Professional Documents
Culture Documents
100615
Uploaded by
vol2no6Original Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
100615
Uploaded by
vol2no6Copyright:
Available Formats
(IJCNS) International Journal of Computer and Network Security, 93
Vol. 2, No. 6, June 2010
Proxy Blind Signature based on ECDLP
Asis Kumar Tripathy1, Ipsita Patra2 and Debasish Jena3
1,2
Department of Computer Science and Engineering
International Institute of Information Technology, Bhubaneswar 751 013, India
1
asistripathy@gmail.com , 2ipsi.lucky@gmail.com
3
Center For IT Education
Biju Pattanaik University of Technology,Bhubaneswar, India
debasishjena@hotmail.com
1.4 Proxy Blind Signature
Abstract: Proxy blind signature is the combination of
properties and behavior of two most common digital signature A proxy blind signature scheme is a digital signature
schemes i.e. proxy signature and blind signature. In this scheme scheme which combines the properties of proxy signature
proxy signer generates the blind signature on behalf of the and blind signature schemes. A proxy blind signature
original signer without knowing the content of the message. scheme is a protocol played by two parties in which a user
Proxy blind signature can be used in various applications such obtains a proxy signer’s signature for a desired message and
as e-voting, e-payment, mobile agent communication. In this the proxy signer learns nothing about the message. With
paper cryptanalysis of DLP based proxy blind signature scheme such properties, the proxy blind signature scheme is useful
with low computation by Aung et al. has been done. An efficient
in several applications
proxy blind signature scheme based on ECDLP has been
proposed.
such as e-voting, e-payment and mobile agent environments.
In a proxy blind signature scheme, the proxy signer is
Keywords: Proxy Signature ,Blind signature,Proxy blind allowed to generate a blind signature on behalf of the
signature,ECDLP. original signer.
1. Introduction 1.5 Properties of the Proxy Blind Signature
Scheme
1.1 Digital Signature
In addition to the properties of Digital signature and proxy
A digital code that can be attached to an electronically blind signature should satisfy the following properties.
transmitted that uniquely identifies the sender. Digital 1.Distinguish-ability: The proxy signature must be
signatures are especially important for electronic commerce distinguishable from the normal signature.
and are a key component of most authentication schemes. 2. Non-repudiation: Neither the original signer nor the
To be effective, digital signatures must be unforgeable. proxy signer can sign message instead of the other party.
There are a number of different encryption techniques to Both the original signer and the proxy signer can not deny
guarantee this level of security. their signatures against anyone.
3. Unforgeability: Only a designated proxy signer can
generate a valid proxy signature for the original signer (even
the original signer cannot do it).
1.2 Proxy signature 4. Verifiability: The receiver of the signature should be able
to verify the proxy signature in a similar way to the
The proxy signature scheme is a kind of digital signature verification of the original signature.
scheme . In the proxy signature scheme , one user called the 5. Identifiability: Anyone can determine the identity of the
original signer ,can delegate his/her signing capability to corresponding proxy signer from a proxy signature.
another user called the proxy signer. This is similar to a 6. Prevention of misuse: It should be confident that proxy
person delegating his/her seal to another person in the real key pair should be used only for creating proxy signature,
world. which conforms to delegation information. In case of any
misuse of proxy key pair, the responsibility of proxy signer
1.3 Blind Signature should be determined explicitly.
7. Unlinkability: When the signature is revealed, the proxy
signer can not identify the association between the message
The signer cannot determine which transformed message and the blind signature he generated. When the signature is
received for signing corresponds with which digital verified, the signer knows neither the message nor the
signature, even though the signer knows that such a signature associated with the signature scheme.
correspondence must exist.
In this paper, cryptanalysis of Aung et al[12] has been done
and an efficient proxy digital signature based on ECDLP has
94 (IJCNS) International Journal of Computer and Network Security,
Vol. 2, No. 6, June 2010
been proposed. The proposed scheme satisfies all the 3. Overview Of Aung et al.’s DLP Based Proxy
properties of a proxy blind signature scheme. Blind Signature scheme With Low
The rest of this paper is organized as follows. In Section
2,some related work are discussed. Overview Of Aung et
Computation
al.’s DLP Based Proxy Blind Signature scheme with Low
Computation has been done in section 3 . In Section 4, In this section,DLP Based Proxy Blind Signature scheme
Cryptanalysis of Aung et al.’s scheme has been done. An With Low Computation has been discussed.
introduction to ECC is being described in section 5. In
Section 6, Proposed scheme is being described. Security
analysis of the proposed scheme has been done in section 7. 3.1 Proxy Delegation Phase
In Section 8, Efficiency of the proposed scheme is being
compared with the previous schemes and concluding
Original signer selects random number and
remarks are being described in Section 9.
computes:
(1)
(2)
2. Related Work
sends along with the warrant to the proxy
D. Chaum [4]introduced the concept of a blind signature signer. And then proxy signer checks:
scheme in 1982. In 1996 Mambo et al [2] introduced the
concept of proxy signature. The two types of scheme: proxy (3)
unprotected (proxy and original signer both can generate a
valid proxy signature) and proxy protected (only proxy can If it is correct, P accepts it and computes proxy signature
generate a valid proxy signature) ensures among other secret key as follow:
things, non-repudiation and unforgeability . (4)
The first proxy blind signature was proposed by Lin and Jan
[1] in 2000. Recently Tan et al. [7] introduced a proxy blind
Note: responding proxy public key
signature scheme, which ensures security properties of the
schemes, viz., the blind signature schemes and the proxy
signature schemes. The scheme is based on Schnorr blind
signature scheme Lee et al.[3] showed that a strong proxy
signature scheme should have properties of strong 3.2 Blind Signing Phase
unforgeability, verifiability, strong identifiability, strong
nonrepudiation and prevention of misuse. Proxy signer selects random number and
Hung-Min Sun and Bin Tsan Hsieh [8] show that Tan et
computes:
al.[6] schemes do not satisfy the unforgeability and
unlinkability properties. In addition, they also point out that
(5)
Lal and Awasthi [7] scheme does not possess the
unlinkability property either. In 2004, Xue and Cao [9]
and then sends to signature asker . To obtain the
showed there exists one
blind signature of message m, original signer randomly
weakness in Tan et al. scheme [5] and Lal et al. scheme [7]
choose two random numbers and computes:
since the proxy signer can get the link between the blind
message and the signature or plaintext with great (6)
probability. Xue and Cao introduced concept of strong (7)
unlinkability and they also proposed a proxy blind signature (8)
scheme.
In 2007 Li et al.[10] proposed a proxy blind signature If =0 then has to select new tuple Otherwise
scheme using verifiable self-certified public key, and their sends to . After receiving proxy signer computes :
scheme is more efficient than schemes published earlier.
Recently, Xuang Yang and Zhaoping Yu[11] proposed new (9)
scheme and showed their scheme is more efficient than Li et
al.[10]. and sends the sign message to .
In 2009 Aung et al.[12] proposed a new proxy blind
signature scheme which satisfied all the security
requirements of both the blind signature scheme and the 3.3 Extraction Phase
proxy signature scheme.
While receiving , computes:
(10)
Finally the signature of message is .
(IJCNS) International Journal of Computer and Network Security, 95
Vol. 2, No. 6, June 2010
3.4 Verification Phase 5.1.2 Point Addition
Consider two distinct points J and K such that
The recipient of the signature can verify the proxy blind
signature by checking whether and Let where,
then,
(11)
Where
If it is true, the verifier accepts it as a valid proxy blind
signature, otherwise rejects. (12)
Verifiability where, s is the slope of the line through J and K. If ,
then where, O is the point at infinity. If
The verifier can verify the proxy blind signature by checking
then, ; point doubling equations are used. Also,
holds.
5.1.3 Point Doubling
4. Cryptanalysis Of the Aung et al.’s Scheme
The scheme doesn’t satisfy the property of verifiability as Consider a point such that where, . Let
mentioned in Aung et al.[12]’s scheme. The verification where, . Then,
steps are not correct.
(13)
5. Elliptic Curve Cryptography
where, s is the tangent at point and is one of the
parameters chosen with the elliptic curve. If = 0
5.1 Elliptic Curve over Finite Field then, where, O is the point at infinity.
The elliptic curve operations defined on real numbers are
slow and inaccurate due to round-off error. Cryptographic 6. Proposed Scheme
operations need to be faster and accurate. To make
operations on elliptic curve accurate and more efficient, In this section, we propose an efficient proxy blind
ECC is defined over two finite fields— prime field and signature scheme based on ECC.The proposed scheme is
binary field . The field is chosen with finitely large divided into five phases: system parameters, proxy
number of points suited for cryptographic operations. delegation, blind signing, signature extraction and
signature verification.
5.1.1 EC over Prime Field
6.1 System Parameters
The equation of the elliptic curve on a prime field is
The entities involved are three parties.We denote the x-
coordinate of a point on the elliptic curve by . The
where, . Here, the elements of the
finite field are integers between 0 and . All the scheme is constructed as follows. We make conventions
operations such as addition, subtraction, division, and that lowercases denote the elements in and capital
multiplication involves integers between 0 and . The letters denote the points in the curve .
prime number p is chosen such that there is finitely large O: the original signer
number of points on the elliptic curve to make the P: the proxy signer
cryptosystem secure. Standards for Efficient Cryptography A: the signature asker
(SEC) specifies curves with p ranging between 112-521 bits : the original signer O's secret key
. The algebraic rules for point addition and point doubling : the original signer O's public key,
can be adapted for elliptic curves over .
: the proxy signer P's secret key
: the proxy signer P's public key,
: the designated proxy warrant which contains the
identities information of the original signer and the proxy
96 (IJCNS) International Journal of Computer and Network Security,
Vol. 2, No. 6, June 2010
signer, message type to be signed by the proxy signer, the The recipient of the signature can verify the proxy blind
delegation limits of authority, valid periods of delegation, signature by checking whether
etc.
h(.) a secure one-way hash function. (24)
|| the concatenation of strings. where
6.2 Proxy Delegation Phase If it is true, the verifier accepts it as a valid proxy blind
signature, otherwise rejects.
Original Signer randomly chooses ,1< < n ; and
computes:
7. Security Analysis of the proposed scheme
(14)
The Scheme has stronger security property because
(15)
ECDLP is more difficult than DLP. While maintaining the
security, the scheme requires less data size and less
sends along with the warrant to the proxy
computations, so it is efficient. In this subsection , we
signer. And then proxy signer checks:
show that our scheme satisfies all the security
requirements of a strong proxy blind signature.
(16)
Distinguish-ability: On the one hand, the proxy blind
If the equation holds, P computes proxy signature secret
signature contains the warrant . On
as follow:
the other hand, anyone can verify the validity of the proxy
blind signature, so he can easily distinguish the proxy
(17) blind signature from the normal signature.
and corresponding proxy public key Nonrepudiation: The original signer does not obtain the
proxy signer’s secret key and proxy signer does not
obtain original signer’s secret key . Thus, neither the
original signer nor the proxy signer can sign in place of
6.3 Blind Signing Phase the other party. At the same time, through the valid proxy
blind signature, the verifier can confirm that the
Proxy Signer randomly choose , where 1 < < n and signature of the message has been entitled by the original
computes: signer, because the verifier must use the original signer’s
public key during the verification. Likewise, the proxy
signer cannot repudiate the signature. The scheme offers
(18) nonrepudiation property.
and then sends to signature asker A. To obtain the Unforgeability: An adversary (including the original
blind signature of message m, original signer O randomly signer and the receiver) wants to impersonate the proxy
choose two random numbers u,v and computes: signer to sign the message m. He can intercept the
delegation information but he cannot obtain
(19) the proxy signature secret key . From Equation (15),
(20) we know that only the proxy signer holds the proxy
(21) signature secret key . Because of 1 < < n , the
adversary can obtain the proper proxy signature secret
If then A has to select new tuple (u,v),Otherwise key by guessing it with at most a probability .That is,
O sends e to P. After receiving e proxy signer P computes : anyone else (even the original signer and the receiver)
can forge the proxy blind signature successfully with a
(22) probability .
Verifiability: The proposed scheme satisfies the property
6.4 Extraction Phase of verifiability. The verifier can verify the proxy blind
signature by checking
holds. This is
While receiving , computes:
(23) because:
Finally the signature of message is
6.5 Verification Phase
(IJCNS) International Journal of Computer and Network Security, 97
Vol. 2, No. 6, June 2010
= Verifiability, unforgeability, Identifiability, Prevention of
misuse and Unlinkability. The proposed scheme is
compared with the known proxy blind signature scheme
which are given below.
=
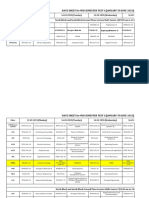
Table 1: Comparative statement among proxy blind
signature schemes
Scheme Basis 80-Bit
Security
Strength
interger IFP 1024-bit
fractorizatio modulus
n problem
discrete DLP |p| = 1024,
logarithm |q| = 160
problem
Proposed ECDLP m= 163 bits
schemes
9. Conclusion
We analyzed that Aung et al.’s DLP based proxy blind
Identifiability: The proxy blind signature signature scheme with low computation does not satisfy
contains the warrant . Moreover, in the verifiability property of proxy blind signature scheme
the verification equation .Compared with Aung et al’s scheme , we present a more
which includes the original signer O’s public key and efficient and secure proxy blind signature scheme to
the proxy signer P’s public key . Hence, anyone can overcome the pointed out drawback of the Aung et al’s
determine the identity of the corresponding proxy signer scheme.We proved that our scheme is more efficient and
from a proxy signature. secure than the previous schemes.
Prevention of misuse: The proposed scheme can prevent References
proxy key pair misuse because the warrant mw includes
original signer and proxy signer identities information, [1] W. D. Lin, and J. K. Jan, "A security
message type to be signed by the proxy signer, delegation personal learning tools using a proxy blind
period, etc. With the proxy key, the proxy signer cannot signature scheme", Proc. Of International
sign messages that have not been authorized by the Conference on Chinese Language Computing, 2000,
original signer. pp.273- 277.
[2] M. Mambo, K. Usuda, and E. Okamoto, "Proxy
Unlinkability: During generation of the signature signatures: Delegation of the power to sign
, the proxy signer has the view of messages", IEICE Transaction on Fundamentals,
transcripts .Since are specified E79-A (1996), pp.1338-1353.
by the original signer for all the signatures under the [3] B. Lee, H. Kim, and K. Kim,"Strong proxy signature
same delegation condition. The proxy unlinkability holds and its application", Australasian Conference on
if and only if there is no conjunction between and Information Security and Privacy(ACISP 2001),
. This is obvious from Equations (16)- LNCS2119, Springer- Verlag, Sydney, 2001, pp.603-
(21). The value is only included in Equation (17) and 608.
connected to through Equation (18). For this, one must [4] D Chaum," Blind signature for untraceable
be able to compute R which is masked with two random payments, Advances in C ryptology", proceeding of
numbers. Similarly, and may be associated with the CRYPTO 82, Springer- Verlag, New York, 1983,
signature through Equation (19) and (20) respectively. pp.199-203.
They fail again due to the random numbers. Even they are [5] Z. W. Tan, Z. J. Liu, and C. M. Tang, "A proxy blind
combined, the number of unknowns is still more than signature scheme based on DLP", Journal of
that of the equations. So, the proposed scheme provides Software, Vol14, No11, 2003, pp.1931-1935.
indeed the proxy blindness property. [6] Tan Z. Liu Z. Tang C. "Digital proxy blind signature
schemes based on DLP and ECDLP". In MM
Research Preprints, No. 21, MMRC,
AMSS,Academia, Beijing, 2002, 212- 217.
8. Efficiency of the proposed scheme
[7] Lal S. Awasthi A K. Proxy" Blind Signature Scheme".
The proposed scheme has been proved to be correct. It Journal of Information Science and Engineering.
also satisfies the properties of proxy blind signature Cryptology ePrint Archive, Report 2003/072.
scheme, i.e, Distinguish-ability, Nonrepudiation, Available at http://eprint.iacr.org/.
98 (IJCNS) International Journal of Computer and Network Security,
Vol. 2, No. 6, June 2010
[8] Hung-Min Sun, Bin-Tsan Hsieh "On the Security of
Some Proxy Blind Signature Schemes".
Australasian InformationvSecurityWorkshop(AIS
W2 004),Dunedin: Australian Computer Society
press, 2004,75-78.
[9] Q. S. Xue, and Z. F. Cao, "A new proxy blind signature
scheme with warrant", IEEE Conference on
Cybernetics and Intelligent Systems (CIS and RAM
2004), Singapore, 2004, pp.1385-1390.
[10] J.G. Li, and S. H.Wang, "New Efficient Proxy Blind
Signature Scheme Using Verifiable Self-certified
Public Key", International Journal of Network
Security, Vol.4, No.2, 2007, pp.193-200.
[11] Xuan Yang, Zhaoping Yu , "Efficient Proxy Blind
Signature Scheme based on DLP", International
Conference on Embedded Software and Systems (
ICESS2008).
[12] Aung Nway Oo and Nilar "The DLP based proxy
blind signature scheme with low computation",
2009 Fifth International Joint Conference on INC,
IMS and IDC.
Authors Profile
Asis Kumar Tripathy received the B.E.
degree in Information Technology from
bialasore College of Engineering and
Technology in 2006. He has joned the
same college as Lecturer since
26.12.2006. Now, he is persuing his
M.Tech degree at International Institute
of Information Technology-Bhubaneswar,
Orissa, India. His research area of interest is Information Security
Ipsita Patra received the MCA degree
from National Institute of Technology
,Rourkela . Now, she is persuing her
M.Tech degree at International Institute of
Information Technology-Bhubaneswar,
Orissa, India. Her research area of interest
are Information Security and Network
security.
Debasish Jena was born in 18th
December, 1968. He received his B
Tech degree in Computer Science and
Engineering, his Management Degree and
his MTech Degree in 1991,1997 and
2002 respectively. He has joined Centre
for IT Education as Assistant Professor
since 01.02.2006. He has submitted his
thesis for Ph.D. at NIT, Rourkela on 5th April 2010. .His research
areas of interest are Information Security , Web Engineering, Bio-
Informatics and Database Engineering.
You might also like
- 100621Document3 pages100621vol2no6No ratings yet
- 100625Document4 pages100625vol2no6No ratings yet
- 100624Document8 pages100624vol2no6No ratings yet
- 100626Document5 pages100626vol2no6No ratings yet
- 100623Document4 pages100623vol2no6No ratings yet
- Study The Effect of Node Distribution On Qos Multicast Framework in Mobile Ad Hoc NetworksDocument7 pagesStudy The Effect of Node Distribution On Qos Multicast Framework in Mobile Ad Hoc Networksvol2no6No ratings yet
- 100620Document5 pages100620vol2no6No ratings yet
- 100622Document5 pages100622ebinrNo ratings yet
- 100619Document5 pages100619vol2no6No ratings yet
- 100610Document4 pages100610vol2no6No ratings yet
- 100617Document7 pages100617vol2no6No ratings yet
- 100616Document7 pages100616vol2no6100% (1)
- Cryptography of A Gray Level Image Using A Modified Hill CipherDocument4 pagesCryptography of A Gray Level Image Using A Modified Hill Ciphervol2no6No ratings yet
- 100613Document4 pages100613vol2no6No ratings yet
- 100611Document5 pages100611vol2no6No ratings yet
- A Specific Replication Strategy of Middleware Resources in Dense ManetsDocument5 pagesA Specific Replication Strategy of Middleware Resources in Dense Manetsvol2no6No ratings yet
- 100609Document6 pages100609vol2no6No ratings yet
- 100603Document10 pages100603vol2no6No ratings yet
- The Use of Mobile Technology in Delivering E-Learning Contents: UNITEN ExperienceDocument6 pagesThe Use of Mobile Technology in Delivering E-Learning Contents: UNITEN Experiencevol2no6No ratings yet
- Solution For Green Computing: Rajguru P.V., Nayak S.K. More D.SDocument4 pagesSolution For Green Computing: Rajguru P.V., Nayak S.K. More D.Svol2no6No ratings yet
- 100607Document4 pages100607vol2no6No ratings yet
- A Bidding Based Resource Allocation Scheme in Wimax: Mahasweta Sarkar and Padmasini ChandramouliDocument11 pagesA Bidding Based Resource Allocation Scheme in Wimax: Mahasweta Sarkar and Padmasini Chandramoulivol2no6No ratings yet
- Formal Specification For Implementing Atomic Read/Write Shared Memory in Mobile Ad Hoc Networks Using The Mobile UnityDocument13 pagesFormal Specification For Implementing Atomic Read/Write Shared Memory in Mobile Ad Hoc Networks Using The Mobile Unityvol2no6No ratings yet
- 100605Document10 pages100605vol2no6No ratings yet
- 100601Document6 pages100601vol2no6No ratings yet
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (894)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- IBM x3550 M1 Service GuideDocument196 pagesIBM x3550 M1 Service GuideRafie JuriNo ratings yet
- Question Total Quality ManagementDocument4 pagesQuestion Total Quality ManagementAztvNo ratings yet
- Automatic College Bell REPORTDocument61 pagesAutomatic College Bell REPORTDebashishParida100% (1)
- 2010 PAARL Standards For Academic LibrariesDocument6 pages2010 PAARL Standards For Academic LibrariesChristian Robert NalicaNo ratings yet
- Water Quality Monitoring Using Iot: Bachelor of EngineeringDocument19 pagesWater Quality Monitoring Using Iot: Bachelor of EngineeringMeghanaNo ratings yet
- Winter 2009Document48 pagesWinter 2009ed bookerNo ratings yet
- Java Placement QuestionsDocument23 pagesJava Placement QuestionsVidhya PrakashNo ratings yet
- BN20 e PreDocument59 pagesBN20 e PreTuan DinhNo ratings yet
- KC130GT 1Document2 pagesKC130GT 1aleenizzyNo ratings yet
- PC Programming Manual: KX-TDA30/KX-TDA100 KX-TDA200/KX-TDA600Document842 pagesPC Programming Manual: KX-TDA30/KX-TDA100 KX-TDA200/KX-TDA600anon_588155774No ratings yet
- Curve Weighting: Effects of High - End Non - LinearityDocument3 pagesCurve Weighting: Effects of High - End Non - LinearityhF2hFhiddenFaceNo ratings yet
- Pioneer Deh 1450ubDocument61 pagesPioneer Deh 1450ubluchoprado33% (3)
- Brksec-3005 (2017)Document100 pagesBrksec-3005 (2017)Paul ZetoNo ratings yet
- Pressure Calibrators: Low, Medium and High PressureDocument2 pagesPressure Calibrators: Low, Medium and High PressureMarcelo PellizzaNo ratings yet
- DS-160 Fault CodesDocument9 pagesDS-160 Fault CodesKrum KashavarovNo ratings yet
- Intel Inside.Document25 pagesIntel Inside.Rashed550% (1)
- Fidelityfx Cas: Lou Kramer, Developer Technology Engineer, AmdDocument92 pagesFidelityfx Cas: Lou Kramer, Developer Technology Engineer, AmdJohn K SmithNo ratings yet
- Final Survey SRM 4th Year ProjectDocument3 pagesFinal Survey SRM 4th Year ProjectJayita KarNo ratings yet
- Advanced Excel Formulas and FunctionsDocument80 pagesAdvanced Excel Formulas and FunctionsSanjay MoreNo ratings yet
- Date Sheet (MST-I)Document12 pagesDate Sheet (MST-I)Tauqeer AhmadNo ratings yet
- GUIDDocument215 pagesGUIDPrakashNo ratings yet
- Frontiers in Advanced Control SystemsDocument290 pagesFrontiers in Advanced Control SystemsSchreiber_DiesesNo ratings yet
- CIS Microsoft Exchange Server 2016 Benchmark v1.0.0Document66 pagesCIS Microsoft Exchange Server 2016 Benchmark v1.0.0Elisha MushaijaNo ratings yet
- HR Practices and Organizational Strategies in Select: IT Companies in India "Document59 pagesHR Practices and Organizational Strategies in Select: IT Companies in India "Sneha MehtaNo ratings yet
- Order 114-4827790-7059411Document1 pageOrder 114-4827790-7059411Anyoni CantiloNo ratings yet
- Teams HandbookDocument18 pagesTeams HandbookLudi D. LunarNo ratings yet
- CSE3003-Operating Systems-Laboratory-Practical ExercisesDocument9 pagesCSE3003-Operating Systems-Laboratory-Practical ExercisesXodiNo ratings yet
- Model Cards For Model ReportingDocument10 pagesModel Cards For Model Reportingoscar Julian Perdomo CharryNo ratings yet
- Forward Error Correction (FEC)Document6 pagesForward Error Correction (FEC)gamer08No ratings yet
- Assignment 2Document2 pagesAssignment 2ni60No ratings yet