Professional Documents
Culture Documents
08016280
Uploaded by
Sandi RahmadikaCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
08016280
Uploaded by
Sandi RahmadikaCopyright:
Available Formats
Securing User Identity and Transactions
Symbiotically: IoT Meets Blockchain
David W. Kravitz Jason Cooper
David.Kravitz@darkmatter.ae Jason.Cooper@darkmatter.ae
AbstractSwarms of embedded devices provide new chal- Our design of the Permissioned Blockchain takes these
lenges for privacy and security. We propose Permissioned long-term issues into account and boasts fundamental features
Blockchains as an effective way to secure and manage these to handle them gracefully. Flexible, established protocols
systems of systems. A long view of blockchain technology yields
several requirements absent in extant blockchain implementa- provide a pathway from existing workflows and trust models
tions. Our approach to Permissioned Blockchains meets the to a robust and enduring system of record.
fundamental requirements for longevity, agility, and incremental Within the Permissioned Blockchain ecosystem, identity and
adoption. Distributed Identity Management is an inherent feature attribute management is built in for both users and devices.
of our Permissioned Blockchain and provides for resilient user Identities, and their associated attributes, transcend any single
and device identity and attribute management.
device or group of devices.
Keywords-IoT; cryptography; security; privacy; permissioned
blockchain; blockchain II. T RANSACTION L ONGEVITY
A. Asymmetric Key Rotation
I. I NTRODUCTION
Asymmetric cryptography (private/public key pairs) offers
A traditional Unix environment conducts logging and per- many advantages, especially when agreeing on a shared secret
missions enforcement from a multi-user system perspective. over an insecure channel or addressing non-repudiation by
With IoT, we now see a network of devices, where each device distancing the ability to verify from the ability to sign.
has different roles, capabilities, and permissions. The network However, caution is in order when designing a system with
has become the system and the devices the users. Effective these primitives.
management of both user and device identities and attributes Private key management is essential. In most designs, the
can be realized with the Distributed Identity Management that private keys become the trust anchor of the system, and the
our Permissioned Blockchain provides. proof of identity. This makes the private keys the prime target
Blockchain is ultimately a distributed, immutable log of of attackers. The longer a private key is held, the higher is
events. When harnessed properly, it greatly facilitates recon- the probability of compromise. A multi-decade system design
ciliation of event history among multiple entities. Blockchain must account for keys in use today being compromised in
enables IoT devices to perform transactions, and to be tracked the future. A strong system will withstand future revelation of
relative to time and location. The major missing link of the private keys.
well-known Bitcoin blockchain is the element of permis- Therefore, our design prioritizes easy rotation of asymmetric
sioning, i.e., a privacy-preserving, traffic-analysis- resistant keys. This degree of freedom gives the protocol the ability
methodology that leverages external trust relationships so as to adopt resilient primitives that do not exist today. Rotating
to establish an auditable identity- and attributes- management signature keys causes an adversary to have to re-attack in order
authorization framework. IoT devices suitably provisioned to be able to continue to sign, provided that the underlying
with identity management trust anchors can securely and signature scheme remains robust. Similarly, rotating key agree-
efficiently transact over permissioned blockchains. ment keys causes an adversary to have to re-attack in order to
Blockchain technology is attempting to revolutionize an be able to recover the plaintext of future transactions.
industry in existence for centuries. The integrity of a trans-
action ledger must remain intact for a decade or more. B. Device Group Membership
When contemplating contractual agreements, integrity must be When discussing proper key management, there are two
maintained for many decades. In other words, the transactions basic principles that have been developed over several decades.
will outlive the cryptographic primitives and devices that they First, assuming a suitable source of entropy, keys should be
were originally secured with. End users will need to vouch for created on the device they are being used for. Second, keys
transactions long after the original device has been removed should never be moved from device to device.
from service. Asymmetric keys may be compromised years If Alice creates a transaction today, with her Android device,
after theyve committed a transaction. she needs to be able to prove that its hers later.
978-1-5090-5873-0/17/$31.00
2017
c IEEE
978-1-5090-5249-3/17/$31.00 2017 IEEE
978-1-5090-5873-0/17/$31.00
Alice has an implicit group, Alices Devices, to which all To do this, we borrow a concept from the distributed version
of her devices belong. Now, when she creates her transaction, control system, git. In git, each commit contains a reference,
we record that it was done by one of Alices Devices. As her by hash, to the previous parent commit. This is very similar
keys are rotated, and devices enter and leave her group, she to how blockchains function. A commit can also refer to more
can still prove, with any of her other devices, that she created than one parent, and conversely, more than one commit can
that transaction. As soon as one of her keys is rotated out, or a refer to a given parent commit. These features enable us to
device is disposed of, we record the event on the blockchain. tie together related transactions.
For embedded systems, with little storage space, the pa-
C. Hash Function Agility rameters may be tweaked. These tiny systems may only need
In the previous sections, we reduced the importance of any the past 24 hours worth of transactions, and only those
single private key by developing a robust key rotation policy, transactions directly pertaining to its job. Multiple references
and the concept of group membership. If the asymmetric facilitate this use case; its akin to only checking out a single
keys are no longer our cryptographic trust anchor, what is? branch of a git source code repository. If more blockchain
The answer resides in the hash functions used to hash each history is needed, the device can request the older data from
transaction and to relate one transaction to another in the its peers.
blockchain. We would like to be able to take advantage of III. OVERVIEW OF OUR I DENTITY AND ATTRIBUTE
the critical role that hash function use plays in formulating a M ANAGEMENT A PPROACH
blockchain.
Attributes can include identities, identifiers, entitlements,
We must protect the blockchain via hash function agility.
etc. User or device Identity and (organizational/device man-
This means that we can start off with one hash function,
ufacturer) Affiliation can be considered special cases of at-
say SHA-2, for hashing transactions. Then, later on, we can
tributes in that these are embedded into relatively long-
compute parallel hashes of existing transactions. Once the
term Enrollment Certificates, while these as well as dynamic
parallel hashes, say SHA-3, are accepted by the community,
attributes are incorporated into Transaction Certificates. A
the old hash algorithm can be deprecated.
user or device may possess multiple Enrollment Certificates
A first- or second- pre-image or collision- attack may exist
concurrently. Enrollment Certificates are used only behind the
against SHA-2 one day, but the parallel hash mechanism gives
scenes to prove provenance of attributes, while Transaction
us the ability to detect such attacks. Even if a signature
Certificates are used within blockchain transactions. These
scheme used for past transactions becomes vulnerable, signing
Transaction Certificates replace the raw/uncertified public keys
a different message as an attempted replacement will result in a
used in Bitcoin addresses.
different hash value under the parallel hash regime. Similarly,
Our protocols are designed to gain the benefits of inheriting
even if a key agreement scheme used for past transactions
trust relationships that are established off-chain as well as
becomes vulnerable, confidentiality of these past transactions
leveraging trust relationships that develop through the history
can be maintained if the current signature scheme is robust
of blockchain transactions. Reciprocally, trust that is built up
and signing by an authorized requester is required. Ciphertext
via the blockchain can be utilized for off-chain services.
stored off-chain and referenced on the blockchain by its hash
Using standardized X.509 PKI and SAML/OAuth/OpenID
can only be requested by an authorized requestor in the current
federated identity management, the system provides trusted
system. This also aids in keeping the blockchain within a
assertions of Identities, and other attributes such as Affiliation,
reasonable size limit, and is consistent with hashing state
user or device qualifications/authorized functionalities, re-
into blocks of transactions, where state results from execution
source entitlements, reputation metrics, etc. Unlike traditional
of transaction chaincode or acceptance of inputs for external
systems, each of these assertions is securely translated into
execution.
unique proofs-of-possession that are embedded into batches of
issued Transaction Certificates. This embedding uses efficient
D. Transaction Expiration
symmetric cryptography in order to hide the information from
How quickly can we reach old transactions relevant to unauthorized access, while enabling the user or device that
new ones? How will resource-constrained embedded devices owns a Transaction Certificate to privately prove possession
interact with the blockchain? of the attribute to intended parties on a selective release basis.
The key to answering these questions is to have a clearly The audit system is further refined, so that appropriate mea-
defined transaction expiration policy. Many government and sures can be applied to limit an authorized Auditors access
regulatory bodies require records to be kept for seven years. down to individual users or devices and/or to circumscribed
Following that example, transactions that are a) older than transaction time periods. Such auditability is designed to be
seven years, and b) are only referred to by transactions older revocable. The issuance of Transaction Certificates is also
than seven years are eligible for expiration. Transactions that auditable, so as to provably confine the Transaction Certificate-
may be older than seven years, perhaps a mortgage, but are specific subject public keys to those that are derived via the
referred to by younger transactions executing the terms of the hidden cryptographic expansion function from a long-term
contract would not be eligible for deletion. subject public key of a legitimate Enrollment Certificate. This
inability to get an arbitrary subject public key included within and references the devices factory-provisioned certificate.
a Transaction Certificate also has ramifications regarding en- Such attribute certificates are used in conjunction with the
abling efficient but secure combining of private or public factory-provisioned device certificate to prove ownership of
keys that improves transaction processing performance. This these attributes to an AA. Standard means based on established
is accomplished without enduring the expense to clients or roots of trust are used for this, such as the device using a
servers of processing individual proofs of possession of subject unique private key with which it had been provisioned (along
private keys in order to safely produce batches of Transaction with certificate on corresponding subject public key) by the
Certificates. device manufacturer in order to sign responses that incorporate
Endorsements and other data relevant to the attributes and AA-issued challenges.
reputation (relative to such attributes) of users or devices that The ACA verifies and collects such AA-issued assertions
are exchanged within transactions can be processed/aggregated that reflect the ACAs challenges into its database encrypted
and fed back into the system so that future Transaction for access only by a Primary Transaction Certificate Authority
Certificates reflect such data within the embedded proofs-of- (TCA). The Primary TCA (which may be split by using
possession of attributes. threshold- or multi- signatures), in turn, generates Template
The core principles outlined above form the basis of Transaction Certificates that incorporate sets of uniquely en-
handling Know Your Customer/Anti- Money-Laundering crypted attributes, and the means for authorized Subordinate
(KYC/AML) for financial services transactions and Know TCAs to generate batches of derivative Transaction Certificates
Your Machine (KYM) for IoT devices [1], without sacrificing (TCerts) that each rekey these encrypted attributes (by using
performance or throughput. The methodology was designed TCert- and attribute- specific attribute encryption keys) and
to also be extensible for use in M2M and other IoT trans- include a TCert-specific subject public key. The keying of
actions that involve severely- resource-constrained devices. the encrypted attributes stems from use of a hierarchical
Transaction Certificates and the cryptographic protocols are key derivation tree, where each Subordinate TCA is granted
structured so as to avoid the need for long-term storage access to node key(s) of that tree in accordance with the
of per-certificate keys, and to minimize client computation, domain of its jurisdiction. The construction of the TCerts
cross-server synchronization, and off-chain transaction setup also involves use of a Client-specific (key-derivation) key that
communications. Our further exploration into the IoT domain is provided alongside the Template Transaction Certificate,
entails extending the capabilities to handle dynamic and static encrypted based on the tree so that it is accessible by the
groups of stationary and mobile devices so as to corroborate Subordinate TCA. The per-TCert subject public keys are
legitimate assertions (such as those pertaining to location or generated using an expansion function of the user/device
proximity) made by each, and to aid in timely detection of long-term public key that is extracted from an Enrollment
anomalous device and/or user behavior for the purpose of Certificate that associates that key with the user/device steady-
effective containment of rogue devices and/or users via revo- state attributes, such as userID/deviceID and user Affiliation
cation of Transaction Certificates or Enrollment Certificates. (or device manufacturer/device type). Batches of TCerts are
Applications include improved identity fraud management and delivered encrypted for use only by the owner Client (to assure
tuning of authorizations to more securely permission high- preservation of unlinkability against traffic analysis), along
value transactions, taking advantage of the immutably ordered with per-TCert keys (also encrypted) that enable regeneration
and time-stamped ledger to aid in correlation of both on- and by the Client of the TCert-specific attribute encryption keys
off- chain transaction activity. (since the Client does not have access to node keys of the tree).
Our solution is characterized by a number of advantageous The enrollment private key known only to the Client plays a
properties, as outlined in the remainder of this section. pivotal role in cryptographically binding the specific Client to
In response to a challenge by a system Attribute Certificate its TCerts. Only that Client can take delivery and derive the
Authority (ACA), a user or device Client acquires fresh per-TCert private keys required to sign blockchain transactions
assertions from one or more Analytics Processors (APs) that that are each accompanied by a one-time-use TCert. Only the
encapsulate the current status of the user or device with regard enrollment private key and the Client-specific key need be
to its cumulative ratings relative to one or more attributes available long-term to the Client. The per-TCert key can be
(as derived by the AP from individual peer ratings on the discarded by the Client once that TCert is used in a transaction.
blockchain it is privy to). The hierarchical key derivation tree is used by TCAs, APs, and
The attributes themselves are asserted by one or more Auditors.
standard Attribute Authorities (AA), where, as prerequisite, We enable transaction continuity via group dynamics: A
the Client provides such an AA with proofs-of-possession device can incorporate into a blockchain transaction the means
of the attribute(s) for which assertions are being requested. (using standard key agreement) of privately targeting data/keys
The Client also provides such AA with a challenge acquired to itself and other devices in the group at the time (i.e.,
from an ACA. Independently of the blockchain system, a reflexive case), as well as to a transaction Validator group
device that is securely over-the-air-provisioned with upgraded and/or an appropriate Auditor (dependent upon policy) and/or
software/firmware may receive a standard (key-less) attribute intended recipient devices that are not in the group at the time.
certificate [2] that expresses the devices resultant functionality A non-targeted device that later joins the group may be able to
gain access to such data/keys by proving its group membership TCertOwnerEncryptionKey256bit
(as an attribute) to a member of such Validator group. Whether = HMAC(TCertOwnerRootKey, 00 100 )
or not such device is entitled to gain access to private data of
(256bit truncation) (4)
previous transactions, it may be able to claim association to
such transactions within a follow-on transaction by selectively
releasing its current membership in the group (by proving TCertOwnerExpansionKey384bit
ownership of that attribute in a purposely non-transferable way = HMAC(TCertOwnerRootKey, 00 200 ) (5)
by privately releasing the associated (Transaction Certificate-
specific) attribute encryption key within the follow-on transac- TCertOwnerRootKey is the Client-specific (key-derivation)
tion that is digitally signed using the Transaction Certificate- key.
unique private key that corresponds to the subject public key of EncryptedTCertIndex
a freshly used Transaction Certificate). Devices can vote other
= AES CBC Encrypt(TCertOwnerEncryptionKey,
devices into or out of groups to which they belong (similarly to
the way ratings are handled). An example application is where TCertIndex || ConstantPad )
a device user proves their current location relative to location (6)
of that user at times of previous correlated transactions e.g.,
in order to establish patterns for their identity profile or to is included within the TCert, where the ConstantPad provides
prove their inability to have feasibly been involved in certain a check of ownership by the User and/or by an Auditor
other on- or off- chain location-dependent transactions (such that is assigned access to TCertOwnerEncryptionKey or the
as card-present credit/debit transactions). This can serve as predecessor TCertOwnerRootKey on an individual User basis.
evidence of an impostor using a device associated with that TCertSpecificExpansionValue384bit
user via group membership.
= (HMAC(TCertOwnerExpansionKey, TCertIndex) ||
IV. C RYPTOGRAPHIC C ONSTRUCTS HMAC(TCertOwnerExpansionKey,
A. Authorization Key Management TCertIndex + 1) ) (mod n)
We now provide a description of major elements of the
(7)
cryptographic constructs in some detail, beginning with an
overview of authorization key management. where n per FIPS186-4 [5] relative to ECDSA, and TCertIndex
is incremented by 2 for subsequent TCert in the batch. The
TCA_CARootKey double HMAC is introduced here to reduce exploitable bias
Primary TCA_ID that could otherwise jeopardize unlinkability. This issue is
(Primary) TCA_RootKey raised in [3], which specifies a PoC for the V2V collision-
avoidance system that we started with when considering how
KeyVersion
to achieve unlinkability within a resource-constrained envi-
TCertsRoot
ronment. The PoC is based on IEEE 1609.2-2016 Standard
EnrollmentPublicKey for Wireless Access in Vehicular Environments Security Ser-
TCertOwnerExpansionKey TCertOwnerRootKey TCertOwnerEncryptionKey vices for Applications and Management Messages, and Crash
TCertIndex TCertIndex || ConstantPad Avoidance Metrics Partners (CAMP) LLC Vehicle Safety
TCertSpecificExpansionValue EncryptedTCertIndex
Communications 5 (VSC5).
EnrollmentPublicKey
B. Key expansion: TCert public key and private key derivation
TCertPublicKey
(with P-384)
Note that (unlike techniques such as Identity Mixer and U-
Prove [4]) the public key expansion is initiated by a TCA
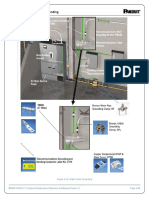
Fig. 1. Represents how authorization is achieved through the generation and
use of TCerts rather than by the Client. Also, these key expansion func-
tions are, by construction, independent of attributes (unlike
More specifically: the generation of public keys stemming from identitybased
TCA RootKey384bit encryption and attribute-based encryption techniques). These
properties give us the capabilities of (1) defining a common
= HMAC(TCA CARootKey, TCA ID) (1) structure for the two kinds of unlinkable public-key bearing
certificates that we require to efficiently manage read- and
TCertsRoot384bit
write- authorizations for use by resource-constrained devices,
= HMAC(TCA RootKey, 00 100 || KeyVersion) (2) namely signature TCerts that are delivered directly to their
owner, and key agreement TCerts that can be safely and
TCertOwnerRootKey384bit usefully be delivered to requesting entities other than their
= HMAC(TCertsRoot, EnrollmentPublicKey) (3) owner, (2) enabling authorized Auditors to manage risk, gauge
compliance, and fulfill regulatory requirements, and (3) en- As an illustrative example of the use of the hierarchical key
abling analytics processing by APs that results in refining derivation tree:
attributes by adding qualifiers such as earned ratings, and
PreK Root = Primary TCAs Root of tree (11)
that aggregates individual device votes in order to determine
whether or not to endow devices with additional attributes such PreK ABC : Available to Auditors/sub-TCAs
as device group membership. with jurisdiction (12)
(Automobile, Banking, Construction)
TCertPublicKey
PreK B = HMAC(PreK ABC, 00 Banking00 ) (13)
= EnrollmentPublicKey
PreK BofZ = HMAC(PreK B, 00 BofZ00 ) : (14)
+ TCertSpecificExpansionValue G (8)
Bank of Z, (Banking)
G per FIPS 186-4 [5] relative to ECDSA.
PreK [BofZ, xyz] = HMAC(PreK BofZ,
TCertPrivateKey
TCertID = 00 xyz00 ) (15)
= (EnrollmentPrivateKey
K TCert = PreK [BofZ, xyz] (16)
+ TCertSpecificExpansionValue) (mod n) (9)
where K TCert provided with TCert that has TCertID =
00
n per [5] relative to ECDSA. Note that the TCertOwner need xyz00 to owner of that TCert, who is required to own ECert
not retain TCertPrivateKey, since it is recomputable from the with Affiliation = Bank of Z.
TCert.
D. Basic Fields of a TCert
C. Attribute Management
Now we move on to being able to manage attributes TCertID (probabilistically unique per TCert) (17)
within TCerts in a way that is compatible with (1) generation
by Subordinate TCAs, with (2) access control relative to Encrypted Attribute [i]
authorizing Auditors and APs, and with (3) selective and
= AES CBC Encrypt(Attribute EncryptionKey [i] ,
purposely non-transferable release of proofs of ownership by
Clients/TCertOwners: Attribute [i]) (18)
TCA_CARootKey
Authenticated Attribute [i]
Primary = HMAC(Attribute HMACKey [i] ,
TCA_ID
Attribute [i]) (19)
(Primary) TCA_RootKey
KeyVersion TCert Public Key (for signature verify) (20)
PreK_Root
[As root of Audit/Subordinate TCA Tree]
Encrypted TCertIndex
K_TCert
= AES CBC Encrypt(TCertOwnerEncryptionKey,
[TCert-Specific] TCertIndex || Constant Pad) (21)
i
Attribute_EncryptionKey[i] KeyVersion (for use by Auditors and TCertOwner) (22)
E. Extending the Key Agreement Structure to Prevent Circum-
Attribute_HMACKey[i]
vention of Audit
Here a Validator group can enforce that a transaction creator
Fig. 2. Audit/Subordinate TCA key management has granted policy-stipulated Auditor access. This can be
accomplished via verifiable key agreement: The basic con-
struct is such that a validator applies a transaction private
Let
key provided securely to the validator by the transaction
PreK Root = HMAC(TCA RootKey, creator. The validator verifies that this transaction private key
00 00
2 || KeyVersion) (10) corresponds to a transaction public key that is included in
the clear within the transaction creator- signed transaction.
Attribute EncryptionKey[i] is derived from K TCert, e.g., as The validator also verifies that included within the signed
HMAC(K TCert, i). transaction is ciphertext that, when decrypted, yields the data
Derive Attribute HMACKey[i] deterministically from en- required to be transferred to an Auditor per the applicable
cryption key, e.g. as HMAC(Attribute EncryptionKey[i], 1). policy.
F. Four Kinds of TCerts that can be Requested from a Subor- where the ciphertexts are:
dinate TCA by a User U / Device D
V Ciphertext = AES Encrypt(Key V,
User Us / Device Ds own signature TCerts
(Attribute Encryption Key(s) of Txn Creator ||
User Us /Device Ds own key agreement TCerts (for
reflexive case or to distribute to others for future trans- Asset || AccountID of Asset Transferee) ) (25)
actions that involve the user U / Device D)
Auditor/AP key agreement TCerts AT Ciphertext = AES Encrypt(Key AT,
Key agreement TCerts of other users/devices (Asset || AccountID of Asset Transferee) ) (26)
These other users/devices may be identified within the
request by userID. Alternatively, these are identified within TC Ciphertext = AES Encrypt(Key TC,
the request by a dynamic attribute: TxnPrivateKey) (27)
E.g., through an in-band transaction or off-chain communi-
cation, user U ascertains an account number of another user State is checked as indicating that accountID of Transaction
(and may or may not know that other users userID). Creator does indeed show Asset is available (such as available
funds if Asset is a dollar amount). Upon successful valida-
V. A SSET T RANSFER
tion and consensus, state is updated to show the Asset has
We give an example below of an asset transfer use case been transferred from accountID of Transaction Creator to
applicable to financial services, since smart cities involve accountID of Asset Transferee.
financial and governmental services as well as cyber-physical
systems. VI. C ONCLUSION
A user draws an asset from an account in order to transfer The use of identity (albeit in weak form such as username
the asset to another account (that belongs to that user or and password) and devices (e.g., one-time codes in SMS
another user). messages for multi-factor authentication) to secure transactions
Let Key V denote an AES key derived from a one-pass is a common practice. We have shown in some detail how
elliptic curve Diffie-Hellman (ECDH) operation, where the this can be made substantially more secure through the use
static key pair (VPrivKey, VPubKey) is associated with a of permissioned blockchain technology. Furthermore, we have
Validator group and the ephemeral key pair for the transaction also demonstrated how to apply our techniques for the other
(TxnPrivKey, TxnPubKey) is generated by the transaction direction, i.e., to improve the robustness of user identity
creator. Similarly for Key TC and Key AT, for Transaction against fraud by privately referencing the users blockchain
Creator and Asset Transferee. transactions. Another area we explored is securing swarms
VPubKey (or the identifier of the Validator group or iden- of devices that fulfill ad hoc or regularly scheduled tasks,
tifier of a certificate that includes VPubKey) may be included via a privacy-preserving rating system for early detection
within the Template Transaction Certificate by Primary TCA of anomalous device behavior that warrants potential device
(and hence in the derivative TCerts generated by a Subor- revocation. The work in this paper presents and extends (with
dinate TCA) if Primary TCA knows which Validator group an emphasis on IoT) that which the first author briefed to
to designate based on the particular collection of Attributes the Linux Foundation Hyperledger Project community [6]; [7]
from which the Template Transaction Certificate generation and at Blockchain Protocol Analysis and Security Engineering
process draws. This field may be included within TCerts as 2017 [8].
an encrypted attribute, in order to not expose this information.
R EFERENCES
This measure could be used to enforce/audit compliance by
the user as Transaction Creator (or to detect non-compliance). [1] Pindar Wong, keynote abstract,
http://wfiot2016.ieee-wf-iot.org/program/
[2] https://tools.ietf.org/html/rfc5755
[3] http://www.its.dot.gov/pilots/pdf/
BasicTransaction SCMS_POC_EE_Requirements.pdf
= (Fresh TCert of Transaction Creator || [4] http://neven.org/papers/ieeecreds.html
[5] http://nvlpubs.nist.gov/nistpubs/FIPS/
Transaction Signature over Text1 || NIST.FIPS.186-4.pdf
[6] https://github.com/hyperledger/hyperledger/
Text) (23) blob/master/2016-06-23_Hyperledger Membership
Services
for: Presentation.pdf
[7] https://github.com/hyperledger/hyperledger/blob/master/
Text 2016-07-13_MembershipServicesInHyperledgerFabric_Part2.pdf
= (TxnPublicKey || KeyAgreement TCert AT || [8] Permissioning Your Blockchain: How to Overlay Hyperledger Fabric
with a Fully Workable System Tapestry:
KeyAgreement TCert TC || V Ciphertext || https://cyber.stanford.edu/blockchainconf
AT Ciphertext || TC Ciphertext ) (24)
1 Generated using Signature TCert Private Key
You might also like
- Introduction To Blockchain: Learn In Depth About The Fundamentals Of Blockchain, Blockchain Architecture And Various Blockchain Use CasesFrom EverandIntroduction To Blockchain: Learn In Depth About The Fundamentals Of Blockchain, Blockchain Architecture And Various Blockchain Use CasesNo ratings yet
- Understanding Blockchain: Tips, Recommendations, and Strategies for SuccessFrom EverandUnderstanding Blockchain: Tips, Recommendations, and Strategies for SuccessNo ratings yet
- Blockchain The India Strategy Part I 2Document5 pagesBlockchain The India Strategy Part I 2Sayyeda SumaiyahNo ratings yet
- Assignment 1Document9 pagesAssignment 1Sarfirey GamersNo ratings yet
- Using The Blockchain For Key Management in The Internet of ThingsDocument4 pagesUsing The Blockchain For Key Management in The Internet of ThingsMircea PetrescuNo ratings yet
- Chapter IiDocument16 pagesChapter IigenelyndelatorredelfinNo ratings yet
- Unlock The Power of Blockchain - DigitalOceanDocument14 pagesUnlock The Power of Blockchain - DigitalOceanMihai TiberiuNo ratings yet
- Cypherium Whitepaper v1.0Document19 pagesCypherium Whitepaper v1.0WaleedNo ratings yet
- 3 Internet of ThingsDocument5 pages3 Internet of ThingsmittleNo ratings yet
- Unit I BCTDocument69 pagesUnit I BCTAkshay HariNo ratings yet
- Cypherium: A Scalable and Permissionless Smart Contract PlatformDocument19 pagesCypherium: A Scalable and Permissionless Smart Contract PlatformChakravartthi UrsNo ratings yet
- SeminarDocument46 pagesSeminarSubham Kumar SahooNo ratings yet
- Blockchain DictionaryDocument2 pagesBlockchain DictionaryVijay DinanathNo ratings yet
- Block ChainDocument13 pagesBlock ChainRaudah YamnaNo ratings yet
- Event Management Ticket Booking Using BlockChainDocument5 pagesEvent Management Ticket Booking Using BlockChainRitesh GuptaNo ratings yet
- Blockchain Glossary PDFDocument2 pagesBlockchain Glossary PDFDiego RomaNo ratings yet
- BLOCKCHAINDocument19 pagesBLOCKCHAINArchisman SahaNo ratings yet
- Uport Whitepaper DRAFT20170221Document16 pagesUport Whitepaper DRAFT20170221matkoshyNo ratings yet
- BCL Assignment 2Document6 pagesBCL Assignment 2amit gujarNo ratings yet
- The Blockchain As Decentralized Security FrameworkDocument4 pagesThe Blockchain As Decentralized Security FrameworkIrwan AlfiansyahNo ratings yet
- Chapter 4 STDocument40 pagesChapter 4 STAschalew AyeleNo ratings yet
- 5 Basic Components of A Blockchain NetworkDocument5 pages5 Basic Components of A Blockchain NetworkAkshay HariNo ratings yet
- Block Chain PowerPoint TemplatesDocument15 pagesBlock Chain PowerPoint TemplatesKim Clint DuhaylungsodNo ratings yet
- Block ChainDocument9 pagesBlock ChainNurul Rofifah MNo ratings yet
- How To Get Into BlockchainDocument4 pagesHow To Get Into Blockchainsend.to.fauzanNo ratings yet
- Tata Communications Blockchain BriefingDocument8 pagesTata Communications Blockchain BriefingSivasankaran KannanNo ratings yet
- Blockchain Technologies: The Foreseeable Impact On Society and IndustryDocument11 pagesBlockchain Technologies: The Foreseeable Impact On Society and Industrymanikandan.hNo ratings yet
- Blockchain Testanment Will PaperDocument5 pagesBlockchain Testanment Will Papermraza2406No ratings yet
- Blockchain: The Distributed LedgerDocument5 pagesBlockchain: The Distributed LedgerKSHITIJ PANDEYNo ratings yet
- Smart Contract: Attacks and Protections: Sarwar Sayeed, Hector Marco-Gisbert, Tom CairaDocument13 pagesSmart Contract: Attacks and Protections: Sarwar Sayeed, Hector Marco-Gisbert, Tom CairascribdseNo ratings yet
- BC Unit I, Ii, IiiDocument22 pagesBC Unit I, Ii, Iiiss9933575No ratings yet
- Mahnoor Qaisar - #1056 - Computer Application in Education Assignment-2Document7 pagesMahnoor Qaisar - #1056 - Computer Application in Education Assignment-2HaseeB MalikNo ratings yet
- TSP Csse 15547Document9 pagesTSP Csse 15547ken.nguyen.1006No ratings yet
- Demystifying Blockchain Codex2199 PDFDocument12 pagesDemystifying Blockchain Codex2199 PDFlordzangNo ratings yet
- Blockchain November 06, 2022Document2 pagesBlockchain November 06, 2022aiza eroyNo ratings yet
- INT Web3.0 Capabilities 2023 V1Document19 pagesINT Web3.0 Capabilities 2023 V1Aritra ChatterjeeNo ratings yet
- Blockchain Unit 1Document13 pagesBlockchain Unit 1sharmanikki8381No ratings yet
- Block Chain Technology Unit-IDocument20 pagesBlock Chain Technology Unit-IsriniefsNo ratings yet
- Blockchain and Its Main ApplicabilityDocument17 pagesBlockchain and Its Main ApplicabilityBrigs MastermindNo ratings yet
- Types of Blockchain: Public BlockchainsDocument3 pagesTypes of Blockchain: Public Blockchainsnaveenallapur2001No ratings yet
- Blockchain RAPORDocument4 pagesBlockchain RAPORAylin ErdoğanNo ratings yet
- Securing Virtual Machine Orchestration With Blockchains: Nikola Bozic, Guy Pujolle, Stefano SecciDocument8 pagesSecuring Virtual Machine Orchestration With Blockchains: Nikola Bozic, Guy Pujolle, Stefano SecciRayhaneh JadidfardNo ratings yet
- 10 1109@iccubea47591 2019 9129289Document6 pages10 1109@iccubea47591 2019 912928965-Vishwakarma DurgeshNo ratings yet
- Do You Need A Blockchain?: Karl Wüst Arthur GervaisDocument10 pagesDo You Need A Blockchain?: Karl Wüst Arthur GervaisKinshuk ShekharNo ratings yet
- About Blockchain TechnologyDocument8 pagesAbout Blockchain TechnologyMadalina AlexandraNo ratings yet
- Blockchain Technology: Is It Building A Brighter Future?: by Anurag Bana, Jane Ellis, Christian DecleDocument14 pagesBlockchain Technology: Is It Building A Brighter Future?: by Anurag Bana, Jane Ellis, Christian DecleAbhishek Kumar ShahNo ratings yet
- MB NotesDocument19 pagesMB NotesBhavik UpadhyayNo ratings yet
- Future With Technology (FinalDocument27 pagesFuture With Technology (FinalkaranNo ratings yet
- Blockchain:A New Era of Technology: Kavya B V and Sachin C LDocument4 pagesBlockchain:A New Era of Technology: Kavya B V and Sachin C LSanthosh C lNo ratings yet
- Unit5 CAT-IIDocument37 pagesUnit5 CAT-IICodeYt WithNo ratings yet
- Blockchain Consensus Protocols in The Wild: Christian Cachin Marko Vukoli C IBM Research - Zurich 2017-07-07Document24 pagesBlockchain Consensus Protocols in The Wild: Christian Cachin Marko Vukoli C IBM Research - Zurich 2017-07-07Mohamed Hechmi JERIDINo ratings yet
- Use of Blockchain Technology: By-Kunal Khandelwal Vikas Saini Arshdeep Rajnish KumarDocument8 pagesUse of Blockchain Technology: By-Kunal Khandelwal Vikas Saini Arshdeep Rajnish KumarRaj NishNo ratings yet
- Cryptocurrency: 51% AttackDocument6 pagesCryptocurrency: 51% AttackRakeshNo ratings yet
- Block Chain CourseDocument6 pagesBlock Chain CoursePrince StefanNo ratings yet
- Blockchainbyamanthakur 220325164814Document22 pagesBlockchainbyamanthakur 220325164814salmanNo ratings yet
- Blockchain Ebook PDFDocument13 pagesBlockchain Ebook PDFBillNo ratings yet
- Hyperledger PDFDocument4 pagesHyperledger PDFvsrajkumarNo ratings yet
- Technology Affecting Business and Finance: E1 Chapter 5Document6 pagesTechnology Affecting Business and Finance: E1 Chapter 5kags tobsNo ratings yet
- Block Chain Unit 2Document19 pagesBlock Chain Unit 2pilli maheshchandraNo ratings yet
- Security Blockchain: Made SimpleDocument7 pagesSecurity Blockchain: Made SimpleSNo ratings yet
- Scanned by CamscannerDocument6 pagesScanned by CamscannerSandi RahmadikaNo ratings yet
- Stress Ringan Sedang BeratDocument15 pagesStress Ringan Sedang BeratSandi RahmadikaNo ratings yet
- Soldier FortuneDocument2 pagesSoldier FortuneSandi RahmadikaNo ratings yet
- Code Vision AVRDocument3 pagesCode Vision AVRMohammed AsharNo ratings yet
- M3LM UlDocument5 pagesM3LM UlSandi RahmadikaNo ratings yet
- Security System For DNS Using CryptographyDocument7 pagesSecurity System For DNS Using CryptographyAbhinavSinghNo ratings yet
- Government of Andhra Pradesh, Grama/Ward Sachivalayam Recruitment-2019 Hall TicketDocument2 pagesGovernment of Andhra Pradesh, Grama/Ward Sachivalayam Recruitment-2019 Hall TicketAnilNo ratings yet
- Reference Architecture Design Guide Part 3,0Document100 pagesReference Architecture Design Guide Part 3,0gurkan arif yalcinkayaNo ratings yet
- Discrete Mathematics AssignmentDocument12 pagesDiscrete Mathematics AssignmentLalitSisodiaNo ratings yet
- Power System Protection: Dr. Ibrahim El-AminDocument53 pagesPower System Protection: Dr. Ibrahim El-AminLegalli AmcaNo ratings yet
- Building Facilities and AdministrationDocument12 pagesBuilding Facilities and AdministrationJoseph Alcoran0% (1)
- Online Application Monitoring ToolDocument43 pagesOnline Application Monitoring ToolMd Shaukat AliNo ratings yet
- Instruction Manual: Lcd-6Oo Security StationDocument10 pagesInstruction Manual: Lcd-6Oo Security StationLeonardusNo ratings yet
- The Accidental BillionairesDocument6 pagesThe Accidental Billionairessaifeez18100% (1)
- Quality Assurance Audit Area: Audit Plan Product (Aircraft) Audit Y12E, 9N-AKU Audit ObjectivesDocument4 pagesQuality Assurance Audit Area: Audit Plan Product (Aircraft) Audit Y12E, 9N-AKU Audit ObjectivesKisna BhurtelNo ratings yet
- Documentation For LogisticsDocument31 pagesDocumentation For LogisticsOsmania MbaNo ratings yet
- 5 Chap Ai PDFDocument18 pages5 Chap Ai PDFTrupti GunajNo ratings yet
- OSASDocument2 pagesOSASZed DeguzmanNo ratings yet
- Raspberry Pi Based Smart Doorbell System With Advanced Encryption SchemeDocument5 pagesRaspberry Pi Based Smart Doorbell System With Advanced Encryption SchemeFaris MuthoaNo ratings yet
- Relativity - Processing User Guide - 9.6 PDFDocument280 pagesRelativity - Processing User Guide - 9.6 PDFJames Stallins Jr.No ratings yet
- Buffalo Link Station Quad LS-QL-R5 User ManualDocument96 pagesBuffalo Link Station Quad LS-QL-R5 User Manualbernardng5591No ratings yet
- Match MakingDocument31 pagesMatch MakingDesmond MccoyNo ratings yet
- Top Links February 2019Document132 pagesTop Links February 2019Andrew Richard Thompson0% (1)
- Verifone vx510Document35 pagesVerifone vx510nemesys1968No ratings yet
- Honeypots Seminar ReportDocument39 pagesHoneypots Seminar ReportKiran Rekhi80% (5)
- NIK Prevents Dual IDentityDocument2 pagesNIK Prevents Dual IDentitytandem82No ratings yet
- Project TitleDocument12 pagesProject Titleselvaasaral9629No ratings yet
- Magnetom C!: MR046/05/R Service Instructions MRDocument8 pagesMagnetom C!: MR046/05/R Service Instructions MRjcleonbNo ratings yet
- GHFFFFDocument2 pagesGHFFFFsarb007No ratings yet
- Nursing Informatics Activity 2Document2 pagesNursing Informatics Activity 2Angelina Nicole G. TungolNo ratings yet
- DAHUA HTTP API FOR IPC Version 1.40Document106 pagesDAHUA HTTP API FOR IPC Version 1.40atsroot100% (1)
- Fsae AdminDocument36 pagesFsae AdminMarcos SaraivaNo ratings yet
- Affidavit For Address ProofDocument4 pagesAffidavit For Address ProofKaur NavneetNo ratings yet
- X11 Forwarding Using SSHDocument11 pagesX11 Forwarding Using SSHipgengNo ratings yet
- Cosmic - Cruise System Final - MinhasDocument26 pagesCosmic - Cruise System Final - Minhasdann_991No ratings yet