Professional Documents
Culture Documents
Readings MMC6612 Fall 2017
Uploaded by
Mindy McAdamsCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Readings MMC6612 Fall 2017
Uploaded by
Mindy McAdamsCopyright:
Available Formats
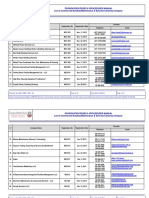
Readings
MMC 6612 New Media and a Democratic Society
Fall 2017
Alhabash, S., & McAlister, A. R. (2015). Redefining virality in less broad strokes: Predicting
viral behavioral intentions from motivations and uses of Facebook and Twitter. New
Media & Society, 17(8), 13171339. doi:10.1177/1461444814523726
Asmolov, G. (2015). Crowdsourcing and the folksonomy of emergency response: The
construction of a mediated subject. Interactions: Studies in Communication & Culture,
6(2), 155178. doi:10.1386/iscc.6.2.155_1
Baird, T. D., & Hartter, J. (2017). Livelihood diversification, mobile phones and information
diversity in Northern Tanzania. Land Use Policy, 67, 460471.
doi:10.1016/j.landusepol.2017.05.031
Barger, W., & Barney, R. D. (2004). Media-citizen reciprocity as a moral mandate. Journal of
Mass Media Ethics, 19(3/4), 191206. doi:10.1080/08900523.2004.9679688
Berger, J., & Milkman, K. (2012). What makes online content viral? Journal of Marketing
Research, 49(2), 192205. doi:10.1509/jmr.10.0353
Brabham, D. C. (2012). Motivations for participation in a crowdsourcing application to
improve public engagement in transit planning. Journal of Applied Communication
Research, 40(3), 307328. doi:10.1080/00909882.2012.693940
Brock, A. (2012). From the blackhand side: Twitter as a cultural conversation. Journal of
Broadcasting & Electronic Media, 56(4), 529549.
doi:10.1080/08838151.2012.732147
Comor, E., & Bean, H. (2012). Americas engagement delusion: Critiquing a public
diplomacy consensus. International Communication Gazette, 74(3), 203220.
doi:10.1177/1748048511432603
Crandall, H., & Cunningham, C. M. (2016). Media ecology and hashtag activism:
#Kaleidoscope. Explorations in Media Ecology, 15(1), 2132.
doi:10.1386/eme.15.1.21_1
Crawford, K. (2016). Can an algorithm be agonistic? Ten scenes from life in calculated
publics. Science, Technology, & Human Values, 41(1), 77-92.
doi:10.1177/0162243915589635
MMC 6612 | Fall 2017 | McAdams 1
Ekstrm, M. (2008). Research on media and democracy: Reflections on changes and
challenges. Nordicom Review, 29(2), 4552. Available:
http://www.nordicom.gu.se/sites/default/files/kapitel-pdf/269_ekstom.pdf
Fuchs, C. (2012). The political economy of privacy on Facebook. Television & New Media,
13(2), 139159. doi:10.1177/1527476411415699
Holt, T. J., Freilich, J. D., & Chermak, S. M. (2017) Internet-based radicalization as
enculturation to violent deviant subcultures. Deviant Behavior, 38(8), 855869.
doi: 10.1080/01639625.2016.1197704
John, N. A. (2014). File sharing and the history of computing: Or, why file sharing is called
file sharing. Critical Studies in Media Communication, 31(3), 198211.
doi:10.1080/15295036.2013.824597
Meyer, R. (2017, August 15). Can the U.S. government seize an anti-Trump website's visitor
logs? The Atlantic. Available:
https://www.theatlantic.com/technology/archive/2017/08/department-of-justice-
dreamhost-trump-visitor-logs-million-ip/536886/
Peretti, J. (2013, April 11). Essay: 13 ways to make something go viral. Available at the
Internet Archive:
http://web.archive.org/web/20170317151545/http://www.facebookstories.com/
stories/1942/essay-13-ways-to-make-something-go-viral
Richards, N. M. (2013). The dangers of surveillance. Harvard Law Review, 126, 19341965.
Available: http://harvardlawreview.org/wp-
content/uploads/pdfs/vol126_richards.pdf and (formatted HTML)
http://www.harvardlawreview.org/issues/126/may13/Symposium_9477.php
Shirky, C. (2011). The political power of social media: Technology, the public sphere, and
political change. Foreign Affairs, 90(1), 2841. Available:
https://www.foreignaffairs.com/articles/2010-12-20/political-power-social-media
Sderberg, J. (2013). Determining social change: The role of technological determinism in
the collective action framing of hackers. New Media & Society, 15(8), 12771293.
doi:10.1177/1461444812470093
Taddicken, M. (2014). The privacy paradox in the social web: The impact of privacy
concerns, individual characteristics, and the perceived social relevance on different
forms of self-disclosure. Journal of Computer-Mediated Communication, 19(2), 248
273. doi:10.1111/jcc4.12052
MMC 6612 | Fall 2017 | McAdams 2
Valenzuela, S., Arriagada, A., & Scherman, A. (2012). The social media basis of youth protest
behavior: The case of Chile. Journal of Communication, 62(2), 299314.
doi:10.1111/j.1460-2466.2012.01635.x
West, A. (2015, June 1). 17 disturbing things Snowden has taught us (so far). Available at
GlobalPost: http://www.globalpost.com/dispatch/news/politics/130703/edward-
snowden-leaks
Wijetunga, D. (2014). The digital divide objectified in the design: Use of the mobile
telephone by underprivileged youth in Sri Lanka. Journal of Computer-Mediated
Communication, 19(3), 712726. doi:10.1111/jcc4.12071
Willson, M. (2016). Algorithms (and the) everyday. Information, Communication & Society
(published online: 20 June 2016). doi:10.1080/1369118X.2016.1200645
Youmans, W. L., & York, J. C. (2012). Social media and the activist toolkit: User agreements,
corporate interests, and the information infrastructure of modern social
movements. Journal of Communication, 62(2), 315329. doi:10.1111/j.1460-
2466.2012.01636.x
MMC 6612 | Fall 2017 | McAdams 3
You might also like
- JOU4930 Artificial Intelligence Syllabus Spring 2021Document9 pagesJOU4930 Artificial Intelligence Syllabus Spring 2021Mindy McAdamsNo ratings yet
- Web Apps Syllabus 2020Document12 pagesWeb Apps Syllabus 2020Mindy McAdamsNo ratings yet
- JOU 4364 Sec 2F03 Advanced Web Apps McAdams s2018Document7 pagesJOU 4364 Sec 2F03 Advanced Web Apps McAdams s2018Mindy McAdamsNo ratings yet
- Advanced Web Apps Syllabus 2017Document7 pagesAdvanced Web Apps Syllabus 2017Mindy McAdamsNo ratings yet
- Web Apps Syllabus 2019Document9 pagesWeb Apps Syllabus 2019Mindy McAdamsNo ratings yet
- Advanced Social Media Syllabus 2017Document6 pagesAdvanced Social Media Syllabus 2017Mindy McAdamsNo ratings yet
- New Media and A Democratic Society Syllabus 2018Document7 pagesNew Media and A Democratic Society Syllabus 2018Mindy McAdamsNo ratings yet
- Advanced Web Apps Syllabus McAdams s2020Document8 pagesAdvanced Web Apps Syllabus McAdams s2020Mindy McAdamsNo ratings yet
- JOU 4364 Advanced Web Apps s2019Document7 pagesJOU 4364 Advanced Web Apps s2019Mindy McAdamsNo ratings yet
- Intro To Web Apps Syllabus 2018Document9 pagesIntro To Web Apps Syllabus 2018Mindy McAdamsNo ratings yet
- Intro To Web Apps Syllabus 2017Document8 pagesIntro To Web Apps Syllabus 2017Mindy McAdamsNo ratings yet
- MMC 6612 Syllabus 2017 v2Document6 pagesMMC 6612 Syllabus 2017 v2Mindy McAdamsNo ratings yet
- Readings MMC6612 Fall 2015Document3 pagesReadings MMC6612 Fall 2015Mindy McAdamsNo ratings yet
- MMC 6612 Syllabus 2016 v.2Document6 pagesMMC 6612 Syllabus 2016 v.2Mindy McAdamsNo ratings yet
- Two Code Courses For Journalism StudentsDocument3 pagesTwo Code Courses For Journalism StudentsMindy McAdamsNo ratings yet
- Transmedia StorytellingDocument7 pagesTransmedia StorytellingMindy McAdamsNo ratings yet
- Social Media Skills Syllabus S2016Document6 pagesSocial Media Skills Syllabus S2016Mindy McAdamsNo ratings yet
- Intro To Web Apps Syllabus 2016Document7 pagesIntro To Web Apps Syllabus 2016Mindy McAdamsNo ratings yet
- Web Apps 2 Syllabus 2016Document6 pagesWeb Apps 2 Syllabus 2016Mindy McAdamsNo ratings yet
- Intro To Web Apps Syllabus 2015Document7 pagesIntro To Web Apps Syllabus 2015Mindy McAdamsNo ratings yet
- Syllabus MMC4341 2015 v2Document7 pagesSyllabus MMC4341 2015 v2Mindy McAdamsNo ratings yet
- MMC 6612 Syllabus 2015Document6 pagesMMC 6612 Syllabus 2015Mindy McAdamsNo ratings yet
- MMC 6612 Syllabus 2014Document5 pagesMMC 6612 Syllabus 2014Mindy McAdamsNo ratings yet
- Readings MMC6612 Fall 2015Document3 pagesReadings MMC6612 Fall 2015Mindy McAdamsNo ratings yet
- Syllabus Social Media MGT 2014Document7 pagesSyllabus Social Media MGT 2014Mindy McAdamsNo ratings yet
- Syllabus JOU6344 Fall 2013Document7 pagesSyllabus JOU6344 Fall 2013Mindy McAdamsNo ratings yet
- Syllabus Social Media Management S2015Document7 pagesSyllabus Social Media Management S2015Mindy McAdamsNo ratings yet
- Readings MMC6612 Fall 2014Document3 pagesReadings MMC6612 Fall 2014Mindy McAdamsNo ratings yet
- Syllabus MMC4341 2014Document6 pagesSyllabus MMC4341 2014Mindy McAdamsNo ratings yet
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (894)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- Megaplex2100 ManualDocument326 pagesMegaplex2100 Manualashraf.rahim139No ratings yet
- RF Basics - Part 1: Demystifying The DBDocument6 pagesRF Basics - Part 1: Demystifying The DBRaúl InfanteNo ratings yet
- 04 SQLQueriesDocument18 pages04 SQLQueriescccc gggg oooNo ratings yet
- Review of Industrial Deployment of Multi-Agent SystemsDocument24 pagesReview of Industrial Deployment of Multi-Agent SystemsVasant RaghavNo ratings yet
- Intel Inside.Document25 pagesIntel Inside.Rashed550% (1)
- Industry LayoutDocument31 pagesIndustry LayoutGiriraj T KulkarniNo ratings yet
- Weekly Home Learning Plans for Empowerment TechnologiesDocument3 pagesWeekly Home Learning Plans for Empowerment TechnologiesCharlon Mamacos100% (9)
- C Pointers Questions PDFDocument30 pagesC Pointers Questions PDFRoshni Khurana0% (2)
- Blockchain Systems and Their Potential Impact On Business ProcessesDocument19 pagesBlockchain Systems and Their Potential Impact On Business ProcessesHussain MoneyNo ratings yet
- Alzheimers Assistant PDFDocument34 pagesAlzheimers Assistant PDFabhirami manikandanNo ratings yet
- Online Book StoreDocument36 pagesOnline Book StoreGourab Dey100% (1)
- Đề Chuyên (Chính Thức) 2017Document10 pagesĐề Chuyên (Chính Thức) 2017Nguyễn Minh ThưNo ratings yet
- Commercial Building Maintenance and External Cleaning CompanyDocument8 pagesCommercial Building Maintenance and External Cleaning Companybisankhe2No ratings yet
- Islamabad Model College For Girls Shalimar F-74Document1 pageIslamabad Model College For Girls Shalimar F-74ADIL DURRANINo ratings yet
- 21 Primavera Tips and ShortcutsDocument30 pages21 Primavera Tips and ShortcutsMarioNo ratings yet
- KPT ShapeShifterDocument28 pagesKPT ShapeShifterLuis TovarNo ratings yet
- Online Dispute Resolution For Smart ContractsDocument24 pagesOnline Dispute Resolution For Smart ContractsRidhima SharmaNo ratings yet
- Soltek SL 65meDocument88 pagesSoltek SL 65meBernardo AntunesNo ratings yet
- SAP Model Company For FinanceDocument1 pageSAP Model Company For FinanceAmar UbheNo ratings yet
- FSP150-50LE Is An Industrial Level of Switching Power Supply - SpecificationDocument1 pageFSP150-50LE Is An Industrial Level of Switching Power Supply - SpecificationJohn HallowsNo ratings yet
- Critical Path MethodDocument6 pagesCritical Path Method6 4 8 3 7 JAYAASRI KNo ratings yet
- Peran Bumdes Dalam Pengelolaan Limbah Kelapa Sawit Di Desa Talang Jerinjing Kecamatan Rengat Barat Kabupaten Indragiri Hulu Provinsi RiauDocument11 pagesPeran Bumdes Dalam Pengelolaan Limbah Kelapa Sawit Di Desa Talang Jerinjing Kecamatan Rengat Barat Kabupaten Indragiri Hulu Provinsi RiauInnaka LestariNo ratings yet
- Java Placement QuestionsDocument23 pagesJava Placement QuestionsVidhya PrakashNo ratings yet
- BA-M-PL 830 G3: Product DatasheetDocument5 pagesBA-M-PL 830 G3: Product DatasheetDavid YazoNo ratings yet
- Nemo Windcatcher: Industry-Leading Drive Test Data Post-Processing and AnalysisDocument2 pagesNemo Windcatcher: Industry-Leading Drive Test Data Post-Processing and AnalysistreejumboNo ratings yet
- LearnTube Project ReportDocument14 pagesLearnTube Project ReportManogya Pratap SinghNo ratings yet
- Contactless Linear Position TransducerDocument5 pagesContactless Linear Position TransducerRONALDECCONANo ratings yet
- Emenuhan Kebutuhan Nutrisi Balita Yang Dirawat Inap Di Rumah SakitDocument7 pagesEmenuhan Kebutuhan Nutrisi Balita Yang Dirawat Inap Di Rumah SakitAnnisa Nur Majidah100% (1)
- Jean Abreu CVDocument3 pagesJean Abreu CVABREUNo ratings yet
- Q4M2 Giving Technical and Operational Def.2.0Document60 pagesQ4M2 Giving Technical and Operational Def.2.0Shadow Gaming YTNo ratings yet