Professional Documents
Culture Documents
Secure Storage Service For Iaas Cloud Users
Uploaded by
rameshOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Secure Storage Service For Iaas Cloud Users
Uploaded by
rameshCopyright:
Available Formats
2013 13th IEEE/ACM International Symposium on Cluster, Cloud, and Grid Computing
Secure Storage Service for IaaS Cloud Users
Jinho Seol, Seongwook Jin, and Seungryoul Maeng
Computer Science Department, KAIST, Daejeon, Korea
{jhseol,swjin}@calab.kaist.ac.kr, maeng@cs.kaist.ac.kr
Abstract—Cloud computing enables to reduce operating costs and
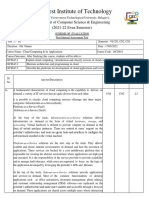
Mgmt. VM Guest VM
maximize resource utilization. However, current cloud infrastructure
is insufficient to guarantee the confidentiality of classified information
for cloud users because one of administrators with privilege or remote Storage
hackers compromising management tools can leak the information. Terminal Driver
This paper addresses storage issues in cloud computing and proposes a in Cloud
secure storage service where stored user data are protected even against
Hypervisor
a malicious administrator and compromised software. We describe the
architecture of proposed design and discuss the security issues of the
design.
Local
Remote
Storage
Storage Cloud Node
I. I NTRODUCTION
Cloud computing refers the computing paradigm where software Privileged Access Illigal Access with Privilege
and hardware are provided as a service. Cloud computing is in
the spotlight because it is possible to reduce operating costs and Fig. 1. Threat Model
maximize resource utilization as pay-as-you-go model is a basic
philosophy of cloud computing. Cloud computing provides attractive
environment in that physical servers don’t have to be managed III. S ECURE S TORAGE R EQUIREMENTS
directly by cloud users and elasticity against scalability problem is A. Assumption & Threat Models
also provided. Cloud systems consist of lots of software components. Among
Nevertheless, companies regarding the security as the first principle them, hypervisor and a management OS coexist with guest VMs
of governance are reluctant to use cloud computing service. The in a single cloud node. When the hypervisor is compromised, the
main reason is anxiety about the security of their VMs. As plenty confidentiality of guest VMs cannot be guaranteed. However, the
of stakeholders including a cloud provider and cloud users co-exist code size of the hypervisor is smaller than that of traditional OS, and
in cloud computing environment, the VMs allocated to a cloud user thus the hypervisor has relatively less security holes[2].
are influenced by hypervisor, a management OS, which means the A management OS is an important attack point of remote hackers
OS of a management VM, or other VMs even in a single cloud or a malicious administrator. The management OS can access its own
node. Furthermore, cloud administrators have privileges to control memory even though the memory of guest VM prevents from being
the VMs. It means a malicious administrator can easily leak the user accessed[2], [3]. It means information leakage by means of observing
data using management tools[4]. As a result, the virtual machines are I/O of guest VMs via split drivers in management OS is still possible.
more vulnerable to information leakage than the physical machines. Therefore, the main threat of this work is information leakage by
In this paper we propose secure storage architecture using crypto- accessing local storage via the management OS or direct access to
processors for cloud users. User data are encrypted and even a remote storage with privilege. We also assume defense mechanisms
malicious administrator cannot access the cryptographic keys, and the against hardware attacks are well-equipped and thus hardware attacks
decrypted data are isolated from the management OS. Accordingly, are inexecutable.
user data are protected from cloud administrators and other users.
More secure cloud computing environment is guaranteed in the B. Requirements
proposed architecture, and thus it is expected to migrate from server The requirements for secure storage summarized as follows.
hosting service to cloud computing service more and more.
• Isolated cryptographic operation: A malicious administrator or
II. BACKGROUND remote hackers can have control over the management OS.
There are three entities to protect the confidentiality of guest Therefore, when plain text or decrypted data are loaded in the
VMs: processing, memory, and I/O. Processing and memory can be memory of the management OS, they can be leaked by using
protected by H/W such as VT-x and AMD-V and S/W techniques privileged operations in the management OS. As a result, the
such as [2], [3]. If processing and memory are protected, the guest result of cryptographic operations should be isolated from the
virtual machine is safe as far as no I/O operation is involved. management OS.
However, transferring the input or output data of computation is an • Infrastructure cryptographic operation: Key delivery from cloud
essential process in cloud computing environment. That’s why the users involves connection to outside cloud systems. It means ad-
last entity, I/O should be protected in cloud computing. Generally, all ditional service is needed for key delivery. Thus, cryptographic
network traffics can be encrypted within a guest virtual machine and keys should exist in the cloud system. Moreover, full-disk
thus, they are safe during transfer. However, it implies an assumption encryption is implementable because guest OS is uninvolved.
that the cryptographic keys are protected safely. The cryptographic • Key protection: To protect the keys perfectly, we need a key
keys are generally stored in the storage. Therefore, protecting storage storage service where the keys are inaccessible even with
is the basic foundation of all other I/O devices. privileged access.
978-0-7695-4996-5/13 $26.00 © 2013 IEEE 190
DOI 10.1109/CCGrid.2013.31
Mgmt. VM Hypervisor Physical
Device Mgmt. VM Guest VM Memory
Authority TPM Crypto−
Processor Page
Driver Driver
Table
Hypervisor Encrypted
Guest VM Nested Data
Page
Table
Guest Plain
EK PCR AIK EK DA Key Page Data
Table
TPM PCI Device
IOMMU
Cloud Node Page
Table
PCI Device
Fig. 2. Architecture Overview
Encrypted Data Access Plain Data Access
Fig. 3. Plain Text Isolation
IV. S YSTEM D ESIGN
A. Overview
D. Safe system state guarantee
Figure 2 shows the overall architecture of our system. Cloud If a malicious administrator or remote hackers can compromise the
nodes are equipped with a crypto-processor, which plays a role of image of hypervisor and reboot the system, compromised hypervisor
encryption, decryption, and key storage, and Trusted Platform Module will be loaded, and thus there is no guarantee that the hypervisor plays
(TPM), which is used to verify the system state of cloud nodes. As a role of isolation. We design that the crypto-processor activates itself
the crypto-processors are the bare bones of the proposed system, only if the system states are attested to avoid unwanted hypervisor.
they have to be verified by third party called Device Authority (DA). We don’t present details of the activation protocol due to space
System states are measured into Platform Configuration Register limitation.
(PCR) of TPM. Endorsement Key (EK) and Attestation Identity Key
(AIK) in the TPM are used to represents the identity of the TPM. A V. S ECURITY A NALYSIS & D ISCUSSION
PCI crypto-processor also has EK for the identity of itself. DA key The secure system states could be used to activate the crypto-
is used for verifying the signature of DA. processor illegally. The malicious management OS on compromised
hypervisor would try to use the measurement value of attested
B. Challenges hypervisor. Thus, DA needs an a-priori list of pairs, which comprise
EK of TPM and EK of crypto-processor from one physical cloud
Even though crypto-processors are operational in cloud node, two
node not to face the unwanted situation. At the last step of activation
main challenges remains to provide a secure storage service. As the
process, DA will attest the system state. During attestation, DA have
device driver of crypto-processor is placed in the management OS, we
to also check whether the system state is from requested node or not.
need to isolate the decrypted (or plain) text from the management OS.
If compromised hypervisor tries to use the system state of another
If the management OS is able to access the result of cryptographic
machine, DA can detect and will refuse the activation request.
operations, the confidentiality of stored data cannot be guaranteed.
The other challenge is to ensure safe system states. Hypervisor is in VI. C ONCLUSION & F UTURE W ORK
charge of access control. Thus, if hypervisor doesn’t protect illegal Security is primary consideration for the users who consider using
access from the management OS, the information leakage of guest cloud services. However, guaranteeing secure cloud computing envi-
VMs is unavoidable. ronment is cumbersome and tortuous. This paper presents a secure
To ensure a secure storage service, the proposed architecture storage service for the users via crypto-processors. The proposed
achieves plain text isolation from the management OS and safe architecture makes the users lighthearted because it is guaranteed
system state guarantee as following two sections. that stored data in cloud systems are encrypted and cannot be leaked
even with privileged accesses. Currently, we are developing a PCI
C. Plain text isolation prototyped board and implementing its functionalities. We plan to
implement a fully functional prototype including PCI device crypto-
Generally, when a guest VM reads stored data block, the man-
processors, device drivers, and the activation server of DA.
agement OS reads the requested block from disk, and afterward,
sends the block to the guest VM. However, as the block is encrypted, ACKNOWLEDGMENT
decrypting process is needed before the block is sent to the guest VM. This work was supported by the IT R&D Program of MKE/KEIT.
At the same time, decrypted text should not be accessed from the [KI002090, Development of Technology Base for Trustworthy Computing]
management OS. To achieve this goal, hypervisor manipulates page
tables to block unauthorized accesses. Figure 3 shows the mapping of R EFERENCES
the management OS, guest VM and crypto-processor. Once encrypted [1] AMD. I/O virtualization technology (IOMMU) specification, 2011.
data are loaded to memory by the management OS, the crypto- [2] C. Li, A. Raghunathan, and N. Jha. Secure virtual machine execution
under an untrusted management OS. In Cloud Computing (CLOUD),
processor is in charge of decryption. The device will access the 2010 IEEE 3rd International Conference on, pages 172–179, 2010.
encrypted data and write plain data to other part of memory after [3] D. G. Murray, G. Milos, and S. Hand. Improving xen security through
decrypting. Hypervisor manipulates page table of the management OS disaggregation. In Proceedings of the fourth ACM SIGPLAN/SIGOPS
and the IOMMU (I/O Memory Management Unit)[1] page table of international conference on Virtual execution environments, VEE ’08,
page 151160, New York, NY, USA, 2008. ACM. ACM ID: 1346278.
the crypto-processor, thus, the device is able to access both encrypted [4] B. D. Payne, M. D. de Carbone, and W. Lee. Secure and flexible
and decrypted data whereas the management OS can access only monitoring of virtual machines. In Computer Security Applications
the encrypted data. As a result, the data of guest VM can preserve Conference, 2007. ACSAC 2007. Twenty-Third Annual, pages 385–397.
confidentiality from the management OS. IEEE, Dec. 2007.
191
You might also like
- Cloud Security Is Not (Just) Virtualization Security: A Short PaperDocument6 pagesCloud Security Is Not (Just) Virtualization Security: A Short PaperalonhazayNo ratings yet
- Cloud Computing Made Simple: Navigating the Cloud: A Practical Guide to Cloud ComputingFrom EverandCloud Computing Made Simple: Navigating the Cloud: A Practical Guide to Cloud ComputingNo ratings yet
- PID3515421 RupeshDocument5 pagesPID3515421 Rupeshamit khapardeNo ratings yet
- CPDPDocument2 pagesCPDPSōda KanNo ratings yet
- Key CloudDocument5 pagesKey CloudLiNuNo ratings yet
- Ijaerv10n20spl 493Document5 pagesIjaerv10n20spl 493amit khapardeNo ratings yet
- Importance of Virtualization TechnologyDocument3 pagesImportance of Virtualization TechnologyRaja FawadNo ratings yet
- Key Infrastructure Elements For Cloud Computing: S.J.Mohana, M.Saroja, M.VenkatachalamDocument4 pagesKey Infrastructure Elements For Cloud Computing: S.J.Mohana, M.Saroja, M.VenkatachalamInternational Journal of computational Engineering research (IJCER)No ratings yet
- 4Document9 pages4Sourabh porwalNo ratings yet
- Unit 5Document19 pagesUnit 5Mail ForSpamersNo ratings yet
- IJEAS0301013Document4 pagesIJEAS0301013erpublicationNo ratings yet
- CCA 1st SchemeDocument7 pagesCCA 1st SchemegangambikaNo ratings yet
- Trusted CloudDocument5 pagesTrusted CloudTooba AamirNo ratings yet
- Cloud Implementation Security ChallengesDocument5 pagesCloud Implementation Security ChallengesMervat BamiahNo ratings yet
- Cloud Cryptography User End EncryptionDocument4 pagesCloud Cryptography User End EncryptionYashil PatelNo ratings yet
- Ijet V3i6p56Document5 pagesIjet V3i6p56International Journal of Engineering and TechniquesNo ratings yet
- Data MangementDocument4 pagesData Mangementessid sabraNo ratings yet
- Virtualization Security For Cloud Computing Service: Shengmei Luo Zhaoji Lin Xiaohua Chen Zhuolin Yang, Jianyong ChenDocument6 pagesVirtualization Security For Cloud Computing Service: Shengmei Luo Zhaoji Lin Xiaohua Chen Zhuolin Yang, Jianyong ChenVeera Reddy DasariNo ratings yet
- Cloud PDFDocument5 pagesCloud PDFhelloeveryNo ratings yet
- Data Storage in Cloud ComputingDocument6 pagesData Storage in Cloud ComputingswathyNandhiniNo ratings yet
- Towards Trusted Cloud Computing: Pramila.S, Sabrabeebe.MDocument5 pagesTowards Trusted Cloud Computing: Pramila.S, Sabrabeebe.MpramilasekarNo ratings yet
- Data Security in Cloud Computing With Elliptic Curve CryptographyDocument5 pagesData Security in Cloud Computing With Elliptic Curve CryptographyRida RizkitaNo ratings yet
- Effective Way To Defend The Hypervisor Attacks in Cloud ComputingDocument6 pagesEffective Way To Defend The Hypervisor Attacks in Cloud ComputingVINOD DADASO SALUNKHE 20PHD0400No ratings yet
- Security Issues in Cloud ComputingDocument8 pagesSecurity Issues in Cloud ComputingsheNo ratings yet
- CCSP Master Notes V2Document54 pagesCCSP Master Notes V2Moazzam ChNo ratings yet
- Virtual Machine Security Challenges: Case StudiesDocument14 pagesVirtual Machine Security Challenges: Case StudiesShaurya KapoorNo ratings yet
- Cloud Network Security and PrivacyDocument5 pagesCloud Network Security and PrivacyBenmbarak omsa3dNo ratings yet
- FCC FinalDocument7 pagesFCC FinalPRIT KHOKHANINo ratings yet
- Cloud SecurityDocument13 pagesCloud SecurityVaishnavi ChockalingamNo ratings yet
- Lecture5 Cloud Computing SecurityDocument18 pagesLecture5 Cloud Computing SecuritykennedyNo ratings yet
- Research On Cloud Computing Security Problem and Strategy: Wentao LiuDocument4 pagesResearch On Cloud Computing Security Problem and Strategy: Wentao LiuayaNo ratings yet
- Live VM Migration Polices Attacks and Security A SurveyDocument8 pagesLive VM Migration Polices Attacks and Security A SurveyhasniNo ratings yet
- Multi Tenancy Issues in Cloud SecurityDocument7 pagesMulti Tenancy Issues in Cloud Securitydarshita singhNo ratings yet
- Term Paper - Virtualization in Cloud ComputingDocument10 pagesTerm Paper - Virtualization in Cloud ComputingSudipNo ratings yet
- Analysis of Various Virtual Machine Attacks in Cloud ComputingDocument4 pagesAnalysis of Various Virtual Machine Attacks in Cloud ComputingVINOD DADASO SALUNKHE 20PHD0400No ratings yet
- Blueshield: A Layer 2 Appliance For Enhanced Isolation and Security Hardening Among Multi-Tenant Cloud WorkloadsDocument4 pagesBlueshield: A Layer 2 Appliance For Enhanced Isolation and Security Hardening Among Multi-Tenant Cloud WorkloadscscNo ratings yet
- (IJCST-V10I5P53) :MR D Purushothaman, M NaveenDocument8 pages(IJCST-V10I5P53) :MR D Purushothaman, M NaveenEighthSenseGroupNo ratings yet
- Security in A Virtualised WorldDocument4 pagesSecurity in A Virtualised WorldShaun NevilleNo ratings yet
- SSRN Id3649074Document3 pagesSSRN Id3649074Riva MakNo ratings yet
- (IJCST-V5I3P25) :suman PandeyDocument7 pages(IJCST-V5I3P25) :suman PandeyEighthSenseGroupNo ratings yet
- Grid and Cloud Unit IIIDocument29 pagesGrid and Cloud Unit IIIcsisajurajNo ratings yet
- Cloud Computing - Unit 1Document61 pagesCloud Computing - Unit 1bpavithra26No ratings yet
- Cloud Models and PlatformsDocument35 pagesCloud Models and PlatformsnoddynoddyNo ratings yet
- Cloud ComputingDocument40 pagesCloud ComputingHimanshu SoniNo ratings yet
- CC PPT4 PDF UNIT 2Document42 pagesCC PPT4 PDF UNIT 2XYZ NKNo ratings yet
- Operating SystemDocument3 pagesOperating SystemSAIMA SHAHZADINo ratings yet
- Cloudcomputing Anintroduction 140522080434 Phpapp01Document32 pagesCloudcomputing Anintroduction 140522080434 Phpapp01Khalid AliNo ratings yet
- Comparative Analysis On Docker and Virtual Machine in Cloud ComputingDocument10 pagesComparative Analysis On Docker and Virtual Machine in Cloud ComputingClyde MarNo ratings yet
- Cloud Computing and Its ApplicationsDocument6 pagesCloud Computing and Its ApplicationsKavinhariharasudhan SankaralingamNo ratings yet
- EN Whitepaper On Cloud Vs On-Premise LoResDocument23 pagesEN Whitepaper On Cloud Vs On-Premise LoResFernando LeonNo ratings yet
- 4 Jaishree JainDocument6 pages4 Jaishree Jainbagulganesh994No ratings yet
- Cloud Computing Security:: Amazon Web ServiceDocument5 pagesCloud Computing Security:: Amazon Web ServicerajaNo ratings yet
- Http://iosrjournals org/IOSR-JCE HTMLDocument7 pagesHttp://iosrjournals org/IOSR-JCE HTMLInternational Organization of Scientific Research (IOSR)No ratings yet
- Data Storage SecurityDocument5 pagesData Storage SecurityAaPka ApNa MaNaSNo ratings yet
- Trusting Your Cloud Provider. Protecting Private Virtual MachinesDocument11 pagesTrusting Your Cloud Provider. Protecting Private Virtual MachinesAleksanderNo ratings yet
- Secured Cloud Data Migration Technique by Competent Probabilistic Public Key EncryptionDocument23 pagesSecured Cloud Data Migration Technique by Competent Probabilistic Public Key EncryptionAzmi AbdulbaqiNo ratings yet
- Cloud Computing Unit-1 (A)Document11 pagesCloud Computing Unit-1 (A)nabeelNo ratings yet
- Cloud: Get All The Support And Guidance You Need To Be A Success At Using The CLOUDFrom EverandCloud: Get All The Support And Guidance You Need To Be A Success At Using The CLOUDNo ratings yet
- AZURE AZ 500 STUDY GUIDE-2: Microsoft Certified Associate Azure Security Engineer: Exam-AZ 500From EverandAZURE AZ 500 STUDY GUIDE-2: Microsoft Certified Associate Azure Security Engineer: Exam-AZ 500No ratings yet
- Cloud computing: Moving IT out of the officeFrom EverandCloud computing: Moving IT out of the officeBCS, The Chartered Institute for ITNo ratings yet
- Encoder Decoder Multiplexers and DemultiplexersDocument40 pagesEncoder Decoder Multiplexers and DemultiplexersSaidur Rahman SidNo ratings yet
- Chapter 11Document22 pagesChapter 11rameshNo ratings yet
- IT2Document23 pagesIT2rameshNo ratings yet
- PC Package Unit 1 Introduction To ComputerDocument28 pagesPC Package Unit 1 Introduction To ComputerrameshNo ratings yet
- MYCH8Document35 pagesMYCH8rameshNo ratings yet
- Lingma Acheson Department of Computer and Information Science, IUPUI Linglu@iupui - EduDocument46 pagesLingma Acheson Department of Computer and Information Science, IUPUI Linglu@iupui - EduBhavani KavyaNo ratings yet
- Java Study MaterialDocument69 pagesJava Study Materialkaviarasi kavi kaviNo ratings yet
- Answer Dec 2018Document62 pagesAnswer Dec 2018rameshNo ratings yet
- Wang 2015Document6 pagesWang 2015rameshNo ratings yet
- Service and Data Security For Multi CloudenvironmentDocument8 pagesService and Data Security For Multi CloudenvironmentrameshNo ratings yet
- IT3Document8 pagesIT3rameshNo ratings yet
- New Allawi2015Document6 pagesNew Allawi2015rameshNo ratings yet
- E CommerceDocument24 pagesE CommercerameshNo ratings yet
- Design and Implementation of A Secure Multi-Cloud Data Storage Using EncryptionDocument5 pagesDesign and Implementation of A Secure Multi-Cloud Data Storage Using EncryptionrameshNo ratings yet
- Password Authentication System (PAS) For Cloud Environment: Open Access Review ArticleDocument5 pagesPassword Authentication System (PAS) For Cloud Environment: Open Access Review ArticlerameshNo ratings yet
- Current Security Threats and Prevention Measures Relating To Cloud Services, Hadoop Concurrent Processing, and Big DataDocument6 pagesCurrent Security Threats and Prevention Measures Relating To Cloud Services, Hadoop Concurrent Processing, and Big DatarameshNo ratings yet
- Dev2012 PDFDocument10 pagesDev2012 PDFrameshNo ratings yet
- Boran Bay Ev 2015Document3 pagesBoran Bay Ev 2015rameshNo ratings yet
- C Answer Set - 1Document50 pagesC Answer Set - 1rameshNo ratings yet
- Deliver A Secure Digital Workspace With Next-Gen Remote Access SolutionsDocument12 pagesDeliver A Secure Digital Workspace With Next-Gen Remote Access SolutionsrameshNo ratings yet
- Exclusive Key Based Group Rekeying Protocols: Jing Liu and Changji WangDocument29 pagesExclusive Key Based Group Rekeying Protocols: Jing Liu and Changji WangrameshNo ratings yet
- Efficient Audit Service Outsourcing For Data Integrity in Cloud ComputingDocument7 pagesEfficient Audit Service Outsourcing For Data Integrity in Cloud ComputingrameshNo ratings yet
- Assessment On Storage Security Progeniesand Prospective Solutions of CloudcomputingDocument7 pagesAssessment On Storage Security Progeniesand Prospective Solutions of CloudcomputingrameshNo ratings yet
- Define Stack and Queue and Also Write Its Basic OperationsDocument36 pagesDefine Stack and Queue and Also Write Its Basic OperationsrameshNo ratings yet
- CONTENTSDocument1 pageCONTENTSrameshNo ratings yet
- SL - No Particulars Page No. 1Document1 pageSL - No Particulars Page No. 1rameshNo ratings yet
- 1Document1 page1rameshNo ratings yet
- E CommerceDocument2 pagesE CommercerameshNo ratings yet
- Allied Princy ItDocument3 pagesAllied Princy ItrameshNo ratings yet
- 3Document8 pages3K@mR@N D@uD P@nHw@RNo ratings yet
- Catalogo Tarifa Hisense 2016Document37 pagesCatalogo Tarifa Hisense 2016David GarciaNo ratings yet
- Chemistry Leuco DyesDocument312 pagesChemistry Leuco Dyeskarel470% (1)
- Performance of A Mid-Sized Harvester-Forwarder System in Integrated Harvesting of Sawmill, Pulpwood and FirewoodDocument16 pagesPerformance of A Mid-Sized Harvester-Forwarder System in Integrated Harvesting of Sawmill, Pulpwood and FirewoodAlexandru Gabriel CotituNo ratings yet
- Principles of Communication Reviewer MidtermDocument5 pagesPrinciples of Communication Reviewer MidtermVon Ryan AlcazarNo ratings yet
- ASC - Chap 1-3 - v2013Document13 pagesASC - Chap 1-3 - v2013Tu vu vanNo ratings yet
- Manual Masina IndesitDocument72 pagesManual Masina Indesitdangb84roNo ratings yet
- U Center UserGuide (UBX 13005250)Document94 pagesU Center UserGuide (UBX 13005250)Phi Ra Uch100% (1)
- Calculating Species Importance ValuesDocument3 pagesCalculating Species Importance Valuesabraha gebruNo ratings yet
- MID TEST Integer, Fraction 20092010Document5 pagesMID TEST Integer, Fraction 20092010mathholic111No ratings yet
- Maths - 2B Imp QuestionsDocument93 pagesMaths - 2B Imp QuestionsBandaru Chiranjeevi100% (1)
- Gurgaon Tuitions Contacts NumbersDocument8 pagesGurgaon Tuitions Contacts NumbersSai KiranNo ratings yet
- RF10 (A4)Document4 pagesRF10 (A4)Dewa Made Astika YathaNo ratings yet
- Service Factors BaldorDocument1 pageService Factors BaldornautelNo ratings yet
- Software Quality EngineeringDocument26 pagesSoftware Quality EngineeringSYED SUMAIR AHMED JAFFRINo ratings yet
- Lehmann Et Al 2013 PDFDocument13 pagesLehmann Et Al 2013 PDFJack HamiltonNo ratings yet
- A Compendium of Blog Posts On Op Amp Design Topics: by Bruce TrumpDocument37 pagesA Compendium of Blog Posts On Op Amp Design Topics: by Bruce TrumpJustine ManningNo ratings yet
- Advanced Math2022fullDocument240 pagesAdvanced Math2022fullMọt PhimNo ratings yet
- Offshore Pipeline Decommissioning Scale and ContextDocument4 pagesOffshore Pipeline Decommissioning Scale and ContextHieu Le TrungNo ratings yet
- 591 Useful Unix Commands PDFDocument1 page591 Useful Unix Commands PDFrohit sharmaNo ratings yet
- CodeDocument8 pagesCodenikhil18salviNo ratings yet
- The Law of CosinesDocument12 pagesThe Law of CosinesLei Xennia YtingNo ratings yet
- Manual EOS UtilityDocument122 pagesManual EOS Utilityjaimegarcia20No ratings yet
- Us 20060145019Document11 pagesUs 20060145019Raymond100% (4)
- MPLS-TP Testing PDFDocument2 pagesMPLS-TP Testing PDFAhsan Mohiuddin100% (1)
- VSANDocument16 pagesVSANaksbehalNo ratings yet
- Heinrich Maximilian TE Finalsubmission2015august MAScDocument213 pagesHeinrich Maximilian TE Finalsubmission2015august MAScWilliam Jaldin CorralesNo ratings yet
- HW 5, 448Document16 pagesHW 5, 448pdrogos02100% (1)
- MODULE 0 CPE105 Review On StatisticsDocument12 pagesMODULE 0 CPE105 Review On StatisticsKishiane Ysabelle L. CabaticNo ratings yet