Professional Documents
Culture Documents
Unity Snapshots SRG
Uploaded by
RatataOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Unity Snapshots SRG
Uploaded by
RatataCopyright:
Available Formats
Welcome to Unity Snapshots.
Copyright ©2016 EMC Corporation. All Rights Reserved. Published in the USA. EMC believes the information in this publication is accurate as o f its publication date. The information is subject
to change without notice.
THE INFORMATION IN THIS PUBLICATION IS PROVIDED “AS IS.” EMC CORPORATION MAKES NO REPRESENTATIONS OR WARRANTIES OF ANY KIND WITH RESPECT TO THE INFORMATION IN
THIS PUBLICATION, AND SPECIFICALLY DISCLAIMS IMPLIED WARRANTIES OF MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE.
Use, copying, and distribution of any EMC software described in this publication requires an applicable software license. The trademarks, logos, and service marks (collectively "Trademarks")
appearing in this publication are the property of EMC Corporation and other parties. Nothing contained in this publication sh ould be construed as granting any license or right to use any
Trademark without the prior written permission of the party that owns the Trademark.
EMC, EMC² AccessAnywhere Access Logix, AdvantEdge, AlphaStor, AppSync ApplicationXtender, ArchiveXtender, Atmos, Authentica, Authentic Problems, Automated Resource Manager,
AutoStart, AutoSwap, AVALONidm, Avamar, Bus-Tech, Captiva, Catalog Solution, C-Clip, Celerra, Celerra Replicator, Centera, CenterStage, CentraStar, EMC CertTracker. CIO Connect,
ClaimPack, ClaimsEditor, Claralert ,cLARiiON, ClientPak, CloudArray, Codebook Correlation Technology, Common Information Model, Compuset, Compute Anywhere, Configuration
Intelligence, Configuresoft, Connectrix, Constellation Computing, EMC ControlCenter, CopyCross, CopyPoint, CX, DataBridge , Data Protection Suite. Data Protection Advisor, DBClassify, DD
Boost, Dantz, DatabaseXtender, Data Domain, Direct Matrix Architecture, DiskXtender, DiskXtender 2000, DLS ECO, Document Sciences, Documentum, DR Anywhere, ECS, elnput, E-Lab,
Elastic Cloud Storage, EmailXaminer, EmailXtender , EMC Centera, EMC ControlCenter, EMC LifeLine, EMCTV, Enginuity, EPFM. eRoom, Event Explorer, FAST, FarPoint, FirstPass, FLARE,
FormWare, Geosynchrony, Global File Virtualization, Graphic Visualization, Greenplum, HighRoad, HomeBase, Illuminator , InfoArchive, InfoMover, Infoscape, Infra, InputAccel, InputAccel
Express, Invista, Ionix, ISIS,Kazeon, EMC LifeLine, Mainframe Appliance for Storage, Mainframe Data Library, Max Retriever, MCx, MediaStor , Metro, MetroPoint, MirrorView, Multi-Band
Deduplication,Navisphere, Netstorage, NetWorker, nLayers, EMC OnCourse, OnAlert, OpenScale, Petrocloud, PixTools, Powerlink, PowerPath, PowerSnap, ProSphere, ProtectEverywhere,
ProtectPoint, EMC Proven, EMC Proven Professional, QuickScan, RAPIDPath, EMC RecoverPoint, Rainfinity, RepliCare, RepliStor, ResourcePak, Retrospect, RSA, the RSA logo, SafeLine, SAN
Advisor, SAN Copy, SAN Manager, ScaleIO Smarts, EMC Snap, SnapImage, SnapSure, SnapView, SourceOne, SRDF, EMC Storage Administrator, StorageScope, SupportMate, SymmAPI,
SymmEnabler, Symmetrix, Symmetrix DMX, Symmetrix VMAX, TimeFinder, TwinStrata, UltraFlex, UltraPoint, UltraScale, Unisphere, Universal Data Consistency, Vblock, Velocity, Viewlets, ViPR,
Virtual Matrix, Virtual Matrix Architecture, Virtual Provisioning, Virtualize Everything, Compromise Nothing, Virtuent, VMAX, VMAXe, VNX, VNXe, Voyence, VPLEX, VSAM-Assist, VSAM I/O
PLUS, VSET, VSPEX, Watch4net, WebXtender, xPression, xPresso, Xtrem, XtremCache, XtremSF, XtremSW, XtremIO, YottaYotta, Zero-Friction Enterprise Storage.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 1
This course covers the Snapshots feature for the EMC Unity platform. It includes Snapshots
for both block and file storage resources. The course provides an overview of the feature,
how Snapshots are created, managed, and used. It also includes the feature capabilities.
Demonstrations of Snapshots are also included.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 2
In this module, an overview of Unity Snapshots is provided. The architecture of Unity
Snapshots with its Redirect on Write technology is discussed and the benefits and
capabilities are listed.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 3
The Unity Snapshots feature is enabled with the Local Copies license for Unity that enables
space efficient point-in-time snapshots of storage resources for Block, File and VMware. The
snap images can be read-only or read/write and used in a variety of ways. They can provide
an effective form of local data protection to restore the production data to a known point-
in-time data state should data be mistakenly corrupted or deleted by the users. Images can
be accessed by hosts for data backup operations, data mining operations, application
testing, or decision analysis tasks. In the upcoming slides we will dive into the details of its
architecture, capabilities, benefits, and specifics of its operations and uses.
Note: Snapshots are not full copies of the original data. It is recommended that you do not
rely on snapshots for mirrors, disaster recovery, or high-availability tools. Because
snapshots of storage resources are partially derived from the real -time data in the relevant
storage resource, snapshots can become inaccessible (not readable) if the primary storage
becomes inaccessible.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 4
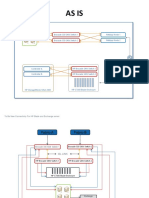
Snapshots of storage resources (block LUNs, file systems, and VMware Datastores) are
architected using Redirect on Write technology. This architecture avoids a performance
penalty that Copy on First Write technology has when existing data is changed. With
Redirect on Write technology, when a snapshot is taken, the existing data on the storage
object remains in place and provides the snapshot point-in-time view of the data.
Production data access also uses this view to read existing data. Another benefit of Redirect
on Write is that no storage resource is needed to create a snapshot. With Copy on First
Write technology, a storage resource had to be reserved to hold original data that changed
to preserve the point-in-time view. As its name implies, with Redirect on Write technology,
when writes are made to the storage object, those writes are redirected to a new location
allocated as needed from the parent pool in 256 megabyte stripes. New writes are stored in
8 kilobyte chunks on the newly allocated stripe. Reads of the new writes are serviced from
this new location as well.
If the snapshot is writable, any writes are handled in a similar manner; stripe space is
allocated from the parent pool and the writes are redirected in 8 kilobyte chunks to the new
space. Reads of newly written data are also services from the new space.
Storage space is needed in the pool to support snapshots as stripes are allocated for
redirected writes. Because of the on-demand stripe allocation from the pool, snapped thick
file systems will transition to thin file system performance characteristics.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 5
A LUN Consistency Group (CG) is a grouping of up to 50 LUNs to form a single instance of
LUN storage. They are primarily designed for a host application that will access multiple
LUNs, like a database application. Snapshots provide a mechanism for capturing a
snapshot of the multiple LUNs within a consistency group. When a Consistency Group
Snapshot is taken, the system will complete any outstanding IO to the group of LUNs, then
suspend writes to the LUNs until the snap operation completes. This allows the snapshot to
capture a write-order consistent image of the group of LUNs.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 6
With Unity Snapshots, it is possible to create multiple snapshots of a LUN to capture
multiple point-in-time data states. In this example the 3 o’clock and the 4 o’clock
snapshots are two different “child” snapshots of a common parent; meaning they capture
two different data states of a common storage object.
It is also possible to copy a snapshot. In this example, the 4 o’clock snapshot is copied and
other than having a unique name, the copy will be indistinguishable from the source
snapshot and both capture identical data states.
LUN snapshots and copies of LUN snapshots are writable objects but are unmodified from
their sources until they are attached to a host. In this example a copy of the 4 o’clock
snapshot is attached to a secondary host for access. At this point the snapshot data state is
marked as modified from its source. A LUN snapshot tree supports one snapshot attach at a
time. To access different snapshots in the tree the host would have to be detached from the
snap and attached to another desired snapshot in the tree.
Any subsequent copy of the attached snapshot will capture the data state of the source
snapshot at the point-in-time of the copy operation.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 7
As with LUN snapshots, it is possible to create multiple snapshots of a file system to capture
multiple point-in-time data states. The 3 o’clock and the 4 o’clock snapshots in this
example are two different “child” snapshots of the same file system parent and capture its
two different point-in-time data states.
Snapshots of a file system can be created either as read-only or read/write and are
accessed in different manners which will be covered later.
Copies of snapshots are always created as read/write snapshots. The read/write snapshots
can be shared by creating an NFS export or SMB share to them. When shared, they are
marked as modified to indicate their data state is different from the parent object.
It is also possible to nest copied and shared snapshots that form a hierarchy of snapshots
to a maximum of 10 levels deep.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 8
The table defines a variety of combined Snapshot capabilities for each of the Unity platform
models. These combined limits have an interaction between each other. For example, if a
Unity 300 system had 10 LUNs and 10 file systems, each LUN and file system could not
have 256 user snapshots because that would exceed the maximum user snapshots of 1000
for the system.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 9
This module covered an overview of Unity Snapshots. The redirect on write architecture of
Unity Snapshots was detailed and its benefits and capabilities were listed.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 10
This module covers the creation of block and file Snapshots. It also details using a schedule
for creating Snapshots. The operations that can be performed on Snapshots are also shown.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 11
Snapshots are created on storage resources for Block, File and VMware. And all are done in
a similar manner.
For Block, the snapshot is created on a LUN or a group of LUNs in the case of a Consistency
Group. For File, the snapshot is configured on a file system. For VMware the storage
resource is either going to be a LUN for a VMFS datastore or a file system for an NFS
datastore. When creating each of these storage resources, the Unity system provides a
wizard for their creation. Each wizard provides an option to automatically create snapshots
on the storage resource. Each resource snapshot creation is nearly identical to the other
resources.
For storage resources already created, snapshots can be manually created for them from
their Properties page. As with the wizard, the snapshot creation from the storage resource
Properties page is nearly identical to the other resources. The following few slides will show
snapshot creation within the Block storage LUN creation wizard and the File storage file
system creation wizard. It will also show creating manual snapshots from the LUN and file
system Properties pages.
Video demonstrations will be provided showing all forms of storage resource snapshot
creation.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 12
LUN snapshots can easily be created in a number of ways. Within the wizard to create a
LUN, there is an option to automatically create snapshots for the LUN based on a schedule.
The wizard contains a dropdown selection that has three different system defined
schedules to select from to create the LUN snapshots. Within each schedule there is also a
snapshot retention value.
A customized schedule can also be created for use. The scheduler provides the ability to
configure a snapshot frequency by the hour, day or week. A snapshot retention policy can
also be defined.
Note: fields annotated with a red asterisk are required for the configuration.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 13
For existing LUNs, snapshots are easily created from the LUN Properties page by selecting
the Snapshots tab.
Select the + icon to create a snapshot of the LUN. The snapshot must be configured with a
name; by default the system provides a name having a year, month, day, hour, minute,
second format. Customized names can also be configured. A Description field for the
snapshot can optionally be annotated. One of three Retention Policies must be configured.
The default retention configuration is the Pool Automatic Deletion Policy which will
automatically delete the snapshot if Pool space reaches a specified capacity threshold. A
customized retention time can alternately be selected and configured for snapshot deletion
on a specified calendar day and time. The other alternative is to select the No Automatic
Deletion option should the snapshot need to be kept for an undetermined amount of time.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 14
Similar to LUNs, file system snapshots can easily be created in a number of ways. Within
the wizard to create a file system, there is an option to automatically create snapshots for
the file system based on a schedule. File system snapshots created by a schedule are read-
only.
The wizard contains a dropdown selection that has three different system defined
schedules to select from to create the file system snapshots. Within each schedule there is
also a snapshot retention value.
A customized schedule can also be created for use. The scheduler provides the ability to
configure a snapshot frequency by the hour, day or week. A snapshot retention policy can
also be defined.
As noted before, fields annotated with a red asterisk are required for the configuration.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 15
Similar to the LUN snapshot seen earlier, existing file systems snapshots are easily created
from the file system Properties page by selecting the Snapshots tab. A manually created
file system snapshot can be read-only or read/write.
Select the + icon to create a snapshot of the file system. The snapshot must be configured
with a name; the system by default provides a name based on the creation time in a year,
month, day, hour, minute, second format. Customized names can also be configured. An
optional Description field for the snapshot can be annotated. One of three Retention Policies
must be configured. The default retention configuration is the Pool Automatic Deletion
Policy which will automatically delete the snapshot if Pool space reaches a specified capacity
threshold. A customized retention time can alternately be selected and configured for
snapshot deletion on a specified calendar day and time within a year of creation. The other
alternative is to select the No Automatic Deletion option should the snapshot need to be
kept for an undetermined amount of time.
The Access Type section requires configuration by selecting one of the two options for the
snapshot to be created read-only or read/write.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 16
The system’s user interface provides a Snapshot Schedule page that lists all the system and
user defined schedules and if they are in use. The user defined schedules can be edited
from this page but the system defined schedules cannot be edited. User defined schedules
can be created using a frequency granularity of hours, daily or weekly and be retained for
31 days.
Additional user defined schedules can be created as shown here. This example shows a
schedule that will create weekend snapshots that will be created at midnight and retained
for two weeks.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 17
To apply a snapshot schedule to a storage resource, simply go to the Snapshots tab on the
Properties page of the resource and select the Schedule Snapshot option. From the
Snapshot schedule dropdown list select the desired schedule to apply to the resource.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 18
This video covers creating Snapshots for each Unity storage resource; LUN and LUN CG, file
system, and VMware datastores. Automatic creation is shown via each resource creation
wizard and manual creation is shown via each resource Properties page.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 19
The operations that can be performed on a snapshot differ based on the type of storage
resource the snapshot is on. Operations on LUN-based snapshots are Restore, Attach to
host, Detach from host, and Copy. Operations on file system-based snapshots are Restore
and Copy.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 20
The Snapshot Restore operation will roll back the storage resource to the point-in-time data
state that the snapshot captures. In this Restore example, a LUN is at a 5 o’clock data state
and is going to be Restored from a snapshot with a 4 o’clock data state.
Before performing a restore operation, detach hosts attached to any of the LUN snapshots.
Also ensure that all hosts have completed all read and write operations to the LUN you want
to restore. Finally disconnect any host accessing the LUN. This may require disabling the
host connection on the host-side.
Now the Restore operation can be performed. From the 4 o’clock snapshot select the
Restore operation. The system will automatically create a snapshot of the current 5 o’clock
data state of the LUN to capture its current data state before the restoration operation
begins. The LUN is restored to the 4 o’clock data state of the snapshot.
The hosts can now be reconnected to the resources they were connected to prior to the
restore and resume normal operations.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 21
The Restore operation is accessed from the Properties page of the storage resource. Select
its Snapshots tab then select the snapshot to restore from. The Restore operation is
accesses from the More Actions dropdown list. The system will create a restore point
snapshot of the current data state of the LUN prior to the restoration operation. Once
complete the new restore point snapshot is listed.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 22
The Snapshot Attach operation will attach a connected host to a snapshot for read/write
access to its point-in-time view of the LUN data. In this Attach example, a secondary host is
going to Attach to the 3 o’clock snapshot of the LUN.
Before performing an Attach operation, hosts must be configured for snapshot access to
the LUN. There are two possible settings: Snapshot access or LUN and Snapshot access.
The Snapshot access setting provides a secondary host read/write access to all the
snapshots associated with the LUN, but no access to the LUN itself. A host can access and
recover data from snapshots associated with the LUN but has no access to the data on the
LUN itself. The LUN and Snapshot access setting provides a primary host read/write access
to both the LUN itself and all of the snapshots associated with the storage resource. A host
can use the LUN data and can recover data from snapshots associated with the LUN.
Now the Attach operation can be performed. From the 3 o’clock snapshot, select the Attach
to host operation. The system will optionally create a copy of the snapshot to preserve its
data state before the attach operation begins. The secondary host is attached to the 3
o’clock snapshot of the LUN.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 23
To give a host access to snapshots of a LUN, from the LUN Properties page select the
Access tab. Hosts can be added to LUN access using the + icon. To provide a listed host
access to snapshots of the LUN, select the Snapshot or LUN and Snapshot setting from the
Modify Access dropdown.
The Attach to host operation is accessed from the Properties page of the storage resource.
Select its Snapshots tab then select the snapshot to attach to. The Attach to host operation
is accessed from the More Actions dropdown list. The system will optionally create a copy
of the snapshot to preserve its integrity.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 24
The Snapshot Detach operation will detach a connected host from a LUN snapshot. In this
Detach example, a secondary host is going to Detach from the 3 o’clock snapshot of the
LUN.
Before performing a Detach operation, allow any outstanding read/write operations of the
snapshot attached host to complete.
Now the Detach operation can be performed. From the 3 o’clock snapshot, select the
Detach from host operation. The secondary host is detached from the 3 o’clock snapshot of
the LUN.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 25
The Detach from host operation is accessed from the Properties page of the storage
resource. Select its Snapshots tab then select the snapshot to detach from. The action for
Attach to host and Detach from host are mutually exclusive operations. The Detach from
host operation is only available for snapshots that are attached. Select an attached
snapshot to detach from. Perform the Detach from host operation by selecting it from the
More Actions dropdown list. In the Detach confirmation window, confirm the detach
operation to complete the operation.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 26
The Snapshot Copy operation will make a copy of an existing snapshot that is either
attached or detached from a host. The copy will capture the existing data state of the
snapshot it copies. In this Copy example, a copy of an existing 4 o’clock snapshot is being
made . The copy inherits the parent snapshot data state of 4 o’clock and its retention
policy.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 27
The Copy operation is accessed from the Properties page of the storage resource. Select its
Snapshots tab then select the snapshot to copy. Perform the Copy operation by selecting it
from the More Actions dropdown list. The system will provide a unique name for the
snapshot copy based on the time of creation or optionally a customized name can be
assigned.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 28
The Snapshot Restore operation for a file system is similar to the Restore operation of a
LUN. It will roll back the file system to a point-in-time data state that a read-only or
read/write snapshot captures. In this Restore example, a file system is at a 5 o’clock data
state and is going to be Restored from a read-only snapshot with a 4 o’clock data state.
Before performing a restore operation, disconnect clients from any of the file system
snapshots. Also quiesce IO to the file system being restored.
Now the Restore operation can be performed. From the 4 o’clock snapshot select the
Restore operation. The system will automatically create a snapshot of the current 5 o’clock
data state of the file system to capture its current data state before the restoration
operation begins. The file system is restored to the 4 o’clock data state of the snapshot.
The connections and IO to the resources can now be resumed for normal operations.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 29
The Restore operation is accessed from the Properties page of the storage resource. Select
its Snapshots tab then select the snapshot to restore from. The Restore operation is
accessed from the More Actions dropdown list. The system will create a restore point
snapshot of the current data state of the file system prior to the restoration operation.
Once complete the new restore point snapshot is listed.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 30
The Snapshot Copy operation will make a copy of an existing file system snapshot that is
either read-only or read/write shared or unshared. The copy will capture the existing data
state of the snapshot it copies. In this Copy example, a copy of an existing 4 o’clock read-
only snapshot is being made . The copy will be read/write and inherits the parent snapshot
data state of 4 o’clock and its retention policy.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 31
The Copy operation is accessed from the Properties page of the storage resource. Select its
Snapshots tab then select the snapshot to copy. Perform the Copy operation by selecting it
from the More Actions dropdown list. The system will provide a unique name for the
snapshot copy based on the time of creation or optionally a customized name can manually
be assigned.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 32
This module covered the creation of snapshot for Unity storage resources; LUNs and LUN
Consistency groups, file systems, and VMware datastores. User customized snapshot
schedules were created and applied to Unity storage resources to automate snapshot
creation and deletion. The operations for LUN and file system snapshots were detailed.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 33
This module covers the use of Snapshots. It details accessing block and file snapshots. It
also shows how the Checkpoint Virtual File System is accessed by Windows and NFS users
to restore corrupted or deleted files.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 34
The process of accessing a LUN snapshot requires performing tasks on the storage system
and on the host that will access the snapshot.
On the storage system the host will have to be configured to access snapshots of the LUN.
This task is done on the LUN Properties page from the Access tab. A host has to have
connectivity to the storage, either via fibre channel or iSCSI, and be registered. Next, from
the Snapshots tab, a snapshot is selected and the snapshot operation Attach to host needs
to be performed.
Now tasks from the host will need to be done. The host will need to discover the disk
device that the snapshot presents to it. Once discovered, then the host can access the
snapshot as a disk device.
A short video follows that demonstrates a host accessing a LUN snapshot.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 35
This is a short video demonstrating a Windows 2012 iSCSI attached host accessing a LUN
snapshot.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 36
The process of accessing a file system read/write snapshot requires performing tasks on
the storage system and on the client that will access the snapshot.
On the storage system an NFS and/or SMB share will have to be configured on the
read/write snapshot of the file system. This task is done from their respective pages.
Now tasks from the client will need to be done. The client will need to be connected to the
NFS/SMB share of the snapshot. Once connected, then the client can access the snapshot
shared resource.
A short video follows that demonstrates client access to a file system snapshot.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 37
This is a short video demonstrating an NFS client accessing a read/write file system
snapshot.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 38
The process of accessing a file system read-only snapshot is very different than accessing a
read/write snapshot. The read-only file system snapshot is exposed to the client through a
checkpoint virtual file system (CVFS) mechanism that Snapshots provides. The read-only
snapshot access does not require performing any tasks on the storage system. All the
tasks are performed on the client through its access directly to the file system. The tasks
for NFS clients are slightly different than the tasks for SMB clients.
The first task for an NFS client is to connect to an NFS share on the file system. Access to
the read-only snapshot is established by accessing the snapshot’s hidden .ckpt data path.
This path will redirect the client to the point-in-time view that the read-only snapshot
captures.
Similarly, the first task for an SMB client is to connect to an SMB share on the file system.
Access to the read-only snapshot is established by the SMB client accessing the SMB
share’s Previous Versions tab. This will redirect the client to the point-in-time view that the
read-only snapshot captures.
Because the read-only snapshot is exposed to the clients through the CVFS mechanism,
the clients are able to directly recover data from the snapshot without any administrator
intervention. For example, if a user either corrupted or deleted a file by mistake, that user
could directly access the read-only snapshot and get an earlier version of the file from the
snapshot and copy it to the file system to recover from.
A short video follows that demonstrates client access to a file system read-only snapshot.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 39
This is a short video demonstrating an NFS client and an SMB client accessing a read-only
file system snapshot via CVFS.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 40
This module covered the process of attaching a host to a LUN snapshot to access its point-
in-time data state. Client access of a read/write file system snapshot was demonstrated.
The CVFS access of a read-only file system snapshot was shown for both NFS and SMB
clients.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 41
This course covered an overview of the Unity Snapshots feature along with its architecture
and capabilities. Snapshots were created for the various Unity storage resources and their
specific snapshot operations were discussed. Finally snapshot usage was shown with hosts
and clients accessing the point-in-time data of snapshots.
This concludes the training.
Copyright 2016 EMC Corporation. All rights reserved. Unity Snapshots 42
You might also like
- Storage Optimization with Unity All-Flash Array: Learn to Protect, Replicate or Migrate your data across Dell EMC Unity Storage and UnityVSAFrom EverandStorage Optimization with Unity All-Flash Array: Learn to Protect, Replicate or Migrate your data across Dell EMC Unity Storage and UnityVSARating: 5 out of 5 stars5/5 (1)
- DD Os 5.4 Differences Full Version - Student GuideDocument183 pagesDD Os 5.4 Differences Full Version - Student Guidesorin_gheorghe20No ratings yet
- System Center Configuration Manager - Administration Ebook v2Document197 pagesSystem Center Configuration Manager - Administration Ebook v2RaphaelNo ratings yet
- 01-Bullion S General Training V3Document66 pages01-Bullion S General Training V3RatataNo ratings yet
- Vplex Fundamentals 6.0 SRG PDFDocument82 pagesVplex Fundamentals 6.0 SRG PDFPinakini MothukuriNo ratings yet
- Unity ReplicationDocument56 pagesUnity ReplicationRatataNo ratings yet
- Unity Basic Maintenance - SRGDocument33 pagesUnity Basic Maintenance - SRGAntoine HenryNo ratings yet
- DELL EMC VxRail NotesDocument8 pagesDELL EMC VxRail NotesVijayenNNo ratings yet
- Unity Hardware Fundamentals - SRGDocument60 pagesUnity Hardware Fundamentals - SRGRatataNo ratings yet
- RecoverPoint With SRMDocument63 pagesRecoverPoint With SRMhemanth-07No ratings yet
- Vplex A&m Student GuideDocument89 pagesVplex A&m Student Guideph5nx100% (1)
- RecoverPoint DemonstrationDocument10 pagesRecoverPoint DemonstrationRob DicksonNo ratings yet
- EMC Data Domain Technical OverviewDocument24 pagesEMC Data Domain Technical Overviewtelagamsetti0% (1)
- Unity Configuration and Implementation - SRGDocument77 pagesUnity Configuration and Implementation - SRGRatata100% (1)
- vSAN Troubleshooting Diagram - CommandAndLogsv7 - 3Document2 pagesvSAN Troubleshooting Diagram - CommandAndLogsv7 - 3Sindhuri Rao100% (1)
- Field Installation GuideDocument35 pagesField Installation GuideBrazinhoNo ratings yet
- DD OS 5.2 Initial Configuration GuideDocument58 pagesDD OS 5.2 Initial Configuration Guidedragos_scribdNo ratings yet
- Dell Midrange SizerDocument4 pagesDell Midrange SizerBobNo ratings yet
- DataDomain Fundamentals 6.0 PDF PDFDocument104 pagesDataDomain Fundamentals 6.0 PDF PDFRatataNo ratings yet
- VSOS51 Lecture V1 PDFDocument360 pagesVSOS51 Lecture V1 PDFMandar BhaveNo ratings yet
- Commvault Intellisnap For Oracle Databases On Pure StorageDocument60 pagesCommvault Intellisnap For Oracle Databases On Pure Storagetung nguyenNo ratings yet
- Brocade Zoning Tutorial: Setup Zones on SwitchDocument6 pagesBrocade Zoning Tutorial: Setup Zones on Switchgkiran_chNo ratings yet
- Data Domain Student GuideDocument288 pagesData Domain Student GuideNitesh RoyNo ratings yet
- Unity Snapshots SRGDocument42 pagesUnity Snapshots SRGRatata100% (1)
- Docker Introduction: Installation, Images, Containerizing AppsDocument19 pagesDocker Introduction: Installation, Images, Containerizing AppsManavi AgrawalNo ratings yet
- h15104 Vxrail Appliance TechbookDocument87 pagesh15104 Vxrail Appliance Techbooktech_haloNo ratings yet
- ONTAP (9.5) Cluster Administration - Lab Setup Guide - v1 - 3Document17 pagesONTAP (9.5) Cluster Administration - Lab Setup Guide - v1 - 3murali krishnaNo ratings yet
- Vmware Operationalizing NSXDocument94 pagesVmware Operationalizing NSXMattNo ratings yet
- Vs Vmware AdminDocument176 pagesVs Vmware Adminpreeti700No ratings yet
- Vmware Vsphere With Ontap Best Practices: Netapp SolutionsDocument36 pagesVmware Vsphere With Ontap Best Practices: Netapp SolutionsSenthilkumar MuthusamyNo ratings yet
- Unified Storage Management Final Lab Guide VNX Lab Guide 2014Document233 pagesUnified Storage Management Final Lab Guide VNX Lab Guide 2014vidyasagarrao100% (1)
- CVSA18-M09-Archive, Index & SearchDocument54 pagesCVSA18-M09-Archive, Index & SearchMuneeza HashmiNo ratings yet
- Isilon PerformanceDocument69 pagesIsilon PerformanceManikandan Bose SNo ratings yet
- OceanStor 5300 V3&5500 V3&5600 V3&5800 V3&6800 V3&6900 V3 Storage System V300R001 Maintenance Guide 06Document359 pagesOceanStor 5300 V3&5500 V3&5600 V3&5800 V3&6800 V3&6900 V3 Storage System V300R001 Maintenance Guide 06Jeerahnon ThanumaiweerakunNo ratings yet
- SL 10327Document115 pagesSL 10327emcviltNo ratings yet
- VPLEX Installation and Config GuideDocument82 pagesVPLEX Installation and Config GuideK00245476No ratings yet
- Brocade San Switch TroubleshootingDocument7 pagesBrocade San Switch TroubleshootingMohaideenNo ratings yet
- FlashArray Installation - Changing Purity - FA Version On A New FlashArrayDocument3 pagesFlashArray Installation - Changing Purity - FA Version On A New FlashArrayDaniel Moreira100% (1)
- The Nutanix Bible: by Steven PoitrasDocument164 pagesThe Nutanix Bible: by Steven PoitrasccuuiioossNo ratings yet
- The Nutanix Bible: by Steven PoitrasDocument164 pagesThe Nutanix Bible: by Steven PoitrasccuuiioossNo ratings yet
- Recover Point Implementation Lab Guidev3.2Document223 pagesRecover Point Implementation Lab Guidev3.2mlinarecNo ratings yet
- SnapMirror SE TrainingDocument121 pagesSnapMirror SE TrainingtungNo ratings yet
- EMC Isilon Customer Troubleshooting Guide - Troubleshoot Your SmartConnect Configuration-Docu63149Document27 pagesEMC Isilon Customer Troubleshooting Guide - Troubleshoot Your SmartConnect Configuration-Docu63149Renisha MsNo ratings yet
- Nutanix Solution NoteDocument14 pagesNutanix Solution Notenaja manNo ratings yet
- Vmax 3 Lab GuideDocument92 pagesVmax 3 Lab GuideSrinivas Gollanapalli100% (1)
- Troubleshooting Storage PerformanceDocument43 pagesTroubleshooting Storage PerformancejcayabNo ratings yet
- Clustered ONTAP 8 2 OverviewDocument33 pagesClustered ONTAP 8 2 OverviewjkargmanNo ratings yet
- SyncIQ Failures CheckingDocument23 pagesSyncIQ Failures CheckingVasu PogulaNo ratings yet
- ScaleIO Fundamentals MR 1WN SIOFUN - Student GuideDocument74 pagesScaleIO Fundamentals MR 1WN SIOFUN - Student GuideReinaldo GuzmanNo ratings yet
- Welcome To The VPLEX VS6 Hardware Architecture CourseDocument38 pagesWelcome To The VPLEX VS6 Hardware Architecture CourserosennedkovNo ratings yet
- CVTSP19M4 - Commvault Hyperscale ElectiveDocument36 pagesCVTSP19M4 - Commvault Hyperscale ElectiveMuneeza HashmiNo ratings yet
- Factory Acceptance Test Plan - LTE ENodeBDocument6 pagesFactory Acceptance Test Plan - LTE ENodeBLaura VillarrealNo ratings yet
- Avamar Data Domain Integration Lab Guide 2014Document41 pagesAvamar Data Domain Integration Lab Guide 2014Ryadh ArfiNo ratings yet
- Vxrail Quickstart Guide: Physical Site PreparationDocument2 pagesVxrail Quickstart Guide: Physical Site PreparationPavan NavNo ratings yet
- VPLEX Administration Student GuideDocument261 pagesVPLEX Administration Student GuideLuis SandersNo ratings yet
- CVTSP1120-M05-Commvault Disaster RecoveryDocument19 pagesCVTSP1120-M05-Commvault Disaster RecoverysahiltomohitNo ratings yet
- Dell XC630-10 Nutanix On VMware ESXi Reference ArchitectureDocument51 pagesDell XC630-10 Nutanix On VMware ESXi Reference ArchitecturePrincipled TechnologiesNo ratings yet
- Isilon Administration and Management PDFDocument2 pagesIsilon Administration and Management PDFDavid GiriNo ratings yet
- Platform Administration Guide-NOS v3 5Document124 pagesPlatform Administration Guide-NOS v3 5Cepi SupriadiNo ratings yet
- Brocade San Ts Exam Study GuideDocument5 pagesBrocade San Ts Exam Study GuideAakashNo ratings yet
- Commvault & Vmware: SvtechDocument32 pagesCommvault & Vmware: SvtechAdmin AdminNo ratings yet
- Nutanix - Advanced-Admin-AOS-v51Document63 pagesNutanix - Advanced-Admin-AOS-v51pkjk07No ratings yet
- VPLEX Administration GuideDocument272 pagesVPLEX Administration GuidePrasadValluraNo ratings yet
- How To Create A Local Mirror of The Latest Update For Red Hat Enterprise Linux 5, 6, 7, 8 Without Using Satellite Server?Document28 pagesHow To Create A Local Mirror of The Latest Update For Red Hat Enterprise Linux 5, 6, 7, 8 Without Using Satellite Server?mysytsNo ratings yet
- v02 NBU83ADM - Lab 02 NetBackup Web UI LinuxDocument34 pagesv02 NBU83ADM - Lab 02 NetBackup Web UI Linuxrambabu koppokuNo ratings yet
- Netapp Multipath StrategyDocument11 pagesNetapp Multipath Strategyaamirhussain75No ratings yet
- Red Hat OpenShift The Ultimate Step-By-Step GuideFrom EverandRed Hat OpenShift The Ultimate Step-By-Step GuideRating: 1 out of 5 stars1/5 (1)
- New connectivity for HP blades and Exchange serversDocument2 pagesNew connectivity for HP blades and Exchange serversRatataNo ratings yet
- SAN - Extended Fabric Configuration GuideDocument17 pagesSAN - Extended Fabric Configuration GuideRatataNo ratings yet
- x460 g2 Data SheetDocument18 pagesx460 g2 Data SheetRatataNo ratings yet
- Configuring The E-Port in ISLDocument10 pagesConfiguring The E-Port in ISLRatataNo ratings yet
- VVOLDocument112 pagesVVOLRatataNo ratings yet
- FOS 700 ChecksumDocument1 pageFOS 700 ChecksumRatataNo ratings yet
- Docu49786 - Data Domain Operating System 5.2 Data Domain Extended Retention Administration Guide PDFDocument40 pagesDocu49786 - Data Domain Operating System 5.2 Data Domain Extended Retention Administration Guide PDFRatataNo ratings yet
- PowerEdge VRTX Dual PERC FailoverDocument13 pagesPowerEdge VRTX Dual PERC FailoverNoel CastroNo ratings yet
- VVOL2Document34 pagesVVOL2RatataNo ratings yet
- DD Security Configuration GuideDocument50 pagesDD Security Configuration GuideRatataNo ratings yet
- Best Practices For Running VMware VSphere On ISCSIDocument37 pagesBest Practices For Running VMware VSphere On ISCSICésar VieiraNo ratings yet
- VVOLDocument112 pagesVVOLRatataNo ratings yet
- IDPA Admin GuideDocument100 pagesIDPA Admin GuideRatataNo ratings yet
- Best Practices For Running VMware VSphere On ISCSIDocument37 pagesBest Practices For Running VMware VSphere On ISCSICésar VieiraNo ratings yet
- 3 Novascale Bullion - SHCDocument43 pages3 Novascale Bullion - SHCRatataNo ratings yet
- 6 Novascale Bullion - Install VMwareDocument39 pages6 Novascale Bullion - Install VMwareRatataNo ratings yet
- 1 Novascale Bullion - HardwareDocument64 pages1 Novascale Bullion - HardwareRatataNo ratings yet
- 5 Novascale Bullion - IcareDocument33 pages5 Novascale Bullion - IcareRatataNo ratings yet
- 2 Novascale Bullion - BiosV2Document51 pages2 Novascale Bullion - BiosV2RatataNo ratings yet
- 4 Novascale Bullion - Toolsv3Document20 pages4 Novascale Bullion - Toolsv3RatataNo ratings yet
- Mais Questo EsDocument5 pagesMais Questo EsVitória MeloNo ratings yet
- Computer Architecture QuestionsDocument1 pageComputer Architecture QuestionsDEBJYOTI SARKARNo ratings yet
- SarafudeenDocument30 pagesSarafudeenLalu KrishNo ratings yet
- Checking Server Hardware and Memory ConfigurationDocument4 pagesChecking Server Hardware and Memory Configurationdip.sankar20049655No ratings yet
- Introducing The Hisense HM516 Rugged Tablet POS System!Document2 pagesIntroducing The Hisense HM516 Rugged Tablet POS System!carlosNo ratings yet
- EEM 486: Computer Architecture: Course Introduction and The Five Components of A ComputerDocument13 pagesEEM 486: Computer Architecture: Course Introduction and The Five Components of A ComputerMahmut Ferit YildizNo ratings yet
- 100 Shortcut by Joshua JabDocument4 pages100 Shortcut by Joshua JabJoshua BaahNo ratings yet
- Adding A Second Controller To Create An HA PairDocument24 pagesAdding A Second Controller To Create An HA PairPurushothama GnNo ratings yet
- Sap ClientDocument66 pagesSap ClientRajkumarNo ratings yet
- 2023 06 095 - LogDocument3 pages2023 06 095 - LogAlauddin Razin bin Ahmad ZawawiNo ratings yet
- Split Tunneling ConcernsDocument6 pagesSplit Tunneling ConcernsAhmed OusamaNo ratings yet
- P 4 GuideDocument128 pagesP 4 Guidediana0926No ratings yet
- 13.5.1 Packet Tracer - WLAN Configuration - ILMDocument4 pages13.5.1 Packet Tracer - WLAN Configuration - ILMJhonathanNo ratings yet
- Dell Vostro V131 Owner's ManualDocument90 pagesDell Vostro V131 Owner's ManualCw TanNo ratings yet
- WHMCS - Printable Ticket VersionDocument5 pagesWHMCS - Printable Ticket VersionAnonymous iKCJrQ37No ratings yet
- Living in The IT Era: Ge Elec 3Document27 pagesLiving in The IT Era: Ge Elec 3Marnie MacapinlacNo ratings yet
- ICAS Network License ConfigurationDocument5 pagesICAS Network License ConfigurationTarunNo ratings yet
- Red Book V7000gen2Document206 pagesRed Book V7000gen2qsef007No ratings yet
- How To Perform A Factory Reset On A Windows 11 Desktop - TechTargetDocument5 pagesHow To Perform A Factory Reset On A Windows 11 Desktop - TechTargetMARK LAWRENZ SERIOSANo ratings yet
- The Complete Guide to 8051 Microcontroller ProgrammingDocument105 pagesThe Complete Guide to 8051 Microcontroller ProgrammingPraveen RathnamNo ratings yet
- IPv6 Routing ProtocolsDocument18 pagesIPv6 Routing ProtocolsjuliardiindraNo ratings yet
- Fen Cris Trau TechDocument76 pagesFen Cris Trau TechBRUNO ADRIEL ZAMORA FERNÁNDEZNo ratings yet
- Hardware Troubleshooting: Course T302Document19 pagesHardware Troubleshooting: Course T302Gajanan Chavhan100% (1)
- CP MPMC Ay22-23Document12 pagesCP MPMC Ay22-23Vedashree ShetyeNo ratings yet
- How To Check Windows 10 Computer System Specs & Requirements - Microsoft PDFDocument8 pagesHow To Check Windows 10 Computer System Specs & Requirements - Microsoft PDFBilal AhmadNo ratings yet
- ScaleIO Alarm Storage Pool Has Degraded CapacityDocument28 pagesScaleIO Alarm Storage Pool Has Degraded CapacityMAHDINo ratings yet