Professional Documents
Culture Documents
Chapter 3
Uploaded by
John Paul0 ratings0% found this document useful (0 votes)
11 views6 pagesCIS chapter 3
Copyright
© © All Rights Reserved
Available Formats
DOCX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCIS chapter 3
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
11 views6 pagesChapter 3
Uploaded by
John PaulCIS chapter 3
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
You are on page 1of 6
Chapter 3: operating system, either
Security Part I: Auditing intentionally or unintentionally.
Operating Systems and Networks Operating Systems Controls
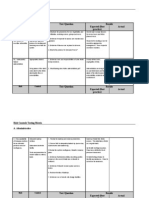
Operating System Control Objectives Access Privileges - Audit Objectives:
Protect itself against tampering by users. Verify that access privileges are
Protect users from accessing, destroying, or consistent with separation of
corrupting another users programs or data. incompatible functions and
Safeguard users application modules from organization policies.
destroying or corrupting other modules. Access Privileges - Audit Procedures:
Safeguard its own modules from destroying Review policies for separating
or corrupting other modules. incompatible functions.
Protect itself from its environment including Review a sample of user privileges,
power failures and other disasters. especially access to data and
Operating Systems Security involves policies, programs.
procedures and controls that determine who can Review security clearance checks of
access the operating system. privileged employees.
Security Components Determine if users have formally
Log-On Procedure: acknowledged their responsibility to
First line of defense against maintain data confidentiality.
unauthorized access consisting of Review users permitted log-on
user IDs and passwords. times.
Access Token: Password Controls
Contains key information about the A password is a secret code user enters to
user which is used to approve gain access to system or data.
actions attempted during the Common contra-security behaviors:
session. Forgetting passwords or failing to
Access Control List: regularly change them.
Assigned to each IT resource and Post-it-syndrome which puts
used to control access to the passwords on display.
resource. Simplistic passwords that are easy
Discretionary Access Privileges: for criminals to anticipate.
Allows user to grant access to Most commonly passwords are reusable.
another user. Management should require
Threats to Operating System Integrity changes and disallow weak ones.
Accidental threats include hardware failures One-time passwords are automatically
and errors in user applications. generated constantly by the system when
Intentional threats are often attempts to user enters a PIN.
illegally access data or violate privacy for Operating Systems Controls
financial gain. Password Control - Audit objectives:
Growing threat is destructive programs with Ensure adequacy and effectiveness
no apparent gain, which come from three of password policies for controlling
sources: access to the operating system.
Privileged personnel who abuse Password Control - Audit procedures:
their authority. Verify passwords are required for all
Individuals who browse the users and that new users are
operating system to identify and instructed in their use and
exploit security flaws. importance.
Individuals who insert viruses or Ensure controls requiring passwords
other destructive programs into the to be changed regularly.
Review password file for weak Two types of audit logs:
passwords. Keystroke monitoring involves
Verify encryption of the password recording users keystrokes and the
file. systems response.
Assess the adequacy of password Event monitoring summarizes key
standards. activities related to system
Review account lockout policies and resources.
procedures. Audit trails can be used to: detect
Controlling Against Malicious & Destructive Programs unauthorized access, reconstruct events and
Organizations can reduce threats: promote personal accountability.
Purchase software from reputable Benefits must be balanced against costs.
vendors in original packages. Operating System Controls
Policy pertaining to unauthorized or System Audit Trails- Audit objectives:
illegal software. Ensure established system audit trail
Examine upgrades and public- is adequate for preventing and
domain software for viruses before detecting abuses, reconstructing
implementation and use. key events and planning resource
Implement procedures for changing allocation.
programs. System Audit Trails- Audit procedures:
Educate users regarding threats. Verify audit trail has been activated
Test all applications before per company policy.
implementation. Use data extraction tools to search
Make frequent backups and limit for defined conditions such as:
users to read and execute rights unauthorized users; periods of
only whenever possible. inactivity; periods of activity
Require protocols to bypass Trojan including log-on and log-off times;
horses and use antiviral software. failed log-on attempts; and specific
Operating System Controls access.
Viruses & Destructive Programs - Audit Sample security violation cases and
objectives: evaluate their disposition to assess
Verify effectiveness of procedures security group effectiveness.
to protect against programs such as Intranet Risks
viruses, worms, back doors, logic Intercepting network messages:
bombs, and Trojan horses. Sniffing: Interception of user IDs,
Viruses & Destructive Programs - Audit passwords, confidential e-mails, and
procedures: financial data files.
Interviews to determine that Accessing corporate databases:
operations personnel have been Connections to central databases
properly educated and are aware of increase risk data will be accessible
risks. to employees.
Verify new software is tested on Privileged employees:
standalone workstations before Overrides may allow unauthorized
being implemented. access critical data.
Verify that antiviral software is Organizations reluctance to
current and that upgrades are prosecute.
frequency downloaded. Negligent hiring liability requires
System Audit Trail Controls employers to check employee
System audit trails are logs that record backgrounds. Courts holding
activity at the system, application and use employers responsible for
level. employee criminal acts that could
have been prevented with Application-level firewalls provide higher,
background check. customizable network security, but add
Internet Risks overhead cost.
IP spoofing is masquerading to gain access Trade-off between convenience and security.
to a Web server and/or to perpetrate an
unlawful act without revealing ones identity. Controlling DOS Attacks
Denial of service (DOS) attack is an assault Smurf attacks: Organizations can program
on a Web server to prevent it from servicing firewalls to ignore identified attacking site.
users. SYN flood attacks have two tactics:
Particularly devastating to business Get Internet hosts to use firewalls
entities that cannot receive and that block invalid IP addresses.
process business transactions. Use security software to scan for
Motivation may be to punish an half-open connections.
organization for a grievance or may To counteract DDos attacks organizations
be done for financial gain. use intrusion prevention systems (IPS) that
Network topologies are subject to risks from employ deep packet inspection (DPI).
equipment failure which can cause Works as a filter that removes
corruption or loss. malicious packets from the flow
Three Common Types of DOS Attacks before they can affect servers and
SYN Flood: When the three-way handshake networks.
needed to establish an Internet connection Encryption
occurs, the final acknowledgement is not Conversion of data into a secret code for
sent by the DOS attacker, thereby tying-up storage and transmission over networks.
the receiving server while it waits. Sender uses an encryption
Smurf: DOS attacker uses numerous algorithm to convert the original
intermediary computers to flood the target cleartext message into a coded
computer with test messages, pings ciphertext which is decoded at
causing network congestion. receiving end.
Distributed Denial of Service May take Earliest is the Caesar cipher method.
the form of Smurf or SYN attacks, but Two fundamental components:
distinguished by the vast number of zombie Key is a mathematical value sender
computers hijacked to launch the attacks. selects.
Algorithm is procedure of shifting
Controlling Risks from Subversive Threats letters in cleartext message number
Firewalls prevent unauthorized access to or of positions key value indicates.
from a private network. To accomplish this: Private key and public key encryption are
All traffic between the outside two commonly used methods.
network and organizations intranet
must pass through the firewall. Digital Signatures & Certificate
Only authorized traffic is allowed to Digital signature is electronic authentication
pass through the firewall which that cannot be forged.
must be immune to all penetration. Sender uses a one-way hashing
Network-level firewalls provide efficient, algorithm to calculate a digest of
low security control. the text message which is encrypted
Screening router examines source to produce the digital signature.
and destination addresses attached Verifying the senders identity requires a
to incoming message packets but digital certificate which is issued by a trusted
does not explicitly authenticate third party called a certification authority
outside users. (CA).
Public key encryption is central to Audit objective is to verify integrity of
digital authentication making public transactions by determining controls are in
key management an important place to detect and correct message loss.
internal control issue. Audit procedures include examining a
Public key infrastructure (PKI) sample of messages for garbled content and
constitutes policies and procedures verifying all corrupted messages were
for administering this activity. retransmitted.
Other Subversive Threat Controls Vertical Parity Bit
Message sequence numbering inserts a
sequence number in each message to
prevent attempts to delete, change or
duplicate a message.
Message transaction log records all
attempted accesses with user ID, time of
access and location.
Request-response technique sends control
messages and responses randomly making it
difficult for an intruder to circumvent.
Call-back device requires a dial-in user to .Auditing Electronic Data Interchange (EDI)
enter and password and be identified. EDI is the intercompany exchange of
Operating Systems Controls computer-processible business information
Subversive Threats- Audit objectives: in standard format.
Verify security and integrity of Key to success is use of standard format for
financial transactions. messaging between dissimilar systems.
Determine network controls (1) can Benefit of EDI:
prevent and detect illegal access; (2) Reduces or eliminates need for data
will render captured data useless; entry.
and (3) are sufficient to preserve Reduction of errors and paper
integrity and security of data. forms.
Subversive Threats - Audit procedures: Mailed documents replaced with
Review adequacy of firewall: cheaper transmissions.
flexibility, proxy services, filtering, Automated manual procedures and
segregation of systems; audit tools; inventory reduction.
weaknesses. Overview of EDI
Verify IPS with DPI for organizations
vulnerable to DDoS.
Review security procedures and
message transaction logs.
Verify encryption process and test
operation of the call-back feature.
Controlling Risks from Equipment Failure
Line errors are losses from communications
noise.
Techniques to detect and correct data errors:
Echo check - receiver returns the
message to the sender.
Parity check - extra bit is added
onto each byte of data similar to
check digits.
Value-added Network and EDI Auditing Electronic Data Interchange (EDI)
Absence of source documents in EDI
eliminates traditional audit trail and restricts
audit tests.
Audit objectives relating to EDI are to
determine:
Transactions are authorized,
validated, and in compliance with
the trading partner agreement.
No unauthorized organizations can
gain access to database.
Authorized trading partners have
access only to approved data.
Auditing Electronic Data Interchange (EDI) Adequate controls are in place to
Electronic funds transfer (EFT) processing ensure a complete audit trail.
more complicated than EDI for purchasing EFT System Using Transaction Control Log for Audi
and selling. Trail
Converting remittance information
to electronic form can result in very
large records.
Both customer and supplier must establish
EDI transactions are valid and authorized.
Some VANs have the capability of
validating passwords and user ID
codes for the vendor.
Before conversion, translation
software can validate trading
partners IDs and passwords.
Before processing, trading partners
application software reference valid
files to validate transaction.
Auditing Procedures for EDI
EFT Transactions Between Trading Partners
Tests of Authorization and Validation
Controls:
Review agreements with VAN to
validate transactions.
Review trading partner files for
accuracy and completeness.
Tests of Access Controls:
Verify limited access to vendor and
customer files.
Verify limited access of vendors to
database.
Test EDI controls by attempting to
violate access privileges.
Tests of Audit Trail Controls:
Verify existence of transaction logs.
Review a sample of transactions to
verify key data values were
recorded correctly.
PC Accounting System Modules Verify segregation of duties and/or adequate
supervision.
Confirm reports are prepared, distributed,
and reconciled by appropriate management
at regular and timely intervals.
Determine multilevel password control as
needed.
Verify drives are removed and stored
appropriately.
Verify backup procedures are appropriate.
Verify software purchases and selection and
PC Systems Risks and Controls
acquisition procedures.
Operating System Weaknesses:
Review policy for using antiviral software.
PCs provide only minimal security
for data files and programs.
Once computer criminal gains
access to users PC, little to prevent
stealing or manipulation of the
data.
Weak access control.
Inadequate segregation of duties.
Multilevel password control used to restrict
employees sharing computers.
Risk of theft and virus infection.
Weak backup procedures.
Audit Objectives Associated with PC Security
Auditor should verify:
Controls in place to protect data,
programs, and computers from
unauthorized access, manipulation,
destruction, and theft.
Adequate supervision and
operating procedures exist to
compensate for lack of segregation
between the duties of users,
programmers, and operators.
Backup procedures are in place to
prevent data and program loss due
to system failures, errors and so on.
Systems selection and acquisition
procedures produce applications
that are high quality, and protected
from unauthorized changes.
System virus free and adequately
protected to minimize the risk of
becoming infected with a virus or
similar object.
Audit Procedures Associated with PC Security
Observe PCs are physically anchored.
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (121)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Cloud Cryptography Report - Nurul HassanDocument53 pagesCloud Cryptography Report - Nurul HassanAditya SharmaNo ratings yet
- Risk Controls Testing Matrix A. AdministrativeDocument9 pagesRisk Controls Testing Matrix A. AdministrativesilkycNo ratings yet
- Slope of A Line Given EquationDocument4 pagesSlope of A Line Given EquationJohn PaulNo ratings yet
- Management Aspects A. Form of Ownership Corporation - B. Organizational ChartDocument3 pagesManagement Aspects A. Form of Ownership Corporation - B. Organizational ChartJohn PaulNo ratings yet
- Auditing ProblemDocument1 pageAuditing ProblemJohn PaulNo ratings yet
- Book 1Document9 pagesBook 1John PaulNo ratings yet
- Fiv3 Fiv3 Fiv3: LL LLL LV LL LLL LV LL LLL LVDocument1 pageFiv3 Fiv3 Fiv3: LL LLL LV LL LLL LV LL LLL LVJohn PaulNo ratings yet
- Slope of A Line Given EquationDocument4 pagesSlope of A Line Given EquationJohn PaulNo ratings yet
- IPAGDocument3 pagesIPAGJohn PaulNo ratings yet
- Republic of The PhilippinesDocument1 pageRepublic of The PhilippinesJohn PaulNo ratings yet
- Cis 6Document1 pageCis 6John PaulNo ratings yet
- Note 17 10Document1 pageNote 17 10John PaulNo ratings yet
- College of Accountancy: Polytechnic University of The Philippines Bataan BranchDocument1 pageCollege of Accountancy: Polytechnic University of The Philippines Bataan BranchJohn PaulNo ratings yet
- Chapter 04Document32 pagesChapter 04John PaulNo ratings yet
- Which of The Following Would You Consider Your Biggest Reason To Go To An Amusement ParkDocument1 pageWhich of The Following Would You Consider Your Biggest Reason To Go To An Amusement ParkJohn PaulNo ratings yet
- College of Accountancy: Republic of The PhilippinesDocument1 pageCollege of Accountancy: Republic of The PhilippinesJohn PaulNo ratings yet
- QuotationDocument2 pagesQuotationJohn PaulNo ratings yet
- Cis 6Document1 pageCis 6John PaulNo ratings yet
- College of Accountancy: Republic of The PhilippinesDocument1 pageCollege of Accountancy: Republic of The PhilippinesJohn PaulNo ratings yet
- Eloda RecomDocument1 pageEloda RecomJohn PaulNo ratings yet
- February 05Document2 pagesFebruary 05John PaulNo ratings yet
- Chapter 3 CISDocument43 pagesChapter 3 CISJohn PaulNo ratings yet
- Tropical Storm Emong' Spotted in Basco, BatanesDocument2 pagesTropical Storm Emong' Spotted in Basco, BatanesJohn PaulNo ratings yet
- Training DesignDocument4 pagesTraining DesignJohn PaulNo ratings yet
- Bracket A (Mosquito) : Team Standing (May 07 - June 12, 2017)Document4 pagesBracket A (Mosquito) : Team Standing (May 07 - June 12, 2017)John PaulNo ratings yet
- Financial Management Part Ii International Managerial FinanceDocument1 pageFinancial Management Part Ii International Managerial FinanceJohn PaulNo ratings yet
- Inter Color Basketball LeagueDocument2 pagesInter Color Basketball LeagueJohn PaulNo ratings yet
- Financial Reporting andDocument58 pagesFinancial Reporting andJohn PaulNo ratings yet
- Tournament Format: 1.elimination: (Bracket) 2.semi Final 3.finalsDocument1 pageTournament Format: 1.elimination: (Bracket) 2.semi Final 3.finalsJohn PaulNo ratings yet
- Inter Color Basketball League1Document3 pagesInter Color Basketball League1John PaulNo ratings yet
- Financial Reporting and - pptx1Document33 pagesFinancial Reporting and - pptx1John PaulNo ratings yet
- Complete Study On Playfair CipherDocument7 pagesComplete Study On Playfair CipherChandan KumarNo ratings yet
- Department of Computer Science CSC-458:Mangement Information System Bahria University BSCS Semester 06 (Fall 2020)Document5 pagesDepartment of Computer Science CSC-458:Mangement Information System Bahria University BSCS Semester 06 (Fall 2020)Haris AftabNo ratings yet
- Honey PotsDocument20 pagesHoney PotsAnkita SinhaNo ratings yet
- HeartDocument27 pagesHearthemavathi1234hemavathiNo ratings yet
- 3466 CloudChecklistDocument6 pages3466 CloudChecklistholamundo123No ratings yet
- HashesDocument3 pagesHashesAira RibadNo ratings yet
- Path To Become A Real Hacker: Deepdotmy OriginalDocument12 pagesPath To Become A Real Hacker: Deepdotmy OriginalRichard KohlsNo ratings yet
- DVB Mitm WebinarDocument53 pagesDVB Mitm WebinarBradMorseNo ratings yet
- Authorization LetterDocument1 pageAuthorization LetternervthcNo ratings yet
- Chapter Two Computer CrimeDocument14 pagesChapter Two Computer Crimeyeshi janexoNo ratings yet
- ch10 KeyManagement Diffie-Hellman ECCDocument26 pagesch10 KeyManagement Diffie-Hellman ECCPranay NandiwadekarNo ratings yet
- An Encryption Protocol For End-To-End Secure Transmission of SMSDocument7 pagesAn Encryption Protocol For End-To-End Secure Transmission of SMSThet Hmue Hay ThiNo ratings yet
- Pki OpensslDocument11 pagesPki OpensslgdeepthiNo ratings yet
- Secure Coding Best Practices Handbook Veracode GuideDocument16 pagesSecure Coding Best Practices Handbook Veracode GuideDomanz Ruler PedroNo ratings yet
- Eliptic Curve Cryptography 2Document7 pagesEliptic Curve Cryptography 2Yashashri NaikNo ratings yet
- Cyber Security For Internet of ThingsDocument9 pagesCyber Security For Internet of ThingsIJRASETPublicationsNo ratings yet
- SOC SIEM Use CasesDocument9 pagesSOC SIEM Use Casesjawwad joeNo ratings yet
- Online Safety, Security, Ethics, and NetiquetteDocument54 pagesOnline Safety, Security, Ethics, and NetiquetteALbert NimasrebNo ratings yet
- NIST SP 800-63b PDFDocument79 pagesNIST SP 800-63b PDFLoctor LoomNo ratings yet
- The Impact of Quantum Computing On Present Cryptography: Vasileios Mavroeidis, Kamer Vishi, Mateusz D. Zych, Audun JøsangDocument10 pagesThe Impact of Quantum Computing On Present Cryptography: Vasileios Mavroeidis, Kamer Vishi, Mateusz D. Zych, Audun JøsangMario AttrovioNo ratings yet
- MALWARE Chap3Document39 pagesMALWARE Chap3Nur SyuhadaNo ratings yet
- POCs For Various Exploits and VulnerabilitiesDocument2 pagesPOCs For Various Exploits and VulnerabilitiesAkhilesh GokhaleNo ratings yet
- Cyber Security Question BankDocument14 pagesCyber Security Question BankKalaiselvi TNo ratings yet
- KAV - CG Mini Project Report FormatDocument5 pagesKAV - CG Mini Project Report FormatAbcdNo ratings yet
- Trustwave Vulnerability Management: Stay Ahead of Network VulnerabilitiesDocument2 pagesTrustwave Vulnerability Management: Stay Ahead of Network VulnerabilitiesEhtasham Ul HaqNo ratings yet
- OWASP 2010 Top 10 Cheat SheetDocument2 pagesOWASP 2010 Top 10 Cheat Sheetobay_osmanNo ratings yet
- Voucher Hasna Hotspot PerjamDocument7 pagesVoucher Hasna Hotspot PerjamYongki suryaNo ratings yet
- 05 Computer SecurityDocument44 pages05 Computer SecurityFarrel KunNo ratings yet