implementations differed
substantially from each other making it difficult for programmers to develop portable
threaded applications. In order to take full advantage of the capabilities provided by
threads, a standardized programming interface was required. For UNIX systems, this
interface has been specified by the IEEE POSIX 1003.1c standard (1995).
Implementations that adhere to this standard are referred to as POSIX threads, or
Pthreads. Most hardware vendors now offer Pthreads in addition to their proprietary
API's. Pthreads are defined as a set of C language programming types and procedure
calls. Vendors usually provide a Pthreads implementation in the form of a header/include
file and a library that you link with your program.
Basic Pthreads Library Calls
Advanced Computer Architecture Lab (TCS-851)
Page | 14
Ideal Institute of Technology
Department of Computer Science &
Engineering
Brief Introduction to Pthreads calls
int pthread_create(pthread_t *thread, const pthread_attr_t *attr,
void*(*start_routine) (void), void *arg) ;
Creates a new thread, initializes its attributes, and makes it run able.
The pthread_create subroutine creates a new thread and initializes its attributes using the
thread attributes object specified by the attr parameter. The new thread inherits its
creating thread's signal mask; but any pending signal of the creating thread will be
cleared for the new thread.
The new thread is made runnable, and will start executing the start_routine routine, with
the parameter specified by the arg parameter. The arg parameter is a void pointer; it can
reference any kind of data. It is not recommended to cast this pointer into a scalar data
type (int for example), because the casts may not be portable.
The pthread_create subroutine returns the new thread identifier via the thread argument.
The caller can use this thread identifier to perform various operations on the thread. This
identifier should be checked to ensure that the thread was successfully created.
void pthread_exit(void *value_ptr);
Terminates the calling thread.
The pthread_exit subroutine terminates the calling thread safely, and stores a termination
status for any thread that may join the calling thread. The termination status is always a
void pointer; it can reference any kind of data. It is not recommended to cast this pointer
into a scalar data type (int for example), because the casts may not be portable. This
subroutine never returns.
Unlike the exit subroutine, the pthread_exit subroutine does not close files. Thus any file
opened and used only by the calling thread must be closed before calling this subroutine.
It is also important to note that the pthread_exit subroutine frees any thread-specific data,
including the thread's stack. Any data allocated on the stack becomes invalid identifier,
since the stack is freed and the corresponding memory may be reused by another thread.
Therefore, thread synchronization objects (mutexes and condition variables) allocated on
a threads stack must be destroyed before the thread calls the pthread_exit subroutine.
Returning from the initial routine of a thread implicitly calls the pthread_exit subroutine,
using the return value as parameter.
Advanced Computer Architecture Lab (TCS-851)
Page | 15
Ideal Institute of Technology
Department of Computer Science &
Engineering
1.3 LOGIC : This program represents the execution of pthreads executing
simultaneously. The program also represents the process of terminating the thread
normally and abnormally.
The header file pthread.h include definition of all the functions such as to create,
execute and terminate the pthread normally and abnormally. The program also show
the method to pass argument in a pthread. The pthread in this program is represented
by an identifier worker.
ADVANCED COMPUTER ARCHITECTURE
(TCS-851)
Questions:
Q1:
What are pthreads?
Q2:
How pthreads are different from threads?
Q3:
Name the function by which pthread can be terminated abnormally?
PROGRAM NO: 03
DEPARTMENT OF COMPUTER
SCIENCE & ENGINEERINGPage | 16
Advanced Computer Architecture Lab (TCS-851)
IDEAL INSTITUTE OF TECHNOLOGY, GHAZIABAD
Ideal Institute of Technology
Department of Computer Science &
Engineering
Program No: 3
TITLE Synchronization of POSIX thread using Semaphores.
1.1 Objective 1.2 Theory 1.3 Logic 1.4. Coding .1.5 Output 1.6 Questions
1.1 OBJECTIVE: Write a Program for synchronizing POSIX thread using
Semaphores.
1.2 THEORY:
What is a Thread?
Technically, a thread is defined as an independent stream of instructions that can
be scheduled to run as such by the operating system. But what does this mean?
To the software developer, the concept of a procedure that runs independently
from its main program may best describes a thread.
What are Pthreads?
Historically, hardware vendors have implemented their own proprietary versions
of threads. These implementations differed substantially from each other making
it difficult for programmers to develop portable threaded applications.
In order to take full advantage of the capabilities provided by threads, a
standardized programming interface was required. For UNIX systems, this
interface has been specified by the IEEE POSIX 1003.1c standard (1995).
Implementations which adhere to this standard are referred to as POSIX threads,
Advanced Computer Architecture Lab (TCS-851)
Page | 17
Ideal Institute of Technology
Department of Computer Science &
Engineering
or Pthreads. Most hardware vendors now offer Pthreads in addition to their
proprietary API's.
Pthreads are defined as a set of C language programming types and procedure
calls, implemented with a pthread.h header/include file and a thread library though the this library may be part of another library, such as libc.
Synchronization
Synchronization is a problem in timekeeping which requires the coordination of events
to operate a system in unison. The familiar conductor of an orchestra serves to keep the
orchestra in time. Systems operating with all their parts in synchrony are said to be
synchronous or in sync. Some systems may be only approximately synchronized, or
plesiochronous. For some applications relative offsets between events need to be
determined, for others only the order of the event is important.
Synchronization using condition variables
Condition variables provide yet another way for threads to synchronize. While
mutexes implement synchronization by controlling thread access to data,
condition variables allow threads to synchronize based upon the actual value of
data.
Without condition variables, the programmer would need to have threads
continually polling (possibly in a critical section), to check if the condition is met.
This can be very resource consuming since the thread would be continuously busy
in this activity. A condition variable is a way to achieve the same goal without
polling.
A condition variable is always used in conjunction with a mutex lock.
We might use a semaphore to manage access to a pool of indistinct resources. Threads
wanting to use the resources in this pool wait on a given semaphore. The object that
manages the pool then sends out a signal for each available resource in the pool. The
same number of waiting threads would then be able to acquire a resource and do some
work with it. As each thread finished with the resource, it would put it back in the pool, at
which point the manager would send out another signal.
1.3 LOGIC:
This simple example code demonstrates the use of several Pthread condition variable
routines. The main routine creates three threads. Two of the threads perform work and
update a "count" variable. The third thread waits until the count variable reaches a
specified value.
This program locks mutex and wait for signal. Note that the pthread_cond_wait
routine will automatically and atomically unlock mutex while it waits. Also, note that if
COUNT_LIMIT is reached before this routine is run by the waiting thread, the loop will
be skipped to prevent pthread_cond_wait from never returning.
Advanced Computer Architecture Lab (TCS-851)
Page | 18
Ideal Institute of Technology
Department of Computer Science &
Engineering
1.4 QUESTIONS:
Q1:
What are condition variables?
Q2:
What is the significance of condition variables in synchronization?
ADVANCED
COMPUTER
ARCHITECTURE
Why the synchronization
is necessary in pthreads?
(TCS-851)
Q3:
PROGRAM NO: 04
DEPARTMENT OF COMPUTER
SCIENCE & ENGINEERINGPage | 19
Advanced Computer Architecture Lab (TCS-851)
IDEAL INSTITUTE OF TECHNOLOGY, GHAZIABAD
Ideal Institute of Technology
Department of Computer Science &
Engineering
Program No: 4
TITLE Synchronization of POSIX thread using mutex variable.
1.1 Objective 1.2 Theory 1.3 Logic 1.4. Coding .1.5 Output 1.6 Questions
1.1 OBJECTIVE: Write a Program for synchronizing POSIX thread using Mutex
variable.
1.2 THEORY :
What is a Thread?
Technically, a thread is defined as an independent stream of instructions that can
be scheduled to run as such by the operating system. But what does this mean?
To the software developer, the concept of a procedure that runs independently
from its main program may best describes a thread.
What are Pthreads?
Historically, hardware vendors have implemented their own proprietary versions
of threads. These implementations differed substantially from each other making
it difficult for programmers to develop portable threaded applications.
In order to take full advantage of the capabilities provided by threads, a
standardized programming interface was required. For UNIX systems, this
Advanced Computer Architecture Lab (TCS-851)
Page | 20
Ideal Institute of Technology
Department of Computer Science &
Engineering
interface has been specified by the IEEE POSIX 1003.1c standard (1995).
Implementations which adhere to this standard are referred to as POSIX threads,
or Pthreads. Most hardware vendors now offer Pthreads in addition to their
proprietary API's.
Pthreads are defined as a set of C language programming types and procedure
calls, implemented with a pthread.h header/include file and a thread library though the this library may be part of another library, such as libc.
Synchronization
Synchronization is a problem in timekeeping which requires the coordination of events
to operate a system in unison. The familiar conductor of an orchestra serves to keep the
orchestra in time. Systems operating with all their parts in synchrony are said to be
synchronous or in sync. Some systems may be only approximately synchronized, or
plesiochronous. For some applications relative offsets between events need to be
determined, for others only the order of the event is important.
Mutex variable:
A mutex lock is the simplest form of lock, providing mutually exclusive access (hence
the term mutex) to a shared resource. Threads wanting to access a resource protected
by a mutex lock must first acquire the lock. Only one thread at a time may acquire the
lock. Any other threads attempting to acquire the lock are blocked until the owner
relinquishes it.
Mutex is an abbreviation for "mutual exclusion". Mutex variables are one of the primary
means of implementing thread synchronization and for protecting shared data when
multiple writes occur.
A mutex variable acts like a "lock" protecting access to a shared data resource. The basic
concept of a mutex as used in Pthreads is that only one thread can lock (or own) a mutex
variable at any given time. Thus, even if several threads try to lock a mutex only one
thread will be successful. No other thread can own that mutex until the owning thread
unlocks that mutex. Threads must "take turns" accessing protected data.
1.3 LOGIC:
This program illustrates the use of mutex variables in a threads program that performs a
dot product. The main data is made available to all threads through a globally accessible
structure. Each thread works on a different part of the data. The main thread waits for all
the threads to complete their computations, and then it prints the resulting sum.
The function dot prod is activated when the thread is created. All input to this routine is
obtained from a structure of type DOTDATA and all output from this function is written
into
Advanced Computer Architecture Lab (TCS-851)
Page | 21
Ideal Institute of Technology
Department of Computer Science &
Engineering
This structure. The benefit of this approach is apparent for the multi-threaded program:
when a thread is created we pass a single argument to the activated function - typically
this argument
is a thread number. All the other information required by the function is accessed from
the globally accessible structure.
The main program creates threads which do all the work and then print out result upon
completion. Before creating the threads, the input data is created. Since all threads update
a shared structure, we need a mutex for mutual exclusion. The main thread needs to wait
for
all threads to complete, it waits for each one of the threads. We specify a thread attribute
value that allows the main thread to join with the threads it creates. Note also that we free
up handles when they are no longer needed.
1.4 QUESTIONS:
Q1:
What are mutex variables?
Q2:
How the mutex variables are used for synchronization?
Q3:
How the mutex variables and condition variables are different?
Advanced Computer Architecture Lab (TCS-851)
Page | 22
Ideal Institute of Technology
Department of Computer Science &
Engineering
ADVANCED COMPUTER ARCHITECTURE
(TCS-851)
PROGRAM NO: 05
DEPARTMENT OF COMPUTER
SCIENCE & ENGINEERING Page | 23
Advanced Computer Architecture Lab (TCS-851)
IDEAL INSTITUTE OF TECHNOLOGY, GHAZIABAD
Ideal Institute of Technology
Department of Computer Science &
Engineering
Program No: 5
TITLE Linear Systems using Gaussian Elimination
1.1 Objective 1.2 Theory 1.3 Logic 1.4. Coding .1.5 Output 1.6 Questions
1.1 OBJECTIVE: Write a program to find solution of linear system using Gaussian
Elimination.
1.2 THEORY: The equation
ax+by+cz+dw=h
Where a, b, c, d, and h are known numbers, while x, y, z, and w are unknown numbers, is
called a linear equation. If h =0, the linear equation is said to be homogeneous. A linear
system is a set of linear equations and a homogeneous linear system is a set of
homogeneous linear equations.
Matrix Representation of a Linear System
Advanced Computer Architecture Lab (TCS-851)
Page | 24
Ideal Institute of Technology
Department of Computer Science &
Engineering
Matrices are helpful in rewriting a linear system in a very simple form. The algebraic
properties of matrices may then be used to solve systems. First, consider the linear system
Set the matrices
Using matrix multiplications, we can rewrite the linear system above as the matrix
equation
As you can see this is far nicer than the equations. But sometimes it is worth to solve the
system directly without going through the matrix form.
As you can see we obtained the same system as before. In fact, we followed the same
elementary operations performed above. In every step the new matrix was exactly the
augmented matrix associated to the new system. This shows that instead of writing the
systems over and over again, it is easy to play around with the elementary row operations
and once we obtain a triangular matrix, write the associated linear system and then solve
it. This is known as Gaussian Elimination.
Gaussian Elimination. Consider a linear system.
1.
Construct the augmented matrix for the system;
2.
Use elementary row operations to transform the augmented matrix into a
triangular one;
3.
Write down the new linear system for which the triangular matrix is the associated
augmented matrix;
Advanced Computer Architecture Lab (TCS-851)
Page | 25
Ideal Institute of Technology
Department of Computer Science &
Engineering
4.
Solve the new system. You may need to assign some parametric values to some
unknowns, and then apply the method of back substitution to solve the new
system.
1.3 LOGIC:
This is the sequential program to solve a linear system Ax = b by using Gaussian
Elimination
Method using scaled column pivoting. In this program
Inputs
A - Matrix A (N by N)
b - Vector b (N by 1)
Outputs
x - Vector x (N by 1)
The given program performs both the forward substitution as well as backward
substation.
1.4 Questions:
Q1:
What is Gauss elimination method?
Q2:
What is the formula of solving Gauss elimination method?
Advanced Computer Architecture Lab (TCS-851)
Page | 26
Ideal Institute of Technology
Department of Computer Science &
Engineering
ADVANCED COMPUTER ARCHITECTURE
(TCS-851)
PROGRAM NO: 06
DEPARTMENT OF COMPUTER
SCIENCE & ENGINEERINGPage | 27
Advanced Computer Architecture Lab (TCS-851)
IDEAL INSTITUTE OF TECHNOLOGY, GHAZIABAD
Ideal Institute of Technology
Department of Computer Science &
Engineering
Program No: 6
TITLE Linear Systems using Jacobi method.
1.1 Objective 1.2 Theory 1.3 Logic 1.4. Coding .1.5 Output 1.6 Questions
1.1 OBJECTIVE: Write a program to find solution of linear system using Jacobi
method.
1.2 THEORY:
The Jacobi method is a method of solving a matrix equation on a matrix that has no zeros
along its main diagonal. Each diagonal element is solved for, and an approximate value
plugged in. The process is then iterated until it converges. This algorithm is a strippeddown version of the Jacobi transformation method of matrix digitalization.
The Jacobi method is easily derived by examining each of the equations in the linear
system of equations
in isolation. If, in the th equation
Advanced Computer Architecture Lab (TCS-851)
Page | 28
Ideal Institute of Technology
Department of Computer Science &
Engineering
solve for the value of
while assuming the other entries of remain fixed. This gives
which is the Jacobi method.
In this method, the order in which the equations are examined is irrelevant, since the
Jacobi method treats them independently. The definition of the Jacobi method can be
expressed with matrices as
where the matrices ,
, and
represent the diagonal, strictly lower triangular, and
strictly upper triangular parts of , respectively.
1.3 LOGIC:
We will use the rather simple iterative method, called Jacobi iteration, so a brief review
of that algorithm is in order. Given a system of linear equations, Ax=f, where A is a
symmetric positive definite matrix:
1. Choose matrices D, U, and L, so that A=D-(U+L), D is diagonal, and U and L is
upper and lower triangular.
2. Choose a suitable starting value
3. Calculate
4. Until the error is ``small enough'', repeat the previous step
The question of ``small enough'' is, in addition to being somewhat poorly defined,
difficult to measure, since measuring the error requires knowledge of the exact solution.
Instead, we can measure how close the value of Av is to f. The value Av-f is called the
residue.
1.4 Questions:
Q1:
What is Jacobi method?
Q2:
Write the formula of Jacobi method?
Q3:
What is the significance of using Jacobi method?
Advanced Computer Architecture Lab (TCS-851)
Page | 29
Ideal Institute of Technology
Department of Computer Science &
Engineering
ADVANCED COMPUTER ARCHITECTURE
(TCS-851)
PROGRAM NO: 07
DEPARTMENT OF COMPUTER
SCIENCE & ENGINEERING
Advanced Computer Architecture Lab (TCS-851)
Page | 30
IDEAL INSTITUTE OF TECHNOLOGY, GHAZIABAD
Ideal Institute of Technology
Department of Computer Science &
Engineering
Program No: 7
TITLE Implementation of parallel Quick sort
1.1 Objective 1.2 Theory & Logic 1.3. Coding .1.4 Output
1.1 OBJECTIVE: Write a program to implement parallel quick sort.
1.2 THEORY& LOGIC:
Parallel Quick sort is a divide-and-conquer algorithm that sorts a sequence by recursively
dividing it into smaller subsequences. Sorting the smaller arrays represents two
completely independent sub problems that can be solved in parallel. Therefore, one way
to parallelize QuickPort is to execute it initially on a single processor; then when the
algorithm performs its recursive calls, assign one of the sub problems to another
processor. Now each of these processors sorts its array by using quick sort and assigns
one of its sub problems to other processors. The algorithm terminates when the arrays
cannot be further partitioned.
1.3 Questions:
Q1:
What is quick sort?
Q2:
Write the logic of quick sort?
Advanced Computer Architecture Lab (TCS-851)
Page | 31
Ideal Institute of Technology
Department of Computer Science &
Engineering
Q3:
What is the significance of using quick sort?
ADVANCED COMPUTER ARCHITECTURE
(TCS-851)
PROGRAM NO: 08
DEPARTMENT OF COMPUTER
SCIENCE & ENGINEERING
Advanced Computer Architecture Lab (TCS-851)
Page | 32
IDEAL INSTITUTE OF TECHNOLOGY, GHAZIABAD
Ideal Institute of Technology
Department of Computer Science &
Engineering
Program No: 8
TITLE Implementation of Fast Fourier Transformation algorithm
1.1 Objective 1.2 Theory 1.3 Logic 1.4. Coding .1.5 Output1.6 Questions
1.1 OBJECTIVE: Write a program to implement Fast Fourier transformation
algorithm.
1.2 THEORY:
The fast Fourier transform (FFT) is a discrete Fourier transform algorithm which reduces
the number of computations needed for points from
to
, where lg is the
base-2 logarithm. If the function to be transformed is not harmonically related to the
sampling frequency, the response of an FFT looks like a sinc function (although the
integrated power is still correct).
FFTs were first discussed by Cooley and Tukey (1965), although Gauss had actually
described the critical factorization step as early as 1805. A discrete Fourier transform can
be computed using an FFT by means of the Danielson-Lanczos lemma if the number of
points is a power of two. If the number of points is not a power of two, a transform
can be performed on sets of points corresponding to the prime factors of which is
Advanced Computer Architecture Lab (TCS-851)
Page | 33
Ideal Institute of Technology
Department of Computer Science &
Engineering
slightly degraded in speed. Prime factorization is slow when the factors are large, but
discrete Fourier transforms can be made fast for
, 3, 4, 5, 7, 8, 11, 13, and 16 .
Fast Fourier transform algorithms generally fall into two classes:
decimation in time, and
decimation in frequency.
The FFT algorithm first rearranges the input elements in bit-reversed order, then builds
the output transform (decimation in time). The basic idea is to break up a transform of
length into two transforms of length
using the identity
1.3 LOGIC:
An example of the fast Fourier transform subroutine with N = 2**M. AR and AI are the
real and imaginary part of data in the input and corresponding Fourier coefficients in the
output. This program rearrange the data to the bit reversed order .This program computes
an in-place complex -to-complex FFT:
x and y are the real and imaginary arrays of 2^m points.
dir = 1 gives forward transform
dir = -1 gives reverse transform
1.4 Questions:
Q1:
What is fast forward transformation method?
Q2:
Write the formula of the method?
Q3:
What is the significance of using the method?
Advanced Computer Architecture Lab (TCS-851)
Page | 34
Ideal Institute of Technology
Department of Computer Science &
Engineering
ADVANCED COMPUTER ARCHITECTURE
(TCS-851)
PROGRAM NO: 09
DEPARTMENT OF COMPUTER
SCIENCE & ENGINEERING Page | 35
Advanced Computer Architecture Lab (TCS-851)
IDEAL INSTITUTE OF TECHNOLOGY, GHAZIABAD
Ideal Institute of Technology
Department of Computer Science &
Engineering
Program No: 9
TITLE Newton Forward Method
1.1 Objective 1.2 Theory 1.3 Logic 1.4. Coding .1.5 Output 1.6 Questions
1.1 OBJECTIVE: Write a program to implement Newton forward difference method.
1.2 THEORY:
Newton's forward difference formula is a finite difference identity giving an interpolated
value between tabulated points
in terms of the first value and the powers of the
forward difference . For
, the formula states
1.3 LOGIC:
Advanced Computer Architecture Lab (TCS-851)
Page | 36
Ideal Institute of Technology
Department of Computer Science &
Engineering
1.
2.
3.
4.
Take the value of x and y.
Take the value at which compute y.
Compute the value of all entries of table for nth terms by
y[i][j]=y[i+1][j-1]-y[i][j-1]
Compute value of y by
1.4
Questions:
Q1: What is Newtons Forward
method?
ADVANCED
COMPUTER
ARCHITECTURE
Q2: Write the formula used for solving problem by Newtons Forward method.
(TCS-851)
PROGRAM NO: 10
DEPARTMENT OF COMPUTER
SCIENCE & ENGINEERING Page | 37
Advanced Computer Architecture Lab (TCS-851)
IDEAL INSTITUTE OF TECHNOLOGY, GHAZIABAD
Ideal Institute of Technology
Department of Computer Science &
Engineering
Program No: 10
TITLE Lagrange Method
1.1 Objective 1.2 Theory 1.3 Logic 1.4. Coding .1.5 Output 1.6 Questions
1.1 OBJECTIVE: Write a program to implement Lagrange method.
1.2 THEORY:
Lagrange method is used to find the value of x for unequal interval .The formula used in
this method is:
f(x0)= (x- x1) (x- x2). (x- xn)/ (x0- x1) (x0 - x2) (x0 - xn) f(x0)+ (x- x0) (x- x2). (x- xn)/
(x1- x0) (x1 - x2) (x1 - xn) f(x1) +.+(x- x0) (x- x1). (x- xn-1)/ (xn- x0) (xn x1) (xn xn-1) f(xn)
1.3 LOGIC :
1. Input the values of xi , f(xi) and value of x for which f(x) is o be calculated.
Advanced Computer Architecture Lab (TCS-851)
Page | 38
Ideal Institute of Technology
Department of Computer Science &
Engineering
n
2. Calculate the values of
Li ( x )
x xj
x xj
j 0 i
j i
3. Find f(x) by using the Lagranges interpolation formula
1.4 Questions:
Q1:
Q2:
How the Lagranges method is implemented?
What is the formula of Lagranges method?
Advanced Computer Architecture Lab (TCS-851)
Page | 39
You might also like
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (120)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Engineering Guide Flex and Rigid Flex PCBsDocument14 pagesEngineering Guide Flex and Rigid Flex PCBsMariano DiazNo ratings yet
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- Mathematics of Neural Networks. Models, Algorithms and Applications (PDFDrive)Document423 pagesMathematics of Neural Networks. Models, Algorithms and Applications (PDFDrive)Roy RoyzNo ratings yet
- Manual Controls C807Document40 pagesManual Controls C807Felipe Aguilar Rivera100% (1)
- Calculating Angles Between Two 3-Space Sensor Devices On A Human BodyDocument24 pagesCalculating Angles Between Two 3-Space Sensor Devices On A Human BodyshravantataNo ratings yet
- Liquid Film CoatingDocument791 pagesLiquid Film CoatingIsa AguirreNo ratings yet
- Seminar: Industrial ChimneysDocument12 pagesSeminar: Industrial Chimneysmanu_696No ratings yet
- A Worked Example-RsaDocument12 pagesA Worked Example-RsasharmaarakeyshNo ratings yet
- 2nd Yr DataDocument3 pages2nd Yr DatasharmaarakeyshNo ratings yet
- Cryptography Quick GuideDocument54 pagesCryptography Quick GuideIbrahimNo ratings yet
- Computer NetworkDocument81 pagesComputer NetworksharmaarakeyshNo ratings yet
- Cryptography Quick GuideDocument54 pagesCryptography Quick GuideIbrahimNo ratings yet
- Approach To Energy Efficiency Among Micro, Small and Medium Enterprises in India - Results of A Field SurveyDocument42 pagesApproach To Energy Efficiency Among Micro, Small and Medium Enterprises in India - Results of A Field SurveysharmaarakeyshNo ratings yet
- 2012 Compiler Design - ECS 603Document3 pages2012 Compiler Design - ECS 603sharmaarakeyshNo ratings yet
- Computer and Network SecurityDocument6 pagesComputer and Network SecuritysharmaarakeyshNo ratings yet
- To Whom It May Concern: DateDocument1 pageTo Whom It May Concern: DatesharmaarakeyshNo ratings yet
- Internet and Java ProgrammingDocument4 pagesInternet and Java ProgrammingsharmaarakeyshNo ratings yet
- Holidays 2015Document6 pagesHolidays 2015s2th9aNo ratings yet
- Lec 05 Logical ClocksDocument26 pagesLec 05 Logical ClockssharmaarakeyshNo ratings yet
- BookunixDocument328 pagesBookunixMohammed AhmedNo ratings yet
- BM106 Misc FileDocument37 pagesBM106 Misc FilesharmaarakeyshNo ratings yet
- Introduction To Distributed Systems: CSE 380 Computer Operating SystemsDocument17 pagesIntroduction To Distributed Systems: CSE 380 Computer Operating SystemssharmaarakeyshNo ratings yet
- Digital Electronics - SImplifiedDocument6 pagesDigital Electronics - SImplifiedsharmaarakeyshNo ratings yet
- Alternating Current Circuits and Electromagnetic Waves ExplainedDocument32 pagesAlternating Current Circuits and Electromagnetic Waves ExplainedKristineNo ratings yet
- Reinforced Concrete WorksDocument5 pagesReinforced Concrete WorksRanjith EkanayakeNo ratings yet
- Week 4 Home Learning PlanDocument11 pagesWeek 4 Home Learning PlanJessel CleofeNo ratings yet
- 0 Finite DifferenceDocument18 pages0 Finite Differencevisamarinas6226No ratings yet
- Botsios, S., Georgiou, D., & Safouris, N. (2008) - Contributions ToDocument16 pagesBotsios, S., Georgiou, D., & Safouris, N. (2008) - Contributions TosplakenerNo ratings yet
- Image CompressionDocument33 pagesImage CompressionMAILMEUSNo ratings yet
- Sec. 6.7 Peak Structural Response From The Response SpectrumDocument2 pagesSec. 6.7 Peak Structural Response From The Response SpectrumIt'x PathanNo ratings yet
- MIND Seamap GunLink 2500Document4 pagesMIND Seamap GunLink 2500Steve HeartNo ratings yet
- Moment of Inertia Basics UnderstandingDocument20 pagesMoment of Inertia Basics UnderstandingRajesh N Priya GopinathanNo ratings yet
- Ch4.1. Black Box Testing Deadline 21 - 00 Mon 07 NovDocument4 pagesCh4.1. Black Box Testing Deadline 21 - 00 Mon 07 Novloitlttl1342002No ratings yet
- Guidlines For SeatrialsDocument14 pagesGuidlines For SeatrialsmariodalNo ratings yet
- Pulp and Paper Tech - I Introduction and History of Pulping ProcessDocument62 pagesPulp and Paper Tech - I Introduction and History of Pulping ProcessVishnu KollarethNo ratings yet
- Ch2 Operating-System StructuresDocument88 pagesCh2 Operating-System Structurescs LiuNo ratings yet
- Performance Indicator - Physics 2Document7 pagesPerformance Indicator - Physics 2lim chuan yangNo ratings yet
- Astrological Sign: Western Zodiac SignsDocument3 pagesAstrological Sign: Western Zodiac SignsmackNo ratings yet
- Wyong Road Enviro Factors Appendix PDocument314 pagesWyong Road Enviro Factors Appendix PAniculaesi MirceaNo ratings yet
- Design Analysis of Algorithms: Technology, West BengalDocument7 pagesDesign Analysis of Algorithms: Technology, West BengalSubhasis MaityNo ratings yet
- of ProjectDocument24 pagesof ProjectamarparimiNo ratings yet
- Final Assignment 2 ChafikDocument16 pagesFinal Assignment 2 ChafikSaheed A BusuraNo ratings yet
- Arti PDFDocument7 pagesArti PDFSuvidVijay FadanvisNo ratings yet
- Chapter 10 Explores Weathering, Soil Formation and Mass WastingDocument34 pagesChapter 10 Explores Weathering, Soil Formation and Mass WastingEverett Heart Pargad VNo ratings yet
- Panel Dual Polarization Half-Power Beam Width Adjust. Electrical DowntiltDocument3 pagesPanel Dual Polarization Half-Power Beam Width Adjust. Electrical DowntiltYarinaNo ratings yet