Professional Documents
Culture Documents
5551232
Uploaded by
pes_krishnaCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
5551232
Uploaded by
pes_krishnaCopyright:
Available Formats
SAPTHAGIRI COLLEGE OF ENGINEERING
# 14/5, Hesarghatta Main Road, Chikkasandra,Bangaluru-560057
Computer Networks Laboratory Manual
For VI Semester B.E (15ECL68)
Student Name: ___________________________
USN :___________________________
Semester & Section: _______________________
Department of Electronics and Communication Engineering
CCN Lab Manual 15ECL68 VI Sem
VTU Syllabus
COMPUTER NETWORKS LABORATORY
(As per the CBCS scheme)
Sub Code: 15ECL68 IA Marks: 20
Hours per Week: 03 Exam Marks: 80
Exam Hours: 03 Credits: 02
Laboratory Experiments
Part A
Simulation experiments using NS2
1. Implement a point – to – point network with four nodes and duplex links between them.
Analyze the network performance by setting the queue size and vary the bandwidth and
find the number of packets dropped.
2. Implement a four node point-to-point network with the links connected as follows: n0
– n2, n1 – n2 and n2 – n3. Apply TCP agent between n0-n3 and UDP between n1-n3.
Apply relevant applications over TCP and UDP agents changing the parameter and
determine the number of packets sent by TCP / UDP.
3. Implement Ethernet LAN using n nodes (6-10), throughput by compare the throughput
by changing the error rate and data rate.
4. Implement Ethernet LAN using n nodes and assign multiple traffic nodes and plot
congestion window for different source / destination.
5. Implement ESS with transmitting nodes in wire-less LAN and obtain the performance
parameters
6. Implementation of Link state routing algorithm
Part B
Implement the following using C
1. Write a program for a HDLC frame to perform the following i) Bit stuffing ii) Character
stuffing
2. Write a program for distance vector algorithm to find suitable path for transmission.
3. Implement Dijkstra’s algorithm to compute the shortest routing path
4. For the given data, use CRC-CCITT polynomial to obtain CRC code. Verify the program
for the cases a. Without error b. With error
5. Implementation of stop and wait protocol and sliding window protocol
6. Write a program for congestion control using Leaky bucket algorithm
Dept of ECE 1 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
TABLE OF CONTENTS
EXP.NO. TITLE OF THE EXPERIMENT
Part A
Introduction to NS2
Implement a point – to – point network with four nodes and duplex links between
1 them. Analyze the network performance by setting the queue size and vary the
bandwidth and find the number of packets dropped.
Implement a four node point-to-point network with the links connected as
follows: n0 – n2, n1 – n2 and n2 – n3. Apply TCP agent between n0-n3 and
2
UDP between n1-n3. Apply relevant applications over TCP and UDP agents
changing the parameter and determine the number of packets sent by TCP / UDP.
Implement Ethernet LAN using n nodes (6-10), throughput by compare the
3 throughput by changing the error rate and data rate.
Implement Ethernet LAN using n nodes and assign multiple traffic nodes and plot
4 congestion window for different source / destination.
Implement ESS with transmitting nodes in wire-less LAN and obtain the
5 performance parameters
6 Implementation of Link state routing algorithm.
Part B
Write a program for a HDLC frame to perform the following i) Bit stuffing ii)
1
Character stuffing
Write a program for distance vector algorithm to find suitable path for
2
transmission.
3 Implement Dijkstra’s algorithm to compute the shortest routing path
For the given data, use CRC-CCITT polynomial to obtain CRC code. Verify the
4
program for the cases a. Without error b. With error
Write a program for congestion control using Leaky bucket algorithm
5
Dept of ECE 2 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
Course objectives:
This course will enable students to:
Choose suitable tools to model a network and understand the protocols at various OSI
reference levels.
Design a suitable network and simulate using a Network simulator tool.
Simulate the networking concepts and protocols using C/C++ programming.
Model the networks for different configurations and analyze the results.
Course outcomes:
On the completion of this laboratory course, the students will be able to:
Choose suitable tool to model a network and understand the protocols at various OSI
reference levels.
Design a suitable network and simulate using a Network simulator tool.
Simulate the networking concepts and protocols using C/C++.
Model the networks for different configuration and analyze the results.
Dept of ECE 3 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
Part A
Simulation using NS2 simulator
Introduction to NS2:
Widely known as NS2, is simply an event driven simulation tool.
Useful in studying the dynamic nature of communication networks.
Simulation of wired as well as wireless network functions and protocols (e.g., routing
algorithms, TCP, UDP) can be done using NS2.
In general, NS2 provides users with a way of specifying such network protocols and
simulating their corresponding behaviors.
Basic Architecture of NS2
Tcl scripting
• Tcl is a general purpose scripting language. [Interpreter]
• Tcl runs on most of the platforms such as Unix, Windows, and Mac.
• The strength of Tcl is its simplicity.
• It is not necessary to declare a data type for variable prior to the usage
Wired TCL Script Components
Create the event scheduler
Open new files & turn on the tracing
Create the nodes
Setup the links
Configure the traffic type (e.g., TCP, UDP, etc)
Dept of ECE 4 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
Set the time of traffic generation (e.g., CBR, FTP)
Terminate the simulation
NS Simulator Preliminaries.
1. Initialization and termination aspects of the ns simulator.
2. Definition of network nodes, links, queues and topology.
3. Definition of agents and of applications.
4. The nam visualization tool.
5. Tracing and random variables.
Initialization and Termination of TCL Script in NS-2
An ns simulation starts with the command
set ns [new Simulator]
Which is thus the first line in the tcl script? This line declares a new variable as using the set
command, you can call this variable as you wish, In general people declares it as ns because
it is an instance of the Simulator class, so an object the code[new Simulator] is indeed the
installation of the class Simulator using the reserved word new.
In order to have output files with data on the simulation (trace files) or files used for
visualization (nam files), we need to create the files using “open” command:
#Open the Trace file set tracefile1 [open out.tr w]
$ns trace-all $tracefile1
#Open the NAM trace file
set namfile [open out.nam w]
$ns namtrace-all $namfile
The above commands creates a dta trace file called “out.tr” and a nam visualization trace file
called “out.nam”.Within the tcl script, these files are not called explicitly by their names,but
instead by pointers that are declared above and called “tracefile1” and “namfile” respectively.
Remark that they begins with a # symbol. The second line open the file “out.tr” to be used for
writing, declared with the letter “w”. The third line uses a simulator method called trace-all
that have as parameter the name of the file where the traces will go.
Dept of ECE 5 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
The last line tells the simulator to record all simulation traces in NAM input format. It also
gives the file name that the trace will be written to later by the command $ns flush-trace.In
our case,this will be the file pointed at by the pointer “$namfile”,i.e the file “out.tr”.
The termination of the program is done using a “finish” procedure.
#Define a ‘finish’ procedure
Proc finish { } {
global ns tracefile1 namfile
$ns flush-trace
Close $tracefile1
Close $namfile
Exec nam out.nam &
E0
}
The word proc declares a procedure in this case called finish and without arguments. The
word global is used to tell that we are using variables declared outside the procedure. The
simulator method “flush-trace” will dump the traces on the respective files. The tcl
command “close” closes the trace files defined before and exec executes the nam program for
visualization. The command exit will ends the application and return the number 0 as status
to the system. Zero is the default for a clean exit. Other values can be used to say that is a exit
because something fails.
At the end of ns program we should call the procedure “finish” and specify at what time the
termination should occur. For example,
$ns at 125.0 “finish”
It will be used to call “finish” at time 125sec.Indeed,the at method of the simulator allows us
to schedule events explicitly.
The simulation can then begin using the command
$ns run
Definition of a network of links and nodes set n0 [$ns node]
The way to define a node is
The node is created which is printed by the variable n0. When we shall refer to that node in
the script we shall thus write $n0.
Dept of ECE 6 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
Once we define several nodes, we can define the links that connect them. An example of a
definition of a link is:
$ns duplex-link $n0 $n2 10Mb 10ms DropTail
Which means that $n0 and $n2 are connected using a bi-directional link that has 10ms of
propagation delay and a capacity of 10Mb per sec for each direction.
To define a directional link instead of a bi-directional one, we should replace “duplex-link”
by “simplex-link”.
In NS, an output queue of a node is implemented as a part of each link whose input is that
node. The definition of the link then includes the way to handle overflow at that queue. In our
case, if the buffer capacity of the output queue is exceeded then the last packet to arrive is
dropped. Many alternative options exist, such as the RED (Random Early Discard)
mechanism, the FQ (Fair Queuing), the DRR (Deficit Round Robin), the stochastic Fair
Queuing (SFQ) and the CBQ (which including a priority and a round-robin scheduler).
In ns, an output queue of a node is implemented as a part of each link whose input is that
node. We should also define the buffer capacity of the queue related to each link. An example
would be:
#set Queue Size of link (n0-n2) to 20
$ns queue-limit $n0 $n2 20
Agents and Applications
We need to define routing (sources, destinations) the agents (protocols) the application that
use them.
FTP over TCP
TCP is a dynamic reliable congestion control protocol. It uses Acknowledgements created by
the destination to know whether packets are well received.
There are number variants of the TCP protocol, such as Tahoe, Reno, NewReno, Vegas. The
type of agent appears in the first line:
set tcp [new Agent/TCP]
The command $ns attach-agent $n0 $tcp defines the source node of the tcp connection.
The command
set sink [new Agent /TCPSink]
Defines the behavior of the destination node of TCP and assigns to it a pointer called sink.
Dept of ECE 7 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
#Setup a UDP connection
set udp [new Agent/UDP]
$ns attach-agent $n1 $udp
set null [new Agent/Null]
$ns attach-agent $n5 $null
$ns connect $udp $null
$udp set fid_2
#setup a CBR over UDP connection
The below shows the definition of a CBR application using a UDP agent
The command $ns attach-agent $n4 $sink defines the destination node. The command $ns
connect $tcp $sink finally makes the TCP connection between the source and destination
nodes.
set cbr [new
Application/Traffic/CBR]
$cbr attach-agent $udp
$cbr set packetsize_ 100
$cbr set rate_ 0.01Mb
$cbr set random_ false
TCP has many parameters with initial fixed defaults values that can be changed if mentioned
explicitly. For example, the default TCP packet size has a size of 1000bytes.This can be
changed to another value, say 552bytes, using the command $tcp set packetSize_ 552.
When we have several flows, we may wish to distinguish them so that we can identify them
with different colors in the visualization part. This is done by the command $tcp set fid_ 1
that assigns to the TCP connection a flow identification of “1”.We shall later give the flow
identification of “2” to the UDP connection.
CBR over UDP
Dept of ECE 8 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
A UDP source and destination is defined in a similar way as in the case of TCP.
Instead of defining the rate in the command $cbr set rate_ 0.01Mb, one can define the time
interval between transmission of packets using the command.
$cbr set interval_ 0.005
The packet size can be set to some value using
$cbr set packetSize_ <packet size>
Scheduling Events
NS is a discrete event based simulation. The tcp script defines when event should occur. The
initializing command set ns [new Simulator] creates an event scheduler, and events are then
scheduled using the format:
$ns at <time> <event>
The scheduler is started when running ns that is through the command $ns run.
The beginning and end of the FTP and CBR application can be done through the following
command
set cbr [new
Application/Traffic/CBR]
$cbr attach-agent $udp
$cbr set packetsize_ 100
$cbr set rate_ 0.01Mb
$cbr set random_ false
TCP has many parameters with initial fixed defaults values that can be changed if mentioned
explicitly. For example, the default TCP packet size has a size of 1000bytes.This can be
changed to another value, say 552bytes, using the command $tcp set packetSize_ 552.
When we have several flows, we may wish to distinguish them so that we can identify them
with different colors in the visualization part. This is done by the command $tcp set fid_ 1
Dept of ECE 9 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
that assigns to the TCP connection a flow identification of “1”.We shall later give the flow
identification of “2” to the UDP connection.
XGRAPH
The xgraph program draws a graph on an x-display given data read from either data file or
from standard input if no files are specified. It can display upto 64 independent data sets
using different colors and line styles for each set. It annotates the graph with a title, axis
labels, grid lines or tick marks, grid labels and a legend.
Trace Format Example
1. An event (+, -, d, r) descriptor
2. Simulation time (in seconds) of that event
3. From node
4. To node (3, 4 identifies the link on which the event occurred)
5. Packet type (in Bytes)
6. Packet size (in Bytes)
7. Flags (appeared as "------" since no flag is set)
8. Flow id (fid) of IPv6 that a user can set for each flow at the input OTcl script. Even
though fid field may not be used in a simulation, users can use this field for analysis
purposes. The fid field is also used when specifying stream color for the NAM
display.
9. Source address in forms of "node.port".
10. Destination address in forms of "node.port".
Dept of ECE 10 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
11. Network layer protocol's packet sequence number. Note that even though UDP
implementations do not use sequence number, NS keeps track of UDP packet
sequence number for analysis purposes.
12. Unique id of the packet
Dept of ECE 11 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
Experiment 1
Aim: Implement a point – to – point network with duplex links between them. Analyze the
network performance by setting the queue size and vary the bandwidth and find the number
of packets dropped.
s1.awk
BEGIN{
count = 0;
}
{
event = $1;
if(event == "d") { count++; }
}
END{
printf("\nNumber of packets dropped is: %d\n", count);
}
s1.tcl
#create new simulation instance
set ns [new Simulator]
#open trace file
set tracefile [open s1.tr w]
$ns trace-all $tracefile
Dept of ECE 12 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
#open nam:animation file
set namfile [open s1.nam w]
$ns namtrace-all $namfile
#define finish procedure to perform at the end of simulation
proc finish {} {
global ns tracefile namfile
$ns flush-trace
#dump all traces and close files
close $tracefile
close $namfile
#execute nam animation file
exec nam s1.nam &
#execute awk file in background
exec awk -f s1.awk s1.tr &
exit 0
}
#create 4 nodes
set n0 [$ns node]
set n1 [$ns node]
set n2 [$ns node]
set n3 [$ns node]
#create labels
$n0 label "TCPSource"
$n3 label "TCPSink"
#set color
$ns color 1 red
#create link between nodes /create topology
$ns duplex-link $n0 $n1 1Mb 10ms DropTail
$ns duplex-link $n1 $n2 1Mb 10ms DropTail
$ns duplex-link $n2 $n3 1Mb 10ms DropTail
#set queue size of N packets between n2 and n3
$ns queue-limit $n2 $n3 5
#create TCP agent and attach to node 0
set tcp [new Agent/TCP]
$ns attach-agent $n0 $tcp
#create TCP sink agent and attach to node 3
set tcpsink [new Agent/TCPSink]
Dept of ECE 13 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
$ns attach-agent $n3 $tcpsink
#create traffic: FTP: create FTP source agent on top of TCP and attach to TCP agent
set ftp [new Application/FTP]
$ftp attach-agent $tcp
#connect TCP agent with TCP sink agent
$ns connect $tcp $tcpsink
#set the color
$tcp set class_ 1
#schedule events
$ns at 0.2 "$ftp start"
$ns at 2.5 "$ftp stop"
$ns at 3.0 "finish"
$ns run
Steps
1) In the command line type gedit s1.awk
2) gedit s1.tcl
3) to run sudo ns s1.tcl
4) Vary the bandwidth from node 0 to 2 and keeping same bandwidth between 2 to 3 and
note down packets dropped.
5) Gedit s1graph and type the above result as below
s1graph
0.25 0
0.50 0
0.75 0
1.00 0
1.25 6
1.50 8
2.00 9
3.00 11
4.00 12
5.00 10
6) xgraph -x "Bandwidth(Mbps)" -y "No of packets dropped" -t "Performance analysis"
s1graph
Dept of ECE 14 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
Experiment 2:
2. Implement a four node point-to-point network with the links connected as follows: n0
– n2, n1 – n2 and n2 – n3. Apply TCP agent between n0-n3 and UDP between n1-n3.
Apply relevant applications over TCP and UDP agents changing the parameter and
determine the number of packets sent by TCP / UDP.
Dept of ECE 15 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
s2.awk
BEGIN {
ctcp = 0;
cudp = 0;
}
{
pkt = $5;
if(pkt == "cbr") { cudp++; }
if(pkt == "tcp") { ctcp++; }
}
END {
printf("\nNo of packets sent\nTcp : %d \n Udp : %d\n", ctcp, cudp);
}
s2.tcl
set ns [new Simulator]
set namfile [open s2.nam w]
$ns namtrace-all $namfile
set tracefile [open s2.tr w]
$ns trace-all $tracefile
proc finish {} {
Dept of ECE 16 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
global ns namfile tracefile
$ns flush-trace
close $namfile
close $tracefile
exec nam s2.nam &
exec awk -f s2.awk s2.tr &
exit 0
}
set n0 [$ns node]
set n1 [$ns node]
set n2 [$ns node]
set n3 [$ns node]
$n0 label "TCP"
$n1 label "UDP"
$n3 label "NULL-TCPSINK"
$ns color 1 red
$ns color 2 blue
$ns duplex-link $n0 $n2 2Mb 10ms DropTail
$ns duplex-link $n1 $n2 2Mb 10ms DropTail
$ns duplex-link $n2 $n3 2.75Mb 20ms DropTail
$ns duplex-link-op $n0 $n2 orient right-down
$ns duplex-link-op $n1 $n2 orient right-up
$ns duplex-link-op $n2 $n3 orient right
set tcp [new Agent/TCP]
$ns attach-agent $n0 $tcp
set tcpsink [new Agent/TCPSink]
$ns attach-agent $n3 $tcpsink
set ftp [new Application/FTP]
$ftp attach-agent $tcp
$ns connect $tcp $tcpsink
#Create a UDP Agent and attach to the node n1
set udp [new Agent/UDP]
$ns attach-agent $n1 $udp
#Create a Null Agent and attach to the node n3
set null [new Agent/Null]
$ns attach-agent $n3 $null
#Create a CBR Traffic source and attach to the UDP Agent
Dept of ECE 17 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
set cbr [new Application/Traffic/CBR]
$cbr attach-agent $udp
#Specify the Packet Size and interval
$cbr set paketSize_ 500
$cbr set interval_ 0.005
#Connect the CBR Traffic source to the Null agent
$ns connect $udp $null
$tcp set class_ 1
$udp set class_ 2 "TCP"
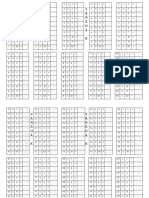
0.25 s2graph
869
$ns at 0.2 "$cbr start" 0.50 1608
$ns at 0.1 "$ftp start" 0.75 2334
$ns at 4.5 "$cbr stop" 1.00 3066
$ns at 4.4 "$ftp stop" 1.25 3780
$ns at 5.0 "finish" 1.50 4500
$ns run 1.75 5220
2.00 5940
2.25 6642
Output 2.50 7110
gedit s2.awk 2.75 7110
gedit s2.tcl
sudo ns s2.tcl "CBR"
Vary bandwidth and note down results 0.25 4478
0.50 5166
No of packets sent 0.75 5166
Tcp : 5940 1.00 5166
Udp : 5166 1.25 5166
1.50 5166
gedit s2graph 1.75 5166
2.00 5166
2.25 5166
2.50 5166
2.75 5166
#xgraph -x "Bandwidth(Mbps)" -y "No of packets sent" -t "Performance analysis" s2graph
Dept of ECE 18 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
Experiment 3
Implement Ethernet LAN using n nodes (6-10), change error rate and data rate and
compare throughput.
Dept of ECE 19 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
s3.awk
BEGIN {
sSize = 0;
startTime = 5.0;
stopTime = 0.1;
Tput = 0;
}
{
event = $1;
time = $2;
size = $6;
if(event == "+")
{
if(time < startTime)
{
startTime = time;
}
}
if(event == "r")
{
if(time > stopTime)
{
stopTime = time;
}
sSize += size;
}
Tput = (sSize / (stopTime-startTime))*(8/1000);
printf("%f\t%.2f\n", time, Tput);
}
END {
}
s3.tcl
set ns [new Simulator]
set namfile [open s3.nam w]
$ns namtrace-all $namfile
set tracefile [open s3.tr w]
$ns trace-all $tracefile
proc finish {} {
global ns namfile tracefile
$ns flush-trace
close $namfile
close $tracefile
exec nam s3.nam &
Dept of ECE 20 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
exec awk -f s3.awk s3.tr > s3graph &
exit 0
}
set n0 [$ns node]
set n1 [$ns node]
set n2 [$ns node]
set n3 [$ns node]
set n4 [$ns node]
set n5 [$ns node]
set n6 [$ns node]
$n0 label "TCPSource"
$n6 label "TCPSink"
$ns color 1 red
$n0 color blue
$n6 color orange
$ns duplex-link $n0 $n1 3Mb 20ms DropTail
$ns make-lan "$n1 $n2 $n3 $n4 $n5 $n6" 2Mb 40ms LL Queue/DropTail Mac/802_3
$ns duplex-link-op $n0 $n1 orient right
set tcp [new Agent/TCP]
$ns attach-agent $n0 $tcp
$tcp set class_ 1
set tcpsink [new Agent/TCPSink]
$ns attach-agent $n6 $tcpsink
set ftp [new Application/FTP]
$ftp attach-agent $tcp
$ns connect $tcp $tcpsink
$ns at 1.0 "$ftp start"
$ns at 5.0 "$ftp stop"
$ns at 5.5 "finish"
$ns run
Output:
#gedit s3.tcl
#sudo ns s3.tcl
Dept of ECE 21 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
#xgraph –x “Time” –y “Throughput” –t “Performance analysis” s3graph
cwnd trace file example
0.00000 2 0 1 0 cwnd_ 1.000
(1) (2) (3) (4) (5) (6) (7)
1. Timestamp
2. Source node id of the flow
3. Source port id
4. Destination node id of the flow
5. Destination port id
6. Name of the variable being traced (cwnd_ , t_seqno_ , throughput, reverse_feedback)
7. Value of the traced variable
Dept of ECE 22 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
Experiment 4
Simulate an Ethernet LAN using n nodes and set multiple traffic nodes and plot
congestion window for different source / destination.
s4.awk
BEGIN {
}
{
if($6 == "cwnd_")
{
printf("%f\t%f\n", $1, $7);
}
}
END {
}
s4.tcl
set ns [new Simulator]
set namfile [open s4.nam w]
$ns namtrace-all $namfile
Dept of ECE 23 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
set tracefile [open s4.tr w]
$ns trace-all $tracefile
proc finish {} {
global ns namfile tracefile
$ns flush-trace
close $namfile
close $tracefile
exec nam s4.nam &
exec awk -f s4.awk cwnd1.tr > tcp1 &
exec awk -f s4.awk cwnd2.tr > tcp2 &
exit 0
}
set n0 [$ns node]
set n1 [$ns node]
set n2 [$ns node]
set n3 [$ns node]
set n4 [$ns node]
set n5 [$ns node]
set n6 [$ns node]
set n7 [$ns node]
set n8 [$ns node]
$ns color 1 Blue
$ns color 2 Red
$n7 shape box
$n7 color Blue
$n8 shape hexagon
$n8 color Red
$ns duplex-link $n1 $n0 2Mb 10ms DropTail
$ns duplex-link $n2 $n0 2Mb 10ms DropTail
$ns duplex-link $n0 $n3 1Mb 20ms DropTail
$ns make-lan "$n3 $n4 $n5 $n6 $n7 $n8" 512Kb 40ms LL Queue/DropTail Mac/802_3
$ns duplex-link-op $n1 $n0 orient right-down
$ns duplex-link-op $n2 $n0 orient right-up
$ns duplex-link-op $n0 $n3 orient right
$ns queue-limit $n0 $n3 20
set tcp1 [new Agent/TCP/Vegas]
$ns attach-agent $n1 $tcp1
set sink1 [new Agent/TCPSink]
$ns attach-agent $n7 $sink1
Dept of ECE 24 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
set ftp1 [new Application/FTP]
$ftp1 attach-agent $tcp1
$ns connect $tcp1 $sink1
$tcp1 set class_ 1
$tcp1 set packetSize_ 55
set tfile1 [open cwnd1.tr w]
$tcp1 attach $tfile1
$tcp1 trace cwnd_
set tcp2 [new Agent/TCP/Reno]
$ns attach-agent $n2 $tcp2
set sink2 [new Agent/TCPSink]
$ns attach-agent $n8 $sink2
set ftp2 [new Application/FTP]
$ftp2 attach-agent $tcp2
$ns connect $tcp2 $sink2
$tcp2 set class_ 2
$tcp2 set packetSize_ 55
set tfile2 [open cwnd2.tr w]
$tcp2 attach $tfile2
$tcp2 trace cwnd_
$ns at 0.5 "$ftp1 start"
$ns at 1.0 "$ftp2 start"
$ns at 5.0 "$ftp2 stop"
$ns at 5.0 "$ftp1 stop"
$ns at 5.5 "finish"
$ns run
Output
#gedit s4.tcl
#sudo ns s4.tcl
#awk -f s4.awk cwnd1.tr > tcp1
#xgraph -x "Time(sec)" -y "CongestionWindowSize" -t "Congestion Window graph for
TCP1" tcp1
Dept of ECE 25 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
#awk -f s4.awk cwnd2.tr > tcp2
#xgraph -x "Time(sec)" -y "CongestionWindowSize" -t "Congestion Window graph for
TCP2" tcp2
Dept of ECE 26 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
Implement Ethernet LAN using n nodes and assign multiple traffic nodes and plot congestion
window for different source / destination.
5. Simulate simple ESS and with transmitting nodes in wire-less LAN by simulation and
determine the performance with respect to transmission of packets.
s5.awk
BEGIN{
PacketRcvd = 0;
Throughput = 0.0;
}
{
if(($1 == "r")&&($3 == "_3_")&&($4 == "AGT")&&($7 == "tcp")&&($8 > 1000))
{
PacketRcvd++;
}
}
END {
Throughput = ((PacketRcvd*1000*8) / (95.0*1000000));
printf("\nThe throughput is:%f\n", Throughput);
}
s6.tcl
set ns [new Simulator]
Dept of ECE 27 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
set tracefile [open s5.tr w]
$ns trace-all $tracefile
set namfile [open s5.nam w]
$ns namtrace-all-wireless $namfile 750 750
proc finish {} {
global ns tracefile namfile
$ns flush-trace
close $tracefile
close $namfile
exec nam s5.nam &
exec awk -f s5.awk s5.tr &
exit 0
}
#get the number of nodes value from the user
set val(nn) 5
#create new topography object
set topo [new Topography]
$topo load_flatgrid 750 750
#Configure the nodes
$ns node-config -adhocRouting AODV \
-llType LL \
-macType Mac/802_11 \
-ifqType Queue/DropTail \
-channelType Channel/WirelessChannel \
-propType Propagation/TwoRayGround \
-antType Antenna/OmniAntenna \
-ifqLen 50 \
-phyType Phy/WirelessPhy \
-topoInstance $topo \
-agentTrace ON \
-routerTrace ON \
-macTrace OFF \
-movementTrace ON
#general operational descriptor storing the hop details in the network
set god_ [create-god $val(nn)]
#create mobile nodes
for {set i 0} {$i < $val(nn)} {incr i} {
set n($i) [$ns node]
}
#label node
$n(1) label "TCPSource"
$n(3) label "Sink"
Dept of ECE 28 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
#Randomly placing the nodes
for {set i 0} {$i < $val(nn)} {incr i} {
set XX [expr rand()*750]
set YY [expr rand()*750]
$n($i) set X_ $XX
$n($i) set Y_ $YY
}
#define the initial position for the nodes
for {set i 0} {$i < $val(nn)} {incr i} {
$ns initial_node_pos $n($i) 100
}
#define the destination procedure to set the destination to each node
proc destination {} {
global ns val n
set now [$ns now]
set time 5.0
for {set i 0} {$i < $val(nn)} {incr i} {
set XX [expr rand()*750]
set YY [expr rand()*750]
$ns at [expr $now + $time] "$n($i) setdest $XX $YY 20.0"
}
$ns at [expr $now + $time] "destination"
}
set tcp [new Agent/TCP]
$ns attach-agent $n(1) $tcp
set ftp [new Application/FTP]
$ftp attach-agent $tcp
set sink [new Agent/TCPSink]
$ns attach-agent $n(3) $sink
$ns connect $tcp $sink
$ns at 0.0 "destination"
$ns at 1.0 "$ftp start"
$ns at 100 "finish"
$ns run
Output
#gedit s5.tcl
#sudo ns s5.tcl 5
The throughput is: 0.579368
Dept of ECE 29 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
Experiment 6
Aim: Implementation of Link state routing algorithm.
set ns [new Simulator]
set namfile [open s6.nam w]
$ns namtrace-all $namfile
set tracefile [open s6.tr w]
$ns trace-all $tracefile
proc finish {} {
global ns namfile tracefile
$ns flush-trace
close $namfile
close $tracefile
exec nam s6.nam &
exit 0
}
set n0 [$ns node]
set n1 [$ns node]
set n2 [$ns node]
set n3 [$ns node]
set n4 [$ns node]
$ns duplex-link $n0 $n1 1Mb 10ms DropTail
$ns duplex-link $n0 $n2 1Mb 10ms DropTail
$ns duplex-link $n0 $n3 1Mb 10ms DropTail
$ns duplex-link $n1 $n2 1Mb 10ms DropTail
$ns duplex-link $n1 $n4 1Mb 10ms DropTail
$ns duplex-link $n2 $n4 1Mb 10ms DropTail
$ns duplex-link-op $n0 $n1 orient right
$ns duplex-link-op $n0 $n2 orient right-down
$ns duplex-link-op $n0 $n3 orient down
$ns duplex-link-op $n1 $n2 orient left-down
$ns duplex-link-op $n1 $n4 orient down
$ns duplex-link-op $n2 $n4 orient right-down
Dept of ECE 30 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
set udp0 [new Agent/UDP]
$ns attach-agent $n0 $udp0
set cbr0 [new Application/Traffic/CBR]
$cbr0 set packetSize_ 500
$cbr0 set interval_ 0.005
$cbr0 attach-agent $udp0
set null0 [new Agent/Null]
$ns attach-agent $n4 $null0
$ns connect $udp0 $null0
set udp1 [new Agent/UDP]
$ns attach-agent $n2 $udp1
set cbr1 [new Application/Traffic/CBR]
$cbr1 set packetSize_ 500
$cbr1 set interval_ 0.005
$cbr1 attach-agent $udp1
set null0 [new Agent/Null]
$ns attach-agent $n4 $null0
$ns connect $udp1 $null0
$ns rtproto LS
$ns rtmodel-at 20.0 down $n1 $n4
$ns rtmodel-at 20.0 up $n1 $n4
$ns rtmodel-at 25.0 down $n2 $n4
$ns rtmodel-at 40.0 up $n2 $n4
$udp0 set class_ 1
$udp1 set class_ 2
$ns color 1 Red
$ns color 2 Green
$ns at 1.0 "$cbr0 start"
$ns at 2.0 "$cbr1 start"
$ns at 45 "finish"
$ns run
Output
#gedit s6.tcl
#sudo ns s6.tcl
Dept of ECE 31 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
Dept of ECE 32 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
Part B
1. Write a program for a HLDC frame to perform the following.
i) Bit stuffing
ii) Character stuffing.
BIT STUFFING
#include<string.h>
#include<stdio.h>
main()
{
char a[20],fs[50]="",t[6],r[5];
int i,j,p=0,q=0;
printf("enter bit string : ");
scanf("%s",a);
strcat(fs,"01111110");
if(strlen(a)<5)
{
strcat(fs,a);
}
else
{
for(i=0;i<strlen(a)-4;i++)
{
for(j=i;j<i+5;j++)
{
t[p++]=a[j];
}
t[p]='\0';
if(strcmp(t,"11111")==0)
{
strcat(fs,"111110");
i=j-1;
}
else
{
r[0]=a[i];
r[1]='\0';
strcat(fs,r);
}
p=0;
}
for(q=i;q<strlen(a);q++)
{
t[p++]=a[q];
}
t[p]='\0';
Dept of ECE 33 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
strcat(fs,t);
}
strcat(fs,"01111110");
printf("After stuffing : %s",fs);
getch();
}
CHARACTER OR BYTE STUFFING
#include<string.h>
#include<stdio.h>
main()
{
char a[30],fs[50]="",t[3],sd,ed,x[3],s[3],d[3],y[3];
int i,j,p=0,q=0;
printf("Enter characters to be stuffed : ");
scanf("%s",a);
printf("\nEnter a character that represents starting delimiter : ");
scanf(" %c",&sd);
printf("\nEnter a character that represents ending delimiter : ");
scanf(" %c",&ed);
x[0]=s[0]=s[1]=sd;
x[1]=s[2]='\0';
y[0]=d[0]=d[1]=ed;
d[2]=y[1]='\0';
strcat(fs,x);
for(i=0;i<strlen(a);i++)
{
t[0]=a[i];
t[1]='\0';
if(t[0]==sd)
strcat(fs,s);
else
if(t[0]==ed)
strcat(fs,d);
else
strcat(fs,t);
}
strcat(fs,y);
printf("\nAfter stuffing : %s",fs);
getch();
}
Dept of ECE 34 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
2. Write a program for distance vector algorithm to find suitable path for
transmission.
#include<stdio.h>
int n, e, s[20][20], graph[20][20];
void initialize()
{
int i, j;
for (i = 1; i <= 20; i++)
for (j = 1; j <= 20 && (s[i][j] = graph[i][j] = 0); j++);
}
void getgraph()
{
int i, strt, end;
printf("Enter no. of routers & edges in the graph: ");
scanf("%d%d", &n, &e);
while (e-- > 0)
{
printf("Enter start router -> end router : ");
scanf("%d%d", &strt, &end);
graph[strt][end] = graph[end][strt] = 1;
}
}
void gettable(int src)
{
int i, j;
printf("Enter information for Source router %d.\n", src);
for (i = 1; i <= n; i++)
if (graph[src][i] == 1)
{
printf("Enter distance from source router %d to %d :", src, i);
scanf("%d", &s[src][i]);
}
printf("Enter the contents of Echo packetof Adacentj routers of %d\n",src);
for (i = 1; i <= n; i++)
if (graph[src][i] == 1)
{
printf("Enter the contents of Echo packet of router %d.\n", i);
for (j = 1; j <= n; j++)
{
if (i == j) continue;
printf("Enter distance from router %d to %d :", i, j);
scanf("%d", &s[i][j]);
}
}
}
void process(int src, int dest)
{
int min = 999, i, delay, via;
for (i = 1; i <= n; i++)
Dept of ECE 35 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
if (graph[src][i] == 1)
{
delay = s[src][i] + s[i][dest];
if (delay < min)
{
min = delay;
via = i;
}
}
printf("Suitable path from router %d to %d is through router %d with delay %d units\n", src,
dest, via, min);
}
int main()
{
int src, dest;
initialize();
getgraph();
printf("Enter the Source & Destination router\n");
scanf("%d%d", &src, &dest);
gettable(src);
process(src, dest);
return 0;
}
3. Implement Dijkstra’s algorithm to compute the shortest routing path.
#include<stdio.h>
void sort(void);
static int dsp[10][10],nodes;
struct{
char src;
char dest;
int length;
}stemp,permanent[10]={' ',' ',0},temp[10]={' ',' ',-1};
static int perm,tem;
void main()
{
int i,j,k,l,m,n=0,point;
char initial,dest,path[10]={' '};
printf("\t\t Shortest Path (Dijkstra's algorithm)");
printf("\n*******************************************************");
printf("\nEnter the number of nodes:");
scanf("%d",&nodes);
Dept of ECE 36 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
printf("\nEnter the adjacency matrix for the graph:\n");
for(i=0;i<nodes;i++)
{
for(j=0;j<nodes;j++)
scanf("%d",&dsp[i][j]);
}
fflush(stdin);
printf("\n enter the source node:");
scanf("%c",&initial);fflush(stdin);
printf("\n Enter the destination node:");
scanf("%c",&dest);
permanent[perm].src=initial;
permanent[perm].dest=initial;
permanent[perm++].length=0;
i=permanent[perm-1].dest-97;
for(j=0;j<nodes;j++)
{
if(i!=j)
{
if(dsp[i][j]>0)
{
temp[tem].src=permanent[perm-1].src;
temp[tem].dest=j+97;
temp[tem++].length=dsp[i][j];
}
}
}
sort();
while(tem>=0)
{
j=permanent[perm-1].dest-97;
for(i=0;i<nodes;i++)
{
if(i!=initial-97)
{
if(dsp[j][i]>0)
{
l=-1;
for(k=0;k<perm;k++)
{
if(permanent[k].dest==(i+97))
l=k;
}
for(k=0;k<=tem;k++)
{
if(temp[k].dest==(i+97))
l=k;
Dept of ECE 37 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
}
if(l<0)
{
temp[tem].src=j+97;
temp[tem].dest=i+97;
for(m=0;m<perm;m++)
{
if(permanent[m].dest==temp[tem].src)
n=permanent[m].length;
}
temp[tem++].length=dsp[j][i]+n;
}
else
{
for(m=0;m<perm;m++)
{
if(permanent[m].dest==j+97)
{
n=permanent[m].length+dsp[j][i];break;
}
else
n=dsp[j][i];
}
if((n<temp[l].length))
{
temp[l].length=n;
temp[l].src=j+97;
temp[l].dest=i+97;
}
}
}
}
}
sort();
}
printf("\nShortest path:\n");
printf("From %c to %c is:",initial,dest);
for(i=0;i<perm-1;i++)
{
if(permanent[i].dest==dest)
{
point=i;n=i; break;
}
} i=0;
for(j=perm;j>0;j--)
{
if(permanent[j-1].dest==permanent[point].src)
Dept of ECE 38 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
{
path[i++]=permanent[point].dest;
point=j-1;
}
}
path[i]=initial;
for(j=i;j>=0;j--)
printf("%c ",path[j]);
printf("\t length=%d",permanent[n].length);
getch();
}
void sort()
{
int i,j,k;
for(i=0;i<=tem;i++)
{
k=1;
for(j=0;j<=tem;j++)
{
if((temp[j].length <= temp[j+1].length))
{
stemp=temp[j];
temp[j]=temp[j+1];
temp[j+1]=stemp; k=0;
}
}
if(k)
break;
}
4. For the given data, use CRC-CCITT polynomial to obtain CRC code. Verify the
program for the cases
a. Without error
b. With error
Dept of ECE 39 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
All computations are done in modulo 2
Algorithm
1. Given a bit string, append 0S to the end of it (the number of 0s is the same as the degree of the
generator polynomial) let B(x) be the polynomial corresponding to B.
2. Divide B(x) by some agreed on polynomial G(x) (generator polynomial) and determine the
remainder R(x). This division is to be done using Modulo 2 Division.
3. Define T(x) = B(x) –R(x)
(T(x)/G(x) => remainder 0)
4. Transmit T, the bit string corresponding to T(x).
5. Let T’ represent the bit stream the receiver gets and T’(x) the associated polynomial.
The receiver divides T1(x) by G(x). If there is a 0 remainder, the receiver concludes T = T’ and
no error occurred otherwise, the receiver concludes an error occurred and requires a
retransmission.
#include<stdio.h>
int a[100],b[100],i,j,len,k,count=0;
//Generator Polynomial:g(x)=x^16+x^12+x^5+1
int gp[]={1,0,0,0,1,0,0,0,0,0,0,1,0,0,0,0,1,};
int main()
{
void div();
printf("\nEnter the length of Data Frame :");
scanf("%d",&len);
printf("\nEnter the Message :");
for(i=0;i<len;i++)
scanf("%d",&a[i]);
//Append r(16) degree Zeros to Msg bits
for(i=0;i<16;i++)
a[len++]=0;
//Xr.M(x) (ie. Msg+16 Zeros)
for(i=0;i<len;i++)
b[i]=a[i];
//No of times to be divided ie. Msg Length
k=len-16;
div();
for(i=0;i<len;i++)
b[i]=b[i]^a[i]; //MOD 2 Substraction
printf("\nData to be transmitted : ");
for(i=0;i<len;i++)
Dept of ECE 40 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
printf("%2d",b[i]);
printf("\n\nEnter the Reveived Data : ");
for(i=0;i<len;i++)
scanf("%d",&a[i]);
div();
for(i=0;i<len;i++)
if(a[i]!=0)
{
printf("\nERROR in Recived Data");
return 0;
}
printf("\nData Recived is ERROR FREE");
}
void div()
{
for(i=0;i<k;i++)
{
if(a[i]==gp[0])
{
for(j=i;j<17+i;j++)
a[j]=a[j]^gp[count++];
}
count=0;
}
}
5. Implementation of Stop and Wait Protocol and Sliding Window Protocol
Stop and Wait Protocol
#include<stdio.h>
#include<conio.h>
#include<stdlib.h>
void main()
{
int i,j,noframes,x,x2;
// clrscr();
//for(i=0;i<2;i++)
// rand();
noframes=10;
i=1;
j=1;
//noframes=noframes/8;
Dept of ECE 41 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
printf("number of frames is %d ",noframes);
// scanf("%d",&noframes);
getch();
while(noframes>0)
{
printf("\nsending frames is %d",i);
// srand(x1++);
x=rand()%15;
if(x%5==0)
{
for(x2=1;x2<2;x2++)
{
printf("\n waiting for %d seconds\n",x2);
sleep(x2);
}
printf("\n sending frames %d\n",i);
//srand(x1++);
x=rand()%10;
}
printf("\n ack for frame %d\n",j);
noframes=noframes-1;
i++;
j++;
}
printf("\n end of stop and wait protocol\n");
Sliding Window Protocol
#include<stdio.h>
int main()
{
int w,i,f,frames[50];
printf("Enter window size: ");
scanf("%d",&w);
printf("\nEnter number of frames to transmit: ");
scanf("%d",&f);
printf("\nEnter %d frames: ",f);
for(i=1;i<=f;i++)
scanf("%d",&frames[i]);
printf("\nWith sliding window protocol the frames will be sent in the following manner
(assuming no corruption of frames)\n\n");
Dept of ECE 42 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
printf("After sending %d frames at each stage sender waits for acknowledgement sent by
the receiver\n\n",w);
for(i=1;i<=f;i++)
{
if(i%w==0)
{
printf("%d\n",frames[i]);
printf("Acknowledgement of above frames sent is received by sender\n\n");
}
else
printf("%d ",frames[i]);
}
if(f%w!=0)
printf("\nAcknowledgement of above frames sent is received by sender\n");
return 0;
}
6. Write a program for congestion control using leaky bucket algorithm.
Theory
The congesting control algorithms are basically divided into two groups: open loop and closed
loop. Open loop solutions attempt to solve the problem by good design, in essence, to make sure
it does not occur in the first place. Once the system is up and running, midcourse corrections are
not made. Open loop algorithms are further divided into ones that act at source versus ones that
act at the destination. In contrast, closed loop solutions are based on the concept of a feedback
loop if there is any congestion. Closed loop algorithms are also divided into two sub categories:
explicit feedback and implicit feedback. In explicit feedback algorithms, packets are sent back
from the point of congestion to warn the source. In implicit algorithm, the source deduces the
existence of congestion by making local observation, such as the time needed for
acknowledgment to come back.
The presence of congestion means that the load is (temporarily) greater than the resources (in part
of the system) can handle. For subnets that use virtual circuits internally, these methods can be
used at the network layer. Another open loop method to help manage congestion is forcing the
packet to be transmitted at a more predictable rate. This approach to congestion management is
widely used in ATM networks and is called traffic shaping.
The other method is the leaky bucket algorithm. Each host is connected to the network by an
interface containing a leaky bucket, that is, a finite internal queue. If a packet arrives at the queue
when it is full, the packet is discarded. In other words, if one or more process are already queued,
the new packet is unceremoniously discarded. This arrangement can be built into the hardware
interface or simulate d by the host operating system. In fact it is nothing other than a single server
queuing system with constant service time.
Dept of ECE 43 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
The host is allowed to put one packet per clock tick onto the network. This mechanism turns an
uneven flow of packet from the user process inside the host into an even flow of packet onto the
network, smoothing out bursts and greatly reducing the chances of congestion.
LEAKY BUCKET
#include<stdio.h>
#include<stdlib.h>
#define MIN(x,y) (x>y)?y:x
int main()
{
int orate,drop=0,cap,x,count=0,inp[10]={0},i=0,nsec,ch;
printf("\n enter bucket size : ");
scanf("%d",&cap);
printf("\n enter output rate :");
scanf("%d",&orate);
do
{
printf("\n enter number of packets coming at second %d :",i+1);
scanf("%d",&inp[i]);
i++;
printf("\n enter 1 to contiue or 0 to quit..........");
scanf("%d",&ch);
}
while(ch);
nsec=i;
printf("\n second \t recieved \t sent \t dropped \t remained \n");
for(i=0;count || i<nsec;i++)
{
printf(" %d",i+1);
printf(" \t%d\t ",inp[i]);
printf(" \t %d\t ",MIN((inp[i]+count),orate));
if((x=inp[i]+count-orate)>0)
Dept of ECE 44 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
{
if(x>cap)
{
count=cap;
drop=x-cap;
}
else
{
count=x;
drop=0;
}
}
else
{
drop=0;
count=0;
}
printf(" \t %d \t %d \n",drop,count);
}
return 0;
}
Viva Questions
1. Explain the functions of OSI layers ?
2. Differentiate between TCP/IP Layers and OSI Layers
3. Why header is required?
4. What is the use of adding header and trailer to frames?
5. What is encapsulation?
6. Why fragmentation requires?
7. What is MTU?
8. Which layer imposes MTU?
9. Differentiate between flow control and congestion control.
10. Differentiate between Point-to-Point Connection and End-to-End connections.
11. What are protocols running in different layers?
12. What is Protocol Stack?
13. Differentiate between TCP and UDP.
14. Differentiate between Connectionless and connection oriented connection.
15. Why frame sorting is required?
16. What is meant by subnet?
17. What is meant by Gateway?
18. What is an IP address?
19. What is MAC address?
20. Why IP address is required when we have MAC address?
21. What is meant by port?
22. What are ephemerical port number and well known port numbers?
23. What is a socket?
24. What are the parameters of socket()?
25. Describe bind(), listen(), accept(),connect(), send() and recv().
26. What are system calls? Mention few of them.
Dept of ECE 45 SCE,Bangalore
CCN Lab Manual 15ECL68 VI Sem
27. What is IPC? Name three techniques.
28. Explain mkfifo(), open(), close() with parameters.
29. What is meant by file descriptor?
30. What is meant by traffic shaping?
31. How do you classify congestion control algorithms?
32. Differentiate between Leaky bucket and Token bucket.
33. How do you implement Leaky bucket?
34. How do you generate bursty traffic?
35. What is the polynomial used in CRC-CCITT?
36. What are the other error detection algorithms?
37. What is difference between CRC and Hamming code?
38. Why Hamming code is called 7,4 code?
39. What is odd parity and even parity?
40. What is meant by syndrome?
41. What is generator matrix?
42. What are Routing algorithms?
43. How do you classify routing algorithms? Give examples for each.
44. What are drawbacks in distance vector algorithm?
45. How routers update distances to each of its neighbor?
Dept of ECE 46 SCE,Bangalore
You might also like
- LabDocument86 pagesLabSalman ShariffNo ratings yet
- LabDocument86 pagesLabsalman shariffNo ratings yet
- Computer Network LaboratorynewDocument63 pagesComputer Network LaboratorynewDeepa JerinNo ratings yet
- CN Lab Manual Ece New MittDocument54 pagesCN Lab Manual Ece New MittNandan NagarajNo ratings yet
- CN Lab Manual VTUDocument68 pagesCN Lab Manual VTUSamarth YadavNo ratings yet
- QMP 7.1 D/F Network Lab ManualDocument64 pagesQMP 7.1 D/F Network Lab Manualget_togetherNo ratings yet
- Network Laboratory: Department of Computer Science & EngineeringDocument77 pagesNetwork Laboratory: Department of Computer Science & EngineeringkarthickamsecNo ratings yet
- CN Lab Manual 2023 24Document41 pagesCN Lab Manual 2023 24sanjayv7210No ratings yet
- COMPUTER NETWORK LAB MANUAL NewDocument64 pagesCOMPUTER NETWORK LAB MANUAL NewprachiNo ratings yet
- CN Lab Manual 2023 24Document44 pagesCN Lab Manual 2023 24sowbhagyasow17No ratings yet
- Lab Manual of Nsit PDFDocument63 pagesLab Manual of Nsit PDFPranav JainNo ratings yet
- CN Lab ManualDocument62 pagesCN Lab ManualAmol MNo ratings yet
- CN Lab ManualDocument57 pagesCN Lab ManualMohammad Ismail NaazNo ratings yet
- CN Lab ManualDocument74 pagesCN Lab Manual6019 - Kamalakar.SNo ratings yet
- LAB Manual: EC8563 - Communication Networks LaboratoryDocument48 pagesLAB Manual: EC8563 - Communication Networks LaboratoryAshok KumarNo ratings yet
- CCN Lab Manual For 6sem PDFDocument32 pagesCCN Lab Manual For 6sem PDFKiran kd0% (1)
- CN Manual (5th Sem)Document44 pagesCN Manual (5th Sem)vaishuteju12No ratings yet
- 18csl57 Cn@Azdocuments - inDocument99 pages18csl57 Cn@Azdocuments - in4GH19CS045 Shashikumar H CNo ratings yet
- CCN Lab Manual-2022 Cycle 1Document29 pagesCCN Lab Manual-2022 Cycle 1LitlatohNo ratings yet
- Computer Networks Lab Manual GuideDocument60 pagesComputer Networks Lab Manual GuideJ ShankarNo ratings yet
- CN ManualDocument57 pagesCN Manualwavovaf945No ratings yet
- Computer Networks Lab Manual and VIVA QuestionsDocument46 pagesComputer Networks Lab Manual and VIVA QuestionsHarryNo ratings yet
- CN Lab9900Document42 pagesCN Lab9900sriharshapatilsbNo ratings yet
- CN Lab 15csl57 Lab ManualDocument49 pagesCN Lab 15csl57 Lab ManualKomal Pallu Sajjan0% (2)
- Computer Networks LabDocument49 pagesComputer Networks LabKumar KumarNo ratings yet
- Introduction to Network Simulator-2 (NS2Document83 pagesIntroduction to Network Simulator-2 (NS21dt19cs056 HemanthNo ratings yet
- Network Simulators IntroductionDocument43 pagesNetwork Simulators IntroductionRavi kumarNo ratings yet
- Computer Networks Lab ManualDocument76 pagesComputer Networks Lab ManualarunasekaranNo ratings yet
- Computer Networks Lab Manual - 14!01!2020Document122 pagesComputer Networks Lab Manual - 14!01!2020AdministerNo ratings yet
- Bangalore Institute of Technology: Affiliated To Visvesvaraya Technological UniversityDocument56 pagesBangalore Institute of Technology: Affiliated To Visvesvaraya Technological Universityfilthy_dlNo ratings yet
- Cn Lab Manual 2023 2Document70 pagesCn Lab Manual 2023 2smileygen123No ratings yet
- CN Lab ManualDocument71 pagesCN Lab ManualmanasisomanNo ratings yet
- Computer Networks Lab Manual: V SemesterDocument53 pagesComputer Networks Lab Manual: V SemesterGanesanDhandapaniNo ratings yet
- Expt No 6. CNDocument6 pagesExpt No 6. CNAnil BegarNo ratings yet
- Syllabus and ManualCBCSDocument64 pagesSyllabus and ManualCBCSPreethuraj RoyNo ratings yet
- Computer Network FileDocument14 pagesComputer Network File046Harmehar KaurNo ratings yet
- YENEPOYA INSTITUTE OF TECHNOLOGY COMPUTER NETWORKS LAB MANUALDocument52 pagesYENEPOYA INSTITUTE OF TECHNOLOGY COMPUTER NETWORKS LAB MANUALAV VNo ratings yet
- Computer Networks Lab Manual - 14-01-2020Document122 pagesComputer Networks Lab Manual - 14-01-2020Prajwal KoppaNo ratings yet
- Network Lab Manual 5th Sem 2017-18Document60 pagesNetwork Lab Manual 5th Sem 2017-18Sam82% (17)
- 06 CSL77 NWLabDocument1 page06 CSL77 NWLabPulakesh BharaliNo ratings yet
- Computer Network Lab 1Document61 pagesComputer Network Lab 1AkshataNo ratings yet
- CCN Completed1Document46 pagesCCN Completed1Deepa JerinNo ratings yet
- Introduction to NS-2 Network SimulatorDocument72 pagesIntroduction to NS-2 Network SimulatorStark NessonNo ratings yet
- Computer Networks Lab Experiments on Simulation & C/C++ ProgrammingDocument1 pageComputer Networks Lab Experiments on Simulation & C/C++ ProgrammingSubramanya BhaskarNo ratings yet
- CN Lab ManualDocument46 pagesCN Lab Manualsundaravanan_rm100% (1)
- CN Lab ProgramsDocument36 pagesCN Lab ProgramsKavitha SANo ratings yet
- NS2 Cnlab PDFDocument60 pagesNS2 Cnlab PDFManish ManuNo ratings yet
- NS2 Cnlab PDFDocument60 pagesNS2 Cnlab PDFManish ManuNo ratings yet
- Networks Laboratory Sub Code: 06CSL77: The Parts Have Equal MarksDocument1 pageNetworks Laboratory Sub Code: 06CSL77: The Parts Have Equal MarksPriyaSrihariNo ratings yet
- DCN FileDocument7 pagesDCN Filekarieshma sharrmaNo ratings yet
- CN Lab Manual ECE 6th SemDocument49 pagesCN Lab Manual ECE 6th Semsachin ninganur50% (2)
- Network LabDocument24 pagesNetwork Labget_togetherNo ratings yet
- CN SimulationDocument13 pagesCN Simulationvvce21cse0119No ratings yet
- 10CSL77 NETWORK - Lab PDFDocument39 pages10CSL77 NETWORK - Lab PDFNooruddinSahebNo ratings yet
- Lab 01Document4 pagesLab 01Charu Roopa VaradarajanNo ratings yet
- Computer Networks Lab ManualDocument45 pagesComputer Networks Lab ManualamitNo ratings yet
- Communication and Computer Networks Simulator (NS2) : January 2014Document18 pagesCommunication and Computer Networks Simulator (NS2) : January 2014Eng. Abdalla sheik Aden RaageNo ratings yet
- DCN FILE ChiiDocument49 pagesDCN FILE ChiiOm DwivediNo ratings yet
- NetworkLab 13MCA38Document62 pagesNetworkLab 13MCA38Joyanta Singha100% (2)
- Cisco Packet Tracer Implementation: Building and Configuring Networks: 1, #1From EverandCisco Packet Tracer Implementation: Building and Configuring Networks: 1, #1No ratings yet
- Bus ElectricalDocument1 pageBus Electricalpes_krishnaNo ratings yet
- Dijkastra SWFDocument1 pageDijkastra SWFpes_krishnaNo ratings yet
- Tables 1Document4 pagesTables 1pes_krishnaNo ratings yet
- DSP-First, 2nd EditionDocument6 pagesDSP-First, 2nd Editionpes_krishnaNo ratings yet
- LM555 Timer (RevDocument25 pagesLM555 Timer (RevJuan Diego ValdezNo ratings yet
- DSP-First, 2nd EditionDocument6 pagesDSP-First, 2nd Editionpes_krishnaNo ratings yet
- LM555 Timer (RevDocument25 pagesLM555 Timer (RevJuan Diego ValdezNo ratings yet
- Chapter - 1: Dept. of ECE, PESCE MandyaDocument57 pagesChapter - 1: Dept. of ECE, PESCE Mandyapes_krishnaNo ratings yet
- LM555 Timer (RevDocument25 pagesLM555 Timer (RevJuan Diego ValdezNo ratings yet
- 2017 06 11 Satellite SchemeDocument3 pages2017 06 11 Satellite Schemepes_krishnaNo ratings yet
- Program Outcomes Attainment AnalysisDocument16 pagesProgram Outcomes Attainment Analysispes_krishnaNo ratings yet
- Satellite Communication VTU 2010Document12 pagesSatellite Communication VTU 2010pes_krishnaNo ratings yet
- DSP-First, 2nd EditionDocument6 pagesDSP-First, 2nd Editionpes_krishnaNo ratings yet
- DSP-First, 2nd EditionDocument6 pagesDSP-First, 2nd Editionpes_krishnaNo ratings yet
- DSE monthly target achievement reportDocument2 pagesDSE monthly target achievement reportpes_krishnaNo ratings yet
- Introduction To MatlabDocument45 pagesIntroduction To MatlabSivaraman ChidambaramNo ratings yet
- Anti Sleep Alarm For StudentsDocument9 pagesAnti Sleep Alarm For StudentsHimanshu Bisht100% (1)
- DSP-First, 2nd EditionDocument6 pagesDSP-First, 2nd Editionpes_krishnaNo ratings yet
- 8086Document1 page8086pes_krishnaNo ratings yet
- Very long document with random text and numbersDocument2 pagesVery long document with random text and numberspes_krishnaNo ratings yet
- Robability and Tatistical Nference: Robert V. Hogg Elliot A. Tanis Dale L. ZimmermanDocument1 pageRobability and Tatistical Nference: Robert V. Hogg Elliot A. Tanis Dale L. Zimmermanpes_krishnaNo ratings yet
- Perfect Conductors Carry Charge Instantaneously From Here To There - Perfect Insulators Carry No Charge From Here To There, EverDocument10 pagesPerfect Conductors Carry Charge Instantaneously From Here To There - Perfect Insulators Carry No Charge From Here To There, Everpes_krishnaNo ratings yet
- Ultrasound GuidedDocument1 pageUltrasound Guidedpes_krishnaNo ratings yet
- Cursive LowercaseDocument3 pagesCursive Lowercasepes_krishnaNo ratings yet
- All Rights Reserved. No Part of This Publication May Be Reproduced or Transmitted in Any Form or by AnyDocument1 pageAll Rights Reserved. No Part of This Publication May Be Reproduced or Transmitted in Any Form or by Anypes_krishnaNo ratings yet
- NOUNSaDocument4 pagesNOUNSapes_krishnaNo ratings yet
- Shirdi Sai Engineering CollegeDocument3 pagesShirdi Sai Engineering Collegepes_krishnaNo ratings yet
- Ultrasound GuidedDocument1 pageUltrasound Guidedpes_krishnaNo ratings yet
- Techniques For Preventing Hypotension During Spinal Anaesthesia For Caesarean Section (Review)Document1 pageTechniques For Preventing Hypotension During Spinal Anaesthesia For Caesarean Section (Review)pes_krishnaNo ratings yet
- Brake Pedals and ValveDocument4 pagesBrake Pedals and Valveala17No ratings yet
- MS 01 182Document5 pagesMS 01 182kicsnerNo ratings yet
- Auto BestBuys MAKATI CITY September ListingDocument5 pagesAuto BestBuys MAKATI CITY September ListingWill GeronaNo ratings yet
- Process Thermodynamic Steam Trap PDFDocument9 pagesProcess Thermodynamic Steam Trap PDFhirenkumar patelNo ratings yet
- Varco Manual ElevatorDocument54 pagesVarco Manual ElevatorJohn Jairo Simanca Castillo100% (1)
- PV Design WorksheetDocument4 pagesPV Design WorksheetLarry Walker II100% (1)
- Ficha Tecnica 750 GPMDocument156 pagesFicha Tecnica 750 GPMByron Chele0% (2)
- Rob Thomas Digital Booklet - Cradle SongDocument15 pagesRob Thomas Digital Booklet - Cradle SongAgnieszka ŁukowskaNo ratings yet
- Factors Effecting PerformanceDocument47 pagesFactors Effecting Performancebembie83No ratings yet
- Prefabricated Structures ComponentsDocument16 pagesPrefabricated Structures ComponentsKrish KrishNo ratings yet
- Christianity and Online Spirituality Cybertheology As A Contribution To Theology in IndonesiaDocument18 pagesChristianity and Online Spirituality Cybertheology As A Contribution To Theology in IndonesiaRein SiraitNo ratings yet
- Hughes Brothers PDFDocument52 pagesHughes Brothers PDFJavier MaldonadoNo ratings yet
- Timeline of Programming Languages PDFDocument11 pagesTimeline of Programming Languages PDFMohd Khir ZainunNo ratings yet
- Fire Pump ChecklistDocument11 pagesFire Pump ChecklistLD Jr FrancisNo ratings yet
- Transient and Random VibrationDocument19 pagesTransient and Random VibrationAman SharmaNo ratings yet
- FiatDocument56 pagesFiatOmkar ParkarNo ratings yet
- Skybox Security Sales&Tech OverviewDocument46 pagesSkybox Security Sales&Tech Overviewerdem100% (1)
- Shivam Public School: Half Yearly Exam (2019-20) Class-VII Subject - S.S.T Time:3 HoursDocument4 pagesShivam Public School: Half Yearly Exam (2019-20) Class-VII Subject - S.S.T Time:3 HoursSHIVAM TAYALNo ratings yet
- MC 8051Document85 pagesMC 8051Sonu SatishNo ratings yet
- List of Linkages2016Document74 pagesList of Linkages2016engrwho0% (1)
- Volvo 850 GLT Owners Manual 1993Document176 pagesVolvo 850 GLT Owners Manual 1993jpaulorosado2186No ratings yet
- L04-L05 Parts 13-25-550 v05 42021Document84 pagesL04-L05 Parts 13-25-550 v05 42021Brandi HillNo ratings yet
- Template Icme 13 PosterDocument1 pageTemplate Icme 13 PosterZulma Xiomara Rueda GarciaNo ratings yet
- POSSIBILITIES OF LOW VOLTAGE DC SYSTEMSDocument10 pagesPOSSIBILITIES OF LOW VOLTAGE DC SYSTEMSTTaanNo ratings yet
- Industry 4.0 FinaleDocument25 pagesIndustry 4.0 FinaleFrame UkirkacaNo ratings yet
- 01 U3 Ws 1 Force DiagramsDocument4 pages01 U3 Ws 1 Force Diagramsapi-197108354No ratings yet
- Scope of Work Project Sahastradhara Road (GYAN CONSTRUCTIONS)Document4 pagesScope of Work Project Sahastradhara Road (GYAN CONSTRUCTIONS)Hotel Central palaceNo ratings yet
- Strategic Information Systems Planning: Course OverviewDocument18 pagesStrategic Information Systems Planning: Course OverviewEmmy W. RosyidiNo ratings yet
- Understand Centrifugal CompressorDocument16 pagesUnderstand Centrifugal Compressorramanathan72-1100% (2)
- Grade 6 Science PuzzleDocument4 pagesGrade 6 Science Puzzlemargie riveraNo ratings yet