Professional Documents
Culture Documents
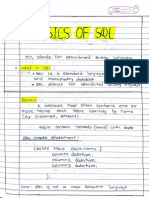
Seven Principles For Selecting Software Packages
Uploaded by
Jatin VarshneyOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Seven Principles For Selecting Software Packages
Uploaded by
Jatin VarshneyCopyright:
Available Formats
doi:10.1145/1787234 .
1 7 8 7 2 5 2
Everything you always wanted to know but
were afraid to ask about the decision-making
process.
by Jan Damsgaard and Jan Karlsbjerg
Seven
Principles
for Selecting
Software
Packages
Around the mid-1950s, in the early years of commercial
use of computers, all software systems were developed
in-house. There was no software industry in existence
at that time.15 As the software industry formed over
the next few decades, many organizations outsourced
their software development to specialized software
suppliers. Most software products ware a way to capture and black-box
were, however, still developed as best practices by embedding it into
unique systems for each organization; the standardized components of the
that is, there was little standardization. systems.16 Next in the standardization
The next step occurred when that soft- process was a step away from propri-
ware producers developed their own etary standard systems that essentially
proprietary software in order to cap- locked customers to a single software
ture economies of scale in developing producer to open software standards.37
the software once and then selling it to In principle, software built on open
multiple customers.2 This standardiza- standards allowed customers to source
tion process also benefitted software from any supplier that could supply
buyers by lowering transaction costs software in accordance with open stan-
and risks, as it was now possible to dards (for example, Java- and XML-
choose among a proven set of applica- based systems).
tions. Moreover, standardization gave Open standards meant that prices
both producers and buyers of soft- dropped and functionality was en-
au g ust 2 0 1 0 | vo l . 5 3 | no. 8 | c o m m u n i c ati o ns o f t he acm 63
practice
hanced, which resulted in a mass
market for many software application
types. In addition, software producers
had enough resources to make their
software even more general-purpose
oriented with larger feature sets that
were organized into a product.8 Soft-
ware became even more standardized,
and in the process, many local markets
were annexed into global markets. For
example, word processing software
was no longer produced specifically
for a particular profession or industry
or nation;26 instead, an almost uni-
versal office suite emerged, such as,
Microsoft Office. The generalized soft-
ware products could be configured in
various ways (for example, program
parameters, macro functionality, lan-
guage support, and so on) to suit spe-
cial needs among customers. These
highly configurable general purpose
software products came to be known
as software packages.23
Until recently in the IS academic
community, there has been a ten-
dency to focus on traditional studies
of software development and imple-
mentation of large custom-made sys-
tems.20,24 This has been despite the
leading trend that organizations use
“shrink wrapped” systems31 where the
core functionalities of the software are implementations are essentially iden- tions means the choice of software
identical across all implementations tical; that is, the main functionalities package has wide ripple effects for
in dozens, thousands or even millions are common to all adopters. While other parts of the organization whose
of different organizations.15 When the core components of a package software packages, implementations,
it comes to managing the process of are identical across all user organiza- and interests may not originally have
identifying and evaluating packages, tions, the implementation into an in- been identified or considered in the
the IS academic community has been dividual organizational information decision process regarding a new soft-
almost silent. infrastructure is usually configured in ware acquisition.
The aim of this article is to provide some manner to fit the requirements Packages are often referred to as
practitioners with a grounded set of of the organization.1,17,22 For the pur- “commercial off-the-shelf” software,31
principles to guide the selection of pose of this article, we define a stan- but open source systems (for example,
software packages. By principles, we dard software package as: a collection Open Office) or other types of nominal-
mean a set of fundamental ideas that of software components which when ly free software, for example, Firefox21
summarize important insights in soft- combined perform a set of generalized or Internet residing systems (for exam-
ware package acquisition that are not tasks that are applicable to a range ple, Google Apps) are other examples
(yet) embedded into the practice of of users. As a package is adopted by of packaged software. Some standard
buying software. The principles are in- many, it forms a standard because the software packages require little adjust-
terdependent and together they form a core components are identical across ment on the part of the user before they
whole that is larger than the sum of the all of its installations. The software can perform (for example, Internet Ex-
parts. Similar to Klein and Myers’ argu- package may be configured or custom- plorer), while other software packages
ment,19 the use of all principles is not ized to make it fit with specific require- are mere tools or platforms on top of
mandatory, but in each case it must be ments unique to the concrete imple- which specific functionalities required
judged whether, how, and which prin- mentation. This is accomplished by by the user can be implemented (for
ciples apply to a specific situation. setting program parameters, install- example, ERP systems).8 Some setups
ing add-on modules, or building in- of parameters may be common among
Packaged Software terfaces with other software systems. several customers, in which case the
Packaged software is a category of Within an organization, the growing producer can offer standard solutions
information systems for which all importance of system interconnec- on top of which only site-specific con-
64 communicat ions of t h e ac m | Au gust 2 0 1 0 | vo l . 5 3 | no. 8
practice
figurations need to be made.35 For ex- field study was conducted using semi- their knowledge and experience with
ample, the ERP producer SAP provides structured interviews. The persons corporate intranets. During the three
more than 25 industry solution portfo- interviewed were five senior directors years the nature of intranets changed
lios for large enterprises that embed with knowledge of—and some power from being home grown, to a situation
best practice (for example, SAP for oil to influence—software acquisition. To where a few local software companies
and gas). broaden our knowledge base, we also vigorously fought over market share,
carried out 34 interviews in 13 other to a situation where intranets were
Seven Guiding Principles for organizations. The interviewees were built upon international standards
Selecting Software Packages CIOs, CFOs, and general managers, and readily available from multiple
Here, we present the guiding prin- and were deliberately chosen because software houses. The seven principles
ciples for making a better informed of their high experience with software have now been presented and critically
choice when selecting software pack- package selection processes. All inter- reviewed at numerous IT managers’
ages. The first principle we label the views were recorded and transcribed conferences, and we are indebted to
founding principle because it is fun- and thematically coded. The longitu- the participants for many of the exam-
damental to the other six. For each dinal approach meant that a theme ples that illustrate the principles.
principle we provide examples that il- identified in one interview could be
lustrate its importance. further investigated and validated in The Fundamental First Principle:
The seven principles were derived subsequent interviews. When you buy packaged software
empirically from a field study and A second source of inspiration was you join its network.
from our understanding of software information about particular software Prior to the emergence of packaged
acquisition. The field study approach standards and packages, vendors, software, any organization that was us-
provided us with in-depth knowledge historic data about system compat- ing software in effect committed itself
Illustratio n by Jam es ga ry
of a number of standards decisions ibility, market shares, and mergers not only to a software product but also
made by actual organizations. The fo- and acquisitions. Yet another source to a particular software producer’s con-
cal company had more than 50,000 of inspiration came from participat- tinued ability to deliver new function-
employees, and we followed its soft- ing in an industry network in the late alities, as organizational requirements
ware acquisition processes and stan- 1990s where representatives from 60 evolved and new technology became
dard choices over three years. The companies met bimonthly to share available. In the present day, most of
au g ust 2 0 1 0 | vo l . 5 3 | no. 8 | c o m m u n i c ati o ns o f t he acm 65
practice
these commitments and dependen- ful users has repeatedly postponed the
cies have evolved from local software sunset date of Windows XP.
producers to global standard software Open source packages, on the con-
packages that can be sourced from, trary, are not owned by a single en-
and configured by, many independent
software vendors with the necessary The users tity; instead, the software is designed
specifically to promote shared own-
competences and technical skills.
The users and producers of a soft-
and producers ership.25,29 Open source software can
appear unattractive and risky to some
ware package constitute a network of of a software because there is no central point of
parties that share a common interest in
its destiny.34 The network is virtual, in
package constitute control from which advice about the
software package and its future devel-
the sense that the members probably a network of opment can be sought. Others view
do not know each other but neverthe-
less share a common interest in pro-
parties that share these properties as strengths since
they protect the standard package
tecting their investments and ensuring a common interest from the opportunistic actions of prof-
the continued evolution of the pack-
age. The network indirectly also has in its destiny. it maximizing software producers. We
shall not conclude the heated debate
other interests in common; for exam- over open source here, but merely em-
ple, the training and education of per- phasise that organizations adopting
sonnel.34 An organization’s purchase a software package need to be alerted
and implementation of a particular to the intimate connection between
software package thus means that the a software package and its associated
organization has joined the network network.
associated with the software package,
and the level of commitment is equal Principle Two:
to the size of the investment (buying Take a long-term perspective:
and configuring the software and the Look ahead but reason back.
training of personnel, and so on). To a Many choices made in the early stages
large extent, the investment represents of an organization’s use of computers
sunk costs,10 which make risk mitiga- have turned out to have surprisingly
tion activities even more central. long-lasting consequences, as both
The network around the package software and data standards have been
has implications for the purchasing shown to be very persistent.20 Many
decision and has to be considered as application types have historically de-
part of the investment decision. Be- veloped in an evolutionary manner,
yond the immediate network of users where the first simple implementa-
and producers, the extended network tions were custom built by innovators,
includes vendors, standard setting and then spread to a small number
institutions, government authori- of early adopters. As the application
ties and other compatible software type benefited its adopters, competing
products. It is imperative to choose to systems became available on the mar-
participate in the network that is per- ket, and finally the application type
ceived to provide the best long-term became a commodity, possibly to be
benefits as the organization, the net- bundled with other software applica-
work and package co-evolve. In the tion types into larger software pack-
network the distribution of power and ages. A similar evolution trajectory will
influence depends chiefly on who con- likely describe the development of fu-
trols the package and thereby its evolu- ture application types that first appear
tion. In the case of most software pack- as isolated systems. As a consequence,
ages, the producer wields the greatest organizations must take a long-term
power over the proprietary software perspective and envision a more com-
network, as they own the rights to the plex and connected future, or else they
package outright and thus control its risk implementing tomorrow’s legacy
further development. The producer’s systems.
power can be challenged if users unite We emphasize this long-term per-
to influence the producer or even chal- spective of software packages. As the
lenge the producer’s ownership; for pace of change in the computer in-
example, by reverse-engineering the dustry reduces the effective lifespan of
package’s functionality. As an example most hardware and software to a few
of influence, the pressure from power- years, the organizational data and the
66 communicat ions of t h e ac m | Au gust 2 0 1 0 | vo l . 5 3 | no. 8
practice
standards that define them are more perpetually, giving organizations the usability, etc. Most often, however,
durable.5 An organization’s standard choice of staying with the incumbent compatibility is not a clear binary issue.
package choice therefore involves par- producer or giving them time to look As standards and packages evolve and
ticipation in networks that may last a for migration paths toward a standard producers compete against each other,
decade or often longer. Shapiro and Var- package with more perceived vitality.17 packages may converge or diverge on
ian34 argue that when buying standard The one-way street scenario describes some features, such as, reaching or
technology we should look ahead but the situation where the organization is breaking compatibility.33 Of course,
reason back, noticing the network and left with little choice when it comes to this development can be caused by le-
the evolution process that produced it. buying upgrades or expansions to the gitimate technical design and imple-
We applaud and echo this advice that package. This is the case when the pur- mentation decisions, but it may also
is valid also when selecting packaged chase of a particular package in effect be caused by the producer’s perceived
software. This principle is useful to in- obliges the organization to place future advantage in changing the degree of
clude when comparing a proprietary purchases with the same software fam- compatibility or interoperability with
software package from a local vendor ily because the product has low compat- competing packages.
with that of a software package built ibility with other families of software A producer may differentiate its
upon an open global standard. or packages. In this situation, the orga- package from the competition by add-
nization may find itself chained to the ing proprietary features and unwar-
Principle Three: producer because the costs involved in ranted proprietary extensions to an
When choosing packaged software, switching to another package are pro- open standard. There are some calls for
there is safety in numbers. hibitively high, and the organization is the execution of this predatory business
One route to mitigating the perceived in effect locked-in.11 This is quite com- technique of “embrace, extend, and ex-
risk in purchasing packaged software is mon for ERP systems where once the tinguish,” and often Microsoft is associ-
to choose a package based on its histori- initial choice between (for example, ated with an almost flawless execution
cal and current success, as measured Oracle Financial Systems and SAP), has of the technique. Only the law suits that
by the financial success of the software been made, it becomes prohibitively doubtlessly follow spoil the perfection.
package’s producer and the size of the expensive to switch. Sometimes, a pack- One historical example is the fight be-
associated network. Flocking behavior age may be so successful in the market tween Sun and Microsoft over Java and
is a low risk strategy that is worth pur- that there are few—if any—viable alter- extensions to Java.32 The practice of add-
suing for software support of non-core native products available to the organi- ing proprietary extensions to an (open)
functionality and for companies that zation, an example of which is the cur- standard is successful when some
consider themselves followers. Below, rent choice of operating systems for PCs adopters find the proprietary features
we describe two scenarios representing being limited to Microsoft Windows, attractive and implement them. Howev-
opposite outcomes of a competition be- creating a near monopoly. However mo- er, it is important to be aware that pro-
tween software packages; namely, blind nopolies are constantly challenged and prietary features that might be useful
alleys and one-way streets.12 they are often short lived in the software for the singular adopter are in fact false
The blind alley scenario refers to the business, as reported by Chapman7 who gold for the network at large. Every time
situation where an organization has narrates the story of how WordPerfect a proprietary feature is implemented it
adopted a package that is losing its lost its near monopoly and how other adds to the switching costs, meaning
market share to competing packages. software packages such as Netscape that it will be harder to pull away from
David12 uses the term “angry orphan” and dBase lost their lucrative position the software package that embeds the
to describe the situation of the los- in the market. proprietary extensions.34 For the net-
ing package. He points out that such work, it means that proprietary fea-
products often show a sudden rapid Principle Four: tures become entrenched as de facto
development when they are losing the Focus on compatibility standards, and for the community in
battle. For example, the greatest speed and beware of false gold.a general, it becomes an insurmountable
of innovation in sail ships happened as Because of the long life expectancy of barrier to change, thus diminishing the
the steam engine challenged the sail as organizational data stored in some (of- value of a standard.
the leading propelling technology on ten proprietary) format (see Principle The break-down of open standards
sea voyages. Despite the sudden and Two), backward compatibility between happens in many cases where there is
remarkable development, sail boats software systems becomes a major fac- no central governance of a standard
never really challenged the inevitable tor when organizations consider new by a central institution or authority,
change to steam engine boats. In a software investments. Sometimes soft- and even if such governance does ex-
similar manner, the losing software ware adheres to one common standard, ist, standards often break down anyway
package might undergo rapid develop- enabling user organizations to choose as competitors extend the limits of the
ments, but shrinking network effects among competing packages based on standard.9 One example that we claim to
make the downward spiral inevitable. features such as price, performance, be false gold comes from the company
In a special case of the blind alley sce- Linksys (owned by Cisco) which has ex-
nario, the losing package manages to a By false gold or fool’s gold we mean something
tended its wireless network equipment
capture a niche market network where that appears attractive but in reality is not valu- with proprietary protocols, thus dou-
it may sustain itself for years—or even able at all. bling the throughput of the non-propri-
au g ust 2 0 1 0 | vo l . 5 3 | no. 8 | c o m m u n i c ati o ns o f t he acm 67
practice
etary protocol IEEE 802.11b. While the but for several reasons, could turn out Producers employ various strat-
products are still backward compat- to be false gold.20,23,35 First of all, the egies for ensuring a pool of knowl-
ible with the open standard backed by customization is often expensive and edgeable users for their software.11
the IEEE, Linksys gives users a strong represents sunk costs that, in practice, One strategy is to produce free or
incentive to use Linksys hardware ex- limit the choices when the package or low cost versions so that interested
clusively. Another large manufacturer, service contract is up for renewal.5,20 people will be more likely to sample
D-Link, does exactly the same thing; Second, when upgrading the software it. Another variation is to make “aca-
however, the proprietary extensions to the next version, usually all custom- demic versions” of the software pack-
of D-Link and Linksys are not compat- izations have to be re-implemented. In age available as free downloads, or to
ible. For the community, the danger addition, the new features of the next bundle the package with textbooks
of proprietary extensions is that it may version are obviously not part of the cus- used in educational institutions. The
not be compatible with the next genera- tomization that was implemented from process of institutionalizing skills is
tion of the open standards (in this case the previous version.8 Beatty and Wil- more complex for packages based on
IEEE 802.11n), and if the proprietary liams5 recommend “un-customizing open source (sendmail, emacs, Linux,
extensions have become entrenched, customizations” before any upgrade is among others), where there may be no
none is willing to adopt the next open attempted because they are found to single trusted certifying institution
standard version. Thus, the network form major technical obstacles and are corresponding to the owner or vendor
has moved from a situation where or- the main threat to achieving a Return of a package. Instead, other forms of
ganizations could choose to buy open on Investment. Instead, Beatty and Wil- legitimization are used, such as a per-
standard compatible equipment from liams5 propose that an upgrade is an son’s rank in recommender-systems
a number of independent suppliers to a opportunity to review critically existing such as discussion Web sites. Such on-
situation where standard evolution has customizations in order to determine line networks also make it possible to
stopped and there is only one supplier whether they are really needed, and if determine the contributions of a par-
of a proprietary de facto standard. In so, to determine if they are supported ticular member, enabling potential
fairness, it should be noted that neither in the new version and eligible for elim- employers to retrieve an account of a
D-Link nor Linksys has been successful ination. In line with this, we advocate person’s skills in regard to a particular
in their effort to manifest their propri- avoiding any comprehensive custom- software package.
etary extensions as de facto standards; ization of packaged software, unless The co-development of the two
however, the risk remains. absolutely necessary. networks (that of the producers and
Organizations should keep their that of the users) has high path de-
options open by buying packaged Principle Five: pendence to the point of being quasi
software that is close to compatible Choose a software package irreversible.11 For a new competing
standards; and if they are already us- with accessible knowledge. software package that starts with es-
ing proprietary standard packages, When an organization chooses to use sentially no network; the existing net-
they should keep their eyes open for custom-built software, it must carry work forms a formidable entry barrier
gateway standards as a way to break an the entire burden of training and re- that is difficult to break.6 If the new
existing lock-in to a proprietary exten- taining personnel to develop the nec- package is proprietary and the own-
sion.13 At the very least, organizations essary skills to use the software. The ers are willing to invest, one way for
should be conscious of the adoption use of packages, however, promises the new standard package to achieve
of proprietary extensions, document access to knowledge of the package’s a critical mass of users is for the own-
their use in the organization, and con- application and implementation. Ide- er to bear some or all of the costs for
sider which steps will be necessary to ally, the network of organizations us- the organizations willing to switch.33
discontinue their use in the future; that ing a package is matched by a network An alternative approach is to invest
is, a viable exit strategy. of individuals competent in configur- in building gateway features into the
Generic software packages do not ing and using it, but often the supply new standard package, thus easing
meet all the requirements of an organi- and demand of certain skills is not the transition from an incumbent
zation;8,28 there are therefore plenty of aligned, as is pointed out by Light.23 package.13 When Microsoft Word was
options offered as part of the package If there is an unmet demand for winning over the majority of the word
to configure it as needed.16,30 Often local knowledge and skills, both user and processing market from WordPerfect
practices or cultural issues add to the producer organizations suffer. One in the first half of the 1990s, Microsoft
desire to customize or localize the pack- historical example of misaligned net- sought to circumvent the knowledge
age.5,22 Customization is different from works is that of ERP systems, where barriers by providing WordPerfect us-
configuration in that customization the number of people with knowledge ers an easy passage. Microsoft Word
is more radical and adds functionality and skills of the configuration of SAP featured two gateways: an alterna-
that was not an intended generic feature systems is far less than the demand tive user interface where Microsoft
in the original package. Customization from user organizations. The result is Word could be made to emulate the
is more lucrative for local software ven- disproportionately high costs for the keyboard shortcuts of WordPerfect,
dors compared to selling the package it- people component of SAP implemen- and “Help for WordPerfect users”
self. For the adopting organization, the tations and delayed projects with re- where the use of Microsoft Word was
option to customize may appear shiny, duced or poor functionality. explained in terms that WordPerfect
68 communicat ions of t h e ac m | Au gust 2 0 1 0 | vo l . 5 3 | no. 8
practice
users were accustomed to. We suggest two reasons: seeking backward com-
using this principle to assess the avail- patibility with data stored in legacy
able knowledge base for the software systems, or seeking to ensure access
package. to the data from other information
Principle Six: By choosing systems in the future; that is, forward
compatibility. By choosing an open
Choose packaged software with
the right type of standardization.
an open standard, standard, an organization can usually
choose between numerous compat-
Standardization can be achieved at an organization ible software packages, thus bringing
various levels and in many forms in
packaged software. Here, we provide
can usually choose the simple advantage of choice. The
disadvantage is that the user organiza-
an overview of the most common types between numerous tion must abstain from using any pro-
of standardization because it is impor-
tant to choose the type that is right for
compatible prietary features or extensions of the
packages chosen (the false gold men-
the particular organization, accord- software packages, tioned in Principle Four) in order to
ing to its available resources and con-
straints. thus bringing the maintain strict data standardization.
Examples of data standards with wide
Standardization of user interface is simple advantage vendor support are the all-purpose in-
a common strategy employed to limit
the need for user training. After some of choice. formation formatting languages XML
and the database query language SQL,
experimental implementations of in- although both are also subject to stan-
formation systems of a particular type, dard deviations among the implemen-
a dominant design typically emerges, tations from various producers.
resulting in striking similarities of More advanced modes of standard-
user interfaces among different soft- ization of data interfaces include inter-
ware systems. Referring to Web site de- connectivity and interoperability.4 In-
sign guru, Nielsen,27 users spend most teroperable information systems are
of their time on other sites, and there- able to communicate during the exe-
fore prefer new Web sites to be de- cution of a particular task. An everyday
signed similar to the sites with which example is that the functionality of an
they are familiar. Dominant designs electronic spreadsheet program can
sometimes become static and end up be employed by a word processing pro-
as anachronisms when the surround- gram to perform a calculation inside a
ings change. For example, the diskette text document. More advanced imple-
icon featured in most software appli- mentations allow interoperability be-
cations invokes the “save” function, tween software running on separate
even though no files are ever saved to computers - even in different locations
diskettes and personal computers no or organizations such as most Web
longer have disk drives. services organized in serviced oriented
In standardization of output, the architectures (SOA).14 Features such
software package’s only compatibil- as these will have far-reaching impli-
ity restraint is that it must produce an cations for the implementation of
output that can be used by recipient standard software packages and inter-
users or software. One example is that organizational information systems in
of Web page production, where dif- the coming years.
ferent departments in an organiza- Organizations may choose stan-
tion may use very different production dardization of skills by employing only
techniques as long as their Web pages people with a particular education or
satisfy agreed-upon requirements. skill set, or if necessary, to carry the
This standardization strategy has the cost of training new employees to some
strength of allowing users greater free- formalized level of training (see Prin-
dom to optimize and personalize their ciple Five). Organizations can choose
production methods. The strategy also to standardize two types of skills: ge-
has serious drawbacks if the users ever neric or specific skills. Generic skills
need to share intermediate data; we are skills that are acquired through
would thus not recommend this strat- education, such as critical thinking,
egy for most organizational standard- programming, business knowledge,
ization issues. and so on Specific skills encompass
An organization might choose stan- a user’s qualifications with a particu-
dardization of data structure for one of lar software package, and these may
au g ust 2 0 1 0 | vo l . 5 3 | no. 8 | c o m m u n i c ati o ns o f t he acm 69
practice
be certified by the product’s producer adopt its predecessor today by joining
or a trusted third party (see Principle its network. Being part of the network
Five). Every major vendor in the pack- will also ensure that special needs are
aged software market has such certi- noted and incorporated into the next
fication programs, and many are even
updated on a continual basis, forcing We promote a version of the package.
certificate holders to take new exams
in order to preserve their status.
view of buying Conclusion
Software packages are replacing cus-
One might argue that if all are using software as a tom built software at a fast pace. Yet,
the same standard software package,
where does competitive advantage
continuous process there is little available advice on how to
evaluate and choose among the offered
come from? As a rule of thumb, we rec- of constantly packages. This article highlights seven
ommend organizations to follow and
standardize in all non-core areas to
trying to match principles that are related to selecting
and assessing software packages. The
bring down costs, and in order to dif- available packages principles extend beyond the two ob-
ferentiate themselves, organizations
must be prepared to lead (be an early with a base of vious but narrow factors of price and
immediate features, to include a wider
adopter) and tolerate a higher degree already installed networked and multilateral view of soft-
of standard uncertainty in core areas.
We will return to the issue of competi- information ware packages. We promote a view of
buying software as a continuous pro-
tive advantage in the conclusion. systems, while cess of constantly trying to match avail-
able packages with a base of already
Principle Seven: anticipating future installed information systems, while an-
All journeys start with
a first step.
organizational ticipating future organizational needs
and advantages in technology. Compa-
In a market of fast update cycles and needs and nies should seek to select the package
many options, some buyers may as-
sume a wait-and-see position, while advantages in that fits their situation. However, this is
not a unilateral decision, as other com-
they let the rest of the market test out technology. panies’ actions also contribute to the
competing products, determine the destiny of the package. Software pack-
necessary feature sets, and so on.3,20 Of ages are networked and built around
course, this strategy will mitigate the standards that allow (and disallow) con-
risks of investing time and money in nection to other software systems and
a software package which later loses these considerations must be added to
in the market, but we advise organiza- the equation, too. It is therefore neces-
tions not to fall into the wait-and-see sary to adopt a multilateral approach
trap for the following two reasons. that asserts the benefits of participation
First, a winner will only emerge when from as many parties as possible in the
organizations actually buy software, selection process.
so an organization stands a greater The proposed principles are useful
chance of finding software that fits its in several ways. First, they form a refer-
needs if it plays an active role in the se- ence point for IT managers when en-
lection process (invest in the package). gaging in software acquisition. Second,
Second, the further development without the principles, IT managers
of packages is inevitable, and thus it would have to spend much time con-
is very likely that while an organiza- densing these foundations from avail-
tion is waiting for a package to appear able theoretical and empirical sources.
in the marketplace for a perfect fit, its Third, the principles help IT managers
requirements may have changed. In ensure that vital aspects of the soft-
fact, it may never be possible to find ware package acquisition process have
a perfect match.36 After a prolonged not been left out or neglected. Finally,
sampling process and the organization the set of principles is an invitation to
finally selecting a software package, formulate a disagreement and start a
activities such as conversion of legacy discussion on what constitutes sound
data may turn into considerable tasks, software acquisition practices.
as there may be no personnel with ex- Here is a checklist that IT managers
pertise in both the legacy system and can consider in addition to the usual
the new software package.20 There- technical features and price, when eval-
fore, the best strategy to ensure that a uating a software package purchase:
better package is there tomorrow is to ˲˲ What companies are involved in
70 communicat ions of t h e ac m | Au gust 2 0 1 0 | vo l . 5 3 | no. 8
practice
producing the package? but after more than a year of attempt- Policy 3 (1988), 165–202.
14. Erl, T. Service-Oriented Architecture: Concepts,
˲˲ How many companies are already ing to implement the new ERP system Technology, and Design. Prentice Hall, Upper Saddle
using the package? the manufacturer had to revert to its old River, NJ, 2005.
15. George, J.F. (ed.) The Origins of Software: Acquiring
˲˲ How many software companies ERP system. The skill set and knowl- Systems at the End of the Century. Framing the
can configure the package? edge base built around the former ERP Domains of It Management: Projecting the Future
through the Past. Pinnaflex Educational Resources,
˲˲ What is the history of the package? system in practice inhibited a switch. Inc., Cincinnati, OH, 2000.
˲˲ Is the package built upon open Returning to the competitive ad- 16. Howcroft, D. and Light, B. Reflections on issues of
power in packaged software selection. Information
standards? vantage discussion initiated earlier Systems Journal 16, 3 (2006), 215–235.
˲˲ How is the fit with other packages? 17. Karlsbjerg, J. Staying outside the mainstream:
and playing the devil’s advocate, one An empirical study of standards choices. Hawaii
˲˲ What kind of standardization does might argue that if everybody were International Conference on System Sciences, Hawaii,
2002.
the package represent? using the same software packages, 18. Karlsbjerg, J., Damsgaard, J., and Scheepers, R. A
˲˲ Is customization of the package where would competitive advantage taxonomy of Intranet Implementation strategies:
To make or to buy? Journal of Global Information
necessary? in the form of differentiation come Management 11, 3 (2003), 151–165.
˲˲ Is there an accessible knowledge from? Succinctly put as a paradox, “In 19. Klein, H.K. and Myers, M.D. Evaluating interpretive field
studies. MISQ 23, 1, 67–94
base for the implementation and ex- the world of software packages, ad- 20. Khoo, H.M. and Robey, D. Deciding to upgrade packaged
ploitation of the package? vantage comes from having the same software: A comparative case study of motives,
contingencies and dependencies. European Journal of
˲˲ What are the costs of switching to packages as everybody else before Information Systems 16, 5 (2007), 555–567.
an alternative package? they do.” Thus, competitive advan- 21. Klein, B. 1998. Microsoft’s use of zero price bundling
to fight the browser wars. The Progress & Freedom
˲˲ What are the implications of post- tage is gained from being able to spot Foundation. Kluwer Academic Publishers, Washington,
poning a decision to adopt? and adopt the packages of the future DC, 1998.
22. Kutar, M. and Light, B. Exploring cultural issues in the
In what direction is the package before they have become the de facto packaged software industry: A usability perspective.
evolving? And is our company headed standard packages, and to identify In Proceedings of the 13th European Conference on
Information Systems (Regensberg, Germany, 2005).
the same way? and phase out the packages of the past 23. Light, B. Potential pitfalls in packaged software
adoption. Commun. ACM 48, 5 (May 2005), 119–121.
The principles can be used prior to before they become legacy systems. 24. Light, B. and Sawyer, S. Locating packaged software
making an investment and be used to in information systems research. European Journal of
Information Systems 16, 5 (2007), 527–530.
monitor the vitality of existing packag- This research was in part supported by the Danish 25. Ljungberg, J. Open source movements as a model for
es. To illustrate, when a university built Research Foundation, grant number 331958. organizing. European Journal of Information Systems.
(Dec. 2000).
a new campus building it came with a 26. Moore, G.C. End user computing and office automation:
References
free proprietary facility management 1. Adam, A. and Light, B. Selling packaged software: An
A diffusion of innovations perspective. Infor 25 (1987),
214–222.
system with the new building already ethical analysis. In Proceedings of the 12th European 27. Nielsen, J. User interface directions for the Web.
Conference on Information Systems. (Turku, Finland,
encoded. However, using the seven 2004).
Commun. ACM 42, 1 (Jan. 1999), 65–72.
28. Pollock, N., Williams, R., and Procter, R. Fitting standard
principles, the university management 2. Attewell, P. Technology diffusion and organizational software packages to non-standard organizations: The
learning: The case of business computing. Organization
decided that even though the package Science 3, 1 (1992), 1–19.
‘biography’ of an enterprise-wide system. Technology
Analysis and Strategic Management 15, 3 (2003),
itself was free of charge, the supporting 3. Au, Y.A. and Kauffman, R.J. Should we wait? Network 317–332.
externalities and electronic billing adoption. Hawaii 29. Raymond, E.S. The Cathedral and the Bazaar:
network around the package was too International Conference on System Sciences. (Hawaii, Musings on Linux and Open Source by an Accidental
local and too small for the university to 2001). Revolutionary. O’Reilly, 1997.
4. Bailey, J., McKnight, L., and Bosco, P. The economics 30. Sawyer, S. Effects of conflict on packaged software
invest in encoding the remainder of its of advanced services in an open communications development team performance. Information Systems
buildings into the package. infrastructure: Transaction costs, production costs, and Journal 11, 2 (2001), 155–178.
network externalities. Information Infrastructure and 31. Sawyer, S. Information systems development: A
Another example of the application Policy 4 (1995), 255–277. market-oriented perspective. Commun. ACM 44, 11
of the principles was the company in 5. Beatty, R.C. and Williams, C.D. ERP II: Best practices (Nov. 2001), 97–102.
for successfully implementing an ERP upgrade. 32. Shankland, S., Kanellos, M. and Wong, W. Sun and
the field study mentioned earlier. The Commun. ACM 49 (Mar. 2006), 105–109. Microsoft settle Java suit. News.com, 2001.
company used the principles to annu- 6. Besen, S.M. and Farrell, J. Choosing how to compete: 33. Shapiro, C. and Varian, H.R. The art of standards wars.
Strategies and tactics in standardization. Journal of California Management Review 41, 2 (1999), 8–32.
ally monitor the decision to stay with Economic Perspectives 8, 2 (1994), 117–131. 34. Shapiro, C. and Varian, H.R. Information Rules: A
7. Chapman, M.R. In Search of Stupidity: Over 20 Years of
a package that had been dominant but High-Tech Marketing Disasters. Apress, Berkeley, CA,
Strategic Guide to the Network Economy. Harvard
Business School Press, Boston, MA, 1999.
was losing market share. The question 2003. 35. Sia, S.K. and Soh, C. An assessment of package-
8. Chiasson, M.W. and Green, L.W. Questioning the IT
was straightforward: Was the network artefact: User practices that can, could, and cannot be
organization misalignment: Institutional and
ontological structures. European Journal of
of users around the software package supported in packaged-software designs. European Information Systems 16, 5 (2007), 568-583.
Journal of Information Systems 16, 5 (2007), 542–554.
sufficiently large to provide the pack- 9. Damsgaard, J. and Lyytinen, K. The role of
36. Truex, D.P., Baskerville, R., and Klein, H. Growing
systems in emergent organizations. Commun. ACM 42,
age owner with revenue that allowed intermediating institutions in diffusion of electronic 8 (Aug. 1999), 117–123.
data interchange: How industry associations in the 37. West, J. The economic realities of open standards:
it to invest in developing the package? grocery sector intervened in Hong Kong, Finland, Black, white and many shades of gray. Standards
For a number of years the answer was and Denmark. The Information Society 17, 3 (2001), and Public Policy. S. Greenstein and V. Stango (eds.).
195–210. Cambridge University Press, Cambridge, MA, 2007.
positive, but when the network was 10. David, J.S., Schuff, D., and Louis, R.S. Managing your
deemed inadequate, it was decided to total IT cost of ownership. Commun. ACM 45, 1 (2002),
101-106.
switch to the dominant package.17 An Jan Damsgaard (jd.caict@cbs.dk) is director and a
11. David, P.A. Clio and the economics of Qwerty. The
professor at the Center for Applied ICT, Copenhagen
illustration of Principle Five and Six is American Economic Review 75, 2 (1985), 332–337.
Business School, Denmark School of Information
12. David, P.A. Narrow Windows, Blind Giants, and
as follows: One large manufacturer had Systems, Curtin University of Technology, Australia.
Angry Orphans: The Dynamics of Systems Rivalries
already implemented one ERP system and Dilemmas of Technology Policy. Technological
Jan Karlsbjerg (jan@jankarlsbjerg.com) is an associate
Innovation Project (No. 10), Stanford University, CA,
when a vendor offered a competing product manager at Active Community Solutions,
1986.
Vancouver, Canada.
13. David, P.A., and Bunn, J.A. The economics of Gateway
ERP system at a very competitive price. technologies and network Evolution: Lessons from
The manufacturer attempted to switch electricity supply history. Information Economics and © 2010 ACM 0001-0782/10/0800 $10.00
au g ust 2 0 1 0 | vol . 5 3 | no. 8 | c o m m u n i c at i o ns o f t he acm 71
Copyright of Communications of the ACM is the property of Association for Computing Machinery and its
content may not be copied or emailed to multiple sites or posted to a listserv without the copyright holder's
express written permission. However, users may print, download, or email articles for individual use.
You might also like
- SQLScript Syntax For SAP HANADocument11 pagesSQLScript Syntax For SAP HANAcharancccNo ratings yet
- Oracle Payroll - SQL QueriesDocument2 pagesOracle Payroll - SQL QueriesRinita BhattacharyaNo ratings yet
- Oracle APEX 5 - Workshop 1 (SG1) (D79653GC20 - sg1) - (2015) PRINT PDFDocument430 pagesOracle APEX 5 - Workshop 1 (SG1) (D79653GC20 - sg1) - (2015) PRINT PDFstda100% (1)
- ITE183 Final Exam NotesDocument13 pagesITE183 Final Exam NotesRenli Dela CruzNo ratings yet
- Pi Odbc ManualDocument117 pagesPi Odbc ManualJordi Cebrián100% (1)
- Teradata Utilities - Breaking The BarriersDocument128 pagesTeradata Utilities - Breaking The Barrierssaurav560No ratings yet
- INV Transactions Errors - Document 1063689.1 PDFDocument10 pagesINV Transactions Errors - Document 1063689.1 PDFappsloaderNo ratings yet
- Connecting A S7-1500 To A SQL DatabaseDocument27 pagesConnecting A S7-1500 To A SQL DatabaseGlauco SantiagoNo ratings yet
- JRMSU Student Government Online Voting System Through Web and Android ApplicationDocument100 pagesJRMSU Student Government Online Voting System Through Web and Android Applicationedmjds100% (2)
- SAFECode Dev Practices0211Document56 pagesSAFECode Dev Practices0211nojeviveNo ratings yet
- ERP in FMCG CompanyDocument48 pagesERP in FMCG Companysaur028No ratings yet
- Software Engineering - NotesDocument172 pagesSoftware Engineering - NotesJASPER WESSLY100% (4)
- ICTSAD609 Project Portfolio.v1.0Document21 pagesICTSAD609 Project Portfolio.v1.0Sundas Ansari100% (1)
- Agile Process Model 1Document44 pagesAgile Process Model 1Nethuli VihasnaNo ratings yet
- GXPDocument8 pagesGXPMichele Vasconcellos0% (1)
- Software Testing Interview Questions You'll Most Likely Be Asked: Job Interview Questions SeriesFrom EverandSoftware Testing Interview Questions You'll Most Likely Be Asked: Job Interview Questions SeriesNo ratings yet
- Identifying Key Stakeholders As Part of Requirements Elicitation in Software EcosystemsDocument8 pagesIdentifying Key Stakeholders As Part of Requirements Elicitation in Software Ecosystems26nkn4xh96No ratings yet
- 3 Development of Enterprise SystemsDocument38 pages3 Development of Enterprise SystemsMagarsa BedasaNo ratings yet
- Prototyping - Alternative SystemsDocument8 pagesPrototyping - Alternative SystemsWhitney LeSueurNo ratings yet
- Unit 10 It Packages in SCM: ObjectivesDocument21 pagesUnit 10 It Packages in SCM: ObjectiveskNo ratings yet
- Process Management in Operating System Research PaperDocument7 pagesProcess Management in Operating System Research Paperfvey0xan100% (1)
- Enterprise Resource Planning: An Open Source SystemDocument3 pagesEnterprise Resource Planning: An Open Source SystemAlviNo ratings yet
- SBL Lecture 20Document22 pagesSBL Lecture 20Alseraj TechnologyNo ratings yet
- Modern Systems Analysis and Design 7th Edition Hoffer Solutions ManualDocument36 pagesModern Systems Analysis and Design 7th Edition Hoffer Solutions Manualinsuliteskinch4wjca100% (12)
- Chapter 2 - The Origins of SoftwareDocument26 pagesChapter 2 - The Origins of Softwareلوي وليدNo ratings yet
- (Article) Software Documentation and Readability - A Proposed Process Improvement (1998)Document3 pages(Article) Software Documentation and Readability - A Proposed Process Improvement (1998)AbusamraMousaNo ratings yet
- ERP CLOUD and Open SourceDocument15 pagesERP CLOUD and Open SourceAKHIL JOSEPHNo ratings yet
- A Framework For Software Product Line Practice, Version 5.0: What's New in Version 5.0Document258 pagesA Framework For Software Product Line Practice, Version 5.0: What's New in Version 5.0Satana UccisoreNo ratings yet
- AssignmentDocument9 pagesAssignmentAkib ZabedNo ratings yet
- Nico Assignment SADDocument16 pagesNico Assignment SADNicolas Lich MatuenyNo ratings yet
- Hris Project On Erp Softwares: Submitted To: By: Ms Teena Bagga Taru Taneja Shalini BahadurDocument23 pagesHris Project On Erp Softwares: Submitted To: By: Ms Teena Bagga Taru Taneja Shalini BahadurtarutanejaNo ratings yet
- Lecture 1Document33 pagesLecture 1ayesha.anwarNo ratings yet
- Chapter - 3 Requirement Specification: 3.1 Functional RequirementsDocument3 pagesChapter - 3 Requirement Specification: 3.1 Functional RequirementsSuraj BahadurNo ratings yet
- 04 - Competing in A Digital World Four Lessons From The Software IndustryDocument6 pages04 - Competing in A Digital World Four Lessons From The Software IndustryAna GonzalezNo ratings yet
- The Multimedia Development ProcessDocument2 pagesThe Multimedia Development ProcessKyrelle Pauline Dimacutac SolisNo ratings yet
- Systems Analysis and Design 11th Edition Tilley Solutions ManualDocument7 pagesSystems Analysis and Design 11th Edition Tilley Solutions Manualbdelliumdimehqa100% (21)
- Systems Analysis and Design 11Th Edition Tilley Solutions Manual Full Chapter PDFDocument28 pagesSystems Analysis and Design 11Th Edition Tilley Solutions Manual Full Chapter PDFdariusluyen586100% (6)
- Support Solutions For Your Open Source Software EnvironmentDocument10 pagesSupport Solutions For Your Open Source Software EnvironmentAnirudha BhamidipatiNo ratings yet
- Question 1) Explain Requirements Elicitation Techniques? Answer 1) Equirements Elicitation Is Perhaps The Most Difficult, Most Error-Prone and MostDocument14 pagesQuestion 1) Explain Requirements Elicitation Techniques? Answer 1) Equirements Elicitation Is Perhaps The Most Difficult, Most Error-Prone and Mostsarthak sharmaNo ratings yet
- 2 - Cómo Implementar QSOSDocument5 pages2 - Cómo Implementar QSOSroberto.monges2No ratings yet
- Enterprise System Week08Document28 pagesEnterprise System Week08Muhammad Fajar PamungkasNo ratings yet
- Software Engineering - 1Document13 pagesSoftware Engineering - 1usmanyakubu541No ratings yet
- Questions and Answers On Software Engineering CIT 745: SUNDAY, 4 MAY 2014Document5 pagesQuestions and Answers On Software Engineering CIT 745: SUNDAY, 4 MAY 2014Nur AsnidaNo ratings yet
- Operating System Research Papers TopicsDocument4 pagesOperating System Research Papers Topicsqzetcsuhf100% (3)
- 1.vision and MissionDocument14 pages1.vision and MissionSnehal MhasavekarNo ratings yet
- Chapter 01Document23 pagesChapter 01devanshkhurana2211No ratings yet
- Operating System Research Papers 2014Document6 pagesOperating System Research Papers 2014eh041zef100% (1)
- Module 1 - Introduction To Software EngineeringDocument24 pagesModule 1 - Introduction To Software EngineeringdashendranNo ratings yet
- PaigeDocument17 pagesPaigeSHUBHAM POLNo ratings yet
- A Devops1 PDFDocument9 pagesA Devops1 PDFkiranNo ratings yet
- Managing Agile Project Requirements With Storytest-Driven DevelopmentDocument9 pagesManaging Agile Project Requirements With Storytest-Driven DevelopmentJae Ho Vince HwangNo ratings yet
- Alternative System Building ApproachDocument21 pagesAlternative System Building ApproachMalik Shahzeb KhanNo ratings yet
- Best Practices For: Managing Software Intellectual PropertyDocument12 pagesBest Practices For: Managing Software Intellectual PropertyM Yasir HassanNo ratings yet
- Bijlsma 06 Reference PDFDocument11 pagesBijlsma 06 Reference PDFBalaji RamasubramanianNo ratings yet
- Homework Chapter 2Document4 pagesHomework Chapter 2Angela PintoNo ratings yet
- SAD-chap5 (Update Mac2021)Document31 pagesSAD-chap5 (Update Mac2021)Sharifah NurulhikmahNo ratings yet
- Exam NotesDocument27 pagesExam NotesAbdighaniMOGoudNo ratings yet
- Software FileDocument12 pagesSoftware FileSANDEEP CHAUHANNo ratings yet
- Approach For Mis DesignDocument22 pagesApproach For Mis DesignSudhir Bodduluri50% (2)
- 3 AgileDocument41 pages3 AgileAbdullah ButtNo ratings yet
- NextLevel! Newsletter by AuguryDocument4 pagesNextLevel! Newsletter by AuguryplarivNo ratings yet
- Software Systems and Application SoftwareDocument13 pagesSoftware Systems and Application SoftwareAditya Singh67% (3)
- Essentials of System Analysis and Design 4th Edition by Valacich George and Hoffer ISBN Solution ManualDocument8 pagesEssentials of System Analysis and Design 4th Edition by Valacich George and Hoffer ISBN Solution Manualalison100% (29)
- Solution Manual For Essentials of System Analysis and Design 4Th Edition by Valacich George and Hoffer Isbn 0136084966 9780136084969 Full Chapter PDFDocument29 pagesSolution Manual For Essentials of System Analysis and Design 4Th Edition by Valacich George and Hoffer Isbn 0136084966 9780136084969 Full Chapter PDFpatrick.coutee753100% (11)
- 08 Handout 1 (Finals)Document4 pages08 Handout 1 (Finals)Emmanuel DelarosaNo ratings yet
- Systems Development Life CycleDocument11 pagesSystems Development Life CyclendebeleashleydNo ratings yet
- 01 - What Is SoftwareDocument6 pages01 - What Is SoftwareRavindu GamageNo ratings yet
- SDTM 3.1 Implementation Guide v1 01Document6 pagesSDTM 3.1 Implementation Guide v1 01kavithaipriya4987No ratings yet
- Azure Container ServicesDocument14 pagesAzure Container Servicesamish rajNo ratings yet
- AI & DS Lab Experiments R2021Document22 pagesAI & DS Lab Experiments R2021keerthigaNo ratings yet
- SQL QuestionsDocument16 pagesSQL QuestionsMahera ShaikhNo ratings yet
- DP 3 2 PracticeDocument5 pagesDP 3 2 PracticeJessica IreneNo ratings yet
- SQL Questions CarsDocument3 pagesSQL Questions CarssamarthNo ratings yet
- DBI202Document51 pagesDBI202Nguyen Hai Anh (K17 HL)No ratings yet
- SQL Server Full Joi PDFDocument4 pagesSQL Server Full Joi PDFJefferson Jhon Delgado VasquezNo ratings yet
- SQL Basics HandwrittenDocument9 pagesSQL Basics HandwrittenProfessorNo ratings yet
- DBMS All UnitsDocument134 pagesDBMS All UnitsGayathri Bhupathi rajuNo ratings yet
- Chapter 1 - Database SystemsDocument34 pagesChapter 1 - Database SystemsDaniel BirhanuNo ratings yet
- SastasafarDocument9 pagesSastasafarRaheel RasheedNo ratings yet
- Dbms 2 MarksDocument17 pagesDbms 2 MarksPraveen KumarNo ratings yet
- An Introduction To Basics of Interfaces in Oracle Apps.: Interface Basics (AP r12 - AR - GL)Document15 pagesAn Introduction To Basics of Interfaces in Oracle Apps.: Interface Basics (AP r12 - AR - GL)kumar_amit_99No ratings yet
- SQL Backtrack TSM ConfigurationDocument21 pagesSQL Backtrack TSM ConfigurationVasanth KumarNo ratings yet
- BDI Tema11 Danuta LaurentiuDocument3 pagesBDI Tema11 Danuta LaurentiuLaurentiu DanutaNo ratings yet
- Microsoft Access RelationshipsDocument15 pagesMicrosoft Access RelationshipsHelder DuraoNo ratings yet
- Design of An Automated Library Management System For State Universities in NigeriaDocument6 pagesDesign of An Automated Library Management System For State Universities in NigeriaIkechukwu OkeyNo ratings yet
- Virtual Vault Best PracticesDocument33 pagesVirtual Vault Best Practicessalman01inNo ratings yet
- SQL Sales ManagementDocument6 pagesSQL Sales ManagementDIVYANSHMUDGAL RA1711003020646No ratings yet
- Phpmyadmin DB NotesDocument25 pagesPhpmyadmin DB NotesrobeecalNo ratings yet
- DBMS LabDocument10 pagesDBMS LabMNo ratings yet
- Connecting To Data SourcesDocument394 pagesConnecting To Data SourceskhaleelapNo ratings yet