Professional Documents
Culture Documents
Guarding Against DB Anti-Forensics
Uploaded by
Tuan Anh NguyenOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Guarding Against DB Anti-Forensics
Uploaded by
Tuan Anh NguyenCopyright:
Available Formats
Guarding against database anti-forensics
Page 1 of 4
Published on Network World Asia (http://www.networksasia.net)
Guarding against database anti-forensics
By Cesar Cerrudo | Nov 18, 2009 Database hacking has gone mainstream and is becoming harder to detect because of the increasingly sophisticated anti-forensic procedures hackers use to cover their tracks. Knowing forensics inside and out, as well as the tricks hackers use to foil forensics, is essential for professionals responsible for protecting the integrity of corporate data. Databases contain a high percentage of confidential data, yet many organizations lack the budget and management buy-in to implement protections. According to studies, 60% of organizations have experienced a breach in the past 12 months, 80% expect database attacks to increase and 40% on average fail security audits. There are plenty of tools to help thwart attacks -- such as vulnerability management products that include vulnerability assessment and user monitoring functionality -- but the trick is to deploy comprehensive solutions that help in forensics and provide visibility into how attackers cover their tracks. Common anti-forensics methodologies Where database actions are traced by different logging mechanisms such as backup, trace, transaction and operating system logs, sophisticated attackers try to hide their activities by gaining database administrator privileges to manipulate those logs. Some common ways attackers obtain administrator privileges include: Exploiting a vulnerability. Finding a valid login and password (by brute force, guessing, stealing or with the help of a trojan). Taking advantage of weak or missing access controls. Exploiting a vulnerability in an application or in the operating system. Attackers interfere with logs using the following techniques:??* Disable logging. Some logging mechanisms can be disabled by administrators by just running a command in the database server. This is the easiest way to avoid some logging mechanisms.
Create PDF with GO2PDF for free, if you wish to remove this line, click here to buy Virtual PDF Printer http://www.networksasia.net/print/4290 11/18/2009
Guarding against database anti-forensics
Page 2 of 4
Intercept and modify logging mechanisms. On most database management systems (DBMS), it's possible to extend functionality by loading external libraries. These libraries have code that can be executed inside the database server process. As a result, the code will have unrestricted access to all database process memory and components, allowing an attacker to manipulate logs at will. The attacker will be able to modify database server memory to intercept and avoid logging, insert backdoors, hijack user sessions and so on. Impersonate other database users. Because some DBMS allow privileged users to execute commands under different user accounts, it's possible to impersonate any user. When logs are reviewed after an attack they will point to an innocent user and send forensic investigators after false leads. Abuse logging mechanism design. With some database servers it's possible to delete and/or overwrite logs. Some logging mechanisms are designed to reuse log space after certain conditions are met. Log space can also be reduced with specific commands, forcing the oldest log entries to be deleted and/or overwritten. Attackers can force these conditions or execute commands to delete and/or overwrite log entries. Comprehensive user rights review capabilities will ensure you have appropriate access controls in place, security features enabled, security patches applied and strong password use enforced. By ensuring your databases are properly locked down, you can block an outside attacker's entry into your system or an insider's ability to escalate his privileges in a system he has legitimate access to.
Integrated vulnerability management in the database There are a number of solutions available to help organizations fight back, but the choices are convoluted so it is essential to develop a comprehensive vulnerability management program. Because attackers are looking for data they can monetize, and that confidential information spends 99% of its time in a database, it's clear that's where the focus should be. The first step toward creating a comprehensive security and compliance strategy at the database level is discovering your database assets. For example, if an attack happens, your remediation strategies grow much more cumbersome if you are unsure of exactly how many database instances you have. Are their multiple copies of those databases? Are there undiscovered databases? Not only will a comprehensive discovery process help you understand what you have to protect, it will help prioritize what to do with those instances containing the most sensitive data. Because an attacker can take over a poorly protected low-priority system and use that access as a launching pad to gain access to a high-priority system, it's key to protect everything connected to your network. Controlling access: Limit roles and privileges
Create PDF with GO2PDF for free, if you wish to remove this line, click here to buy Virtual PDF Printer http://www.networksasia.net/print/4290 11/18/2009
Guarding against database anti-forensics
Page 3 of 4
A critical component in protecting sensitive enterprise information is ensuring the segregation of duties in the database. Most organizations have no idea who has access to what data, and this makes them vulnerable to malicious insiders. It also means they're facing potentially non-compliant status if they were to be audited. Having an all-encompassing view of all user rights, roles and privileges across the enterprise allows internal audit teams and IT organizations to identify how certain privileges within one particular role were obtained -- and the potential vulnerabilities created with that role simply existing. For example, if a human resources person leaves a company, there is probably still a role that was created for that ex-employee in specific databases. It's worth examining that role to see the level of access, the criticality of the information stored and initiate steps to ensure that role is eliminated. Not only is this an important component of the vulnerability management life cycle, but demonstrating the segregation of duties is a critical component of many compliance mandates, including The Sarbanes-Oxley Act, the Health Insurance Portability and Accountability Act and others. Know what they're doing Another integral part of developing a comprehensive vulnerability management program is implementing database activity monitoring of user activity that will detect attacks of varying types. Preserving the evidence of the attack in a protected repository outside of a hacker's reach helps establish a powerful front against attackers who are applying antiforensics methods. Database monitoring (DAM) is all about privileged database users who can manipulate this functionality, monitoring the health and performance of the database, to avoid and/or disable monitoring as previously explained. These privileged users are by definition given access to the innermost zones. Even in a heavily secured environment, trust and verification drive the need for DAM in any system. DAM can be performed using third-party tools that can track all database activity based on predefined policies. When suspicious activity is detected by these tools, like anti-forensic procedures, they can fire alerts, block current activity, record the entire session and so on. When these tools are not part (not "inside") of the database server they can also closely monitor database administrators activities. Network-based monitoring can monitor multiple databases concurrently, but they can't see encrypted traffic or monitor local sessions (i.e., a database administrator using SSH to log on remotely and then connect locally to the database server). Host-based tools can monitor local and remote sessions but can only monitor databases running on the same server.
As database hacking cases involving sophisticated anti-forensic procedures continue to climb, these attacks will require equally sophisticated countermeasures. Understanding
Create PDF with GO2PDF for free, if you wish to remove this line, click here to buy Virtual PDF Printer http://www.networksasia.net/print/4290 11/18/2009
Guarding against database anti-forensics
Page 4 of 4
the fundamentals of forensics and the techniques hackers use to foil forensics are essential for professionals responsible for protecting the integrity of corporate data. Proactive security teams that establish a baseline of controls and segregation of duties at the database level and deploy the right mix of comprehensive database security, risk and compliance solutions will be able to protect the crown jewels of the organizationc -enterprise data. Cerrudo is a Team SHATTER Researcher with Application Security.
Create PDF with GO2PDF for free, if you wish to remove this line, click here to buy Virtual PDF Printer http://www.networksasia.net/print/4290 11/18/2009
You might also like
- WP Real Time Database MonitoringDocument12 pagesWP Real Time Database MonitoringngvsonNo ratings yet
- Chapter II NewwDocument3 pagesChapter II NewwCHARLES REBOLLOSNo ratings yet
- Database Security (Final Paper)Document21 pagesDatabase Security (Final Paper)mjcendanaNo ratings yet
- Database Security Concerns The Use of A Broad Range of Information Security Controls To ProtectDocument6 pagesDatabase Security Concerns The Use of A Broad Range of Information Security Controls To ProtectRahulJaiswalNo ratings yet
- 8 Steps To Holistic Database SecurityDocument6 pages8 Steps To Holistic Database SecurityelazarineNo ratings yet
- Dbprotect: Ensure Your Sensitive Data Is Secure and Your Compliance Requirements Are AchievedDocument6 pagesDbprotect: Ensure Your Sensitive Data Is Secure and Your Compliance Requirements Are AchievedRachid RachNo ratings yet
- Chapter - 1 Explain CIA ModelDocument68 pagesChapter - 1 Explain CIA ModelPriyaSharmaNo ratings yet
- C) 256 Bits AESDocument4 pagesC) 256 Bits AESsyafiq rossleyNo ratings yet
- Database - Security (1) AssignmentDocument23 pagesDatabase - Security (1) AssignmentAbdul Rehman ButtsarkarNo ratings yet
- Government Postgraduate Islamia College Faisalabad AssignmentDocument19 pagesGovernment Postgraduate Islamia College Faisalabad AssignmentAbdul Rehman ButtsarkarNo ratings yet
- SecurityDocument4 pagesSecurityRavindra PawarNo ratings yet
- Unit 5-DBPDocument37 pagesUnit 5-DBPHafiz RahmanNo ratings yet
- Security of Relational Database Management SystemDocument6 pagesSecurity of Relational Database Management Systemgicogap739No ratings yet
- Bit 420 Cat 1 and 2 Gs180289bsitDocument24 pagesBit 420 Cat 1 and 2 Gs180289bsitMERCY-JEDIDIAH-BELOVED OF JEHOVAH Nungari mukuruNo ratings yet
- DBSM Lect2Document30 pagesDBSM Lect2paki.kakawzdNo ratings yet
- CIS Assign3Document3 pagesCIS Assign3Roisu De KuriNo ratings yet
- TranslateDocument5 pagesTranslateBeltsazar AlfeusNo ratings yet
- Latest PPT Write UpDocument5 pagesLatest PPT Write Upvaishali guptaNo ratings yet
- Security of Database Management Systems: January 2016Document7 pagesSecurity of Database Management Systems: January 2016aNo ratings yet
- Kivy Akram Hama Database ReportDocument15 pagesKivy Akram Hama Database ReportKivy AkramNo ratings yet
- DBMS Unit - 5Document27 pagesDBMS Unit - 5JANMEETNo ratings yet
- DBprotect DatasheetDocument6 pagesDBprotect DatasheetmkrafessNo ratings yet
- Enhanced Distributed Accountability Framework With Indexing in The Cloud and Its Security AnalysisDocument6 pagesEnhanced Distributed Accountability Framework With Indexing in The Cloud and Its Security AnalysistheijesNo ratings yet
- White Paper Cyber Attack SurvivalDocument15 pagesWhite Paper Cyber Attack SurvivalshellrootNo ratings yet
- A System For Profiling and Monitoring Database Access Patterns by Application Programs For Anomaly DetectionDocument18 pagesA System For Profiling and Monitoring Database Access Patterns by Application Programs For Anomaly DetectionMansoorSulaimanNo ratings yet
- IT FP2250 KellyTravis Assessment6 1Document6 pagesIT FP2250 KellyTravis Assessment6 1Anas ToufeeqNo ratings yet
- A.2.3 Describe How A DBMS Can Be Used To Promote Data Security. Database SecurityDocument3 pagesA.2.3 Describe How A DBMS Can Be Used To Promote Data Security. Database SecurityPreeti SinghalNo ratings yet
- DSM Assignment 1Document15 pagesDSM Assignment 1Malik GoharNo ratings yet
- Chapter 3 Computer SecurityDocument17 pagesChapter 3 Computer SecurityYared AyeleNo ratings yet
- Database Security+Protection+RecoveryDocument8 pagesDatabase Security+Protection+RecoveryShivam PatelNo ratings yet
- Provide Network System Administration Last EditedDocument19 pagesProvide Network System Administration Last Editedsenderajemal30No ratings yet
- SSH CryptoAuditor 20120725 2Document10 pagesSSH CryptoAuditor 20120725 2JohnNo ratings yet
- OWASP Top 10 2021Document18 pagesOWASP Top 10 2021darknetbot307No ratings yet
- Database Security - Attacks and Control Methods: Emil BurtescuDocument6 pagesDatabase Security - Attacks and Control Methods: Emil BurtescurajipeNo ratings yet
- Cloud Security ConsiderationsDocument6 pagesCloud Security ConsiderationsPLHNo ratings yet
- Encryption NAS Environments WP (En) v2 WebDocument7 pagesEncryption NAS Environments WP (En) v2 Webunicycle1234No ratings yet
- Nine Principles of Security ArchitectureDocument5 pagesNine Principles of Security Architectureprateek217857No ratings yet
- A D S S F: Atabase Ystem Ecurity RameworkDocument10 pagesA D S S F: Atabase Ystem Ecurity RameworkAnonymous Gl4IRRjzNNo ratings yet
- Phases of The SDLCDocument5 pagesPhases of The SDLCAnnarathna ANo ratings yet
- Types of VulnerabilitiesDocument5 pagesTypes of VulnerabilitiesNikhil NaikNo ratings yet
- Auditing Operating SystemDocument10 pagesAuditing Operating SystemAndreasadityakurniantoNo ratings yet
- Isrm (1,2,3)Document21 pagesIsrm (1,2,3)Section DeeNo ratings yet
- Top 35 MitigationsDocument2 pagesTop 35 MitigationsskyrbNo ratings yet
- Tripwire ReportDocument30 pagesTripwire ReportNithin NaraynNo ratings yet
- Cyber Unit4 Lecture 5Document8 pagesCyber Unit4 Lecture 5Nitish YadavNo ratings yet
- Mod 2Document101 pagesMod 2MUSLIMA MBA21-23No ratings yet
- 3114 Securing Active Directory An Overview of Best Practices ArticleDocument6 pages3114 Securing Active Directory An Overview of Best Practices Articlej_cuenca_castro6473No ratings yet
- Network Security: Compiled: Engineer M. Mago, Mba, MSC (Electronics & Automation Engineering, Telecoms)Document16 pagesNetwork Security: Compiled: Engineer M. Mago, Mba, MSC (Electronics & Automation Engineering, Telecoms)prosper mukaroNo ratings yet
- What Is A Database Access Manager and Dynamic Data MaskingDocument3 pagesWhat Is A Database Access Manager and Dynamic Data Maskingoluyinkaa14No ratings yet
- 1763 ReadingDocument8 pages1763 ReadingTarik ShiguteNo ratings yet
- Security of DBMSDocument6 pagesSecurity of DBMSAshour MostafaNo ratings yet
- Intrusion Detection System For Database With Dynamic Threshold ValueDocument5 pagesIntrusion Detection System For Database With Dynamic Threshold ValueIjarcet JournalNo ratings yet
- Internet Security Journal - Internet Security Principles by Obedience Munashe KuguyoDocument9 pagesInternet Security Journal - Internet Security Principles by Obedience Munashe KuguyoObedience Munashe Kuguyo100% (15)
- Introduction To Enterprise Data ManagementDocument5 pagesIntroduction To Enterprise Data ManagementBenz ChoiNo ratings yet
- DBSM Lect3Document14 pagesDBSM Lect3paki.kakawzdNo ratings yet
- Team Members: Aparna Kolli, Anupama, Lakshmi GaneshDocument5 pagesTeam Members: Aparna Kolli, Anupama, Lakshmi GaneshvinhneNo ratings yet
- AZURE AZ 500 STUDY GUIDE-1: Microsoft Certified Associate Azure Security Engineer: Exam-AZ 500From EverandAZURE AZ 500 STUDY GUIDE-1: Microsoft Certified Associate Azure Security Engineer: Exam-AZ 500No ratings yet
- Security Operations Center - Analyst Guide: SIEM Technology, Use Cases and PracticesFrom EverandSecurity Operations Center - Analyst Guide: SIEM Technology, Use Cases and PracticesRating: 4 out of 5 stars4/5 (1)
- Penetration Testing Fundamentals-2: Penetration Testing Study Guide To Breaking Into SystemsFrom EverandPenetration Testing Fundamentals-2: Penetration Testing Study Guide To Breaking Into SystemsNo ratings yet
- Three Auth Protocols and Three Shakespeare TragediesDocument169 pagesThree Auth Protocols and Three Shakespeare TragediesKoldo UrculluNo ratings yet
- Siber Güvenlik SorularDocument14 pagesSiber Güvenlik SorularAnonymous eUJXtKNo ratings yet
- PDF Matriz de Riesgos NTP 330Document95 pagesPDF Matriz de Riesgos NTP 330Fede RamosNo ratings yet
- Income Tax Act, 2058 and Income Tax Regulation, 205921201613436 PMDocument248 pagesIncome Tax Act, 2058 and Income Tax Regulation, 205921201613436 PMSagun KatuwalNo ratings yet
- BankDocument3 pagesBankSS EntertainmentNo ratings yet
- Steem Keys PDFDocument1 pageSteem Keys PDFBarrëno I-lendrïxNo ratings yet
- Username EavDocument11 pagesUsername EavHarold BustamanteNo ratings yet
- Certified List of Overseas Voters (Clov) (Landbased)Document1,509 pagesCertified List of Overseas Voters (Clov) (Landbased)picefeatiNo ratings yet
- Email LogDocument23 pagesEmail LogIlham RamdhaniNo ratings yet
- PCI DSS v3-2Document139 pagesPCI DSS v3-2justforfun2009No ratings yet
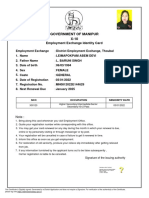
- Government of Manipur X-10: Employment Exchange Identity CardDocument1 pageGovernment of Manipur X-10: Employment Exchange Identity CardNongmaithem Bilash SinghNo ratings yet
- Semrush CookieDocument8 pagesSemrush CookieLaura Moreno RuizNo ratings yet
- Best Practices For Securing An Intelligent Building Management SystemDocument16 pagesBest Practices For Securing An Intelligent Building Management SystembdsisiraNo ratings yet
- Multi-Master Replication of OpenLDAP Server On CentOS 6.4Document5 pagesMulti-Master Replication of OpenLDAP Server On CentOS 6.4Sharizan SumuuiNo ratings yet
- Chapter 9Document7 pagesChapter 9Kad Saad100% (2)
- AWS Sso UgDocument146 pagesAWS Sso UgTanayaNo ratings yet
- Hows To Set Up SSH ServerDocument72 pagesHows To Set Up SSH Serversignup101No ratings yet
- EMC32 InstallationManual A5 en 11Document32 pagesEMC32 InstallationManual A5 en 11tuanvuanh200777No ratings yet
- Coalfire PCI 3 On AWS With Vormetric White Paper 2014 0312PCIDSSDocument22 pagesCoalfire PCI 3 On AWS With Vormetric White Paper 2014 0312PCIDSSval shaNo ratings yet
- Unit I (1.security Attacks & Services)Document28 pagesUnit I (1.security Attacks & Services)NandhiniRameshNo ratings yet
- PDF RPP Ukin DLDocument28 pagesPDF RPP Ukin DLyuniNo ratings yet
- Eve NG AddonsDocument24 pagesEve NG AddonsSureSh FreemanNo ratings yet
- Updates December 11 TH 2011Document5 pagesUpdates December 11 TH 2011Estêvão SchmitzNo ratings yet
- Eaadhaar 442910215551 01082017075641 316979Document1 pageEaadhaar 442910215551 01082017075641 316979Narasimhulu dhanikelaNo ratings yet
- Orange - HRM Test CaseDocument32 pagesOrange - HRM Test CasesyedNo ratings yet
- Salesforce - CRM Security Audit GuideDocument14 pagesSalesforce - CRM Security Audit GuideArthur EckleyNo ratings yet
- Auth Shield Lab - Mobile One Touch Authentication SolutionsDocument12 pagesAuth Shield Lab - Mobile One Touch Authentication SolutionsAuthShield LabNo ratings yet
- LinkDocument2 pagesLinkMorshedDenarAlamMannaNo ratings yet
- Lisa12 Final 22 #LoginInspectorDocument15 pagesLisa12 Final 22 #LoginInspectorsmanzzzNo ratings yet
- Python Requests Essentials - Sample ChapterDocument17 pagesPython Requests Essentials - Sample ChapterPackt PublishingNo ratings yet