Professional Documents
Culture Documents
Container Firewall Guide
Uploaded by
ashokvardhnCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Container Firewall Guide
Uploaded by
ashokvardhnCopyright:
Available Formats
Cloud-Native
Container Firewalls
A Comparison Of
Container Firewalls vs.
Next Generation Firewalls vs.
Web Application Firewalls
© 2017 NeuVector Inc
CONTINUOUS NETWORK SECURITY FOR CONTAINERS
Container Firewalls vs. NGFWs vs. WAFs
What is a Container Firewall? And how is it different than a Next Generation Firewall
and a Web Application Firewall?
Containers and microservices are revolutionizing computing. But
can firewalls help secure these? Next Generation Firewalls (NGFW)
were supposed to handle the latest threats and data center
designs, but fall short in the new cloud microservices
environments. Web Application Firewalls (WAF) provide dedicated protection from
malicious HTTP clients attacking web front-ends, but are not designed for internal
application protection.
Before we get into the feature comparison of NGFWs, WAFs, and container
firewalls, let’s take a look at the attributes of containers and microservices.
Containers are part of a larger trend toward virtualized application workloads.
Virtualized workloads, whether they are containers, IoT devices, or serverless
computing provide a wealth of declarative meta-data from which security policies
and decisions can be derived.
Attributes of Microservices – An Explosion of East-West Traffic
The migration from monolithic applications to container-based
microservices brings many benefits but also changes
communication patterns. The most significant change from a
networking and security view is that there is now an explosion
of East-West, or internal, traffic within hosts and between
hosts. While each running container can be hardened and
expose limited interfaces there are also many more opportunities for attackers to
probe and find vulnerabilities.
Containers are designed to be deployed in seconds and an orchestration system
can launch new containers on the same hosts or across hosts depending on service
demands and host resources available. Each container has its own mapped
network interfaces which get assigned and deallocated on the fly.
© 2017 NeuVector Inc. info@neuvector.com 2
CONTINUOUS NETWORK SECURITY FOR CONTAINERS
Security Issues of Container Deployments
With containers being started and stopped constantly, and rapid deployment of
updates to applications through a continuous integration and continuous delivery
(CI/CD) pipeline, it becomes very difficult to monitor and secure container traffic at
the network layer. NGFWs and WAFs are designed mainly to be a gateway for
external, or north-south traffic, and can’t protect container traffic.
Not only is it difficult for traditional firewalls to see east-west internal traffic within a
host or between hosts, it is also impossible for them to keep up with the constant
changes as containers launch and disappear. As one network security architect put
it “in a containerized world you can’t be messing with iptables or manually updating
firewall rules.”
Why is it important to monitor containers at run-time? One reason is the frequent
use of open source software for building container applications. Often, developers
may not understand the application vulnerabilities which are introduced with each
open source package or library used. And once in production, it is easy to lose track
of which containers are vulnerable to new vulnerabilities discovered, often years
after they are put into production.
Key Features of a Cloud-Native Container Firewall
So what is a container firewall? A container firewall provides much of the same
protections that next generation firewalls provide at the edge, but in a cloud-native
© 2017 NeuVector Inc. info@neuvector.com 3
CONTINUOUS NETWORK SECURITY FOR CONTAINERS
environment for all container traffic. This includes east-west, north-south, and
container to non-container traffic.
A cloud-native container firewall is able to isolate and protect workloads,
application stacks, and services, even as individual containers scale up, down, or
across hosts. It must also protect the ingress and egress from external networks
and legacy applications much like a traditional gateway firewall does, except with
container awareness.
Here are the key features of a Cloud-native Container Firewall
• Intent based intelligence. Understands intent of applications from meta-data and
behavioral analysis. Characteristics include:
o Declarative, automated protection. Discovers application behavior and
security requirements and adapts to changes and updates.
o Whitelist based rules. Assumes a zero-trust model and defines allowed
behavior.
o Application based (Layer 7) policy. Does not use IPtables or only L3/L4 rules.
• Container level protection. Drop suspicious connections or quarantine entire
container.
• Integrates with container orchestration. Scales across hosts, clouds and adapts
to updates.
• Supports container platforms and run-time engine. Runs seamlessly with system
security libraries, overlay networks, and Docker engine.
© 2017 NeuVector Inc. info@neuvector.com 4
CONTINUOUS NETWORK SECURITY FOR CONTAINERS
• Supports common containerized application protocols. Recognize and enforce
policy based on popular application protocols such redis, mysql, mongodb.
• Fits into CI/CD processes. Integrate into automated pipelines using REST API to
support scripting, Jenkins etc.
A container firewall also includes many next generation firewall features, such as:
• Layer 7 deep packet inspection (DPI). Many microservices communicate over
HTTP, and detecting and protecting based on application protocol is critical.
• Threat protection. Protects against internal application level attacks such as DDoS,
DNS attacks commonly found in web application firewall (WAF) devices.
• Blacklist rules. Ability to set rules based on IP addresses, ranges, or other L3/L4
policies.
Because a container firewall is meant to primarily protect container traffic, it is not
meant to replace the NGFW, IDS/IPS, or WAF at the edge. However, it must protect
against common known application attacks which could originate internally.
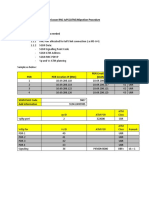
The diagram below shows how an NGFW provides multi-protocol protection, while
a WAF provides additional web application protection to containers exposed to the
internet.
A container firewall provides inspection and protection of all traffic into and out of a
container. While this might be primarily container to container traffic, a container
© 2017 NeuVector Inc. info@neuvector.com 5
CONTINUOUS NETWORK SECURITY FOR CONTAINERS
firewall must also protect ingress from external sources to containers, and egress
from containers to external applications and the internet.
Key Features of a Next Generation Firewall (NGFW)
Next generation firewalls provide advanced protection for traditional data centers,
where traffic from the internet or from untrusted networks need to be secured.
In general, a next generation firewall will include these features:
• L7 Application Awareness. Monitor connections by inspecting the application
protocols at network layer 7, in addition to Layers 2-4.
• Threat Detection Through Intrusion Detection/Protection System (IDS/IPS). An
IPS system will detect and block known attacks through the use of signatures,
behaviors, and other detection techniques.
• Stateful Inspection. Traffic inspection and protection policies are based on the
state of connections. An NGFW can enforce stateful inspection policies based on not
only L2-4 but also up to Layer 7.
• User-Identity Policies. Access to resources can be controlled by user identity, not
just the IP address or type of connection. In a container firewall, a similar capability
is to restrict container to container traffic based on behavioral learning.
• Support for Routed and Bridged Modes. Firewalls may be deployed as a bridge
(L2) and/or a router (L3) depending on the topology and requirements. Container
firewalls are host deployed and operate like a bridge (bump in the wire) to monitor
packets and block if enabled.
Next Page: NGFW vs Container Firewall
© 2017 NeuVector Inc. info@neuvector.com 6
CONTINUOUS NETWORK SECURITY FOR CONTAINERS
Chart: NGFW vs Container Firewall Comparison
Next Generation Firewall
Container Firewall
(NGFW)
• Cloud-native
• L7 Stateful Application • L7 Inspection / Isolation
Inspection • Declarative, Automated Policy
• IDS/IPS • Whitelist based
Functions
• User Identity Policies • Scale up / down
• Manual blacklist/whitelist • Internal threat protection
policies
• Other container security
features*
• Host
• Gateway/Edge • East-west + north-south
Deployment
• North-south visibility visibility
• Container ingress and egress
• Container engine (Docker)
• Orchestration (e.g.
• SIEM Kubernetes)
Integration
• CI/CD pipeline
• SIEM
*See Continuous Security below for additional container security features
© 2017 NeuVector Inc. info@neuvector.com 7
CONTINUOUS NETWORK SECURITY FOR CONTAINERS
Key Features of a Web Application Firewall (WAF)
Web application firewalls provide advanced protection for web-based traffic,
typically HTTP/S where traffic from the internet first interacts with the ‘front-end’ of
an application. Most WAFs detect a number of application threats including
the OWASP Top 10.
In general, a web application firewall will include these features:
• Detect Application Attacks. Detect SQL injection, Cross-site scripting (XSS), DDoS,
DNS attacks etc.
• Protocol, Logic, and Object Format Support. JavaScript, SQL, HTML, XML, JSON,
Cookies, etc.
• Support HTTP and HTTPS. Some WAFs will terminate SSL connections, while others
rely on termination by a load balancer in front.
• Virtual Patching. Temporarily ‘patch’ vulnerabilities with network blacklist policies
until application can be patched.
Next Page: WAF vs Container Firewall
© 2017 NeuVector Inc. info@neuvector.com 8
CONTINUOUS NETWORK SECURITY FOR CONTAINERS
Chart: WAF vs Container Firewall Comparison
Web Application Firewall
Container Firewall
(WAF)
• Cloud-native
• HTTP/S web server protection
• Application Intelligence & L7
• Cross-site scripting (XSS), SQL
Inspection
injection, OWASP Top 10, etc.
• Declarative, Automated,
Functions • Advanced inspection of cookies,
Whitelist based Policy
form data, URIs
• Container threat protection
• Virtual patching
• Other container security
• Cloud based signature updates
features*
• Host
• Gateway/Edge • East-west + north-south
Deployment visibility
• North-south visibility
• Container ingress and
egress
• Container engine (Docker)
• Orchestration (e.g.
• SIEM Kubernetes)
Integration
• CI/CD pipeline
• SIEM
*See below for other container security features
© 2017 NeuVector Inc. info@neuvector.com 9
CONTINUOUS NETWORK SECURITY FOR CONTAINERS
Continuous Security for Containers
Like any environment, a containerized environment requires a layered security
strategy with multiple protection layers. It’s critical to build in security throughout
the Build, Ship, and Run cycle. For run-time visibility and protection, a container
firewall plays a central role.
“A container firewall can provide not only network layer inspection and
protection but is also in a unique position to monitor host and container
processes and perform security audits.”
Because of its distributed nature, host-based container firewalls provide efficient
local monitoring and protection. With its integration with the Docker engine and
orchestration and container management tools, a container firewall can also
provide host and container process inspection, security auditing and testing, and
resource monitoring. Container firewalls often contain the following additional
features:
• Host process monitoring and security for privilege escalations, suspicious
processes and breakouts
• Vulnerability scanning in registries, hosts, and running containers
• Auditing and compliance with CIS Benchmarks security tests
• Packet capture for forensics and debugging.
Securing container deployments requires some new technologies such as container
firewalls as well as traditional solutions such as next generation firewalls. For new
virtualized workloads, application intelligence, declarative policies, and integration
with cloud-native orchestration tools are required to monitor and secure them.
See the NeuVector Container Firewall In Action
To learn more about NeuVector:
• Contact us at info@neuvector.com
• Visit us at https://neuvector.com
Schedule a private demo, or request a free trial. We’ll need your Docker hub ID to
enable you to download the NeuVector container.
© 2017 NeuVector Inc. info@neuvector.com 10
You might also like
- Microservices and Container Security Feature Comparison Vendor ScorecardDocument7 pagesMicroservices and Container Security Feature Comparison Vendor ScorecardCognitive UnityNo ratings yet
- Aqua Security Ebook Container Security-10 Things DevOps Need To DoDocument12 pagesAqua Security Ebook Container Security-10 Things DevOps Need To DoJulio Cesar Juan LuisNo ratings yet
- Continuous Kubernetes Security PDFDocument113 pagesContinuous Kubernetes Security PDFtanmayNo ratings yet
- Palo Alto Networks Ebook Prisma Container Security101 PDFDocument8 pagesPalo Alto Networks Ebook Prisma Container Security101 PDFRavi KiranNo ratings yet
- A Guide To Impliment DevSecOpsDocument21 pagesA Guide To Impliment DevSecOpsMuhammad YasinNo ratings yet
- Continuous Deployment for Docker Apps to Kubernetes GuideDocument17 pagesContinuous Deployment for Docker Apps to Kubernetes GuideMiguel CasasNo ratings yet
- Identity-Based Microsegmentation For KubernetesDocument3 pagesIdentity-Based Microsegmentation For KubernetesNapster KingNo ratings yet
- AWS Amazon VPC Connectivity Options PDFDocument31 pagesAWS Amazon VPC Connectivity Options PDFShantanu MukherjeeNo ratings yet
- 10 Things To Get Right For Successful DevSecOpsDocument15 pages10 Things To Get Right For Successful DevSecOpsyns100% (1)
- Kubernetes' Architecture Deep Dive - Umeå May 2019Document62 pagesKubernetes' Architecture Deep Dive - Umeå May 2019Davinder SinghNo ratings yet
- Openshift4 Open19publicsector 190625091340Document51 pagesOpenshift4 Open19publicsector 190625091340Kamal MOULINE100% (1)
- Kubernetes Security GuideDocument64 pagesKubernetes Security Guidesunnyj25No ratings yet
- 06 - Spring Into Kubernetes - Paul CzarkowskiDocument66 pages06 - Spring Into Kubernetes - Paul CzarkowskiKyawzaw AungNo ratings yet
- CI CD Workshop 20200322 v2.0Document18 pagesCI CD Workshop 20200322 v2.0Hussain HarbooshNo ratings yet
- DOP327-R2 - Monitoring and Observability of Serverless Apps Using AWS X-RayDocument22 pagesDOP327-R2 - Monitoring and Observability of Serverless Apps Using AWS X-RayTony100% (1)
- Guidelines Implementing Aws WafDocument28 pagesGuidelines Implementing Aws Waftech zoneNo ratings yet
- Cloud WAF CDN Technical in DepthDocument46 pagesCloud WAF CDN Technical in DepthtuanltNo ratings yet
- Container Security Going Beyond Image ScanningDocument18 pagesContainer Security Going Beyond Image ScanningnicolepetrescuNo ratings yet
- Migration Modernization Strategy For IesDocument30 pagesMigration Modernization Strategy For IesJawhny CookeNo ratings yet
- AWS MicroservicesDocument39 pagesAWS MicroservicesRudrasatyanarayana BattuNo ratings yet
- ShowIT Openshift - Mini OCP - DevOps 20180131 - Jiri - KolarDocument59 pagesShowIT Openshift - Mini OCP - DevOps 20180131 - Jiri - KolarmamoncinNo ratings yet
- DevOps Process Flow PDFDocument1 pageDevOps Process Flow PDFFelipe NahumNo ratings yet
- CIS Kubernetes Benchmark v1.4.1Document254 pagesCIS Kubernetes Benchmark v1.4.1Anonymous 4uxmV5Z4oNo ratings yet
- DevOps Vs DevSecOps Everything You Need To Know!Document9 pagesDevOps Vs DevSecOps Everything You Need To Know!Nife LabsNo ratings yet
- Secure OpenShift Applications W IBM Cloud App IDDocument117 pagesSecure OpenShift Applications W IBM Cloud App IDContus FirmasNo ratings yet
- KuburnetsDocument67 pagesKuburnetsonubeyNo ratings yet
- Advanced Container Security - Jason Umiker - 28jun - FinalDocument68 pagesAdvanced Container Security - Jason Umiker - 28jun - FinalKumar GollapudiNo ratings yet
- 05 - SecurityDocument59 pages05 - SecurityashooNo ratings yet
- Container SecurityDocument37 pagesContainer SecuritysureshchandrhceNo ratings yet
- Docker SecurityDocument8 pagesDocker Securitydeniz bayraktarNo ratings yet
- 16 Transit VPCDocument9 pages16 Transit VPCYNo ratings yet
- Trustwave TPP Palo Alto Next Generation Firewall Deployment ServiceDocument9 pagesTrustwave TPP Palo Alto Next Generation Firewall Deployment Servicefateh tiribarkNo ratings yet
- Software Supply Chain Best Practices: #CncfsecuritytagDocument45 pagesSoftware Supply Chain Best Practices: #CncfsecuritytagmiekNo ratings yet
- Centralizing Kubernetes OperationsDocument24 pagesCentralizing Kubernetes OperationsmillajovavichNo ratings yet
- CIS Kubernetes V1.23 Benchmark V1.0.1 PDFDocument316 pagesCIS Kubernetes V1.23 Benchmark V1.0.1 PDFstalemate97No ratings yet
- Handout Introduction To AWS Services Networking, SecurityDocument20 pagesHandout Introduction To AWS Services Networking, SecurityNishi GuptaNo ratings yet
- Palo Alto User GroupsDocument5 pagesPalo Alto User GroupsRyanb378No ratings yet
- Docker Kubernete For TrainingDocument26 pagesDocker Kubernete For TrainingSwathi GNo ratings yet
- Devopsrecipeswithazure PDFDocument207 pagesDevopsrecipeswithazure PDFBabageedhey Ojo100% (1)
- Kubernetes Security Ebook Tips Tricks Best Practices PDFDocument20 pagesKubernetes Security Ebook Tips Tricks Best Practices PDFSam SonyNo ratings yet
- Doctor-Patient-Webapp - Devops Professional-Capstone Proposal DocumentDocument9 pagesDoctor-Patient-Webapp - Devops Professional-Capstone Proposal Documenthema100% (1)
- Terraform AzureDocument297 pagesTerraform AzurePrasanth RowloNo ratings yet
- AwsDocument47 pagesAwstwister100% (2)
- Dzone Guide - Cloud Development PDFDocument31 pagesDzone Guide - Cloud Development PDFNikolaMilosevicNo ratings yet
- Secrets ManagementDocument19 pagesSecrets ManagementSalah AyoubiNo ratings yet
- PF Aws Container Security Monitoring GuideDocument50 pagesPF Aws Container Security Monitoring GuideSandro MeloNo ratings yet
- CounterBreach DatasheetDocument6 pagesCounterBreach DatasheetmannuxNo ratings yet
- Toolchains 2021Document79 pagesToolchains 2021meong423No ratings yet
- Kubernetes Hardening SecurityDocument12 pagesKubernetes Hardening SecurityVasile IrimiaNo ratings yet
- High Level Design ServiceDocument2 pagesHigh Level Design ServicepruebaNo ratings yet
- Secure Your Cloud Applications: Sander Veenstra Technical Trainer AWSDocument35 pagesSecure Your Cloud Applications: Sander Veenstra Technical Trainer AWSmohit narayanNo ratings yet
- Cisco Firepower Next-Generation Firewall (NGFW) Data Sheet - CiscoDocument37 pagesCisco Firepower Next-Generation Firewall (NGFW) Data Sheet - CiscoRajeev SinghalNo ratings yet
- HashiCorp Terraform-Cloud PDFDocument1 pageHashiCorp Terraform-Cloud PDFShirazNo ratings yet
- Hashicorp Vault On The Aws CloudDocument19 pagesHashicorp Vault On The Aws CloudsarasasasaNo ratings yet
- What S New in OpenShift Container Platform 4-1Document51 pagesWhat S New in OpenShift Container Platform 4-1Scriba S100% (1)
- Nagios 3Document11 pagesNagios 3Bryce Montgomery0% (1)
- Expedition Ver 1.1.0 QuickStartDocument51 pagesExpedition Ver 1.1.0 QuickStartRamya lankacomNo ratings yet
- 3 CR 10payDocument5 pages3 CR 10payashokvardhnNo ratings yet
- 3 CR 10payDocument5 pages3 CR 10payashokvardhnNo ratings yet
- SOC Trainee JDDocument1 pageSOC Trainee JDashokvardhnNo ratings yet
- Usage of Robot Framework in Automation of Functional Test RegressionDocument5 pagesUsage of Robot Framework in Automation of Functional Test RegressionashokvardhnNo ratings yet
- TlsDocument1 pageTlsashokvardhnNo ratings yet
- HttpsDocument1 pageHttpsashokvardhnNo ratings yet
- BESCOM Revised Retail Supply Schedule For FY18Document14 pagesBESCOM Revised Retail Supply Schedule For FY18Aravinda K VNo ratings yet
- An Overview of Software-Defined Network: Presenter: Xitao WenDocument44 pagesAn Overview of Software-Defined Network: Presenter: Xitao WenashokvardhnNo ratings yet
- Where did my packets goDocument50 pagesWhere did my packets gopavaniNo ratings yet
- SRE GoogleDocument1 pageSRE GoogleashokvardhnNo ratings yet
- Attendance Slip KitexDocument1 pageAttendance Slip KitexashokvardhnNo ratings yet
- Robot Framework User GuideDocument163 pagesRobot Framework User GuideashokvardhnNo ratings yet
- Kitex Annual Report - WEB View - 2017-18Document160 pagesKitex Annual Report - WEB View - 2017-18ashokvardhnNo ratings yet
- Container Firewall GuideDocument10 pagesContainer Firewall Guideashokvardhn100% (1)
- Container Firewall GuideDocument10 pagesContainer Firewall Guideashokvardhn100% (1)
- Install OpendaylightDocument1 pageInstall OpendaylightKodoNo ratings yet
- Config Reference KiloDocument773 pagesConfig Reference KiloashokvardhnNo ratings yet
- Unix Commands With File PermissionsDocument15 pagesUnix Commands With File PermissionsashokvardhnNo ratings yet
- CVD Iwandesign Mar2017Document46 pagesCVD Iwandesign Mar2017ashokvardhnNo ratings yet
- VoLTE SIP MO-MT Call Flow PDFDocument14 pagesVoLTE SIP MO-MT Call Flow PDFRiteshNo ratings yet
- Manual Mecury MounainerDocument248 pagesManual Mecury Mounainerarmando_loco83372No ratings yet
- ReddithtmlDocument122 pagesReddithtmlZoya GoelNo ratings yet
- Ericsson RNC Iu PS Link Creation ProceduDocument9 pagesEricsson RNC Iu PS Link Creation ProceduhamidboulahiaNo ratings yet
- My NotaDocument27 pagesMy NotahusnaNo ratings yet
- Scade Display Technical DatasheetDocument4 pagesScade Display Technical DatasheetEswara RaoNo ratings yet
- Using Phonetic Matching To Move Excel Data Into A Visual FoxPro DatabaseDocument19 pagesUsing Phonetic Matching To Move Excel Data Into A Visual FoxPro DatabaseSylvester Alelele100% (2)
- 01 ST1030 Machine Overview - enDocument41 pages01 ST1030 Machine Overview - enMiguel RomoNo ratings yet
- C Programming Language Functions NotesDocument35 pagesC Programming Language Functions NotesnagajaneehaNo ratings yet
- MSS-SP-25 (2013) PDFDocument31 pagesMSS-SP-25 (2013) PDFPubcrawl67% (3)
- Universiti Malaysia Sabah: Aturcaraan Kontrak Dan TaksiranDocument40 pagesUniversiti Malaysia Sabah: Aturcaraan Kontrak Dan Taksiranjackie_9227No ratings yet
- Safety Series Ladders PDFDocument12 pagesSafety Series Ladders PDF_jessecaNo ratings yet
- Questionnaire-Benchmarking of Best HR PracticesDocument13 pagesQuestionnaire-Benchmarking of Best HR PracticesUtkalKhatiwadaNo ratings yet
- Engineering Design Guidelines and Standard DrawingsDocument84 pagesEngineering Design Guidelines and Standard DrawingsUdomsin Wutigulpakdee100% (1)
- Management ReviewDocument17 pagesManagement ReviewRamesh Acharya100% (4)
- Manual Ceberus EcoDocument60 pagesManual Ceberus EcoAad Pupu SaputraNo ratings yet
- Amphenol Relay SocketsDocument33 pagesAmphenol Relay SocketsTHBFLNo ratings yet
- Conventional Zone Interface Module P/N 55-055 and 55-060 2-Wire Detector Compatibility DocumentDocument10 pagesConventional Zone Interface Module P/N 55-055 and 55-060 2-Wire Detector Compatibility DocumentErnesto OtazuNo ratings yet
- Masters Manual Operations Manual For Offshore Service Vessels On The NCSDocument26 pagesMasters Manual Operations Manual For Offshore Service Vessels On The NCSHakim FeghoulNo ratings yet
- 0819 Ewd Standards Self Assessment ChecklistDocument90 pages0819 Ewd Standards Self Assessment Checklistholamundo123No ratings yet
- FAQ - FactoryTalk Historian SE CollectivesDocument2 pagesFAQ - FactoryTalk Historian SE CollectivesjaysonlkhNo ratings yet
- DF11serie Eng Tds PDFDocument14 pagesDF11serie Eng Tds PDFviaxaNo ratings yet
- Comparison IFS Food v7 and IFS Food v6.1 For All Parts of The StandardsDocument49 pagesComparison IFS Food v7 and IFS Food v6.1 For All Parts of The StandardsSzabó TamásNo ratings yet
- Hitachi excavator technical manual overviewDocument6 pagesHitachi excavator technical manual overviewyasirNo ratings yet
- ServiceManual2000 2001 PDFDocument330 pagesServiceManual2000 2001 PDFedson_luiz_6No ratings yet
- Bottom Loading Arms for Safe Petroleum and Chemical TransfersDocument2 pagesBottom Loading Arms for Safe Petroleum and Chemical Transfersjhonarext100% (1)
- Dimension I MiDocument8 pagesDimension I Miismet mehmetiNo ratings yet
- 2015 Ford Figo & Figo Aspire - User ManualDocument244 pages2015 Ford Figo & Figo Aspire - User ManualsachinvasudevNo ratings yet
- CQI-27 Stakeholder Review FinalDocument15 pagesCQI-27 Stakeholder Review FinalSelvaraj Simiyon50% (4)