Professional Documents
Culture Documents
Neural Cryptography For Secret Key Exchange
Uploaded by
IJMTST-Online JournalOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Neural Cryptography For Secret Key Exchange
Uploaded by
IJMTST-Online JournalCopyright:
Available Formats
International Journal for Modern Trends in Science and Technology
Volume: 03, Issue No: 03, March 2017
ISSN: 2455-3778
http://www.ijmtst.com
Neural Cryptography for Secret Key Exchange
Prof.Pranita P.Hadke1| Prof.Madhuri R. Dubey2
1 Department of Information Technology, Yeshwantrao Chavan College of Engineering, Nagpur, Maharashtra, India.
2 Department of Information Technology, SBJITMR, Nagpur, Maharashtra, India
To Cite this Article
Prof.Pranita P.Hadke and Prof.Madhuri R. Dubey, Neural Cryptography for Secret Key Exchange, International Journal
for Modern Trends in Science and Technology, Vol. 03, Issue 03, 2017, pp. 15-18.
ABSTRACT
The goal of any cryptography system is the exchange of information among the intended user without any
leakage of information to other who may have unauthorized access to it. A common secret key could be
created over a public channel accessible to any opponent. Neural networks can be used to generate common
secret key. In case of neural cryptography, both the communicating networks receive an identical input
vector, generate an output bit and are trained based on the output bit. The two networks and their weights
vectors exhibit a new phenomenon, where the networks synchronize to a state with identical time-dependent
weights. The generated secret key over a public channel is used for encryption and decryption of the message
or information send over the channel.
KEYWORDS: Neural networks, Cryptography, Key exchange, neural cryptography.
Copyright 2017 International Journal for Modern Trends in Science and Technology
All rights reserved.
decryption. These keys can be identical as a public
I. INTRODUCTION and a private key.
Nowadays information security has become an Key generation is the most significant issue in
important aspect in every organization. In other cryptography technique. In recent times wide
words people have to be assured that the ranges of techniques are developed to protect data
information to be read by only the sender and and information from eavesdropper. These
receiver. The basic need to provide security is using algorithms have their virtue and shortcomings. A
cryptography. Cryptosystem are commonly used neural network based approach offers an attractive
for protecting the integrity, confidentiality, and solution to this problem in that it provides a
authenticity of information resources. The design suitable framework within which data can be
of cryptography algorithm is complicated by the readily code. Neural networks are non linear
fact that a variety of cryptanalytic attacks are statistical data modeling tools. They can be used to
available that can often be successfully used to model complex relationship between inputs and
recover the key or the plaintext. outputs or to find patterns in data. A phenomenon
Cryptography has two style of encrypting data; of neural networks is applied in cryptography
symmetrical and asymmetrical. Symmetric system. This is used for generating secret key.
encryptions use the same key for encryption and
decryption process, and also can be defined as a II. PROBLEM OF SECRET KEY EXCHANGE IN
CRYPTOGRAPHY
secret-key, shared-key, and private-key.
Asymmetric cryptography uses different encryption The problem of key exchange is one of the main
keys for encryption and decryption process. In this concerns of classical cryptography and it was
case an end user on a network, public or private, extensively studied in classical cryptography. The
has a pair of key; one for encryption and one for first published key exchange protocol was based on
number theory and it is known by Diffie-Hellman
15 International Journal for Modern Trends in Science and Technology
Prof.Pranita P.Hadke and Prof.Madhuri R. Dubey : Neural Cryptography for Secret Key Exchange
key exchange protocol. While it depends on the coupled to the two system. The networks received a
difficulties of computing discrete logarithms, it is common input vector after calculating their output
vulnerable to man-in-middle attack. Moreover, it is and updated their weight vector according to the
computationally intensive. The man-in-middle match between their mutual outputs in every time
attack is solved by authentication mechanisms. step. The input and output relations are not
exchanged through a public channel until their
III. RELATED WORK weight vectors are matched and can be used as a
This paper [1] proposed two artificial neural secret key for encryption and decryption of secret
networks for cryptography. Experimental results message. The weight vectors of the two neural
show that the two networks are secure, without networks begin with random number, which are
any result about efficiency. generated by Pseudo-Random Number Generator
This paper [2] presented synchronization (PRNGs). The proposed model fixed the security
neural key-exchange algorithm for cryptography. against numerical attacks.
The model has multi-layer feed-forward neural This paper [6] proposed a secret key over a
network which have two tree parity machine (TPM) public channel using artificial neural network. The
that synchronized with a random initial weight act artificial neural network contains of two multi layer
as common secret key for the encryption and neural networks trained on their mutual output
decryption process. The weight can be updated bits and able to synchronize. The two network
according to the learning rules only if the output starting from random initial weights and learning
values of the two machines are equal. Throughout from each other with two multilayer networks relax
the synchronization process, only the input vectors to the state with time dependent identical synaptic
and the output vectors are transmitted over the weights. The partners didnt exchange any
public channel. information over a secret channel before their
This paper [3] presented a new modification of communication. Synchronization of neural
the Advanced Encryption Standard to be immune networks can be considered as the key generation
against some attacks using non linear neural in cryptography. The common identical weights of
network. The neural network model performs the two partners can be used as a key for key
cryptography processes via a symmetric key cipher generation over public channels which are not
that used as the initial weights for the neural based on number theory. Experimental result
network which trained to its final weight fast and shows that the model is fast, simple, and secure.
low cost algorithm. The objective form the network This paper [7] presented a secured
has been selected to equivalent the output of the cryptography secret-key based on neural network
AES that have an efficient and recommended in a public channel. The proposed model has two
security. Simulation results show the proximity of neural network that are trained on their alternative
the result accomplished by the proposed NN-based output synchronized to an equal time dependent
AES cryptosystem with that of the normal AES. weight vector through a chaos synchronization
This paper [4] proposed multi-layer neural system that starting from different initial condition.
networks in cryptography. The multilayer neural The system combined the neural network with the
networks in cryptography. The multilayer neural logistic chaotic map. The both partners used their
networks modified by back-propagation. The neural networks as input for the logistic maps
planned model converted the input message into which generated the output bits to be learned, by
ASCII code then gets the sequence of bits for each mutually learning. The two neural networks
code which divides into 6 bit blocks are used as approach each other and generated a matching
input for the encryption process. The cipher key is signal to the chaotic maps. The chaotic
the neural network structure contained input synchronization applied in the neural
layer, hidden layer, output layer, and updated cryptography enhanced the cryptography system
weights. Experimental results show that the and improved the security.
system is secure. This paper [8] proposed a common secret key
This paper [5] proposed a secret key using generated based on neural networks. The neural
neural cryptography, based on synchronization of cryptography has two communication networks
Tree Parity Machine (TPMs) by mutual learning. that received an identical input vector, generated
The system has two identical dynamical system, an output bit and are trained based on output bit.
which starting from different initial conditions and The network model initials the weight randomly
synchronized by a common input values which are and the outputs bit are generated finally and
16 International Journal for Modern Trends in Science and Technology
Prof.Pranita P.Hadke and Prof.Madhuri R. Dubey : Neural Cryptography for Secret Key Exchange
exchange between partners. The weight may be
modified if the outputs of both partners are
matched. The modified weight after synchronize
act as a secret key for the encryption and
decryption process. Simulation results show that
the cryptosystem based on ANNs is secure.
In this paper [9] a secret key is generated over a
public channel based on neural network. The
model has a neural network machine contains of
two partners started with initial weights and Tree Parity Machine
different initial condition which synchronized by a
common external signal and received a common 3. Tree Parity Machine
random input vector and learned their mutual
output bits. The synaptic weights are used as a Tree Parity Machine is special type of multi-layer
secret key over a pubic channel. Simulation results feed-forward neural network. It consist of one
show that the model are secure and efficiency. output neuron, K hidden neurons and K*N input
neurons. Inputs to the networks take 3 values:
IV. PROPOSED SYSTEM xij 1,0,1
Proposed Approach The weights between input and hidden neurons
take the values:
1. Interacting Neural Networks and wij , ,0, . , +
Cryptography Output values of each hidden neurons is
calculated as a sum of all multiplication of input
i. Two identical dynamic systems, starting from neurons and these weights:
different initial condition can be synchronized = ( =1 )
by a common external signal which is coupled
Sig num is a simple function, which returns -1,0 or
to the two systems. Two networks which are
1:
trained on their mutual output can
1 < 0,
synchronize to a time dependent state of
Sgn (x)= 0 = 0,
identical synaptic weights. 1 > 0.
ii. This phenomenon is also applied to
If the scalar product is 0, the output of the hidden
cryptography. Neural networks learn from
neuron is mapped to -1 in order to ensure a binary
examples. Training means, that synaptic
output values. The output of neural network is
weights adopt by simple rules to the
then computed as the multiplication of all values
input/output pairs. After the training phase
produced by hidden elements:
the neural network is able to generalize: it can
classify the input pattern which does not =
belong to the training set. =1
iii. The two patterns A and B do not have to share Output of the tree parity machine is binary.
the common secret key but use their identical
weights as a secret key need for encryption. 4. Secret Key Generation
iv. In neural network an attacker E who knows all
the details of the algorithm and record any The different stages in the secret key generation
procedure which is based on neural networks can
communication transmitted through this
be stated as follows:
channel finds it difficult to synchronize with the 1. Determination of neural network parameter: K
parties, and hence to calculate the common the number of hidden layers units, n the input
secret key. layer units for each hidden layer unit, l the
2. Neural Key Exchange range of synaptic weight values is done by the
The most used protocol for key exchange two machine A and B.
between two parties A and B in the practice is 2. The network weight to be initialized randomly.
3. The following steps are repeated until
Diffie-Hellman protocol. Neural key exchange,
synchronization occurs.
which is based on the synchronization of two tree 4. Inputs are generated by the third party (key
parity machine, should be a secure replacement. distribution center).
5. The inputs of the hidden units are calculated.
17 International Journal for Modern Trends in Science and Technology
Prof.Pranita P.Hadke and Prof.Madhuri R. Dubey : Neural Cryptography for Secret Key Exchange
6. The output bit is generated and exchange [2] Ajit Singh, Havir Singh, Cryptography for Secret
between the two machine A and B. Key Exchange and Encryption with AES,
7. If the output vectors of both the machine agree International Journal of Advanced Research in
with each other then the corresponding weights Computer Science and Software Engineering, Vol. 3,
are modified using the learning rules. Issue. 5, 376-381, 2013.
8. When synchronization is finally occurred, the [3] Siddeq Y. Ameen, Ali H. Mahdi, AES Cryptosystem
synaptic weights are same for both the Development using Neural Networks, Inernational
networks. And these weights are used as secret Journal of Computer and Electrical Engineering,
key. Vol. 3, No. 2, 315-318, 2011.
[4] Eva Volna, Martin Kotyrba, Vaclav Kocian, Michal
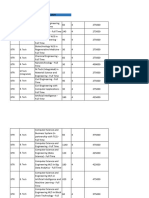
5. Proposed Architecture Janosek, Cryptography based on neural network,
Proceedings 6th European Conference on Modelling
and Simulation, 2012.
[5] N. Prabakaran, P. Vivekanandan, A New Security
on Neural Cryptography with Queries, International
Journal of Advanced Networking and Apllication
(IJAIA), Vol.2, No. 1, 60-69, 2011.
[6] Wolfgang Kinzel, IdoKanter, Neural Cryptography,
Proceedings TH2002 Supplement, Vol. 4, 147-153,
2003.
[7] Einat Klein, Rachel Mislovaty, Idokanter, Andreas
Ruttor, Wolfgang Kinzel, Synchronization of neural
network by mutual learning and its application to
cryptography, International Proceeding of:
Advances in Neural Information Processing System
17, Neural Information Processing System NIPS,
2004.
[8] R. M. Jogdand, Sahana S. Bisalapur, Design of an
efficient neural key generation, International
Journal of Artificial Intelligence & Application
(IJALA), Vol. 2, No. 1, 60-69, 2011.
[9] Pratap Singh, Havir Singh, Cryptography in
Structure adaptable digital neural networks,
V. RESULTS National monthly refereed journal of research in
It is expected that the proposed approach make science & technology, Vol. 1, Issue. 12, 35-44,2012.
the error rate as minimum as possible and highly [10] William Stalling, Cryptography and Network
Security: Principles and Practicle, (5 th Edition),
increase the security of data in data
Prentice Hall, 2010.
communication system.
[11] M. Arvandi, A. Sadeghian, On the use of Recurrent
Neural Networks to Design Symmetric Cipher, IEEE
VI. CONCLUSION AND FUTURE WORK Computational Intelligence Magazine, pp. 42-53,
Artificial neural network is an efficient technique May 2008.
which has the ability to implement security using [12] Khalil Shihab, A back propagation Neural Network
tree parity machine (i.e. special type of feed forward for computer Network Security, Journal of
neural network). One of the primary aspect in this computer science 2(9): 710-715, 2006.
[13] Behrouz A. Forouzan, Cryptography and Network
field of neural cryptography appears to be the
Security, Tata McGraw-Hill, Special Indian Edition,
discovery of neural architecture with very high
2007.
synchronization speed, and design the encoding [14] Meghdad Ashtiyani, Soroor Behbahani, Saeed Asadi,
and entropy of the information exchanged during Parmida Moradi Birgani, Transmitting Encrypted
mutual learning, to prevent the synchronization of Data by Neural network, 2007 IEEE International
an attacker during the mutual learning process. Symposium on Signal Processing and Information
Technology, pp. 385-389, 2007.
REFERENCES [15] Seref S. Neclao, Neural Solution for Information
[1] Navita Agarwal, Prachi Agarwal, Use of Artificial Security, Politeknik Dergisi, Journal of Polytechnic,
Neural Network in the Field of Security, MIT Vol. 10, No. 1, 21-25,2007.
International Journal of Computer Science &
Information Technology, Vol. 3, No. 1, 42-44, 2013.
18 International Journal for Modern Trends in Science and Technology
You might also like
- Etextbook PDF For The Essentials of Technical Communication 4th by Elizabeth TebeauxDocument61 pagesEtextbook PDF For The Essentials of Technical Communication 4th by Elizabeth Tebeauxrhea.dixon130100% (38)
- Cyber Security 2017Document8 pagesCyber Security 2017Anonymous i1ClcyNo ratings yet
- Symmetric Cryptography Using Nural NetworksDocument59 pagesSymmetric Cryptography Using Nural NetworksNAVEENA.VEMPADANo ratings yet
- Cyber Security Final RepoDocument16 pagesCyber Security Final Reporaj anaNo ratings yet
- AMPC A Lightweight Hybrid Cryptographic Algorithm For Wireless Sensor NetworksDocument5 pagesAMPC A Lightweight Hybrid Cryptographic Algorithm For Wireless Sensor NetworksInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- 18 05 Ijsartv4i523250Document5 pages18 05 Ijsartv4i523250Haroon KhanNo ratings yet
- Symmetric Cipher Design Using Recurrent Neural NetworksDocument8 pagesSymmetric Cipher Design Using Recurrent Neural NetworksTCCLONo ratings yet
- Neural Network Based Message Concealment SchemeDocument13 pagesNeural Network Based Message Concealment SchemeIJRASETPublicationsNo ratings yet
- Design and Implementation of A New DNA Based Stream Cipher Algorithm Using PythonDocument12 pagesDesign and Implementation of A New DNA Based Stream Cipher Algorithm Using PythonAlnmer MohammedNo ratings yet
- Cryptography Using Artificial Neural NetworkDocument18 pagesCryptography Using Artificial Neural NetworkPrayNo ratings yet
- Quantum CryptographyDocument20 pagesQuantum CryptographyBridget SmithNo ratings yet
- Cryptography ReportDocument10 pagesCryptography ReportAkshath KandlurNo ratings yet
- 24-03-2022-1648118520-6-.-1. Engg - A New Varying Cipher For Symmetric Key CryptosystemsDocument10 pages24-03-2022-1648118520-6-.-1. Engg - A New Varying Cipher For Symmetric Key CryptosystemsImpact JournalsNo ratings yet
- Cryptography Based On Artificial Neural NetworkDocument5 pagesCryptography Based On Artificial Neural NetworkSaddam Al-KhamaysehNo ratings yet
- Rsa PDFDocument5 pagesRsa PDFRoseri SinagaNo ratings yet
- SACA: A Study of Symmetric and Asymmetric Cryptographic AlgorithmsDocument8 pagesSACA: A Study of Symmetric and Asymmetric Cryptographic Algorithmsghada sayedNo ratings yet
- Applied Neuro CryptographyDocument191 pagesApplied Neuro CryptographyRaiee Dee100% (1)
- Bello M ConfDocument11 pagesBello M ConfSýstëmàtíçBéllóNo ratings yet
- Image/Data Encryption-Decryption Using Neural Network: Shweta R. Bhamare, Dr. S.D.SawarkarDocument7 pagesImage/Data Encryption-Decryption Using Neural Network: Shweta R. Bhamare, Dr. S.D.SawarkarPavan MasaniNo ratings yet
- New Cryptography Algorithm To Provide Security For Wireless Sensor NetworkDocument3 pagesNew Cryptography Algorithm To Provide Security For Wireless Sensor Networkit89No ratings yet
- A New Method For Encryption Using Fuzzy Set TheoryDocument7 pagesA New Method For Encryption Using Fuzzy Set TheoryAgus S'toNo ratings yet
- Combined Strength of Steganography and Cryptography-A Literature SurveyDocument4 pagesCombined Strength of Steganography and Cryptography-A Literature SurveyFalasifaNo ratings yet
- A Review Paper On AES and DES Cryptographic AlgorithmsDocument6 pagesA Review Paper On AES and DES Cryptographic AlgorithmsFadhil SahibNo ratings yet
- Research ArticleDocument11 pagesResearch ArticleEdison QuimbiambaNo ratings yet
- AP - K E S A N: AIR Wise EY Stablishment Cheme For D Hoc EtworksDocument12 pagesAP - K E S A N: AIR Wise EY Stablishment Cheme For D Hoc EtworksAIRCC - IJCNCNo ratings yet
- I.: Neural Cryptography With Queries: Journal of Statistical Mechanics Theory and Experiment December 2004Document13 pagesI.: Neural Cryptography With Queries: Journal of Statistical Mechanics Theory and Experiment December 2004Francisco QuingaNo ratings yet
- Chapter 94Document5 pagesChapter 94cheintNo ratings yet
- An Overview of Major Developments, Applications and Challenges in Quantum CryptographyDocument9 pagesAn Overview of Major Developments, Applications and Challenges in Quantum CryptographyInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Paper 41-A Survey On The Cryptographic Encryption AlgorithmsDocument12 pagesPaper 41-A Survey On The Cryptographic Encryption Algorithmsmcselles100% (1)
- Network Coding-Based Post-Quantum CryptographyDocument27 pagesNetwork Coding-Based Post-Quantum CryptographyTanu PraNo ratings yet
- A Review Paper On Data Encryption and DecryptionDocument9 pagesA Review Paper On Data Encryption and DecryptionIJRASETPublicationsNo ratings yet
- (IJCST-V5I3P31) :P. Rajesh Kannan, Dr. MalaDocument5 pages(IJCST-V5I3P31) :P. Rajesh Kannan, Dr. MalaEighthSenseGroupNo ratings yet
- paperIJERM0205069 1Document5 pagespaperIJERM0205069 1amit raiNo ratings yet
- Proxy Re-Encryption Scheme Secured Against Chosen Cipher Text AttackDocument5 pagesProxy Re-Encryption Scheme Secured Against Chosen Cipher Text Attackeditor_ijarcsseNo ratings yet
- DES, AES and Blowfish: Symmetric Key Cryptography Algorithms Simulation Based Performance AnalysisDocument7 pagesDES, AES and Blowfish: Symmetric Key Cryptography Algorithms Simulation Based Performance AnalysisRini Angraini100% (1)
- 3.1 Public Key CryptographyDocument20 pages3.1 Public Key CryptographyTHIRU MURUGAN R 2k20BCA339No ratings yet
- A Chaotic Block Cipher For Real-Time MultimediaDocument7 pagesA Chaotic Block Cipher For Real-Time Multimedia91charlyNo ratings yet
- Complexity AnalysisDocument5 pagesComplexity AnalysisRama ChandranNo ratings yet
- 26 29, Tesma501, IJEAST PDFDocument4 pages26 29, Tesma501, IJEAST PDFsanketNo ratings yet
- Energy-Efficient Secure Data Aggregation Framework (Esdaf) Protocol in Heterogeneous Wireless Sensor NetworksDocument10 pagesEnergy-Efficient Secure Data Aggregation Framework (Esdaf) Protocol in Heterogeneous Wireless Sensor Networksijire publicationNo ratings yet
- A Secure Network Communication Protocol Based On TextDocument7 pagesA Secure Network Communication Protocol Based On TextLarisaNo ratings yet
- A Comprehensive Review of Cryptographic AlgorithmsDocument9 pagesA Comprehensive Review of Cryptographic AlgorithmsIJRASETPublicationsNo ratings yet
- Patel 2016Document5 pagesPatel 2016Disha ModiNo ratings yet
- Cloud Computing PPDocument4 pagesCloud Computing PPcse3No ratings yet
- Securing Information: Cryptography and SteganographyDocument5 pagesSecuring Information: Cryptography and SteganographyNull PointerNo ratings yet
- RoopeshKumar CryptoDocument13 pagesRoopeshKumar Cryptoمنار المالكيNo ratings yet
- Secure Data Communication and Cryptography Based On DNA Based Message EncodingDocument6 pagesSecure Data Communication and Cryptography Based On DNA Based Message EncodingHaroonRashidNo ratings yet
- VTU Network Security (10ec832) Unit-2 Notes..Document91 pagesVTU Network Security (10ec832) Unit-2 Notes..jayanthdwijesh h p100% (3)
- 2012 CTRSA Plaintext CheckableEncryptionDocument17 pages2012 CTRSA Plaintext CheckableEncryptionzfrqgw2cjpNo ratings yet
- Distributed Computing of DNA Cryptography and Randomly Generated Mealy MachineDocument10 pagesDistributed Computing of DNA Cryptography and Randomly Generated Mealy MachineIJRASETPublicationsNo ratings yet
- Route Diversity Based Optimal Path Selection Using Random Key GenerationDocument8 pagesRoute Diversity Based Optimal Path Selection Using Random Key GenerationJournal of Computer ApplicationsNo ratings yet
- (IJCT-V2I5P16) Authors :A.Senthilkumar, R.DivyaDocument5 pages(IJCT-V2I5P16) Authors :A.Senthilkumar, R.DivyaIjctJournalsNo ratings yet
- Audio Encryption Optimization: Harsh Bijlani Dikshant Gupta Mayank LovanshiDocument5 pagesAudio Encryption Optimization: Harsh Bijlani Dikshant Gupta Mayank LovanshiAman Kumar TrivediNo ratings yet
- Sem CompDocument5 pagesSem CompsrisairampolyNo ratings yet
- Public Key Based Cryptoschemes For Data Concealment in Wireless Sensor NetworksDocument8 pagesPublic Key Based Cryptoschemes For Data Concealment in Wireless Sensor Networkspoonam pandeyNo ratings yet
- 9 Dr. Amit Sharma 1459672381 - 254VDocument6 pages9 Dr. Amit Sharma 1459672381 - 254VamittechnosoftNo ratings yet
- S 2 SE An Encryption Methodology PDFDocument3 pagesS 2 SE An Encryption Methodology PDFThet Hmue Hay ThiNo ratings yet
- Cryptography and Network Security Lecture NotesDocument171 pagesCryptography and Network Security Lecture NoteskomalNo ratings yet
- JournalNX - Neural NetworksDocument4 pagesJournalNX - Neural NetworksJournalNX - a Multidisciplinary Peer Reviewed JournalNo ratings yet
- A Security Scheme For Wireless Sensor NetworksDocument5 pagesA Security Scheme For Wireless Sensor NetworksRonaldo MilfontNo ratings yet
- Dynamic Data Discovery and Diffusion With Security in Wireless Sensor NetworksDocument22 pagesDynamic Data Discovery and Diffusion With Security in Wireless Sensor NetworksAjonna LNo ratings yet
- New Frontiers in Cryptography: Quantum, Blockchain, Lightweight, Chaotic and DNAFrom EverandNew Frontiers in Cryptography: Quantum, Blockchain, Lightweight, Chaotic and DNANo ratings yet
- Arduino Based Traffic Monitoring and Controlling SystemDocument4 pagesArduino Based Traffic Monitoring and Controlling SystemIJMTST-Online JournalNo ratings yet
- Synthesis of Natural Food Colour From Carotenoid Using Flower PetalsDocument10 pagesSynthesis of Natural Food Colour From Carotenoid Using Flower PetalsIJMTST-Online JournalNo ratings yet
- An Multi-Input ZCS DC-DC Front-End - Converter Based Multilevel Inverter For The Integration of Renewable Energy SourcesDocument4 pagesAn Multi-Input ZCS DC-DC Front-End - Converter Based Multilevel Inverter For The Integration of Renewable Energy SourcesIJMTST-Online JournalNo ratings yet
- IoT Mining Tracking &worker Safety Emergency AlertDocument4 pagesIoT Mining Tracking &worker Safety Emergency AlertIJMTST-Online JournalNo ratings yet
- Performance Evaluation and Optimization of Wind-Solar PV Hybrid Electricity Generation and Application To Electric VehicleDocument17 pagesPerformance Evaluation and Optimization of Wind-Solar PV Hybrid Electricity Generation and Application To Electric VehicleIJMTST-Online JournalNo ratings yet
- Automatic Plaster MachineDocument4 pagesAutomatic Plaster MachineIJMTST-Online JournalNo ratings yet
- A Study On The Attitude and Purchase Intention of Consumer Regarding Green ElectronicsDocument13 pagesA Study On The Attitude and Purchase Intention of Consumer Regarding Green ElectronicsIJMTST-Online JournalNo ratings yet
- Design and Implementation of Women Safety SystemDocument5 pagesDesign and Implementation of Women Safety SystemIJMTST-Online JournalNo ratings yet
- 8 Ijmtst0606016 PDFDocument4 pages8 Ijmtst0606016 PDFIJMTST-Online JournalNo ratings yet
- Identification of Brain Tumor Using MATLABDocument4 pagesIdentification of Brain Tumor Using MATLABIJMTST-Online JournalNo ratings yet
- Experimental Validation On ASTM A516 Grade 70 Carbon Steel by Non-Destructive TestingDocument4 pagesExperimental Validation On ASTM A516 Grade 70 Carbon Steel by Non-Destructive TestingIJMTST-Online JournalNo ratings yet
- Manually Operated Dry Land Weeder: A StudyDocument7 pagesManually Operated Dry Land Weeder: A StudyIJMTST-Online JournalNo ratings yet
- Recent Development and Advancement of Regenerative Braking in Electric BikeDocument4 pagesRecent Development and Advancement of Regenerative Braking in Electric BikeIJMTST-Online JournalNo ratings yet
- Ijcta MitsDocument8 pagesIjcta MitsIJMTST-Online JournalNo ratings yet
- Effective Service Security Schemes in Cloud Computing: K.Sravani, K.L.A.NiveditaDocument6 pagesEffective Service Security Schemes in Cloud Computing: K.Sravani, K.L.A.NiveditaInternational Journal of computational Engineering research (IJCER)No ratings yet
- Checkpoint HealthCheck-Audit Checklist Ver 1 0Document1 pageCheckpoint HealthCheck-Audit Checklist Ver 1 0Sandeep Thete100% (1)
- Electronic Mail SecurityDocument35 pagesElectronic Mail SecurityKAVITHA TNo ratings yet
- Spin 2Document1 pageSpin 2Rebecca FrancisNo ratings yet
- Cmek CsekDocument2 pagesCmek Csekkishore.zero9No ratings yet
- SRM KTR Fees 2024-25Document31 pagesSRM KTR Fees 2024-25M Manikanda PrabhuNo ratings yet
- College of Engineering: Chemical DepartmentDocument40 pagesCollege of Engineering: Chemical DepartmentjaiminNo ratings yet
- Past Question ICSDocument2 pagesPast Question ICSAnanya SwaminathanNo ratings yet
- Cross Certification p37 v03Document37 pagesCross Certification p37 v03pinevn2010No ratings yet
- FPIP Park PAss ID Application Form Rev 03 PDFDocument2 pagesFPIP Park PAss ID Application Form Rev 03 PDFLorielaneSorianoGonzalesNo ratings yet
- W Pacb54Document306 pagesW Pacb54VirgilHerciu100% (1)
- Osint 1624490707Document13 pagesOsint 1624490707Caio Andrade100% (1)
- Checkmarx vs. SonarQube Report From PeerSpot 2022-05-07 1epfDocument34 pagesCheckmarx vs. SonarQube Report From PeerSpot 2022-05-07 1epfMaster BatNo ratings yet
- ADWEA - IS - Risk Monitoring and Reporting v1Document15 pagesADWEA - IS - Risk Monitoring and Reporting v1tabishasifiNo ratings yet
- Ethical HackingDocument19 pagesEthical HackingAhmed OusmanNo ratings yet
- Test Cases.Document8 pagesTest Cases.Назар БачинськийNo ratings yet
- App Certification Standards FinalDocument16 pagesApp Certification Standards FinalSteveEpsteinNo ratings yet
- Computer and Information Security End User QuestionnaireDocument12 pagesComputer and Information Security End User QuestionnaireAnil ThomasNo ratings yet
- SAD Module 1 Introduction To System Analysis and DesignDocument38 pagesSAD Module 1 Introduction To System Analysis and DesignPam VillegasNo ratings yet
- BYOD Security Engineering A Framework & Its AnalysisDocument19 pagesBYOD Security Engineering A Framework & Its AnalysisrizkiNo ratings yet
- CASP Practice QuestionsDocument43 pagesCASP Practice Questionskeimma33% (3)
- Ask Me (Ask4pc)Document2 pagesAsk Me (Ask4pc)Rahul Jaiswal100% (1)
- Cybercriminal Impacts On Online Business and Consumer ConfidenceDocument11 pagesCybercriminal Impacts On Online Business and Consumer ConfidenceMissShellyBabyNo ratings yet
- ME Computer Networks Syllabus - 5!8!13Document38 pagesME Computer Networks Syllabus - 5!8!13megharodeNo ratings yet
- Gwhs Annex CDocument48 pagesGwhs Annex CMonchie RoseteNo ratings yet
- Mitnick Important PointsDocument4 pagesMitnick Important PointsRohit SahayNo ratings yet
- ICT Post TestDocument6 pagesICT Post Testleajoycalape014No ratings yet
- L4 Slides - Cyber Security - Y9Document23 pagesL4 Slides - Cyber Security - Y9haydenNo ratings yet